In today’s digital world, protecting our information is not only wise—it’s necessary. Therefore, the solution is data protection services and strong Critical Infrastructure Cybersecurity measures.
Whether it’s a service that protects files with a locked state, provides conditional viewing capabilities to other individuals, minimises the loss of data, etc., these services endeavour to keep information protected before disaster strikes.
We will discuss the potential online disasters that may affect us in 2025, the service features that may provide us peace of mind, the advantages of using the services, and an introduction to Qualysec and how it can help. Let’s get started.
The New Age of Digital Danger
Attackers are a threat to critical services, making Critical Infrastructure Cybersecurity more important than ever. In late 2024 and into 2025, we have counted at least 18 variants, such as Interlock and other high-impact ransomware variants specifically targeting business and critical infrastructure actors.
These actors leverage a fusion of credential theft, remote-access abuse, and software exploits in order to move fast and create maximum disruption. The trend is clear: money-motivated or politically motivated operations both legitimately put essential services at risk.
Weak Links in Critical Infrastructure Cybersecurity
Cyberattacks on critical services occur when vulnerabilities exist in the systems that support those services. Vulnerabilities may come from legacy systems, poor system configurations, or human error, and while they may not be new, moments of vulnerability may present opportunities for potential attackers.
In order to secure the vulnerabilities that impact its operation, we need to determine the types of vulnerabilities, and once we have evaluated the last set of vulnerabilities for security or technology improvement opportunities, we can have our systems operational without the risk of disruptions.
1. Legacy Operational Technology (OT) Systems
Many critical infrastructure providers still have OT systems that were implemented decades ago. These systems were not constructed to withstand modern cybersecurity incidents, and upgrading is often complicated by costs or disruptions inherent in taking operational processes offline. Because many OT systems operate 7 days a week, 24 hours a day, an update or patching is rarely an option, and vulnerabilities become synonymous with the system. Attackers are able to leverage these vulnerabilities to take over a control system or disrupt operations.
2. Inadequate Segmentation of IT and OT Networks
At most organisations, the business (office) network is connected to the networks that run operations for simple convenience. This can be dangerous. If an office employee is deceived by a phishing email, the hackers can then access the operational systems.
There are also big issues if the office computer system becomes infected with a worm or ransomware that quickly spreads from the business systems and into the operational systems that control equipment and processes needed for operation. Therefore, physical cyber separations between business systems and operational systems are very helpful for avoiding bigger cyber disasters.
3. Inadequate credential management and authentication
During discussions with cybersecurity risk and incident management professionals in OT environments, it was astonishing to hear many old-school security practices remain status quo—shared accounts, weak passwords and unconstructive use of multi-factor authentication. And in a much wider criminal fraternity, where organizations poorly manage user accounts, attackers can easily steal or guess credentials; once inside the network, elevate privileges, disable relevant security tools or gain control of mission-critical IT or OT systems without immediate alarm.
4. Lag Time on Patching and Vulnerable Supply Chains
Time can become a real problem when patches need to applied to operationally critical systems, where time frames for patch implementations can take weeks and sometimes months. Exploiters will have time to take advantage of any known vulnerabilities because a significant lag can definitely be used to an attacker’s advantage. Vulnerabilities in the supply chain, such as malware that vendors or software updates directly introduce into operationally critical systems, compound the problem.
5. Risks and Mistakes from Inside
When people have access, you never know if something can happen. Employees, contractors, and partners can present problems without intention and even be malicious. For instance, an employee who may not have been trained well clicks on a bad link from an email, connects a bad USB, or changes a security setting and allows risk to spread. On the other side of the coin, an employee with malicious intent wants to damage the systems from the inside out. It is also why trust and training are equal to safety tools.
Stay secure with Qualysec—your trusted partner in Cyber Security Testing.
Top 5 Proven Moves to Outsmart Hackers
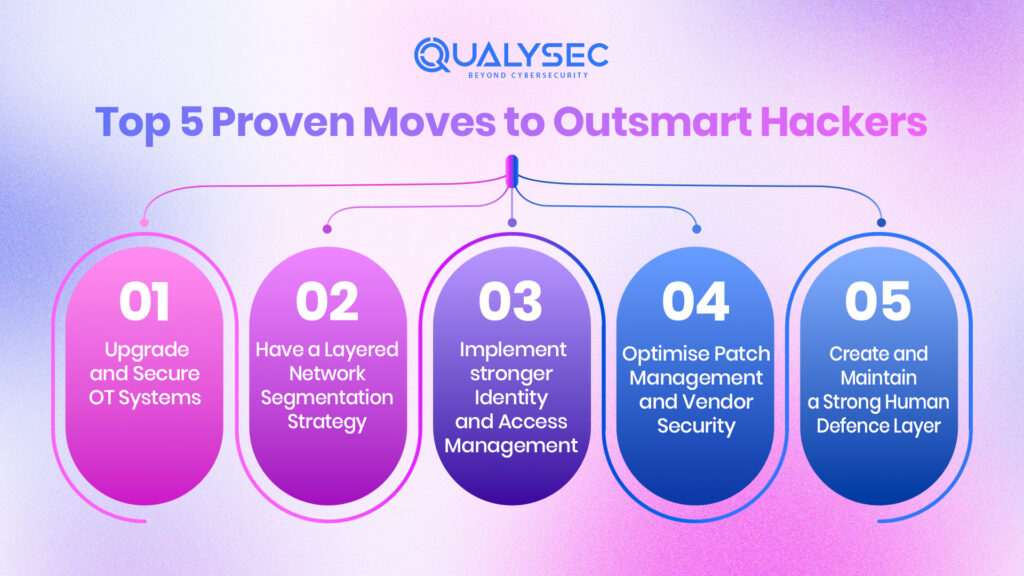
Protecting critical systems requires the right tools, proper policies, and trained personnel. Cybersecurity threats are too fast-changing for a single “set it and forget it” solution—security must be a continuous and adaptable process. By taking an effective, preventative approach, organisations can reduce risk, mitigate threats, or minimise disruptions to critical services.
1. Upgrade and Secure OT Systems
When possible, update old software or hardware components and install protection layers on old systems. Virtual patching tools, intrusion detection systems, and secure gateways can protect OT environments and utilise the ability to add these security layers without adversely affecting availability due to technical downtime. You should carry out regular asset reviews to identify the systems that pose the greatest exposure to the organisation and prioritise upgrades accordingly.
2. Have a Layered Network Segmentation Strategy
Ensure your IT and OT networks are segmented using firewalls, secure gateways, and enforce access policies. This will allow your organisation to limit threats to operational systems from breaches originating in the office IT network. Firewalls and segmentation of critical functions into less connected zones can help limit the potential impact of propagating from a single zone or segment if a breach occurs.
3. Implement stronger Identity and Access Management
Where possible, utilise multifactor authentication – even for on-site users. Assign and enforce role-based permissions over all access-related decision processes so that employees have access to the minimum necessary to do their jobs. Regularly review and remove idle accounts to limit the number of entry points available to attackers.
4. Optimise Patch Management and Vendor Security
Establish and maintain a consistent, fast timeline for completing patch updates, even when short-lived downtime is expected. Utilise testing environments to ensure that patches will not affect business operations, and actively vet suppliers to understand their cybersecurity practices while ensuring the supplier’s update process is secure to reduce the risk of supply chain management.
5. Create and Maintain a Strong Human Defence Layer
Invest time and money to engage employees, contractors, and partners in continual cybersecurity education/training on how to recognise phishing, suspicious activities, and unsafe practices. Along with the training, provide a reporting mechanism to allow the employees to notify any attempted breaches, which allows potential threats to be flagged and documented quickly and take appropriate action. Ending the risk associated with accidental or insider threats
Latest Penetration Testing Report

How can Qualysec help?
Qualysec makes organisations safer and better prepared for online threats. They help protect critical operations from brand-new threats that emerge each day, as well as emerging threats that evolve.
Their team conducts security, system and functional testing, as well as Behaviour and Security Testing of both office systems and operating systems to examine for vulnerabilities. They employ current tested tools, research current knowledge of threats, and examine vulnerabilities faster than a hacker can exploit them. They educate organisations to consider good security, to keep their networks isolated, limit access to those who need it, and update any software.
In addition to testing, Qualysec can continue ongoing assessment support, perform compliance for security regulations, and assist in developing a response plan in preparation for emergencies. Qualysec offers organisations a trusted partner in protecting their work, data and reputation.
Hackers don’t take breaks — neither should your security. Trust Qualysec to guard your operations 24/7. Book a meeting now with cybersecurity professionals today.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Conclusion
Critical infrastructure Cybersecurity is about more than just technology – it’s about risk management that is mission-focused. The threats are real and evolving, but the way forward is straightforward: identify and map your assets; adopt a zero trust model and segmentation for your networks; patch promptly; monitor your systems closely; and exercise your responses with your partners.
By investing now, you will decrease your probability of outages, protect your people, and spend less money in the future. Take security seriously and address it as an operational concern rather than an afterthought.
Don’t wait for a breach to find your weak spots. Partner with Qualysec and stay ahead of cyber threats.























































































































































































































































































































































































































































































































































































































0 Comments