The NCA compliance is gaining more and more importance for businesses in Saudi Arabia. The government body dealing with the issue of cybersecurity in the Kingdom is the National Cybersecurity Authority (NCA). In addition, organisations should be aware that NCA compliance requirements are compulsory for governmental organisations and the critical infrastructural sectors. Moreover, proper NCA cybersecurity controls will assist businesspeople in the preservation of their valuable assets and the fulfilment of regulatory requirements. Moreover, the knowledge of Saudi Arabia NCA regulations ensures that organisations can operate within the legal and safe framework of the region.
Saudi Arabia has been developing in the field of cybersecurity over the last years. As a result, companies are under pressure to introduce stiff security measures. Thus, this handbook will allow organisations to navigate the world of the NCA compliance requirements and give valuable insights on how to implement it successfully.
What Are the Essential Components of the NCA Cybersecurity Framework?
The NCA cybersecurity controls framework has a number of specialised control sets which are aimed to cover different operational environments. All sets of controls have particular risks and security issues that an organisation encounters in its online activities.
Essential Cybersecurity Controls (ECC)
The ECC is the bottom tier of Saudi Arabia NCA regulations. Such controls offer a basic set of controls to be applied in every organisation. Also, five major domains of the ECC encompass all cybersecurity requirements.
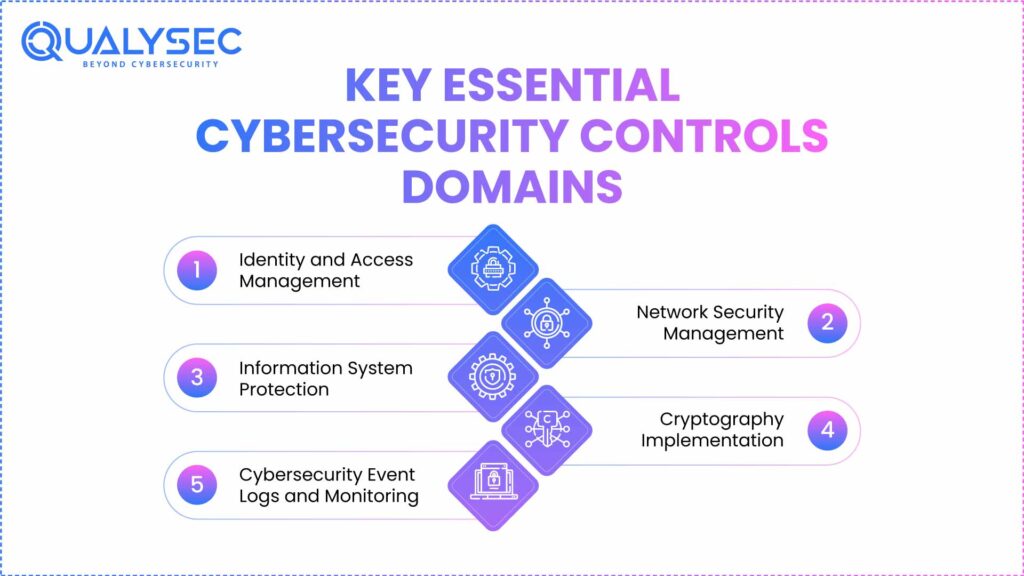
Key ECC Domains:
- Identity and Access Management
- Network Security Management
- Information System Protection
- Cryptography Implementation
- Cybersecurity Event Logs and Monitoring
The ECC framework makes sure that organisations have set a minimum level of security. Moreover, the controls assist in avoiding usual cyber threats and ensuring the efficiency of operations. This is why it is necessary to make ECC implementation the top priority of business in the first place, as it leads to NCA compliance.
Cloud Cybersecurity Controls (CCC)
The CCC contains the special requirements of cloud computing security. Those organisations that utilise cloud services must have these extra controls on top of the minimum ECC control requirements. In addition, there are obligations of both Cloud Service Providers (CSPs) and Cloud Service Tenants (CSTs) within this framework.
There are four domains in the CCC model and 24 subdomains. It also targets four strategic pillars, namely Strategy, People, Procedures and Technology. These aspects collaborate in bringing about complete cloud security in place.
Other Specialized Control Frameworks
NCA compliance requirements also include several specialised frameworks:
- Telework Cybersecurity Controls (TCC) – Addresses remote work security
- Critical Systems Cybersecurity Controls (CSCC) – Protects critical infrastructure
- Operational Technology Cybersecurity Controls (OTCC) – Secures industrial systems
- Data Cybersecurity Controls (DCC) – Focuses on data protection throughout its lifecycle
| Control Framework | Primary Focus | Target Organizations |
| ECC | Fundamental cybersecurity | All organizations |
| CCC | Cloud security | Cloud users and providers |
| TCC | Remote work security | Organizations with telework |
| CSCC | Critical systems | Government and critical infrastructure |
| OTCC | Operational technology | Industrial and manufacturing |
| DCC | Data protection | Data-handling organizations |
Latest Penetration Testing Report

How Can Organizations Implement Effective NCA Compliance Programs?
The NCA compliance is of concern to be implemented in a systematic manner that covers technical and organisational requirements. Organisations are required to ensure that they come up with comprehensive programs that address all the control frameworks that apply. Also, the effective implementation requires powerful leadership and sufficient resource distribution.
Establishing a Compliance Foundation
Companies ought to start with the NCA audit and evaluation processes. It is done to detect the existing security gaps and compliance deficiencies. In addition, the evaluation gives a map on how to focus on improvement and the provision of resources.
Key Implementation Steps:
- Conduct comprehensive risk assessments
- Map existing controls to NCA requirements
- Identify compliance gaps and vulnerabilities
- Develop remediation plans with clear timelines
- Establish ongoing monitoring and reporting processes
- Train staff on new policies and procedures
Technical Implementation Requirements
The NCA cybersecurity controls need to have certain technical implementations in different areas of technology. Organisations should have made sure that their systems are able to produce proper logs, take correct access control measures and have secure settings. Additionally, technical controls should be able to merge with any existing infrastructure and fulfil their performance requirements.
Network security management is a very important element of technical implementation. Companies should carry out an appropriate network segmentation, intrusion detection system, and secure remote access protocols. Also, there are encryption requirements which require certain cryptographic implementations to protect data.
Organisational Process Development
In addition to technical controls, the NCA compliance requirements will require strong processes within the organisation. These processes maintain continuity in the implementation of security controls and their maintenance. In addition, compliance management should have defined roles and responsibilities in organisations.
Process Development Areas:
- Policy development and maintenance
- Incident response and threat management
- Change management procedures
- Security awareness training programs
- Vendor management and third-party assessments
- Documentation and record-keeping systems
What Are the Key Challenges in Achieving NCA Compliance?
Organizations are faced with many difficulties in applying the Saudi Arabia NCA rules. Such challenges include technical challenges and resource constraints. Furthermore, the threat environment is rapidly changing, which demands the identification of the security measures
Technical Complexity Challenges
There is a tendency for NCA cybersecurity controls to involve advanced technical implementation. The challenge of adopting new security tools in an organisation that is already in place is a problem in many organisations. It is also a constant problem to ensure that the system is well configured and at the same time make it efficient to operate.
Elderly systems present specific challenges to NCA compliance. These systems might not have the latest security measures, which are desirable as per the existing regulations. Moreover, the modernisation or change of the old infrastructure would demand a lot of investment and planning.
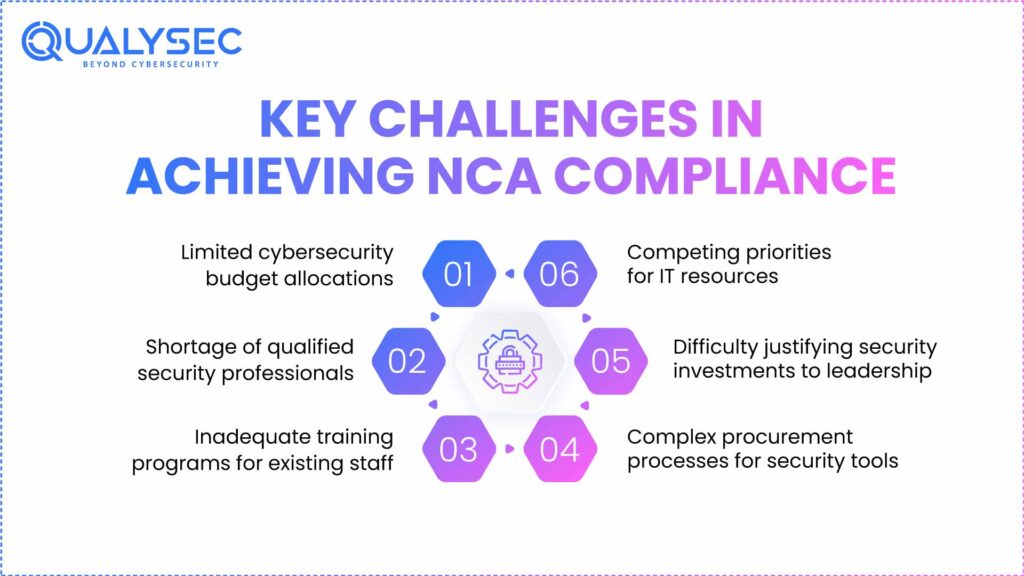
Resource and Expertise Limitations
Most organisations do not have adequate cybersecurity skills to enforce the NCA compliance requirements. It is not easy to establish internal capabilities, since there is a shortage of qualified cybersecurity professionals. Moreover, organisations have to reconcile security investment with other areas of business.
Common Resource Challenges:
- Limited cybersecurity budget allocations
- Shortage of qualified security professionals
- Inadequate training programs for existing staff
- Competing priorities for IT resources
- Difficulty justifying security investments to leadership
- Complex procurement processes for security tools
Ongoing Compliance Maintenance
Initial compliance with NCA is just the start of an organisation. The ongoing process of compliance is only possible by constantly monitoring, updating, and enhancing security controls. Besides, the organisations have to be flexible to changing threats and regulatory variations.
Periodic NCA assessment and audit are done to reinforce compliance. These tests are, however, intensive in terms of resources and expertise. In addition, the organisations have to respond to observed deficiencies as soon as possible to save their compliance status.
How Does Professional NCA Compliance Consulting Add Value?
NCA compliance consulting services offer expert skills to an organisation and best practices. The professional consultants can be of great help when it comes to understanding the regulatory requirements and the best practices in their implementation. Also, they assist organisations to overcome the usual traps and to speed up their compliance process.
Expert Knowledge and Experience
Professional consultants have profound experience with the regulations of the Saudi Arabia NCA in different industries. They are knowledgeable about the details of various control structures and can give specific instructions. Also, consultants are up to date with the regulatory changes and new threats.
Consultant Value Propositions:
- Comprehensive knowledge of all NCA control frameworks
- Industry-specific implementation experience
- Access to proven methodologies and tools
- Ongoing regulatory update awareness
- Risk-based approach to compliance prioritisation
- Cost-effective resource utilisation strategies
Accelerated Implementation Timelines
NCA compliance consulting services assist the organisations in reaching compliance quickly than by working individually. Consultants give systematic project management and implementation roadmaps. In addition, they assist organisations to prevent expensive errors and redoing of work in the implementation process.
Professional consultants also come with established relationships with vendors and recommendations of tools. This experience assists companies in choosing suitable security solutions and not causing needless complexity. Moreover, the consultants may also offer training and transfer of knowledge to the internal teams.
Why Qualysec Leads NCA Compliance Excellence in Saudi Arabia
In Saudi Arabia, the leader in the field of NCA compliance consulting is Qualysec. The firm brings together profound regulatory knowledge and experience in practice in different industries. Moreover, the personnel at Qualysec consists of qualified experts who are well aware of the regulations of Saudi Arabia NCA.
Qualysec’s Unique Advantages:
Qualysec will provide the entire NCA compliance services covering all control frameworks such as ECC, CCC, TCC, CSCC, OTCC, and DCC. The company strategy will start with intensive NCA audit and evaluation processes which will give clear insight on the existing compliance status. Also, Qualysec will design tailored remediation strategies that are consistent with the goals of business and budget limitations.
The technical knowledge of the company deals with the entire NCA cybersecurity controls application. The consultants at Qualysec have practical experience in the implementation, management and integration issues of security tools. In addition, they offer continuous assistance in maintaining compliance sustainability.
The service offerings of Qualysec can be categorized as risk analysis, policy gap analysis, policy development, technical implementations, training of staff and continuous compliance monitoring. The project management approach adopted by the company provides quality delivery at its desirable time. Moreover, Qualysec offers detailed documentation and transfer of knowledge to the client teams.
Contact Qualysec today for a free consultation and discover how their expertise can accelerate your NCA compliance journey while reducing costs and risks.
Qualysec is based in Saudi Arabia and has sufficient knowledge of the local business settings and cultural dynamics. The consultants of the company collaborate with their clients to achieve knowledge transfer and a successful implementation process. Also, Qualysec has a flexible model of engagement that fits a wide range of organizational needs and budgets.
Conclusion
The NCA compliance is one of the most serious demands of the business environment in the developing sphere of cybersecurity in Saudi Arabia. However, organizations should realize that NCA cybersecurity controls take extensive planning, resource provision, and devotion. In addition, Saudi Arabia NCA laws are quite complicated and require expert skills to be implemented successfully.
The different control frameworks, such as ECC, CCC, TCC, CSCC, OTCC and DCC, have diverse risk settings and environments of operation. Hence, the organisations must be very keen to evaluate what frameworks can be applied in their particular circumstances. Also, appropriate NCA audit and assessment operations assist in covering all the areas of compliance.
NCA compliance consultation services offered by professionals are useful during the implementation process. Expert consultants introduce specialised expertise, methodology, and expediting schedules of great value to organisations. Moreover, the continued support can ensure compliance and adjust to the changing needs.
Schedule your free NCA compliance consultation with Qualysec experts today to begin your journey toward comprehensive cybersecurity compliance in Saudi Arabia.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
FAQ
Q1. What is NCA in compliance?
NCA compliance is defined as compliance with cybersecurity standards put in place by the National Cybersecurity Authority of Saudi Arabia. Companies have to adopt numerous NCA cybersecurity controls, such as Essential Cybersecurity Controls (ECC) and other specific frameworks.
Q2. What is NCA in Saudi Arabia?
The National Cybersecurity Authority (NCA) is the main cybersecurity regulatory institution in Saudi Arabia and the main one that oversees the cybersecurity environment in the country. The NCA regulates the Saudi Arabia NCA regulations that control cybersecurity operations within governmental and non-governmental organisations in the country.
Q3. What is the NCA framework?
NCA compliance requirements are a set of various controls that are oriented towards meeting different requirements in cybersecurity. The framework consists of Essential Cybersecurity Control (ECC) and specialised controls such as CCC, TCC, CSCC, OTCC, and DCC.
Q4. What is the full form of NCA in cybersecurity?
NCA is abbreviated as National Cybersecurity Authority in relation to cybersecurity. These government bodies come up with the Saudi Arabia NCA regulations, which are the central body of cybersecurity regulations in the Kingdom.
Ready to achieve NCA compliance? Contact Qualysec now for expert guidance and comprehensive compliance solutions tailored to your organization’s needs.

























































































































































































































































































































































































































































































































































































































0 Comments