Penetration test guidance under FedRAMP is crucial to cloud service companies that intend to provide services federally and uphold high standards of cybersecurity. FedRAMP involves a security assessment, and this should be conducted to a greater extent as penetration testing forms a vital element of the authorization process. Get information about good FedRAMP penetration test guidance, and the cloud providers can easily avoid the compliance regulations and still secure confidential government information.
The cloud providers that work in the federal space would have to establish their security posture by going through intensive testing methodologies. Penetration testing, including FedRAMP penetration testing, is not like any regular security test, and therefore, the FedRAMP will involve different and special approaches tailored to the government security structure and risk management approaches. This exhaustive outline gives detailed reports on how to carry out successful penetration tests according to FedRAMP standards.
FedRAMP requirements of penetration testing are complex and require planning, implementation, and documentation. The cloud providers should be aware of the regulatory framework for federal cloud security, as well as the technical process of testing. With the use of established FedRAMP pentest recommendations, an organization is able to get authorization quickly and gain the trust of the government customers.
What Is FedRAMP Penetration Testing?
Definition and Core Components
FedRAMP penetration testing is a controlled security evaluation procedure that caters to cloud service providers, according to federal agencies of the U.S. government. It is an advanced type of testing that tests the cloud system’s security stance against a rigorous set of requirements that are described in the FedRAMP security control baseline.
Elements of FedRAMP Penetration Testing:
- Government-Specific Framework: includes federal security requirements and approaches to risk assessment techniques
- 3PAO Qualification: They must be performed by a third-party assessment organization under qualification
- Multi-Layer Assessment: Analyzes network, application, and data levels of security. It can be performed at the network, application, and information security layers.
- Compliance Verification: the verification of implementation of NIST SP 800-53 controls
- Thorough Reporting and Evidence Gathering: Extensive reports and data have to be collected
Overview of testing methodology
FedRAMP pentest guidance indicates that a systematic approach should be adopted, which would entail, amongst others:
Technical Assessment Areas:
- Network Infrastructure Security: Network segmentation, firewall setups, and intrusion detection systems
- Application Security: Input validation, Secure coding initiatives, and authentication mechanisms
- Data Protection: The use of encryption, classification of the data, and access control
- Access Control: Access identity, privilege, and authentication
- Incident Response: Monitoring, response process and forensic preparation
Elements of Process Evaluation:
- Security Control Implementation: Confirmation of the necessary controls by the FedRAMP baseline
- Policy and Procedure Review: evaluation of recorded security procedures
- Configuration Management: Change Control and System Hardening Review
- Continuous Monitoring: Audit of the ongoing security validation activities
- Risk Management: Evaluation of identifying and mitigating risk measures
Get Expert FedRAMP Penetration Testing Guidance Today!
Don’t navigate the complex FedRAMP compliance landscape alone. Our certified security professionals have helped over 500+ organizations achieve successful FedRAMP authorization through comprehensive penetration testing services.
Why Is Penetration Testing Critical for FedRAMP Compliance?
Penetration testing of FedRAMP is an important part of the federal cloud authorization process, as part of the FedRAMP penetration testing is necessary to validate security controls and risk management processes. There has to be total assurance that the cloud services are secure before the government agencies give them the responsibility of holding sensitive federal information. FedRAMP penetration test guidance assures cloud providers that they can show their capacity to block any advanced cyber threats that could alter government systems.
Government Security Requirements
The result of FedRAMP penetration testing helps form the mainstay of the federal cloud authorization procedure, delivering necessary confirmation of security arrangements and risk management processes. Government agencies can only entrust cloud services with sensitive federal data when they are confident beyond any doubt about the level of security of the mainframes involved.
Critical Security Areas:
- Threat Resistance: The confirmation that systems would be able to resist intelligent cyber attacks
- Data Protection: Having reliable protection of sensitive information of the government
- Operational Continuity: Assuring business-oriented security doesn’t damage critical activities.
- Verification of compliance: confirmation of compliance with federal security requirements
- Risk Mitigation: Finding and solving possible security vulnerabilities
Advantages of Cloud Providers to Businesses
Compliance with FedRAMP penetration testing guidelines is very beneficial:
Benefit of Market Access:
- Federal Customer Trust: Demonstrates commitment to government security standards
- Competitive Advantage: Government cloud service contracts must be provided
- Risk Reduction: Proactive security risk vulnerability detection
- Compliance Assurance: Continuous assurance validation of the effectiveness of security controls
- Business Continuity: Lower chances of security attacks and data loss
Is Your Cloud FedRAMP-Ready? Uncover hidden risks with expert penetration testing. Secure Your Cloud Now.
Qualysec’s cloud pentest gives you results—no endless emails, no digging through PDFs, no guesswork.

FedRAMP Penetration Test Requirements at a Glance
The FedRAMP penetration testing requirements are elaborate and have to be performed as per certain set guidelines provided by the FedRAMP Program Management Office (PMO). To conduct such assessments, cloud service providers have to employ accredited 3PAOs to perform these tests by using reference methodologies and records. The FedRAMP pentest checklist consists of several parts that should be considered in the course of the tests.
The most important FedRAMP penetration test guidance requirements are:
- Scope Definition: Closely define the scope of testing where all the system parts are inside the authorization boundary.
- Testing Methodology: Apply accepted QA/testing frameworks that conform to NIST standards and FedRAMP testing standards.
- Documentation Standards: Keep well-documented records of what occurred in all testing activities, results, and remediation activities.
- Qualified Staff: This should also involve testing by duly qualified personnel having proper security clearances.
- Reporting Requirements: Produce detailed reports that are FedRAMP documented.
FedRAMP penetration testing requires particular tests to be conducted and a specific frequency of attacks. Authorization needs thorough baseline testing in the initial stage and frequent assessment cycles in compliance. All the key systems (network infrastructure, applications, databases, and supporting services) should be inspected in the FedRAMP penetration testing.
In FedRAMP vulnerability assessment processes, users should include both automatic and manual testing methods. Automated tools help cover the most common vulnerabilities, and testers use manual testing to address complex attack scenarios and business logic flaws. The duo helps provide an end-to-end assessment of security posture at the different levels of the systems.
The FedRAMP pentest checklist demands the authentication of certain security controls identified in NIST SP 800-53. These controls cut across various security families, such as access control, audit/accountability, configuration management, and system and communications protection. Testing requires verification to determine the extent of implementation and performance of every control that applies.
Step-by-Step FedRAMP Penetration Test Guidance
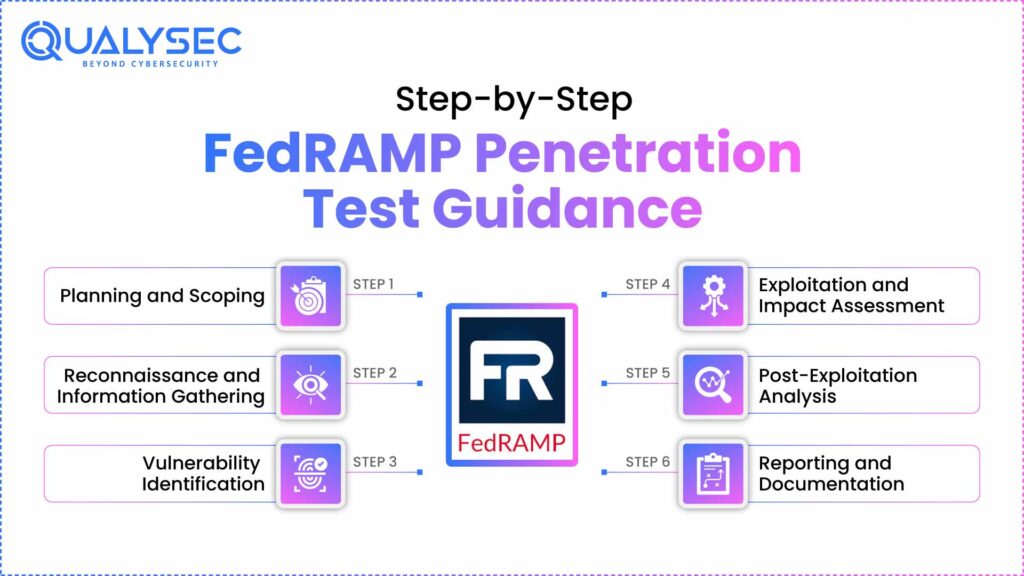
Step 1: Planning and Scoping
Obligatory planning, including the scope of the FedRAMP penetration test, stands first on the list of its steps. The cloud providers also have the obligation of collaborating with their 3PAO to establish the radius of the test and purpose and strategy. This phase will require extensive documentation of the systemic design, containing all the attributes of the authorization boundary.
The FedRAMP penetration testing planning method calls for paying a little attention to the most granular characteristics of the government clouds. It also involves the awareness of the sensitivity types of data, compliance, and operational limitations requirements, which may influence the testing process. Planning prepares the stage for the successful conduction of the tests, and there is a need to ensure every stakeholder is aware of their roles and duties.
Step 2: Reconnaissance and Information Gathering
FedRAMP pentest guidance has placed a lot of focus on how to conduct investigations during reconnaissance activities, which are meant to be akin to real-life attacks. The testing teams need to obtain the information on target systems by means of the approved methodologies that do not hinder the operations. This step determines possible attack vectors and assists in providing direction to the testing procedure in accordance with risk ranking.
The FedRAMP penetration testing activities should be able to abide by the FedRAMP penetration testing requirements and cover as much of the possible content of the target environment as possible. Testing teams use many techniques to map network topology, identify services, and list possible entry points. They should well record any kind of reconnaissance operation to aid in later testing processes.
Step 3: Vulnerability Identification
The vulnerability identification part of the FedRAMP vulnerability assessment entails the scanning and analytical evaluation of target systems systematically. Testing teams make use of authorized tools and methods to detect possible security vulnerabilities in all components of the system. The phase should not be so comprehensive that it jeopardizes important services of the government.
Penetration testing for FedRAMP needs full-fledged vulnerability testing, including technical and procedural vulnerabilities. Testing teams have to assess the security of the network, the vulnerabilities in the application, incorrect configuration, and lapses in access control. The identification phase should reveal enough information to do efficient risk assessment and prioritization.
Step 4: Exploitation and Impact Assessment
FedRAMP penetration test guidance entails proper exploitation of perceived identified vulnerability in an attempt to prove the impact that this may have on government operations. The testing teams should adhere to accepted methodologies that test security vulnerabilities without causing any form of disruption to the operations. This step gives clear points on the security gaps, including their likely effects.
The exploitation segment of FedRAMP penetration testing requirements should be the most careful one to safeguard delicate government information. Testing teams should receive the right approvals prior to trying to exploit and should possess good rollback measures. Every exploitation effort should be well documented to facilitate remedial planning.
Step 5: Post-Exploitation Analysis
After successful exploitation, the FedRAMP penetration testing involves a thorough examination of possible attack progress and possibilities of data access. Testing teams are required to determine how compromised they can be based on the identified vulnerabilities and determine how confidentiality, integrity, and availability of government data can be adversely affected.
Government cloud environments have specific issues that post-exploitation analysis needs to take into account. FedRAMP pentest guidance also focuses on knowing how the vulnerabilities may be exploited so as to reach a broad compromise of the system itself. The analysis will facilitate proper risk assessment and will allow one to prioritize remediation.
Step 6: Reporting and Documentation
The last step in the FedRAMP penetration test guidance is to report exhaustively on the documentation requirements of FedRAMP. The testing teams must provide a report that contains an executive summary, technical results, risks, and remediations. They should present the reports in a way that is acceptable to technical and executive readers.
FedRAMP penetration tests should also have certain details that are stipulated by the FedRAMP PMO. This incorporates weakness ratings, effect examination, and thorough repair directives. Reports should be transparent, must be able to take action, and bring adequate information to facilitate proper remediation planning and implementation.
Schedule Your Free FedRAMP Readiness Consultation and discover:
- Gap analysis of your current security posture
- Customized penetration testing roadmap
- 3PAO coordination and project management
- Ongoing compliance support and monitoring
Book Your Free 30-Minute Strategy Call Now → [Contact Our FedRAMP Experts]
Our experts at Qualysec have helped secure fintech, SaaS, and enterprise systems across 25+ countries. Manual + Automated Pentesting. No false positives. Actionable reports.

Tips to Prepare Your Cloud System for a FedRAMP Penetration Test
- FedRAMP penetration testing relies on preparation to achieve prosperous results. Before bringing in 3PAOs, cloud providers are expected to perform an internal assessment in an effort to discover and patch apparent deficiencies. This is a proactive way of decreasing the probability of any critical discoveries in the course of the official testing and shows organizational adherence to high levels of security.
- The FedRAMP pentest guidance advises the execution of full logging and monitoring functions before the onset of testing. The systems give useful information on the testing processes and enable organizations to know the efficacy of their security measures. Appropriate logging also helps in the incident response and forensic analysis, where necessary.
- System documents have to be up-to-date as well as complete in order to facilitate a proper FedRAMP vulnerability assessment exercise. Cloud providers ought to keep elaborate network designs, system layouts, and security control implementations. It enables testing teams to know how the systems are designed and place their emphasis on essential parts.
- Training and awareness should be included when preparing the FedRAMP penetration testing. Technical teams should be aware of testing procedures and the role they play in assisting assessment procedures. Proper communication channels and escalation are necessary to ensure there is fluid execution of testing activities and a quick response in case anything goes wrong.
- Before the testing starts, the FedRAMP pentest checklist must be thoroughly examined. Organizations are supposed to ensure that they have the necessary security controls in place and are in proper condition. This comparison allows for determining possible shortcomings and provides opportunities to take active remedial action.
Before your assessment, explore how vulnerabilities are identified and remediated. Download Our Cloud App Penetration Testing Sample Report
Common Challenges and How to Overcome Them
FedRAMP penetration testing presents unique challenges that require specialized expertise and careful planning to overcome. One common challenge involves balancing thoroughness with operational continuity, as government systems often support critical functions that cannot be disrupted during testing. FedRAMP pentest guidance addresses this challenge by emphasizing careful planning and coordination with operational teams.
Scope creep represents another significant challenge in FedRAMP penetration testing requirements. Complex cloud environments often have interconnected components that extend beyond the initial authorization boundary. Testing teams must maintain clear scope boundaries while ensuring comprehensive coverage of all security-relevant components.
Resource constraints can impact the effectiveness of FedRAMP vulnerability assessment activities. Qualified testing personnel are in high demand, and comprehensive testing requires significant time and resources. Organizations can overcome this challenge by planning assessments well in advance and working with experienced 3PAOs who understand FedRAMP requirements.
Documentation requirements for FedRAMP penetration testing are extensive and must meet specific government standards. Many organizations struggle with producing reports that satisfy both technical and compliance requirements. Working with experienced consultants and following established templates can help overcome documentation challenges.
Talk to our experts at QualySec to understand how we address these common challenges and ensure successful FedRAMP compliance outcomes through our advanced penetration testing services.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
FedRAMP Penetration Testing Best Practices
Implementing best practices is essential for successful FedRAMP penetration test guidance execution. Organizations should establish clear testing objectives that align with business goals and compliance requirements. These objectives guide testing activities and help ensure that assessments provide meaningful insights into security posture.
- FedRAMP penetration testing best practices emphasize the importance of continuous improvement and lessons learned integration. Organizations should conduct post-testing reviews to identify areas for improvement in both security controls and testing processes. This iterative approach helps enhance security posture over time.
Communication management is critical throughout FedRAMP pentest guidance implementation. All stakeholders must understand their roles and responsibilities, and clear escalation procedures must be established. Regular status updates and progress reports help maintain alignment and address issues promptly.
- FedRAMP penetration testing requirements demand rigorous quality assurance throughout the testing process. Testing teams should implement peer review processes and quality checkpoints to ensure accurate and comprehensive results. Quality assurance helps prevent errors that could impact compliance outcomes.
Risk management must be integrated throughout FedRAMP vulnerability assessment activities. Testing teams should continuously assess and mitigate risks associated with testing activities while ensuring comprehensive coverage of security controls. This balanced approach protects operational systems while achieving testing objectives.
Book a free consultation with QualySec today to learn how our specialized FedRAMP penetration testing services can accelerate your path to government cloud authorization and ensure long-term compliance success.
Conclusion
FedRAMP penetration test guidance provides cloud service providers with the framework necessary to achieve and maintain government cloud authorization. The comprehensive testing requirements ensure that federal agencies can trust cloud services with sensitive government data and mission-critical applications. Following established FedRAMP pentest guidance helps organizations navigate the complex compliance landscape while building robust security postures.
Success in FedRAMP penetration testing requires careful planning, qualified expertise, and thorough execution of approved methodologies. Cloud providers must invest in proper preparation, documentation, and ongoing compliance maintenance to achieve sustainable authorization outcomes. The investment in comprehensive FedRAMP vulnerability assessment processes pays dividends through increased government market access and enhanced security capabilities.
The evolving nature of cyber threats demands continuous attention to FedRAMP penetration testing requirements and ongoing security improvement. Organizations that embrace comprehensive testing and constant monitoring position themselves for long-term success in the government cloud market. By following the step-by-step guidance outlined in this article, cloud providers can achieve FedRAMP compliance efficiently and effectively.
Download our Pentest Report template to see how QualySec delivers comprehensive FedRAMP compliance documentation that exceeds government standards and accelerates your authorization timeline.
Latest Penetration Testing Report

FAQs
1. How to prepare for a FedRAMP?
Preparing for FedRAMP penetration testing requires comprehensive planning and a systematic approach to security control implementation. Organizations should begin with a detailed gap analysis comparing the current security posture against FedRAMP penetration testing requirements. This assessment identifies areas needing improvement before formal testing begins.
Key preparation steps include implementing comprehensive logging and monitoring systems, updating system documentation, and conducting internal security assessments. Organizations should also ensure staff training on FedRAMP pentest guidance procedures and establish clear communication protocols with testing teams.
2. What is the cost of FedRAMP penetration testing?
The cost of FedRAMP penetration testing varies significantly based on system complexity, scope, and chosen 3PAO provider. Typical costs range from $50,000 to $500,000, depending on the authorization level and system architecture. FedRAMP vulnerability assessment costs include 3PAO fees, remediation efforts, and ongoing compliance maintenance.
Organizations should budget for both initial testing costs and ongoing compliance expenses. FedRAMP pentest guidance recommends obtaining detailed cost estimates from multiple 3PAOs and factoring in potential remediation costs when planning budgets.
3. How often is FedRAMP penetration testing required?
FedRAMP penetration testing frequency depends on the authorization level and system changes. Initial authorization requires comprehensive baseline testing, while ongoing compliance demands annual assessments for most systems. FedRAMP penetration testing requirements may require additional testing following significant system changes or security incidents.
Continuous monitoring and FedRAMP vulnerability assessment activities supplement formal penetration testing cycles. Organizations must maintain ongoing security validation between formal testing periods to ensure continued compliance with government standards.
4. What types of systems are in scope for FedRAMP testing?
FedRAMP penetration testing scope includes all components within the defined authorization boundary of cloud service offerings. This typically encompasses network infrastructure, applications, databases, supporting services, and administrative interfaces. FedRAMP pentest guidance requires comprehensive coverage of all security-relevant system components.
The FedRAMP pentest checklist includes both technical systems and supporting processes, such as incident response procedures and security control implementations. Testing scope must be clearly defined during planning phases to ensure comprehensive coverage while maintaining operational continuity.























































































































































































































































































































































































































































































































































































































0 Comments