Cloud computing is being quickly adopted by businesses globally, particularly in India, where agility, scalability, and Digital Transformation are strong business drivers. Although Cloud technology offers businesses unique opportunities, its implementation generally introduces substantial business risks that require sound processes and controls including cloud risk management to manage those risks effectively.
Cloud technology also introduces new areas of complexity and creates a wider gap between the level of visibility into business processes and the actual protection of your data, applications, and IT infrastructure if they are not properly managed.
Businesses, both in India and the rest of the world, are starting to realize that they need to develop a Cloud Risk Management strategy. That’s why it’s important to know what Cloud Computing Risk Frameworks, Cloud Risk Assessment Tools, and Cloud Risk Management Best Practices can bring to bear on those risks across all of your Cloud platforms (AWS, Azure, Google Cloud, and Private Cloud).
In this blog, we are going to explore the significance of cloud risk management and the best practices of multi-cloud.
Introduction to Cloud Risk Management
Business establishments all over India and other places are rapidly adopting cloud computing during this digital era to enhance agility, scalability, and corporate transformation. Migration to the cloud, however, particularly in a multi-cloud setup, harbors several security threats in cloud computing that demand stringent risk management plans.
Cloud technologies also come with complexity, visibility gaps, and potential vulnerabilities when not managed accordingly. The importance of cloud risk management is that multiple cloud systems, such as AWS, Azure, Google Cloud, and even private clouds, are utilized to store data, applications, and infrastructure.
It is particularly relevant to the context of the Indian digital economy and compliance since it is a comprehensive guide to Cloud Safety threats, Cloud vulnerability risk management, risk structures, risk assessment tools, and best practices tailored to manage risk effectively in the context of a multi-cloud setup.
Key Challenges and Cloud Security Risks in Multi-Cloud

Multi-cloud environments are those in which companies are consuming the services of many cloud providers, which provides flexibility and reduces the lock-in offered by vendors. These have specific security issues, including:
1. Increased Attack Surface
More possible entry points for hackers result from several cloud services, therefore demanding more extensive surveillance and sophisticated defenses.
2. Configurations and Visibility Gaps
Misconfigurations are among the top causes of cloud breaches; every provider has unique security settings, so coordinated configuration management is challenging without centralised solutions.
3. Identity and Access Management Risks
Poor or erratic identification controls on clouds can result in unlawful access or abuse of privileges.
4. Compliance and Legal Challenges
Different clouds might work in areas with different compliance needs, including India’s data localisation directives or GDPR.
5. Shared Responsibility Misunderstandings
Though most cloud data security and access restrictions fall under the client’s responsibility, cloud providers ensure the infrastructure, a major source of ambiguity that can expose flaws.
Together, these and other issues constitute fundamental Cloud Security Risks that businesses have to continuously evaluate and manage.
Protect your cloud infrastructure with Qualysec’s expert-driven cloud risk management solutions. Get a comprehensive risk assessment tailored to your multi-cloud environment and stay ahead of emerging threats.
Cloud Risk Management Frameworks
Effective security risks in cloud computing backbone is a systematic approach that offers reproducible procedures and best practices across multi-cloud settings.
1. NIST Cybersecurity Framework (CSF)
Organisations may use this risk-based approach to identify, protect, detect, react, and recover from threats. Its great flexibility and worldwide acceptance in cloud security make it very appealing.
2. ISO/IEC 27001 & ISO Cloud Extensions
Tailor ISO 27001 to include cloud controls; it will also assist in comprehensively managing risk.
3. Cloud Security Alliance’s Cloud Controls Matrix (CCM)
Built especially for cloud settings, CCM maps controls across important areas including governance, data protection, and access management—perfect for multi-cloud risk assessments.
4. CIS Benchmarks
Vendor-agnostic security standards for hardening configurations across cloud systems minimize vulnerabilities and errors in settings.
These systems are essential parts of any cloud-based risk management plan since they help to match corporate risk appetite with compliance needs and cloud activities.
Critical Best Practices for Managing Cloud Risk
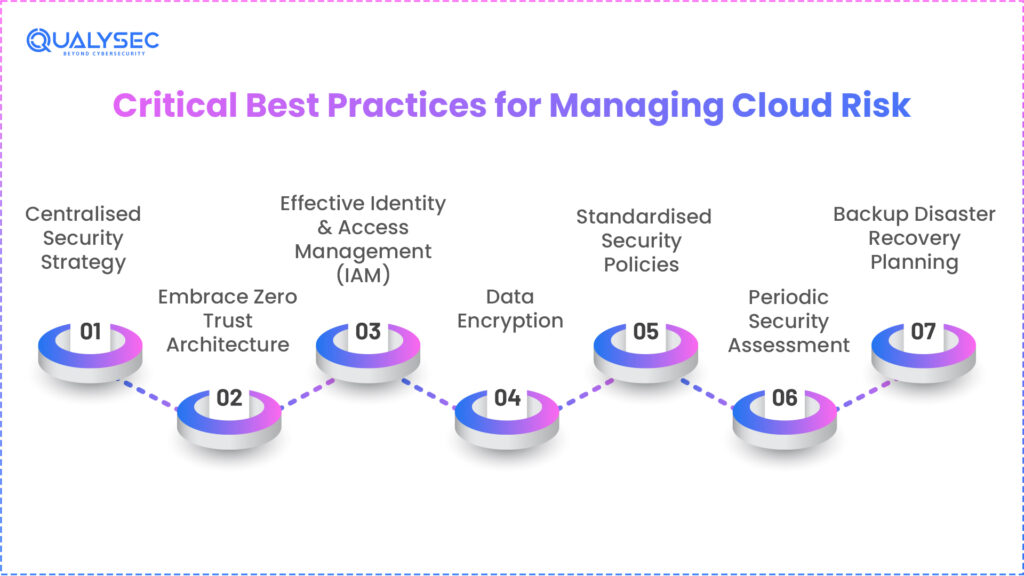
Practical tips to improve your cloud security posture follow:
1. Centralised Security Strategy
to maintain visibility across every cloud, apply centralized software and management tools, such as CSPM (Cloud Security Posture Management), SIEM (Security Information and Event Management), and SOAR (Security Orchestration, Automation and Response).
2. Embrace Zero Trust Architecture
Zero trust implies that there should be continuous policy assessment before accessing any services and an implied suspicion towards all users or devices, including those internal to the company.
3. Effective Identity & Access Management (IAM)
It should use least-privilege access, multi-factor authentication (MFA), role-based access control (RBAC), and identity Federation between cloud accounts.
4. Data Encryption
To prevent the exposure or exfiltration of sensitive data to unauthorized parties, it is necessary to encrypt data both at rest and in transit.
5. Standardised Security Policies
To ensure consistent configurations, utilize unified policies and Infrastructure as Code (IaC) templates, hence lowering human errors throughout clouds.
6. Periodic Security Assessment
Regular Cloud Security Risk Assessments (such as penetration tests, compliance audits, and vulnerability scans) may expose the gaps at a tender age.
7. Backup Disaster Recovery Planning
Ensure business continuity in case of outages: This can be ensured by ensuring that robust data backups and disaster recovery plans are accessible in all cloud environments.
Qualysec assists in the management of cloud risks, whether it is through continuous monitoring or high penetration testing.
From continuous monitoring to advanced penetration testing, Qualysec helps you manage cloud risks effectively. Contact Qualysec today to secure your multi-cloud environment with confidence.
Cloud Vulnerability Management & Cloud Security Tools
In dynamic multi-cloud situations, Cloud Vulnerability Management is the active process of finding, prioritizing, and fixing flaws in cloud systems—very important. Below are the key cloud security tools:
- Automatic posture management across clouds (used to find misconfigurations).
- Cloud Workload Protection Platforms (CWPP) protect containers and workloads, including any Policy Enforcement between Cloud Services and Users by means of a Cloud Access Security Broker (CASB).
- Solutions such as Security Information and Event Management (SIEM) and Extended Detection and Response (XDR) support centralized detection of Threats and Response Across Clouds.
- Automated Vulnerability Scanners identify Compliance Gaps, Errors, and Vulnerabilities.
The best combination of options will differ based on an organization’s specific concerns about Security, the Cloud Platforms it utilizes, and the needs of the organization.
Building a Cloud Security Assessment Checklist
Organisations should keep a Cloud Security Assessment Checklist with items to operationalise cloud risk management:
- Asset inventory and categorization
- MFA enforcement and IAM policy revision
- Authentication of Encryption
- API security and ethical coding guidelines
- Regular log and alert monitoring
- Incident reaction preparedness
- Compliance mapping to frameworks: ISO27001, NIST, etc.
- Regular security assessments and penetration tests
This checklist assists teams in formally establishing proactive closing of security gaps, testing, and remediation processes.
Steps to Implement Effective Cloud Risk Management
The following is an action plan:
1. Scope and Objectives of Your Cloud Risk Management Plan.
To begin with, determine resources, workloads, data sensitivity, and business impact of your Cloud Risk Management Plan. Clearly document ownership of the assets/resources, Compliance Requirement/ Acceptable Levels of Risk of each asset/resource, and how they are relevant to the business objective.
2. Assess the Risk
After identifying your assets/resources, it is necessary to undertake a systematic Risk Assessment to find out the threats to, vulnerabilities in, and potential harm to your Cloud Assets/Resources. Determine the impact of Misconfigurations, Access to Assets and Third-Party Dependencies on the security of your Cloud Assets/Resources.
3. Determine the right framework for your Cloud Risk Management Plan.
Choose the right framework (e.g., CSA CCM, NIST, ISO 27001) that could be utilized as a guide in the formulation of your Risk Management Plan. An established cloud risk management framework will assist in standardizing your Risk Management Controls and give uniformity to several Cloud Providers.
4. Introduce Security Controls
Apply Security Controls through IAM, Encryption, Network Segmentation, and Continuous Monitoring. If possible, automate all the Security Controls to remove human error and enhance efficiency.
5. Monitor, Test, and Improve
Run Vulnerability Scanning and Cloud Security Testing periodically to scan the existing environment and determine any vulnerabilities. Adjust Security Controls (as needed) and continue to monitor Cloud Assets/Resources to be in compliance with the Regulatory Agencies and to be prepared in case of any changes in Threats.
Cloud Risk Monitoring and Continuous Testing
Cloud risk is dynamic; regular testing and monitoring are essential:
- Real-time analysis lets you keep an eye on cloud activity and oddities.
- Organize regular penetration testing and vulnerability scans.
- Regular compliance audits and policy amendments should be performed.
Automated testing orchestration keeps teams ahead of quickly changing hazards.
Regulatory and Compliance Considerations (India Focus)
Compliance and regulatory factors within India have an enormous impact on how organizations establish their cybersecurity and risk management programs around the sectors that are subject to high levels of regulation.
These include Banking, Financial Services, Insurance, and Healthcare. In order for organizations to maintain compliance with the rules set forth by the Indian government’s Central Banks (RBI), the Due Process (CERT-In), and the Digital Personal Data Protection Act, they need to adhere to guidelines established by each of these three Authorities.
When organizations align their internal Risk Management practices with these rules, the organization is both legally compliant and can reduce its operational risk while also building trust with both customers and the regulators.
Future Trends in Cloud Cyber Security
In future cloud cybersecurity systems, automation, intelligence, and proactive risk reduction are expected to play a much larger role than they have in the past, given the growing complexity of today’s cloud environment.
One of the greatest advancements would be the use of artificial intelligence and machine learning to detect risks in real-time and provide automatic action to resolve those risks.
Also, the use of predictive analytics for Security Posture Management (SPM) is emerging as a growing trend. This will allow companies to identify vulnerabilities and misconfigurations before they are actually exploited.
The use of DevSecOps at all stages of the software development cycle (CI/CD) will be a growing area of focus. DevSecOps allows companies to incorporate security into their development process rather than add it as an afterthought.
Zero Trust architectures and Microsegmentation are expected to be widely adopted for use across multi-cloud and hybrid cloud environments. This model’s defaults limit access to a specified area of the cloud network and minimize lateral movement within a cloud environment. All of these trends represent a movement toward adaptive, intelligent, and automated methods for Cloud Risk Management.
Conclusion
In multi-cloud systems, cloud risk management is absolutely necessary for securing digital assets, maintaining consumer trust, and adhering to changing rules; it is no longer voluntary. Using established frameworks, including robust IAM, encryption, continuous monitoring, Cloud Security Tools, and testing techniques, will help companies to considerably lower threats while propelling innovation in the cloud.
Partner with Qualysec to identify vulnerabilities, ensure compliance, and implement best practices across all your cloud platforms. Schedule a cloud security consultation and build a resilient multi-cloud strategy.
FAQs
1. What is cloud risk management?
The procedure of identifying, evaluating, and reducing risks that show up in cloud computing systems to safeguard data, apps, and infrastructure is known as cloud risk management.
2. Why is cloud risk management important?
It enables companies to avoid data leaks, keep compliance, minimise operational interruptions, and protect cloud assets against evolving threats.
3. What are the common risks in cloud computing?
Among the usual risks are data breaches, insecure APIs, unlawful access, misconfigurations, and compliance violations.
4. How do you implement cloud risk management?
By means of defining scope, utilizing risk frameworks, implementing controls (IAM, encryption), continuous monitoring, and periodic security assessments.
5. What are the benefits of cloud risk management?
Enhanced trust, improved security stance, decreased likelihood of breach, operational resilience, regulatory compliance, and better quality of life.
6. Can cloud risk management prevent data breaches?
Effective cloud risk management lowers the risk and repercussions of data leaks by spotting vulnerabilities and implementing protective measures, even if no system is flawless.

























































































































































































































































































































































































































































































































































































































0 Comments