From startups building SaaS platforms to enterprises with serious workloads, cloud adoption has become the “backbone” of the ecosystem. Even though the benefits of using the cloud are endless, it also comes with an undeniable truth. It is indeed one of the most actively targeted areas for cyberattacks. That is exactly why opting for the best Cloud Vulnerability Scanner is extremely advantageous for your business.
Reports in 2025 show that 85% of large Indian enterprises encountered at least one cloud-related security incident in the last year. Although they are often the result of minor problems such as a misconfigured storage bucket or an exposed API endpoint, these errors have a tendency to result in colossal ramifications. Leaks of sensitive data, heavy penalties for non-compliance, and outages can be the final outcomes of the whole process.
This explains the need for a reliable Cloud Vulnerability Management. The presence of so many tools is bound to confuse. To ensure you are well-informed, we have curated a list of reliable cloud vulnerability scanners, how to choose one, and how they work.
What is a cloud vulnerability scanner?
A cloud vulnerability scanner is a tool that automatically checks your cloud infrastructure, apps, and APIs for weaknesses in case of a potential cyberattack.
Cloud scanners are different from traditional network scanners that have their focus on physical servers or endpoints. Instead, they are suitable for dynamic and flexible environments. They check everything from storage and identity settings to exposed APIs and containers.
Cloud based vulnerability scanning is best for finding:
- Misconfigured storage
- Weak IAM policies granting excessive privileges to users or services
- Outdated software components running in virtual machines or containers
- Unsecured APIs or endpoints that reveal sensitive data
Request a free cloud vulnerability assessment today.
Top 5 cloud vulnerability scanners
The presence of too many cloud vulnerability scanners in the market can confuse businesses. One must look carefully to find and use the tools that best suit their needs.
Here is a list of the top 5 cloud vulnerability scanners that businesses can opt for:
1. Qualysec
Qualysec boasts of having one of the best cloud vulnerability scanners. We opt for a hybrid approach – combining automated scanning with manual verification and remediation guidance. Our cloud security testing covers AWS, Azure, and Google Cloud, identifying vulnerabilities in configurations, APIs, containers, and web apps.
What sets Qualysec apart is its consultative delivery. We offer detailed reports, guided fixes, and retesting to confirm remediation. We don’t just leave you with the reports. With operations across 20+ countries and a strong Indian presence, Qualysec bridges the gap between tools and human expertise.
Best for: Businesses seeking both scanning automation and expert-led testing for actionable, verified results.
Features:
- Seamless ulnerability detection
- Prioritized findings report in detail
- Compliance and regulatory support
- Continuous monitoring and retesting
Book your free consultation and start improving your cloud security posture!
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
2. Prisma Cloud by Palo Alto Networks
Prisma Cloud is an enterprise-level platform that combines vulnerability scanning with compliance checks, identity analysis, and runtime security all the way through hybrid environments, containers, and serverless workloads.
Features:
- Code to cloud visibility
- Contextual risk-based prioritization
- Address and remediate vulnerabilities quickly
- Seamless CI/CD integration
3. Wiz
Wiz is the cloud security platform that has been most extensively discussed in the world. It does not use agents; instead, it scans your whole cloud environment by means of read-only API access. With AWS Vulnerability Scanning, it also automatically identifies the assets, finds misconfigurations, vulnerabilities, and identifies the risks connected to the identity on AWS, Azure, and Google Cloud.
Features:
- Unified vulnerability management
- Agentless-first and cross-cloud scanning
- Reduced MTTR
- Risk-based prioritization of vulnerabilities
4. Detectify
Detectify integrates automated web and API scanning with continual vulnerability updates that are based on the findings of ethical hackers. This reliable web application vulnerability scanner emphasizes web exposure, which includes scanning the domains and subdomains that are facing the internet, as well as APIs, for misconfigurations or code flaws.
Features:
- Web application scanning with advanced crawling and fuzzing
- Quick remediation + powerful integrations
- Prioritization of risk findings
- Continuous scanning
5. Tenable Cloud Security
Tenable’s cloud security suite from the makers of Nessus puts the spotlight on exposure management. With vulnerability scanning, they uncover misconfigurations, excessive permissions, and vulnerabilities that already exist in the clouds.
Features:
- Unified visibility for multi-cloud and hybrid resources
- 360-degree risk view
- Quick identification of high-risk attack paths
- Continuous exposure management
How to choose the best cloud vulnerability scanner?
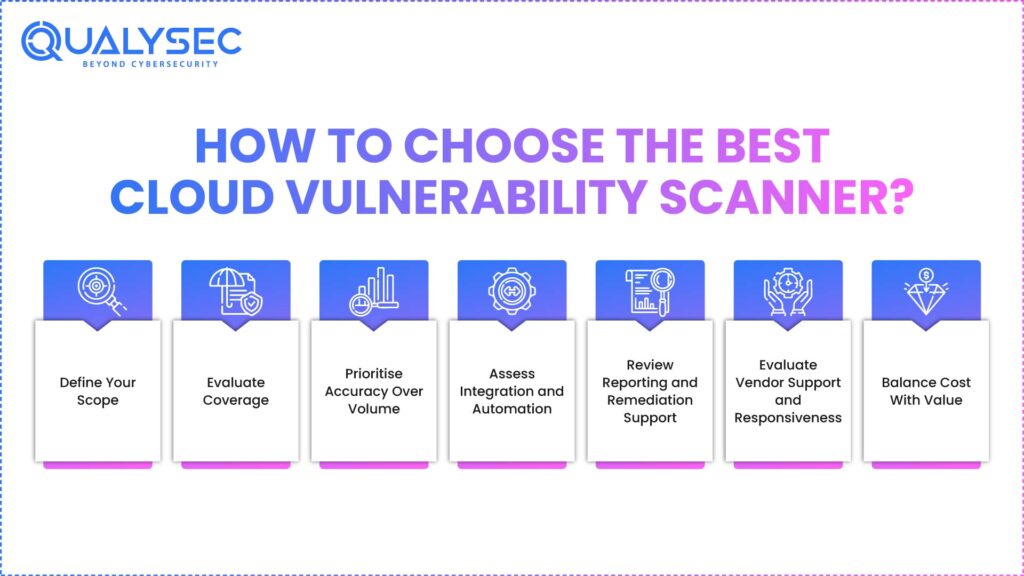
The selection of a cloud vulnerability scanner is not just choosing the most popular one, but rather a combination of your infrastructure, team capabilities, and risk tolerance.
Follow the step-by-step guide below for a successful selection process.
1. Define Your Scope
Initially, describe in detail what you want to protect. It could be cloud infrastructure, web applications, APIs, or containers. A scanner with strong infrastructure analysis capabilities might not even consider API vulnerabilities; hence, being clearer here will save you money or prevent you from having a blind spot.
2. Evaluate Coverage
Try to find the tools that are compatible with your setup:
- Multi-cloud support: Is it AWS, Azure, GCP, or a mixed setup?
- Application coverage: Are there web apps, APIs, and serverless functions?
- Infrastructure checks: Are IAM roles, storage permissions, network exposure, and configurations correct?
3. Prioritise Accuracy Over Volume
The reporting of too many false positives is a source of wastage of time and eventually leads to the development of alert fatigue. Find out if the api vulnerability scanner gives contextual prioritisation (e.g., Wiz or Tenable) or includes manual validation like Qualysec.
4. Assess Integration and Automation
Your scanner should smoothly mix with daily workflows such as CI/CD pipelines, ticketing systems, and dashboards.
5. Review Reporting and Remediation Support
Readable, actionable reports make a big difference. The best Cloud security service explains risks in plain terms and suggests clear fixes.
6. Evaluate Vendor Support and Responsiveness
Time zones and communication play a critical role, particularly for Indian firms collaborating with global partners. Consider whether the provider offers regional support or operates within your working hours.
7. Balance Cost With Value
Price alone shouldn’t drive the decision. Consider the total cost, like subscription, onboarding time, manpower for validation, and follow-up effort. Sometimes a slightly higher subscription pays off in saved engineering hours and verified security.
Cloud vulnerability scanner: How does it work?
Cloud environments are dynamic. New assets are presented every day, permissions are modified, configurations are drifting, and the server room is not even in view. Proper cloud Vulnerability Management is important to monitor these moving parts, as it will inspect your surroundings on an ongoing basis to identify the weak areas.
Here’s how the process typically works:
- Asset Discovery
The scanner first maps your entire cloud footprint. This includes virtual machines, storage buckets, databases, APIs, and containers. It identifies every active resource through cloud provider APIs. - Configuration and Vulnerability Assessment
Once assets are discovered, the scanner analyses their settings and software versions. It compares them against security benchmarks and vulnerability databases. - Risk Prioritisation
Not all vulnerabilities are equally good at finding the right vulnerabilities. Good scanners correlate each issue with its potential impact. - Reporting and Remediation Guidance
These findings are then summarized as a report that prioritizes the vulnerabilities of the highest priority and provides solutions to the same. - Verification and Continuous Monitoring
After the issues are resolved, rescanning is done. Constant monitoring is essential before a small error blows up to be a huge loss.
Conclusion
Selecting the best Cloud Vulnerability Scanners is not just a security issue. It is an enterprise choice that impacts uptime, customer confidence, and adherence. The right tool or partner lets you identify all the hidden dangers in your cloud before attackers strike.
At Qualysec, we combine an automated system with verification of reports and remediation recommendations by experts. With our assistance, you can keep your cloud environment secure and compliant.
Schedule a consultation with Qualysec’s cloud security team today!
Download the Exclusive Pen Testing Report

FAQs
1. What Is a Cloud Vulnerability Scanner?
A cloud vulnerability scanner is a tool that helps to scan your cloud automatically. This will cover servers, storage, APIs, and misconfigured security weaknesses or applications. It constantly recognizes vulnerabilities in security, like open ports, public databases, or poor access controls, and enables them to be rectified before the attackers take advantage of them.
2. How Do Cloud Vulnerability Scanners Work?
They use the method of collecting all your cloud assets and then comparing them to known vulnerability databases and configuration benchmarks through analysis. Each issue is scored by severity, followed by a report that guides remediation. The best scanners also offer continuous monitoring and rescan capabilities after fixes.
3. Why Is Cloud Vulnerability Scanning Important?
Cloud systems never stay the same; they change with code pushes, API updates, and other events that are risk-introducing and can happen quickly. The scanning provides continuous visibility and compliance, keeping businesses from exposing their data and incurring costly breaches.
4. Which Are the Best Cloud Vulnerability Scanners in 2025?
It is impossible to designate just one scanner as the best in 2025. The best cloud vulnerability scanner is the one that is perfectly suited for your business. For example, if you are looking for enterprise-scale environments, Wiz or Orisma Cloud is a good option. However, if proven results and remediation advice are what you need, then the right choice is Qualysec.
5. What Is the Difference Between Cloud Vulnerability Scanning and Penetration Testing?
Vulnerability scanning happens automatically. It points out possible weaknesses. Penetration testing is done manually. In this case, the experts are exploiting those weaknesses actively to determine real-world impact. In reality, both methods are used in conjunction with each other: scanning keeps the risks visible all the time, while pentesting confirms the highest severity risk.
























































































































































































































































































































































































































































































































































































































0 Comments