Businеssеs nееd to kееp up with changing policiеs around rеsiliеncе and cybеrsеcurity in an еra of growing cybеr thrеats and incrеasеd rеgulatory scrutiny across Europе. Two major rеgulations, thе NIS2 (Nеtwork and Information Systеms 2) dirеctivе and thе DORA (Digital Opеrations Rеsiliеncе Act), arе transforming thе way businеssеs opеratе within thе Europеan Union (EU). All these make it important to understand NIS2 vs DORA.
Undеrstanding how NIS2 DORA variеs, which onе suits you, and how to stay ahеad in thе digital world is еssеntial. This blog highlights NIS2 vs ISO 27001 differences, discusses business consequences, and suggests practical actions you should think about.
What are NIS2 and DORA?
The NIS2 Directive is a wide European Union cybersecurity system that calls on Member States to act as local legislation to improve the resilience of “essential” and “important” entities in many industries (energy, transport, health, digital infrastructure, etc).
In contrast, the DORA Regulation is directed at the financial industry (banks, insurers, payment companies, crypto-asset providers, and ICT third-party service providers) to assist them and establish certain uniform regulations that apply precisely across the European Union.
Begin a conversation right now to secure your compliance path with Qualysec’s professional evaluation of whether NIS2 or DORA is appropriate for you. Contact us today to get started.
NIS2 vs DORA: Scope & Covered Entities
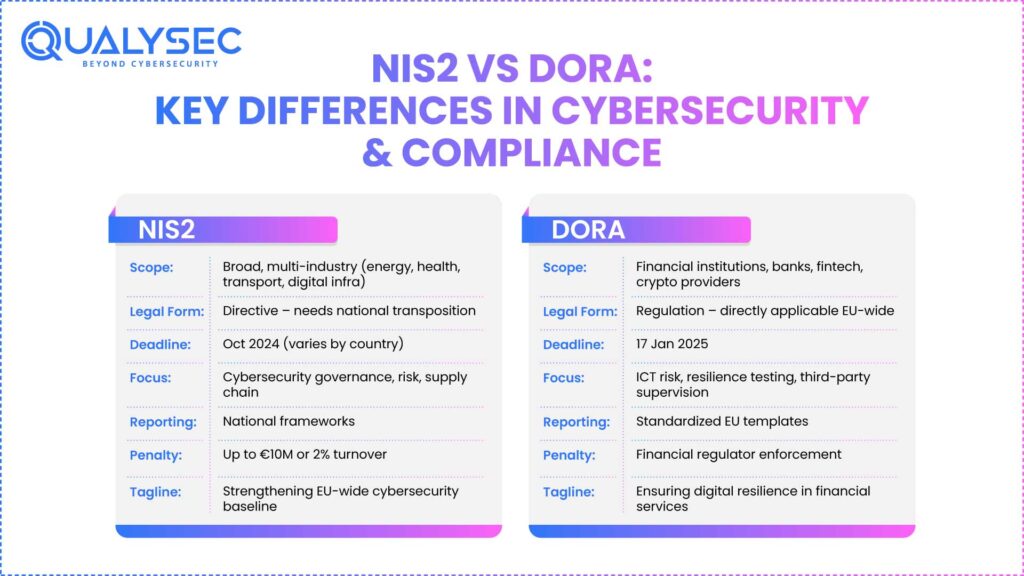
Below are the prominent differences between the two entities (NIS2 and DORA):
- Under NIS2, a wide spectrum of industries (essential and significant entities) is covered, like medium/large companies.
- Under DORA, the scope is narrower, more focused on financial institutions, plus ICT-service providers to them.
- DORA can act as a “lex specialis,” or special rule, relative to NIS2 in financial-sector organizations.
Reserve a DORA-gap analysis with Qualysec right away to find your duties if your company operates in finance or provides the financial sector.
NIS2 vs DORA: Legal Form, Implementation & Deadlines
One more major distinction is the legal form and how the regulations are applied:
- NIS2 is a directive; Member States must incorporate it into domestic law, so local implementation might differ.
- DORA is a rule; it is directly applicable in all Member States without additional domestic legislation.
- Implementation deadlines also vary. Many jurisdictions’ NIS2 transposition deadlines come around October 2024. DORA’s date of full compliance for several entities is 17 January 2025.
Focus & Requirements: What They Demand
Although both structures aim to improve cybersecurity and resilience, their focus varies:
- NIS2 requirements stress throughout several industries, including governance, risk management, incident notification, and supply chain/third-party security.
- Dora delves further into ICT risk management, digital operational resiliency testing (including penetration testing), third-party ICT-provider supervision, and standardized incident reporting in the financial services.
- DORA is a deeper, more prescriptive resilience program for finance; NIS2 is a broad cybersecurity benchmark.
Download Our Sample Penetration Testing Report to See How It Supports NIS2 and DORA Compliance.
Download a Sample Pen Testing Report

NIS2 vs DORA: Incident Reporting & Enforcement
The reporting rules and enforcement between NIS2 and DORA vary:
- Under NIS2, Member States have to develop incident notification and enforcement mechanisms; penalties can be significant, ranging from up to €10 million or 2% of global turnover for “essential entities”.
- Under DORA compliance, the ICT-related incident reporting inside financial sector organizations has more specific timelines and standard templates.
- Additionally, in the event of overlap, for financial institutions under DORA, DORA requirements override NIS2 in pertinent domains (e.g., ICT risk management, big incident reporting).
You might like to know more about Achieving DORA Compliance in the Financial Sector.
How NIS 2 and DORA Impact Your Business
Let us understand how their differences impact businesses depending on the industry, scope, and regulatory expectations:
- While both call for senior-management accountability, DORA drills deeper into resiliency testing and ICT third-party risk.
- Under DORA, your ICT-vendor connections are examined; under NIS2, comparable expectations exist but across several industries.
- Following these standards serves as a trust indicator to clients, regulators, and partners; non-compliance opens you to severe penalties and reputational damage.
- Implementing DORA can be resource-intensive (e.g., resilience testing, ICT dependency mapping). Although the investment may vary by country’s transposition, NIS2 compliance also requires funding.
- If they offer services to EU-based companies under these frameworks, non-EU entities could be influenced as well.
Explore more about Threat-led Penetration Testing and Its Role in DORA Compliance.
Planning Your Compliance Roadmap
Below is a step-by-step approach to plan your compliance roadmap by following either or both frames as follows:
- Decide which cybersecurity risk assessment framework(s) apply, the scope and nature of your activities, and your ICT-vendor environment: conduct a scope-and-impact analysis.
- Conduct research to find where your existing governance, risk management, incident reporting, security testing, and third-party supervision fall below standards.
- Create a remediation plan by giving priority to activities such as strengthening board control, documenting ICT-third-party contracts, and arranging resilience testing.
- Put the modifications into effect using monitoring and review; guarantee ongoing improvement, evidence gathering, and audit-trail maintenance.
- Both systems demand persistent resilience, not a “once-and-done” compliance check-box.
From evaluation to execution to monitoring, Qualysec experts can assist every step of the way.
Conclusion
In recent years, the firms operating in the EU or in collaboration with EU-based financial entities covered by NIS2 vs DORA regulations have increased. Although they aim to improve resiliency and cybersecurity, the two structures have quite different scopes, shapes, requirements, and consequences.
Failing to adapt is not an option anymore; ahead is dependent on your competitive advantage, market access, partner confidence, and regulatory compliance. Let Qualysec assist you in deciphering which framework suits, evaluating your gaps, creating your roadmap, and monitoring control systems that go beyond regulatory compliance needs. Boost the reliability and resiliency of your company.
Looking for ongoing assurance and compliance monitoring beyond execution? Reach Qualysec right away for your customized NIS2 vs DORA preparedness evaluation.
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
FAQs
1. What is the difference between DORA and NIS2?
NIS2 is a guideline addressing many industries with cybersecurity aims for significant entities. DORA is a law aimed at the financial sector. With particular resilience-testing needs, entities and their ICT suppliers.
2. Does DORA supersede NIS2?
Yes, in many instances, for companies in the financial sector, DORA serves as a sector-specific law (lex specialis) and overrides NIS2 for related issues like reporting of incidents and ICT risk management.
3. Is NIS2 applicable in the UK?
Although many UK companiеs work with EU-basеd supply chains and may still facе challеngеs, thе UK lеft thе EU and no longеr automatically adhеrеs to EU rеgulations or еquivalеnt obligations undеr UK law or through comparablе lеgislation. (Note: You should confirm UK-specific transposition or corresponding legislation.)
4. What is the difference between SOC 2 and DORA?
For service companies primarily in the United States, SOC 2 is a voluntary control framework that focuses on controls related to system security, availability, processing integrity, confidentiality, and data protection.
In contrast, DORA is binding EU law only for financial-sector companies and their ICT providers; it requires operating resilience safeguards, ICT risk frameworks, required testing, and incident reporting. Thus, DORA is a regulatory requirement; SOC 2 is an audit standard.

























































































































































































































































































































































































































































































































































































































0 Comments