A Privacy Impact Assessment (PIA) Philippines collects and processes personal data from its customers. Companies should have a clear understanding of how the data flows through their system. Identifying privacy risks early and then putting actions in place to address the risks ensures that companies comply with the Data Protection Act and other data protection regulations in the Philippines.
A good PIA process will also build confidence and trust among clients and the government. This document will give you a step-by-step approach for creating a successful Privacy Impact Assessment.
What Is a Privacy Impact Assessment (PIA)?
A PIA (Privacy Impact Assessment) is an analysis of how private information will be handled. It shows how your private information will be handled from beginning to end and shows us where there are risks of mishandling. In addition to identifying these risks associated with technical and operational aspects of the organisation’s business processes. It also ensures that all of these processes are aligned with the law.
Therefore, PIAs play an important role in understanding all technological aspects involved in the handling of individuals’ Private Information and are essential for assisting organisations in making informed decisions concerning privacy compliance in the Philippines. Well-prepared PIAs will provide documentation that the organisation understands and successfully manages its privacy risks.
When is a PIA Required Under the Philippine Data Privacy Act (DPA)?
Privacy Impact Assessments (PIA) are mandatory under the Philippine Data Privacy Act for all personal data projects. Government agencies and private organisations must conduct a PIA before implementing a new technology or system that includes personal data.
A PIA must also be prepared when a significant change occurs in how a business processes personal data. The purpose of this requirement is to promote proactive management of personal data risk in the Philippines. Conducting a PIA shows you are accountable to the National Privacy Commission (NPC) and provides the company with a greater degree of compliance with the law.
Key Benefits of Conducting a PIA for Businesses in the Philippines

An organisation will experience tangible and strategic advantages by performing a Privacy Impact Assessment (PIA). It offers confidence to stakeholders and supports a well-established process for managing risk, including IT security audits. It also helps in managing compliance based on strong data protection impact assessment practices.
Enhanced Regulation of Compliance
A PIA will help businesses comply with both the Philippines’ requirements for conducting PIAs and the Philippines’ Data Protection Act (DPA). It can be done through documentation of compliance measures taken, as well as the minimisation of the risk of incurring penalties from authorities. Conducting PIAs routinely facilitates the efficient performance of inspections and audits by regulatory authorities.
Identifying and mitigating risks
Organisations can eliminate or mitigate privacy risks before a data breach occurs by identifying risks through a PIA. It also allows organisations to implement appropriate control measures. Conducting PIAs facilitates the identification of both technical and operational vulnerabilities.
It allows organisations to evaluate the potential consequences of data breaches on the individual. Proactive elimination or mitigation of risks results in the minimisation of both financial losses and reputational loss.
Establishing stakeholder trust
Transparent privacy practices encourage stronger customer, partner, and employee relationships. Conducting a PIA demonstrates an organisation’s commitment to protecting sensitive personal data. It also improves their reputation with respect to the credibility and reliability of the organisation.
Operational Efficiency
By conducting a PIA, companies identify inefficiencies and gaps in their existing processes. When combined with vulnerability and penetration testing (VAPT), improvements to workflows and controls. It enables companies to have the ability to manage data more securely. Efficiency in processes will also reduce operational overhead and allow companies to be more consistent.
See how businesses in the Philippines achieved compliance and reduced risk. Read our case studies.
Step‑by‑Step Process for Conducting an Effective PIA
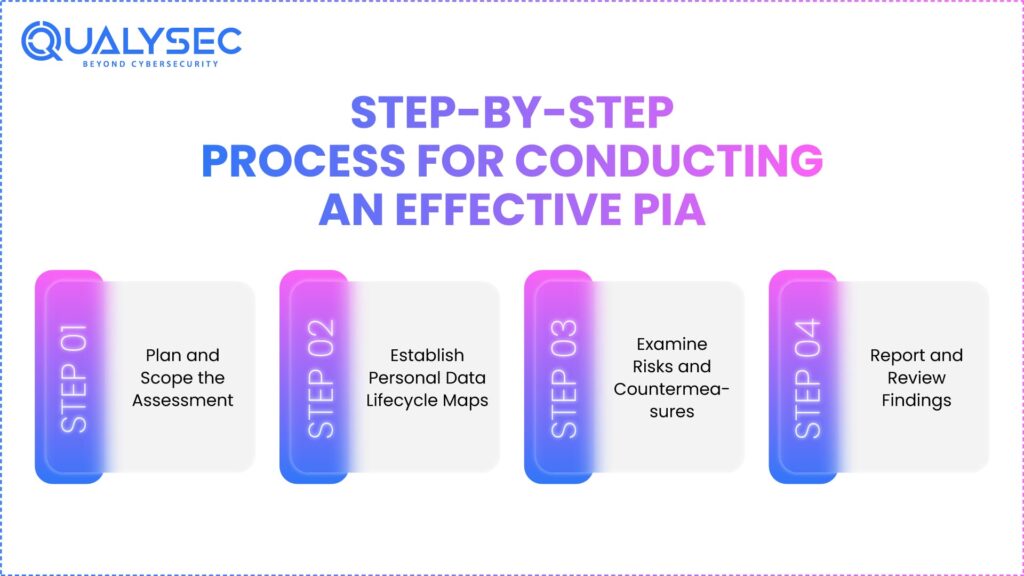
A structured Privacy Impact Assessment (PIA) provides clarity and enables compliance with the Philippines Data Privacy Act. Each phase enables businesses to thoroughly assess the potential privacy risks associated with their processing of personal information.
1. Plan and Scope the Assessment
Establish the overall goal, scope, and stakeholders for your PIA. Identify the categories of personal information being used and the activities being conducted to process that information. The Planning Component of the PIA will ensure you are using your resources effectively.
2. Establish Personal Data Lifecycle Maps
Capture information on the entire lifecycle of personal data, including the collection, use, and destruction of your personal data. Create a picture of where each person or group has access to each piece of personal data. Data map creation also helps to uncover unidentified vulnerabilities and build a framework for assessing risk. Learn more about Cybersecurity Risk Assessment Frameworks.
3. Examine Risks and Countermeasures
Determine all possible risks to personal data, then assess existing countermeasures, both Technical Controls and Organisational Controls. This will assist with prioritising risks by assessing their severity and probability of occurrence.
4. Report and Review Findings
Compile the assessment results that include risk evaluations and recommendations. Review the cybersecurity assessment findings with the affected stakeholders to confirm the accuracy and completeness of all findings. A complete and thorough report will support the stakeholders in preparing compliance reports and inform their future decisions.
Assessing Privacy Risks and Potential Impacts
Organisations can protect data subjects from harm through the use of Privacy Risk Assessment, which enables them to respond effectively to privacy issues before they occur.
Identifying Threats
Identify all possible threats that may arise from either outside or inside the company, like unauthorised access, data breaches, or unintentional erasures. A thorough examination of potential threats can help you develop effective control measures.
Evaluating Potential Impact
Evaluate how the potential security threat of a privacy violation might impact your customers and how your business may be harmed in terms of finances, reputation, and compliance. This will allow you to determine the order of priority when mitigating any identified risks.
Estimating Likelihood
For each risk identified, estimate how likely it is that this risk will occur. To do this properly, consider how often data will be processed and what their relative vulnerability levels are. By scoring the likelihood of each risk, you can allocate the right level of resources to the most serious threats.
Prioritising Risks
Once you have established the potential impact and likelihood of occurrence for each risk, rate them in order based on their importance. By combining the two, you will be able to make decisions regarding which ones to address first. Also, need to ensure that all areas that are at the highest risk receive immediate attention.
You might like to know about What Is AI Threat Detection. How ML Identifies Cyber Threats in Real-Time.
Evaluating Existing Security Measures and Gaps
Assessing existing protections is essential in assessing the efficacy of the privacy controls established by the organisation.
Benchmark Privacy Controls
Compares the organisation’s privacy controls against established best practices for all types of privacy safeguards – technical, administrative, and physical. The benchmarking will show where privacy controls can be improved.
Gap Analysis
Identifying the limitations of privacy protections caused by missing or ineffective controls helps organisations know where weaknesses actually exist. After being supported by a security testing methodology, this approach enables quicker identification of vulnerabilities and more effective allocation of resources to mitigate those risks.
Technical Evaluate Controls
Review Technical Safeguards, Encryption, Access Control, Monitoring, and Data Backup Systems. Compare them against the Risk Levels for which they are intended to provide protection. Conducting this Technical Evaluation allows for an assessment of whether or not the Technical Safeguards were functioning properly.
Organisational Evaluate Controls
Review the Privacy Policy, Staff Training, and Accountability Frameworks. The Organisational Controls increase the Enhanced Security of Technical Controls to provide for continued compliance with applicable laws and regulations.
Request a security assessment to identify gaps and protect your security defenses.
Developing Risk Mitigation and Compliance Controls
Mitigation Strategies provide the means through which to manage risks identified.
Define Remedial Action
Remediation actions are the clear steps identified to reduce or remove risk as part of effective cybersecurity risk management. Each action must be identified, and the expected outcome of each action should be specified. Remediation action should consider the operational feasibility of reducing the risk versus the benefits of operationally mitigating.
Assign Responsibility
The responsibility for implementing and monitoring the mitigation strategies should be assigned to individuals or teams. Holding someone accountable ensures there will be ongoing follow-through to complete the control measures within the designated timeframe.
Establish Target Timelines
Realistic due dates should be set for the mitigation strategy action plan completion. The timelines serve as a guide for tracking mitigation strategy progress and holding individuals accountable.
Documenting and Submitting the PIA to the NPC (When Required)
When it comes to showing that you’re following the PIA rules in the Philippines, having good documentation is really important. I mean, without it, it’s hard to prove anything.
Compile a PIA Report
One thing you have to do is put together a PIA report. That means summing up how you did the vulnerability assessment, what you found out, and any ways to fix the problems. It keeps everything clear, and it makes sure you’re ready if someone comes to check on you. Transparency like that just helps avoid issues later.
Include Stakeholder Inputs
Including what stakeholders say is another part. You know, like notes from the people who own the data or the privacy experts. Getting their input makes the whole thing more accurate, I think, and it covers everything without missing spots.
Maintain Revision History
Sometimes it feels like tracking changes is the boring part, but maintaining a revision history for the PIA is key for audits and security audits. You just keep records of all the updates over time. That shows you’re on top of privacy stuff proactively. It seems straightforward, but it can get messy if you don’t stay organised from the start.
Common Mistakes Businesses Make During PIAs
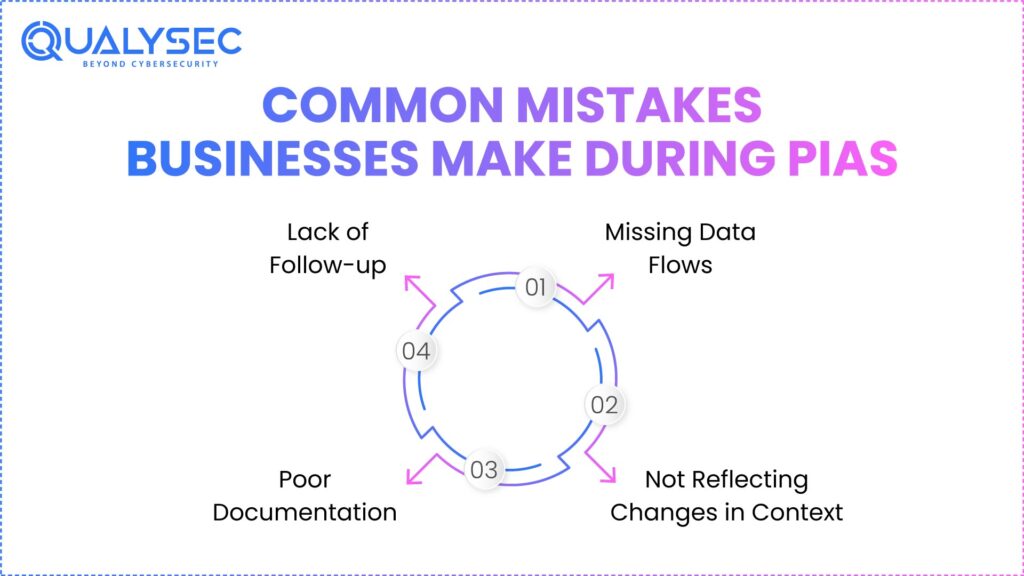
By understanding common mistakes, evaluators can enhance compliance and improve the quality of assessments.
Missing Data Flows
If all the data flows are not mapped, some unidentified risk may exist. The goal of comprehensive mapping is to ensure all personally identifiable (PII) data is accounted for.
Not Reflecting Changes in Context
When process changes occur, if someone does not update the PIA requirements after the process change takes place, there can be situations where an evaluator’s PIA is non-compliant. Regular PIA updates are needed to ensure that they accurately reflect the day-to-day operational environment.
Poor Documentation
Poor Documentation, including incomplete or vague reports, undermines credibility and results in a lack of readiness for audit. Assessments that are well-documented provide a basis for effective risk management decisions.
Lack of Follow-up
If remediation plans are not implemented, any risk identified remains unresolved. To successfully mitigate, management must complete all mitigation actions, and as such, they must follow up on any mitigation action at the appropriate level.
Download a sample penetration testing reportto understand where PIAs go wrong and how to fix those gaps early.
How Penetration Testing Supports Stronger Data Protection in PIAs
Penetration testing is basically a way to check if privacy controls are actually doing their job and to find those vulnerabilities that are not obvious at first.
We think the main thing it does is uncover hidden vulnerabilities through simulated attacks. These attacks show weaknesses in both the technical stuff and the operational controls, so that someone does not miss potential risks somehow. It feels like, without this, organisations might overlook some real threats.
When it comes to testing real-world scenarios, penetration testing looks at how systems hold up under conditions that mimic actual attacks. This helps confirm if the existing controls can really withstand those threats or not. That part seems important because theory is one thing, but practice is different. Know about penetration testing services for compliance and regulations.
The results from these tests also support risk prioritisation. Organisations can focus on the most critical vulnerabilities right away, which means they allocate resources more efficiently. Otherwise, everything might just pile up without a clear plan.
It validates the effectiveness of controls too, making sure mitigation measures work as intended. This ties into ongoing efforts for personal data risk assessment, especially in places like the Philippines. We’re not totally sure how that specific part plays out everywhere, but it supports the whole process.
Why Choose Qualysec for Privacy & Data Protection Assessments
Let us provide professional Privacy Impact Assessment Philippines services for you. Their staff is familiar with PIA Philippines regulations and customises the assessments to fit business requirements. They couple penetration testing with detailed documentation to accurately determine privacy risks.
Qualysec also offers actionable mitigation recommendations and NPC-ready reporting. This includes a whole array of ongoing monitoring services that help keep your data protection compliance in the Philippines fit and healthy for the long term.
Teaming up with Qualysec means you can establish a proactive, compliant and scalable privacy program that meets and exceeds the regulatory standards.
Conclusion
Privacy Impact Assessment Philippines is a must to ensure the protection of personal data. An organised Privacy Impact Assessment facilitates data protection compliance in the Philippines and reduces potential privacy issues.
It builds trust with customers, partners, and regulators to have better operational efficiency. Regular PIAs also help to keep organisations compliant with the Prosecution Authority of the Philippines Data Privacy Act.
Combining Risk assessment and mitigation, businesses establish a more resilient foundation for cyber privacy. Being on the front foot, managing privacy is now a competitive advantage.
Schedule a meetingto understand your security challenges and align your organisation with best practices and compliance standards.
FAQ’s
1. What does a privacy impact assessment do?
A Privacy Impact Assessment identifies how an organisation collects, uses, and stores an individual’s personal information. It evaluates the organisation’s privacy risks and the potential impact of those risks on individuals. The PIA also enables the organisation to implement controls that help eliminate compliance or security risks.
2. Is PIA a legal requirement?
Yes, the Philippines Data Privacy Act requires a PIA for certain types of processing activities to enable compliance with the law. Government entities are required to conduct a PIA for all their programmes that involve an individual’s personal data. Private sector entities must also conduct PIAs for processing their individuals’ personal data when processing that data creates a high level of privacy risk.
3. What is included in a PIA report?
A Privacy Impact Assessment Report will document the mapping of the data flows, identify and assess the privacy risk associated with the processing of the data, identify any security controls that are in place and describe the methods to mitigate the risks associated with the identified privacy risk. It will also define who is accountable for the privacy risk and outline the timelines and decisions required for compliance actions.
4. What is the meaning of PIA in the Philippines?
In the Philippines, the term PIA stands for Privacy Impact Assessment, which the National Privacy Commission mandated through the Data Privacy Act of 2012 as part of the implementation of the Data Privacy Act and compliance with other Philippine Laws.
5. Who needs to conduct a PIA?
Individuals or organisations collecting Personal Data from other individuals must conduct PIA assessments. All Government Agencies must conduct PIA cyber security assessments for every Data Processing System. All other organisations in the private sector will also be required by law to conduct PIA assessments of high-risk Data Processing Activities.
6. What are PIA rules?
According to PIA Rules, they must complete PIA Assessments before the commencement of Data Processing. They must update the data when new Data Processing technologies and methods are used. All PIA Assessments need to document and provide information to the National Privacy Commission on request.

























































































































































































































































































































































































































































































































































































































0 Comments