Ensuring cloud-native security has never been more vital than in today’s hybrid workplace with multi-tenant systems and remote access. Organizations seeking strong systems fit for cloud settings have given rise to “ISO 27017 Cloud Security.” A significant standard is ISO/IEC 27017:2015 (or ISO 27017 for short), which provides tips on ISO for cloud security and works seamlessly with other standards, including ISO 27018.
This blog explores the basics of ISO 27017 end-to-end, how it compares (and aligns) to ISO 27018, the certification path for each, and some practical steps to follow in establishing a solid cloud security posture.
Contact a compliance specialist like Qualysec today for help becoming certified or improving your cloud security posture.
What is ISO 27017 and Why Does it Matter for Cloud Security?
The cloud environment introduces unique challenges: multi-tenancy, shared responsibility, automated provisioning, spins up and rips down VMs in minutes. While basic, traditional ISMS frameworks (for example, ISO/IEC 27001) don’t specifically cover a lot of cloud-defined nuances.
ISO 27017 is based on ISO/IEC 27002, “Information technology & Security techniques, which has a code of practice for information security controls in cloud services.” It gives more guidance for pertinent controls from ISO 27002, as well as a group of newly created controls for cloud service providers (CSPs) and cloud service customers (CSCs).
For instance:
- Clarity of shared roles and duties between provider and customer.
- Control of virtual environments in a cloud context (separating and hardening of VMs). Return or removal of assets when the agreement terminates.
Adopting this cloud security standard, ISO 27017, helps define and show a systematic, auditable approach to cloud-specific information security for any company offering cloud services.
Interested in getting started? Talk to Qualysec experts to obtain a roadmap to ISO 27017 certification.
Who Should Implement ISO 27017?
ISO 27017’s relevance is across the spectrum of cloud users and providers, not only for major cloud-native technology companies; here is a breakdown:
1. Cloud Service Providers (CSPs)
ISO 27017 helps you specify the controls you expose to your consumers if you provide cloud services—whether IaaS, PaaS, SaaS; therefore, making your ISO for cloud security offers more credibility. Many well-known cloud platforms now state adherence to ISO 27017.
2. Cloud Service Customers (CSCs)
ISO 27017 gives you a framework to assess and confirm the controls of the cloud provider and so match your internal policies, even if you are a user or customer of cloud security services – for instance, a company transferring workloads to a public cloud.
3. Organisations with Shared Cloud Responsibilities
Organisations that split liability with external providers gain from the clarity and formalized controls ISO 27017 offers, as the cloud challenges conventional constraints, including hardware, network, and data centre.
If cloud-based environments are part of your business and cloud data security is a priority, ISO 27017 certification is a smart investment.
Let Qualysec walk you through your cloud gap assessment and implement controls so you can map your cloud stack to ISO 27017.
Qualysec’s cloud pentest gives you results—no endless emails, no digging through PDFs, no guesswork.

Key Elements and Structure of ISO 27017

Understanding the framework helps you drive a project plan rather than treat ISO 27017 as a checklist. Based on ISO/IEC 27002, several of the baseline control aspects (like access control, cryptography, operations security, and cloud web security) transfer over.
Further, ISO 27017 adds cloud-specific controls (sometimes referenced as seven extra cloud controls):
- Shared responsibility clarification
- Assets returned or removed when the cloud contract terminates
- Virtual machine isolation and hardening
- Watch of cloud services
- Other administrator activities in a cloud context
The standard can be used by all cloud deployment models (public, private, hybrid) and applies to the “provision and use of cloud services” (both CSP and CSC functions).
Usually, implementation includes risk analysis, gap analysis, specifying controls/responsibilities, using cloud-specific procedures, cloud security audit evidence, and ongoing maintenance and monitoring. With a specialised partner such as Qualysec, this lifecycle can be simplified.
Set for cloud-specific security governance? Investigate Qualysec’s ISO 27017 implementation solutions.
ISO 27017 and ISO 27018: How They Compare
A frequently asked question: What differentiates ISO 27017 from ISO 27018? Though they cover different facets of the cloud ecosystem, they are connected.
Broadly on cloud information security measures (for both providers and clients), ISO 27017 concerns the technical and practical security of cloud services.
Operating as processors, ISO 27018 targets specifically the protection of personally identifiable information (PII) in public cloud systems.
| Standard | Focus | Typical Audience |
| ISO 27017 | Cloud security controls (shared roles, virtual computing environment, lifecycle) | CSPs and CSCs are looking for general cloud security assurance |
| ISO 27018 | Cloud privacy controls (PII protection, consent, transparency) | CSPs handling PII in public cloud environments |
Organisations adopting both ISO 27017 and ISO 27018 enhance trust and maturity in handling customer personal data through stronger cloud cyber security practices.
If you are a cloud provider managing client personal data, it is also possible and sometimes useful to apply both. Companies that incorporate cloud security standard ISO 27017 and enhance it with ISO 27018 show a great sign of maturity and trust.
Talk with Qualysec about integrating ISO 27017 + ISO 27018 for full coverage if you are processing PII in the cloud.
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
Achieving ISO 27017 Certification: What to Expect
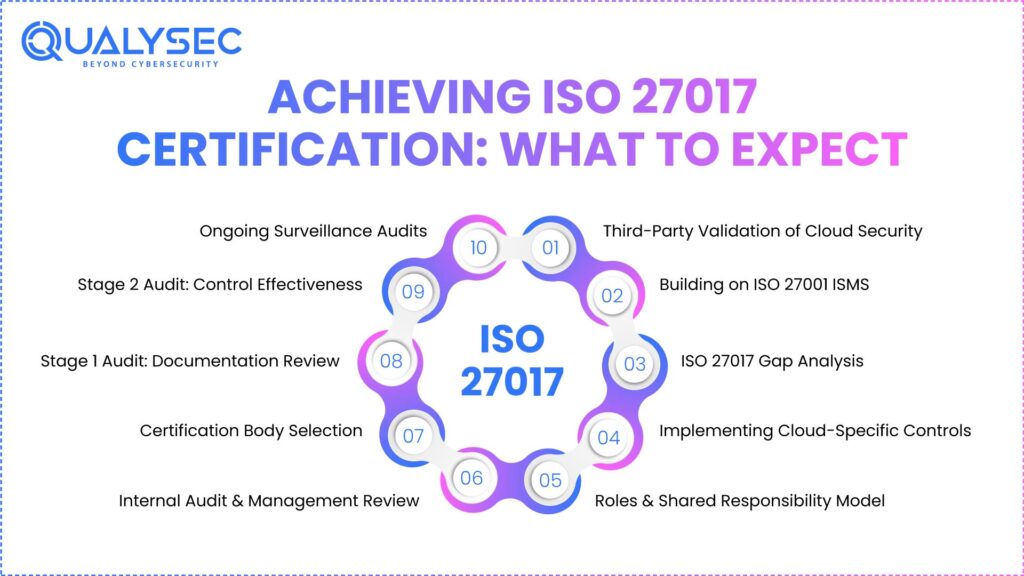
Many cloud-service contracts, customer audits, and tenders now demand proof of cloud-specific standards, even if regulation does not always require ISO 27017 certification. Certification provides third-party confirmation.
Why pursue certification?
- Proves your dedication to cloud security compliance and fosters consumer confidence.
- Supports distinguish your offerings in a challenging environment.
- Enables customers’ contracts, shared responsibilities, and internal processes to match.
Common certification process overview:
- Create or improve your ISMS—usually through ISO 27001 compliance.
- Carry out a gap analysis based on cloud-specific standards ISO 27017.
- Implement or improve controls, write roles/responsibilities (shared model), asset returns, VM hardening, and service monitoring.
- Carry out a vulnerability management analysis and internal audit.
- Select an approved certification organization.
- First stage-1 audit, documentation review; second stage-2 audit: evidence, practical controls.
- Yearly (or per the certifier’s cycle), surveillance audits.
Note: Though it is not legally necessary, certification is viewed by several consumers and regulators as a reliable measure of strong cloud security.
Practical Tips to Implement ISO 27017 in Your Cloud Environment
Organisations starting this trip can find these practical suggestions helpful as part of a strong cloud security strategy:
- Early shared responsibilities on a map: In every cloud contract, specify what the provider does and what stays with the client. ISO 27017 emphasises this.
- Keep a flag-offboard/asset return process: Make sure measures are in place to return or safely erase assets/data upon the termination of your cloud connection.
- Correctly secure the virtual environment: Controls must encompass VMs, containers, snapshots, network segmentation, and host isolation beyond the physical data centre.
- Use monitoring and auditing technologies: Cloud environments are dynamic. Constant monitoring, alerting, and logging with documentation are critical.
- Share other systems: ISO 27017 operates within a certain context. Local data protection regulations, GDPR (if applicable), ISO 27001, and ISO 27018 can all be harmonized.
- Instruct teams: Understand cloud hazards and responsibilities for cloud-operations teams, security, DevOps, and procurement.
- Document everything: Audit trails, configuration baselines, service-level agreements (SLAs) with providers, change logs—these support evidence for certification and compliance.
By acting on controls instead of considering them a checklist, you can go from compliance box-ticking to a strong cloud security profile.
Must Read: Top Cloud Security Vendors for Enhanced Data Protection
Summary
The need for a strong, cloud-specific security architecture cannot be overemphasized as cloud adoption accelerates, especially in India’s expanding digital environment. For companies to improve their cloud security posture, define provider/customer shared responsibilities, virtual environment restrictions, and indicate trust to consumers and authorities. The combination of the ISO 27017 and 27018 offers a comprehensive framework.
Whether as a provider or consumer, aligning with the cloud security standard ISO 27017 is a wise decision if you use any kind of cloud service. If your operations include personal data in the cloud, integrating ISO 27018 with ISO 27017 provides a whole cybersecurity risk assessment framework.
Interested in moving forward? Customized for international best practices, Qualysec can walk you through assessment, ISO penetration testing, implementation, and certification.
Download a Sample Pen Testing Report

FAQ
1. What is ISO 27017 used for?
Both for providers and consumers, ISO 27017 offers guidance and control targeted specifically to cloud services. It clarifies shared roles, protects virtual environments, and guarantees strong cloud-centric control.
2. Who should implement ISO 27017?
It should be considered by any firm involved in heavy cloud consumption (CSC) or cloud service delivery (CSP). Operating or using cloud infrastructure or services will help you.
3. What are the key differences between ISO 27017 and ISO 27018?
Targets cloud security in a broad sense, ISO 27017 offers controls for cloud services. ISO 27018 concentrates especially on protecting personally identifiable information (PII) in public cloud systems.
4. Can penetration testing support ISO 27017 compliance?
Of course. Evidence of controls operating in practice (e.g., VM hardening, segregation, and access controls) can come from penetration testing, vulnerability assessments, and monitoring of cloud infrastructure. These support the operational side of ISO 27017.
5. Is ISO 27017 certification mandatory?
Though many cloud agreements and consumers expect it, ISO 27017 certification is not required by law. It is a best practice framework offering competitive and compliance advantages.

























































































































































































































































































































































































































































































































































































































0 Comments