Did you know 92% of organizations use a multi-cloud strategy as per Flexera’s 2024 State of the Cloud report? The use of multi-clouds is flexible, resilient, and economical. Nevertheless, new risks also accompany it. Misconfigurations, identity sprawl, and compliance issues are usually magnified. Nevertheless, the situation is even more at stake for businesses in Germany and throughout the EU. This places multi cloud security not only as a technical matter, but as a compliance necessity.
In this blog, we will discuss what multi-cloud security is, why it is important, the most common challenges in multi cloud network securit,y and the best practices that enterprises can adopt to ensure that they secure data and remain compliant.
What is Multi-Cloud Security?
Multi-cloud security refers to policies, tools, and practices that safeguard applications, data, and cloud infrastructure on two or more cloud platforms. Multi-cloud is a contrast to hybrid cloud, where security is managed in more than two public or private cloud services.
The main features of multi cloud security are:
- Identity and Access Management (IAM): Making sure that there are uniform user permissions and roles that are secure across the providers.
- Data Protection: Encrypting data at rest and in transit, with enterprise-controlled keys.
- Monitoring and Visibility: Gathering and evaluating security records of every supplier in a common manner.
- Compliance Governance: Ensuring alignment with GDPR, ISO 27001 and industry-specific regulations such as Bafin regulations in Germany.
Why is Multi-Cloud Security Important?
Multi cloud security services are not an option anymore, but a business reality. By diversifying to different providers, organisations are able to maximise their costs, use the best-in-class services, and minimise vendor lock-in.
Have a look at the reasons why multi cloud network security is important.
- Protecting sensitive data. Each provider has unique security models. Without unified controls, data may be exposed through inconsistent access rules or weak encryption settings.
- Ensuring compliance. German and EU businesses should show compliance to GDPR and industry-related requirements. Lack of coherent treatment of security results in a hard time demonstrating compliance during the audits.
- Preserving business continuity. Incorrect settings or intrusions in one cloud can spill to others resulting in downtime, loss of money, and a tarnished reputation.
Discover Your Cloud Security Gaps Today – Assess how secure your multi-cloud environment is and protect your data from cyber threats.
Qualysec’s cloud pentest gives you results—no endless emails, no digging through PDFs, no guesswork.

Challenges of Multi-Cloud Security
Although the advantages of multi-cloud are apparent, the multi cloud security challenges are usually more complicated than the simplicity of single-provider systems.
The most acute multi-cloud security challenges are listed below:
| Challenge | Description | Impact |
| Fragmented visibility | Security logs and alerts live in different dashboards. Blind spots emerge when monitoring is not unified. | Hampers GDPR Article 30 compliance (records of processing and access logs). |
| Configuration drift | Security baselines set in code (Terraform, ARM templates) can be altered manually, creating gaps across environments. | Complicates ISO 27001 evidence collection and weakens audit trust. |
| Cross-cloud attack surface | More APIs, endpoints, and inter-cloud links increase opportunities for attackers to pivot laterally. | Increases the risk of data breaches requiring GDPR breach notification within 72 hours. |
| Usage of too many tools | Businesses adopt multiple CSPM/CIEM/SIEM tools without integration. Overlaps lead to wasted effort and accountability gaps. | Regulators may question governance if security responsibilities are unclear |
| Data transfer & storage | Workloads may run in non-EU regions by default, creating legal risks under Schrems II. | May result in unlawful data transfers and regulatory penalties. |
Start your GDPR compliance journey with a Qualysec security audit.
Multi-Cloud Compliance in Germany/EU
Security and compliance go hand in hand to organisations that conduct business in Germany and the EU region, in general. The most important frameworks and regulations that should be considered with respect to multi cloud compliance are:
- GDPR (General Data Protection Regulations):
- Articles 30 and 32 mandate proper processing, tracking, powerful access control, and encryption of personal data. Multicloud security solutions without centralized logging, or whose IAM is not uniform, soon become non-compliant.
- Schrems II ruling:
In 2020, the EU-US Privacy Shield was declared invalid by the European Court of Justice, and it has complicated the process of cross-border data transfer. Standard Contractual Clauses (SCCs) are required to be used by organisations and providers should be able to demonstrate that they handle EU data lawfully. - ISO/IEC 27001:
A widely adopted standard for information security compliance management. In a multi-cloud context, Annex A controls around access management, logging, and incident response must be consistently applied across all providers. - BaFin and BSI requirements:
German regulators for finance (BaFin) and critical infrastructure (BSI) emphasise traceability, resilience, and incident response. Using multiple cloud providers doesn’t reduce the expectation for unified governance.
You might like to know more about Data Security Compliance: A Step-by-Step Guide
Latest Penetration Testing Report

10 Best Practices to Maintain Multi-Cloud Security Services
Companies need to embrace systematic practices in order to make the operations less complex and avoid multi cloud security challenges.
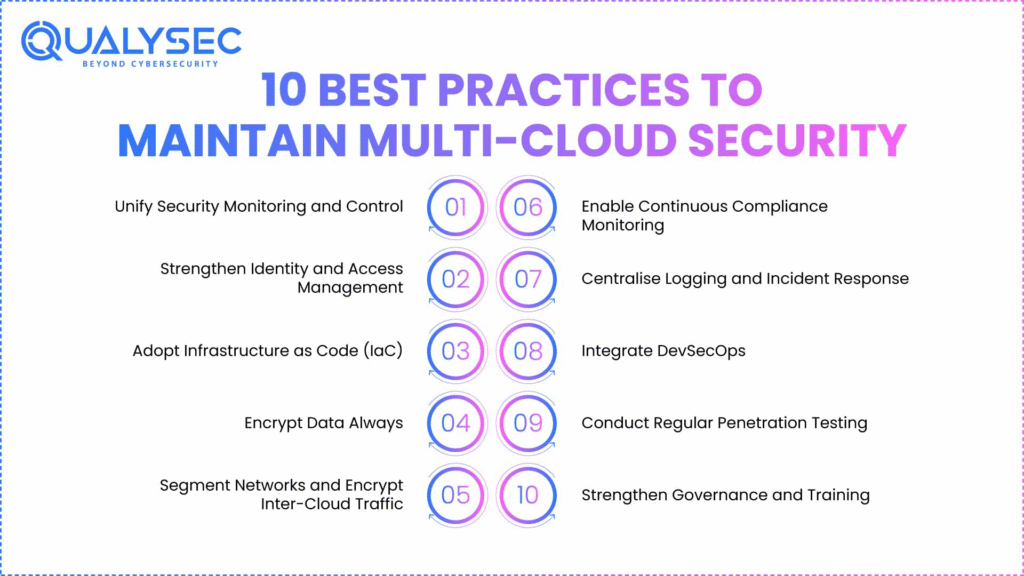
Here are some multi cloud security best practices to follow:
1. Unify Security Monitoring and Control
Multi-cloud visibility is broken when the logs are distributed in AWS CloudTrail, Azure Monitor, and GCP Cloud Logging. The centralisation of a SIEM or SOAR solution groups them and offers a central control centre, making it one of the best multi cloud security best practices.
2. Strengthen Identity and Access Management
The most common cause of cloud breaches is identity. In a multi-cloud environment, roles, groups and service accounts are proliferated quickly. Breaking down SSO with an identity provider, implementing MFA on all privileged accounts, and implementing Cloud Infrastructure Entitlement Management (CIEM) to identify over-permitted users is a sure way to maintain the same control.
3. Adopt Infrastructure as Code (IaC)
In manually configured settings, teams lose their resources to settings that are no longer secure. Organisations can describe infrastructure in code of versions in IaC tools such as Terraform, CloudFormation, or ARM templates. This enhances the consistency and generates auditable gap of ISO 27001 Annex A controls.
4. Encrypt Data Always
You must encrypt information at rest and in transit, and you must keep key management under your control. BYOK or HYOK are the multi cloud security solutions that can guarantee that providers cannot unilaterally access sensitive data.
5. Segment Networks and Encrypt Inter-Cloud Traffic
Lateral movement by attackers is easy since it takes place between clouds that are flat. Workloads need to be divided in terms of environment (production, testing, development) and sensitivity. Data between the clouds is expected to be routed over encrypted VPN tunnels or special interconnects. This is one of the most efficient multi cloud security best practices.
6. Enable Continuous Compliance Monitoring
The cloud is dynamic on a daily basis, and no one can manually review it. Cloud Security Posture Management (CSPM) tools use vulnerable scan settings to identify inappropriate policy settings, whereas Cloud Workload Protection Platforms (CWPP) identify runtime threats.
7. Centralise Logging and Incident Response
Multiple providers usually have a role in security incidents, and piecemeal logs are hard to investigate. The centralisation of logs into a SIEM allows log correlation across AWS, Azure and GCP.
8. Integrate DevSecOps
The developers are issuing code quickly, and multi-cloud setups are increasing the chances of insecure deployments. Integrating security checks into CI/CD pipelines, e.g., the container image scanning, dependency vulnerability testing, and secret detection, are the different ways of spotting issues as soon as possible. .
9. Conduct Regular Penetration Testing
Automated multi cloud security tools point to misconfigurations, but it is a professional pentest that demonstrates how attackers use them when traversing clouds. Penetration testing authenticates IAM regulations, network division, encryption, and monitoring controls.
10. Strengthen Governance and Training
Multi-cloud environments cannot be secured by technology alone. Well defined governance policies minimize shadow IT and accountability loopholes. Individual training of employees regarding compliance roles will help to fulfill the GDPR-related task in terms of daily operations.
Schedule a consultation with Qualysec experts now to secure your multi-cloud environment and stay compliant!
How Qualysec Can Help?
Although the fact remains that the creation of resilience lies in the foundation of best practices and automated tools, it does not imply a guarantee of resilience. Attackers will use the misconfigurations or unmonitored permissions to invade multi cloud security solutions. Here is where penetration testing adds indispensable value.
At Qualysec, we opt for a hybrid approach to penetration testing. Our qualified experts combined manual methods with automated scans to ensure you get compliance-ready reports. We provide detailed reports with proof that controls are tested, validated, and remediated while being aligned with multi cloud security compliance.
Conclusion
Securing a multi-cloud data security environment is not about merely adding more tools. For German and EU enterprises, regulations like GDPR, Schrems II, and ISO 27001 require that companies provide evidence that security controls are not only implemented but proven to work.
The challenges of fragmented visibility, IAM sprawl, and compliance complexity can overwhelm even mature organisations. That is why opting for multi cloud security is not enough. It needs to be tested, and without independent validation, controls remain assumptions.
That’s where Qualysec comes in. With 600+ assessments across 21+ countries, and deep expertise in AWS, Azure, and GCP testing, we help enterprises turn theory into audit-ready evidence.
Book a Multi-Cloud Security Assessment with Qualysec today. Contact us to secure your cloud environment!
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
FAQs
1. What are the top 5 cloud computing security challenges?
The most common challenges are misconfigurations, identity and access management (IAM) complexity, lack of visibility, data residency concerns, and compliance with frameworks such as GDPR.
2. What is multi-cloud challenge?
The major problem in a multi-cloud setup is to have consistent security controls among the providers. Clouds differ in terms of configurations and APIs, thereby complicating them and resulting in high chances of misconfigurations.
3. Which of the following is a common security challenge in multi-cloud environments?
Fragmented visibility is one of the common problems. The providers distribute the logs and alerts, and they find it hard to identify the incidents promptly and to keep the audit trails needed to comply with the requirements.
4. What is multi-cloud security?
Multi-cloud security is the framework of practices, tools, and governance designed to protect applications, workloads, and data across multiple cloud providers. It includes IAM, encryption, monitoring, and compliance alignment to ensure consistent protection and regulatory adherence.
More:
Have questions about multi-cloud security? Chat with our AI Chatbot now for instant guidance and expert answers.























































































































































































































































































































































































































































































































































































































0 Comments