In today’s digital world, protecting our information is not just a good idea; it’s a necessary thing to do. This is where data protection services come into play. There are many different types of data protection services, including tools that lock your files, manage who has access to your files, retrieve lost data, and much more, to protect your files. These services are here to protect you before a problem occurs. In this article, we will discuss data security services in cybersecurity and the major online threats we will face potentially in 2025, the main services that will protect us, the benefits of each of them, and how Qualysec could fit in. Let’s go.
Key Threats to Data Security Services in Cybersecurity
Threats on the internet are emerging faster than ever before, putting secure information and data security at ongoing risk. Hackers have new tricks, like using AI-powered attacks, and future threats are being tested with computing beyond current capabilities. Portable internet-connected devices are also very difficult to manage and track. Increased awareness of these issues is the first step in establishing strong protections.
1. AI-Driven Threats
Hackers are using AI to produce highly believable scam emails, fake videos, and intelligent viruses that can learn to defeat protection efforts. These attacks will become increasingly difficult to identify and evade normal protections.
Read Also: AI Threat Intelligence: Enhancing Penetration Testing Strategies
2. Ransomware & Supply Chain Risks
Ransomware remains acute and is amplified by the reliance on supply chain attacks. Attackers are increasingly targeting supply chains to compromise several organisations simultaneously. By penetrating a single vendor, hackers are given a back door into thousands of networks.
3. Shadow IT & Unsanctioned Tools
Using unsanctioned apps and cloud tools creates vulnerabilities, often without added scrutiny from security teams. “Shadow IT” examples make it more difficult for security teams to monitor and protect sensitive information.
4. Quantum and Future Threats
Quantum computing threatens traditional encryption methods. Once quantum computing becomes mainstream, then organizations that are slow to implement quantum-safe cryptography will be at risk.
Every threat has a solution. Let Qualysec help you build a strong defense before it’s too late.
Core Data Security Services in Cybersecurity
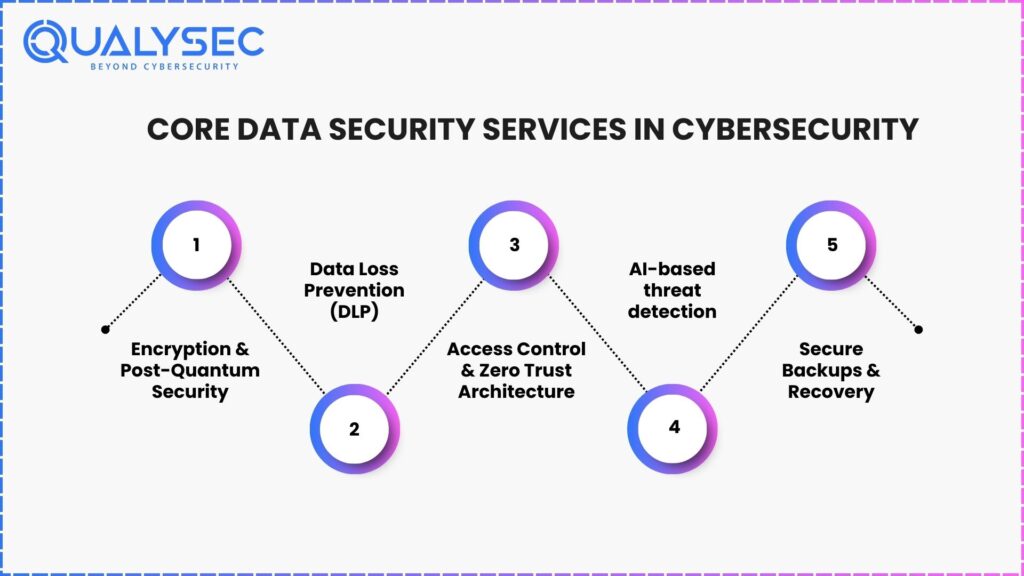
Nowadays, data security is more than installing an antivirus solution. Real security means creating several layers of protection that work together. Precision data protection consists of limiting the threat, detecting and identifying the threat and acting accordingly.
In the context of cybersecurity, limiting the threat means securing data at a data source with strong access controls, utilising AI tools to watch for suspicious behaviours, maintaining regular backups of the data, and limiting access to sensitive data through information security services.
1. Encryption & Post-Quantum Security
Encryption is amongst the most significant tools—it encrypts data for the unauthorised, whether in storage or when shared. By 2025, the majority of businesses will be utilising strong and future-proof encryption capable of withstanding advanced computer attacks.
2. Data Loss Prevention (DLP)
DLP manages the movement of sensitive information. DLP prevents inadvertent leaks of data, prevents unauthorised sharing of data, and helps an organisation comply with Data Protection Regulations.
3. Access Control & Zero Trust Architecture
Zero trust architecture verifies EVERY request to access sensitive or valuable information – regardless of where the data is being accessed. Organisations also take a ‘least privilege’ approach, ensuring users are assigned only the permissions required to access services or assets. The organisation also micro-segments access to applications and deploys production assets with Infrastructure as Code.
Read Also: What is Infrastructure Security Assessment?
4. AI-based threat detection
AI peruses through all network activity all the time, learns normal patterns for each user and device, and detects anything abnormal or harmful. AI can also quickly respond to contain threats.
5. Secure Backups & Recovery
With encrypted backups and an enterprise-level tested recovery plan, you can recover data in just a few minutes, versus hours or days. The faster a recovery occurs, the less business downtime is experienced—helping minimize losses from hacks, crashes, or other unexpected calamities.
Your data is your most valuable asset — allow Qualysec to protect it. Robust security for a rapidly evolving digital world.
Our experts at Qualysec have helped secure fintech, SaaS, and enterprise systems across 25+ countries. Manual + Automated Pentesting. No false positives. Actionable reports.

Advantages of Data Security Services
As cyber threats become more sophisticated, robust data security is no longer optional; it is a necessity.
These services not only protect systems and data, but they may also minimise risks, comply with regulations, build customer trust and offer businesses some degree of resilience against potential crises. Understanding these benefits helps organisations develop informed decisions and plan for long-term security scenarios with the support of data breach prevention services.
1. Improved Protection from Attacks
Multiple layers of security (data locking, AI threat detection, strict access control) make it exceedingly more difficult for hackers to infiltrate a business. If one security measure is compromised, the others are all in place to prevent any sensitive information from being compromised.
2. Increased Compliance
Data security services help keep organisations in compliance with regulations and laws, such as HIPAA or GDPR, by providing consistent monitoring, reports on deficiencies and controls to help avoid costly fines. By keeping these compliance processes in place, organisations are audit-ready and have things under control.
3. Intelligent Risk Management
With current capabilities, organizations can see threats when they happen, quickly solve weaknesses, and have plans in place to recover wherever possible. This means less disruption and damage when things go bad.
4. Prepared for the Future
The right tools can mitigate today’s vulnerabilities and tomorrow’s unknowns. With stronger future-proof encryption and AI monitoring, organizations are safe no matter the next threat.
Learn how penetration testing testing helps to secure your data from online threats. Download a real sample penetration testing report.
Latest Penetration Testing Report

How Qualysec Can Help?
At Qualysec, we offer a full suite of data security services to help mitigate threats to sensitive information from some of today’s most sophisticated cyber threats. Our services include post-quantum-ready encryption, AI-driven threat detection, and Zero Trust controls to only allow access to the right people and the right data.
We also offer secure backup and recovery planning so your business can recover quickly after an incident. Most importantly, we have an experienced team oriented to help organisations comply with regulations and ultimately improve overall security.
Whether you’re trying to prevent a breach or simply preparing for the future, Qualysec has the expertise and resources to keep your data secure.
Protect your data before hackers strike — partner with Qualysec today. Secure, compliant, and future-ready protection starts here.
Conclusion
In 2025’s ever-evolving threat landscape, cybersecurity data protection services are your best chance at defending against ever-changing threats. Whether it’s AI-driven detection, quantum-ready encryption, or strong recovery, security data protection centres on your most valuable digital assets. Are you ready to kick your data protection into gear? Let’s move toward a smarter and safer future today.
Don’t wait for a breach to happen — get Qualysec on your side. We stop threats before they become disasters. Talk to Our Experts.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
FAQ’s
1. What are data security services within cybersecurity?
Data security services are specific technologies and methodologies within cybersecurity that defend critical data from unauthorized access, loss, or theft.
Encryption, access control, detection of threats, and secure backup of information are just a few of the aspects of data security services that protect data from breaches, even when it is in use.
2. How are data security services effective in preventing cyberattacks?
They identify or deny suspicious activity through AI-driven monitoring, insight and trends for anomalous behaviour profiling, IDS/IPS, and Zero Trust configuration.
Each of these services can identify malicious activity, mitigate risk and lower the probability of successfully acting on the malicious intent.
3. What types of companies are the best candidates for data security services?
Any company that stores or interacts with sensitive customer data, customer financial information, or provides proprietary data should invest in data storage services.
Companies within the healthcare sector, financial institutions, e-commerce companies that hold credit card details and government agencies are likely to be the most at risk or have the highest regulatory standards.
4. What is the distinction between cloud data security and on-premise security?
Cloud security is concerned with keeping data safe when it’s stored or processed online. In general, the ownership and responsibility for security rest with both the company and the cloud provider.
On-premise security is completely customer-owned and customer-managed when the organization owns and operates an asset.
5. What best practices should companies follow to protect data?
Companies should lock their data with strong encryption, control access to data, audit security policies, and train staff on how to use and be responsible with data.
Two important tools for protecting data include a Zero Trust strategy (where no one is trusted as a default) and ensuring regular backups.
Have any questions? Feel free to ask now—our cybersecurity experts are here to help.

























































































































































































































































































































































































































































































































































































































0 Comments