Key Takeaways
- Active medical device security monitoring is mandatory throughout the lifecycle.
- Proactive vulnerability monitoring MDR must include all SBOM components.
- Regular vulnerability assessment and penetration testing ensure EU MDR PMS cybersecurity.
- Strict timelines govern the reporting of medical device cybersecurity incidents.
- Qualysec provides expert testing to ensure MDR post-market surveillance cybersecurity.
Introduction
Data indicates that medical devices are more prone to cyber attacks. Nearly 77,000 internet-connected devices in the UK alone are vulnerable owing to outdated and misconfigured systems.
Such attacks may threaten patient safety and result in unauthorized access and exploitation of known vulnerabilities. Under EU MDR 2017/745, manufacturers must conduct continuous security monitoring, vulnerability monitoring, and EU MDR post-market surveillance cybersecurity.
A structured Post-Market Surveillance (PMS) system helps identify risks and take corrective action, ensuring compliance and long-term device security.
Is your medical device secure?
No. Outdated, unpatched, or misconfigured systems expose nearly 77,000 internet-connected devices in the UK to cyberattacks. These risks include unauthorized access, vulnerability exploitation, and disruption of clinical functions.
Why is a CE Mark no longer enough for EU MDR cybersecurity?
Previously, the CE mark indicated a device was safe and market-ready. Under EU MDR, this is no longer sufficient.
1. SOTA Requirement
The Cybersecurity State of the Art (SOTA) requirement evolves with new vulnerabilities. Failure to update security invalidates compliance.
2. Shift in Approach
Cybersecurity is now a continuous process. CE marking proves initial safety, while Post-Market Surveillance ensures ongoing protection.
3. Living Technical File
Technical documentation must remain updated with real-world data, making it a “living document.”
EU MDR Requirements for Cybersecurity Monitoring
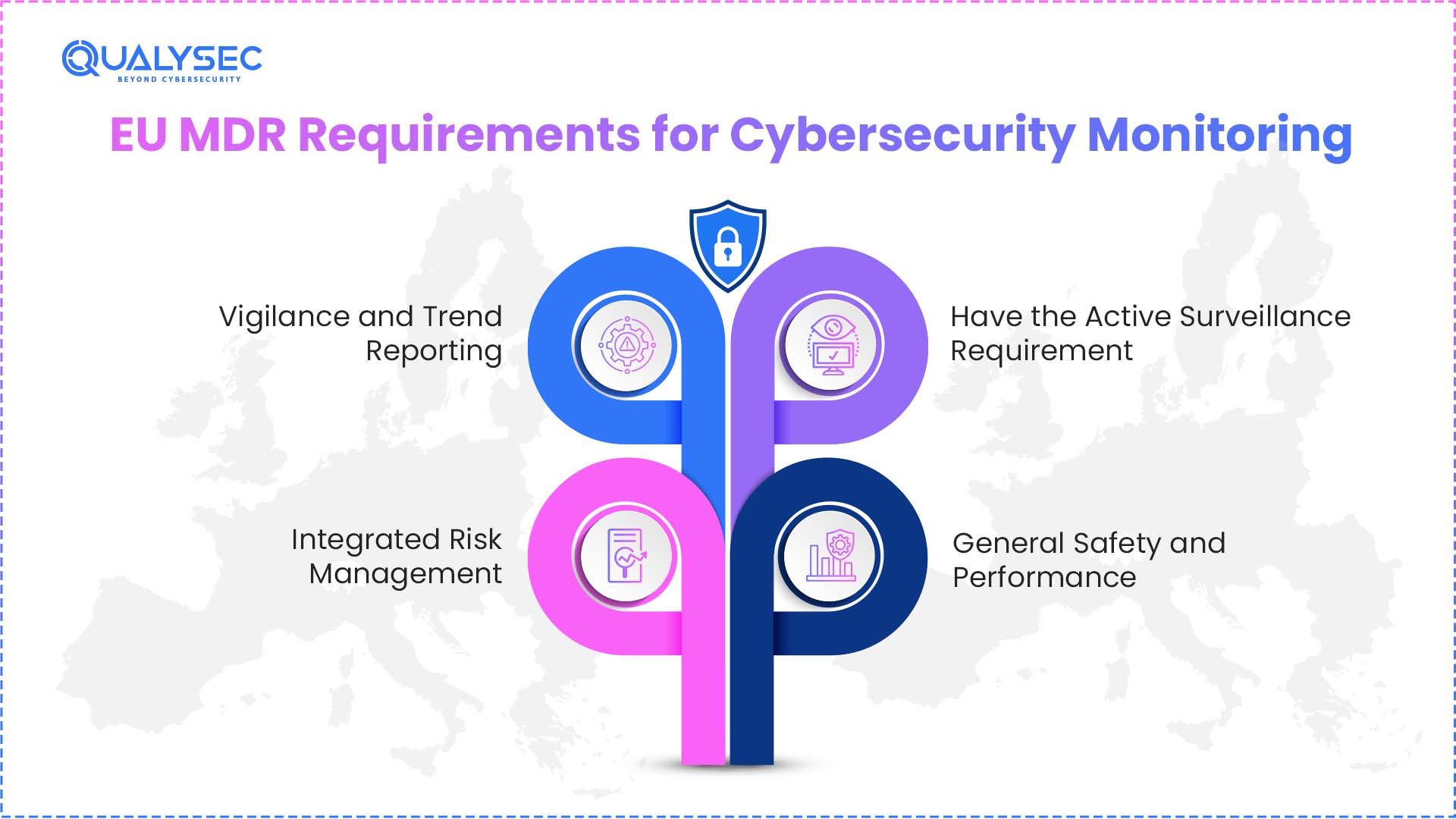
Under EU MDR compliance, cybersecurity monitoring is a continuous and legally mandated process.
1. Active Surveillance Requirement
Article 83 mandates a Post-Market Surveillance system across the device lifecycle. This includes monitoring vulnerabilities, threat intelligence, incidents, and third-party components.
A Coordinated Vulnerability Disclosure (CVD) process must also be implemented.
2. General Safety and Performance
Devices must minimize IT-related risks, including unauthorized access and harmful system interactions.
Annex I – GSPR 17.4 enforces lifecycle-based software risk management and continuous updates.
3. Vigilance and Trend Reporting
Manufacturers must report serious cybersecurity incidents within strict timelines (15 days or 2 days for critical threats).
Trend monitoring requires reporting statistically significant increases in vulnerabilities.
The Periodic Safety Update Report (PSUR) includes analysis of incidents, vulnerabilities, and trends.
4. Integrated Risk Management
Risk management must be continuous throughout the device lifecycle, addressing vulnerabilities, unauthorized access, and exploitation scenarios.
Monitoring threat intelligence and emerging risks is essential, and corrective actions must be taken when needed.
Talk to an expert to build a strong, compliant, and future-ready EU MDR post-market cybersecurity strategy.
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
Role of Post-Market Surveillance in Cybersecurity
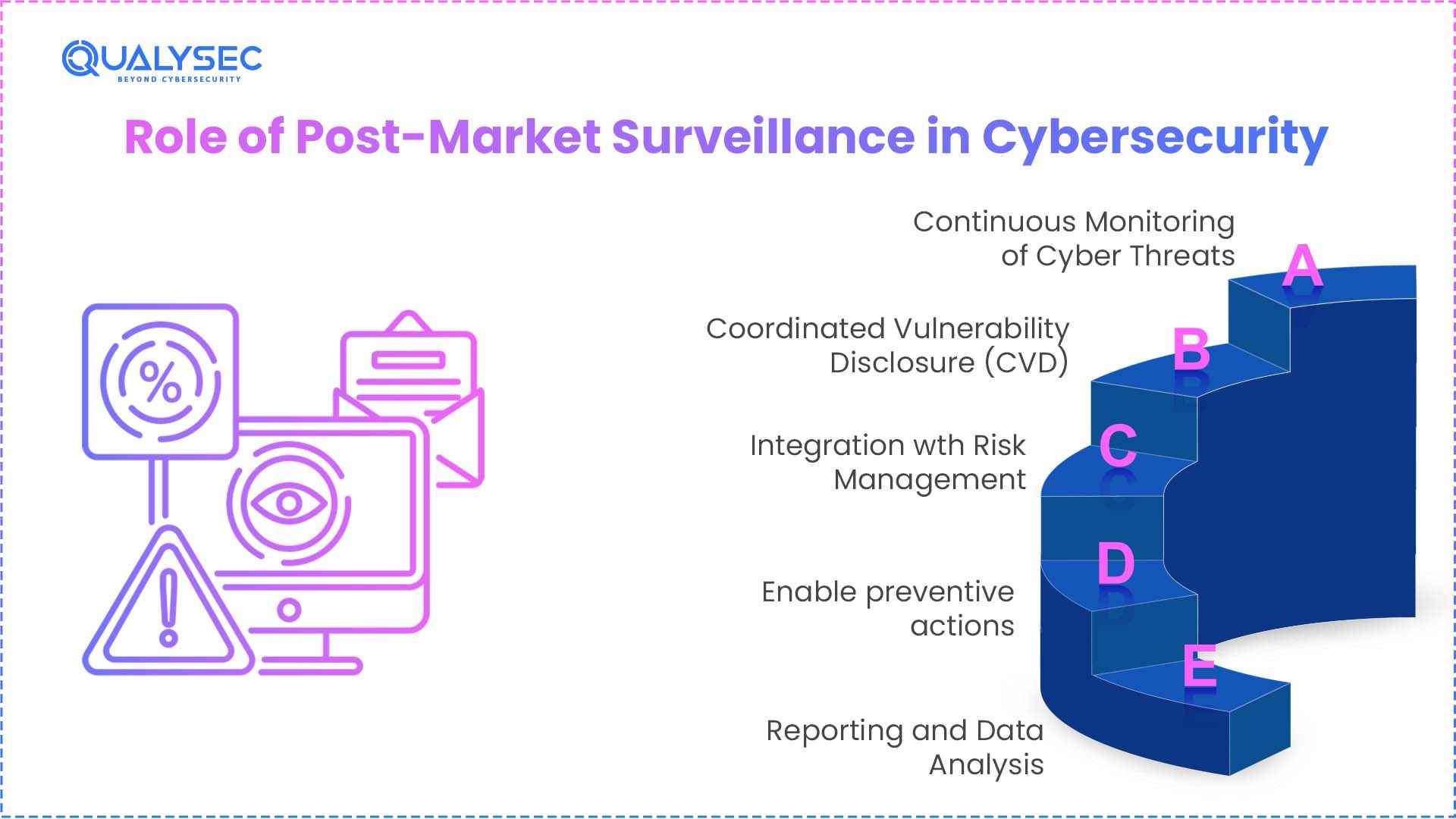
Post-Market Surveillance (PMS) is how manufacturers monitor the real-world performance and safety of their devices once patients and healthcare providers start using them.
The main objectives:
- Ensure clinical safety
- Update technical documentation/risk management
- Detect long-term risks
- Have rapid corrective/preventive actions (CAPA)
PMS requires manufacturers to:
1. Continuous Monitoring of Cyber Threats
Post-Market Surveillance requires continuous monitoring of medical devices for emerging threats, vulnerabilities, and real-world incidents only when they enter the market.
Manufacturers must actively collect and analyze data from sources such as user feedback, threat intelligence, and vulnerability databases. This is achieved through a Software Bill of Materials (SBOM), which allows manufacturers to cross-reference their device components against public vulnerability databases (like CVE).
2. Coordinated Vulnerability Disclosure (CVD)
Coordinated Vulnerability Disclosure (CVD) is a process of reporting and managing vulnerabilities. It is used by researchers, manufacturers, and regulators to protect users and medical devices. Vulnerabilities are reported privately, assessed, fixed, and then disclosed publicly. Under the EU MDR, it is used whenever security issues are identified post-market.
3. Integration wth Risk Management
Newly identified vulnerabilities, attack patterns, or weaknesses must be evaluated and incorporated into the risk management file. It continuous reassessment of the device’s benefit-risk profile.
4. Enable preventive actions
Manufacturers are mandated to implement corrective and preventive actions (CAPA) in response to cybersecurity risks. For this, they need security patches, firmware updates, or configuration changes to mitigate vulnerabilities.
5. Reporting and Data Analysis
Cybersecurity teams must properly report cybersecurity-related data, including vulnerabilities, incidents, and mitigation actions, as follows:
| Required Report | Meaning | Update Frequency |
| Post-Market Surveillance Report (PMSR) | It is a summary of PMS data, conclusions, and corrective actions for Class I devices | When necessary |
| Periodic Safety Update Report (PSUR) | It is a detailed report containing PMS data, benefit-risk evaluation, incidents, and CAPA for Class IIa devices | Update Report (PSUR) At least every 2 years |
| Periodic Safety Update Report (PSUR) | It is a safety and performance report for Class IIb devices | At least annually |
| Periodic Safety Update Report (PSUR) | It is a continuous safety evaluation report for Class III devices | At least annually |
Can your security records pass a Notified Body audit?
Under the EU MDR 2017/745, the Notified Bodies (NBs) are now specifically trained to look for the “digital paper trail” that proves your device remains safe against an evolving threat. During an audit, notified bodies do not ask whether your device is secure. They request documented evidence of your medical device security monitoring and evaluate how you respond to new threats.
The auditor will look into:
- Active vulnerability monitoring: The auditor will look for a systematic vulnerability monitoring MDR process. It should contain evidence that you are monitoring every third-party component (SOUP) listed in your Software Bill of Materials, documenting
- Documentation of medical device cybersecurity incidents: The auditor will look at whether your records prove that cybersecurity incidents are handled with precaution and rigorous efforts.
- Integration of Post-Market Surveillance: EU MDR PMS cybersecurity data must flow into your regulatory reports. It should clearly show how you, as the manufacturer, are tracking the frequency of security threats.
Pro Tip:
Maintain a real-time “Digital Paper Trail” of all scans to prove continuous compliance during unannounced Notified Body audits.
How can Qualysec help
Qualysec is a specialized cybersecurity firm that provides high-end security testing and compliance solutions tailored for the MedTech industry. We help manufacturers navigate the complex EU MDR PMS cybersecurity landscape by providing the technical evidence required for a successful Notified Body audit.
- Continuous Vulnerability Management: Qualysec automated and manual vulnerability monitoring MDR services scan your entire SBOM and SOUP components to identify threats before they compromise patient safety.
- Active Security Surveillance: We deliver the proactive medical device security monitoring and penetration testing required to maintain your “State-of-the-Art” status and Technical File.
- Incident & Vigilance Support: In the event of medical device cybersecurity incidents, we provide the forensic triage and remediation data necessary to meet strict 2-to-15-day regulatory reporting timelines.
- Audit-Ready Reporting: Our documentation directly supports your MDR post-market surveillance cybersecurity requirements, providing the “digital paper trail” needed for your PSUR and PMSR submissions.
Conclusion
In conclusion, medical device security monitoring in the context of EU MDR involves continuous monitoring of vulnerabilities to ensure the safety of medical devices. Vulnerability monitoring MDR is a critical aspect of medical device security, allowing medical device manufacturers to mitigate potential risks. In the event of a medical device cybersecurity threat, medical device manufacturers must adhere to the set guidelines to ensure prompt resolution of the threat. EU MDR post-market surveillance cybersecurity guidelines mandate medical device manufacturers to develop a strong post-market surveillance system to respond to potential security and vulnerability threats. By updating their documentation, medical device manufacturers prove their dedication to keeping their devices secure and compliant.
Explore our case studies to see how we solved EU MDR cybersecurity challenges and achieved compliance.
See How We Helped Businesses Stay Secure

Frequently Asked Questions (FAQs)
1. What cybersecurity monitoring is required after CE approval?
After CE marking, manufacturers need to maintain a post‑market surveillance system that collects, records, and analyses real‑world performance and safety data continuously throughout the device’s life, including vulnerabilities and software security issues.
2. How does MDR address cybersecurity incidents?
You must report serious incidents, including those related to security or IT failures, to the competent authorities under the vigilance and reporting system using EUDAMED, where required, within the prescribed timelines.
3. What is the role of post-market surveillance in cybersecurity?
PMS surveillance ensures that medical devices are safe and protected against cyberattacks and threats once they enter the market.
4. How should vulnerabilities be reported under MDR?
MDR doesn’t define a specific vulnerability reporting protocol; the relevant personnel must capture security-related events that impact device safety/performance in the PMS system and report them via established vigilance channels.
5. How often should security updates be evaluated?
Security and safety data evaluators must continuously evaluate the data through PMS, and they must update periodic reports (PSURs) at least annually for higher-risk devices and every two years for Class IIa.

























































































































































































































































































































































































































































































































































































































0 Comments