Key Takeaways
- Technical documentation is a mandatory, living record of device lifecycle compliance.
- GSPR 17.2 requires the implementation of state-of-the-art measures to reduce the risk of unauthorised access.
- Risk management must link every cyber threat directly to patient safety.
- Notified Bodies often expect independent security testing evidence, especially for connected or higher-risk devices.
- Post-market surveillance must include active CVE monitoring and rapid patch protocols.
Introduction
IBM reports that the average healthcare data breach cost reached $10.93 million. A single digital vulnerability, if exploited, can compromise patients’ safety, cause financial loss, delay critical care, or even disrupt the system. To introduce medical devices in the European Union Market, obtaining the CE mark is necessary, which requires compliance with the EU Medical Device Regulation (MDR) 2017/745. Under this regulation, manufacturers must prepare technical documentation (technical file) to show that the medical device meets safety, performance, and cybersecurity requirements. This includes identifying vulnerabilities, assessing associated risks, and implementing appropriate risk control measures throughout the device lifecycle. With a strong focus on EU MDR technical file security to ensure proper documentation, traceability, and protection of cybersecurity evidence. This guide shows the essential medical device Technical File requirements and auditor expectations, providing the strategic clarity needed to secure both regulatory approval and long-term operational integrity.
What is the EU MDR Technical File?
Under the EU Medical Device Regulation 2017/745, the technical file is officially called Technical Documentation. It is a mandatory set of records under Article 10 of the EU MDR to show that the medical device complies with the regulatory requirements of General Safety and Performance Requirements (GSPR). This applies both before and after it is placed on the market. The technical documentation is a live document; it evolves with the product or system. It must be clear, unambiguous, organised, easily readable, and searchable.
What does the Technical File tell:
- What the device is: The device description, intended use, and exact software/hardware specifications.
- How the device was built: Detailed manufacturing information and the “Design and Development” records (including the software architecture).
- Proof it works: Clinical evaluation data and results from “Verification and Validation” testing.
- Proof whether the device is safe: The Risk Management File identifies hazards (like a data breach or system hack) and shows how organisations mitigate them.
- How the device is monitored: The Post-Market Surveillance (PMS) plan explains how the company will track and fix new security vulnerabilities after the device reaches the end users.
Importance of Technical File
- Gateway to sell in the European Market: Without a complete and audited E MDR Technical File, a manufacturer cannot obtain a CE Mark, which means the manufacturer cannot sell or distribute the medical device within the European Union.
- Shows Security by Design: The Technical File shows the evidence to prove that the developers have created the appropriate cybersecurity software in the medical device for protection against unauthorised access.
- Legal Defence: In the case of a data breach or device malfunction, the EU MDR Technical File security is a legal defence to show that the manufacturer followed state-of-the-art safety protocols and identified potential cyber threats.
- Operational Continuity: The Technical File ensures that cybersecurity is not a “one-time fix” but a continuous process in the medical device.
- Maintain Quality Management System (QMS): The Technical File shows that Quality Management System is followed in the system to ensure that every code change and system update is verified, validated, and traceable.
What are the requirements of the EU MDR Technical File Security?
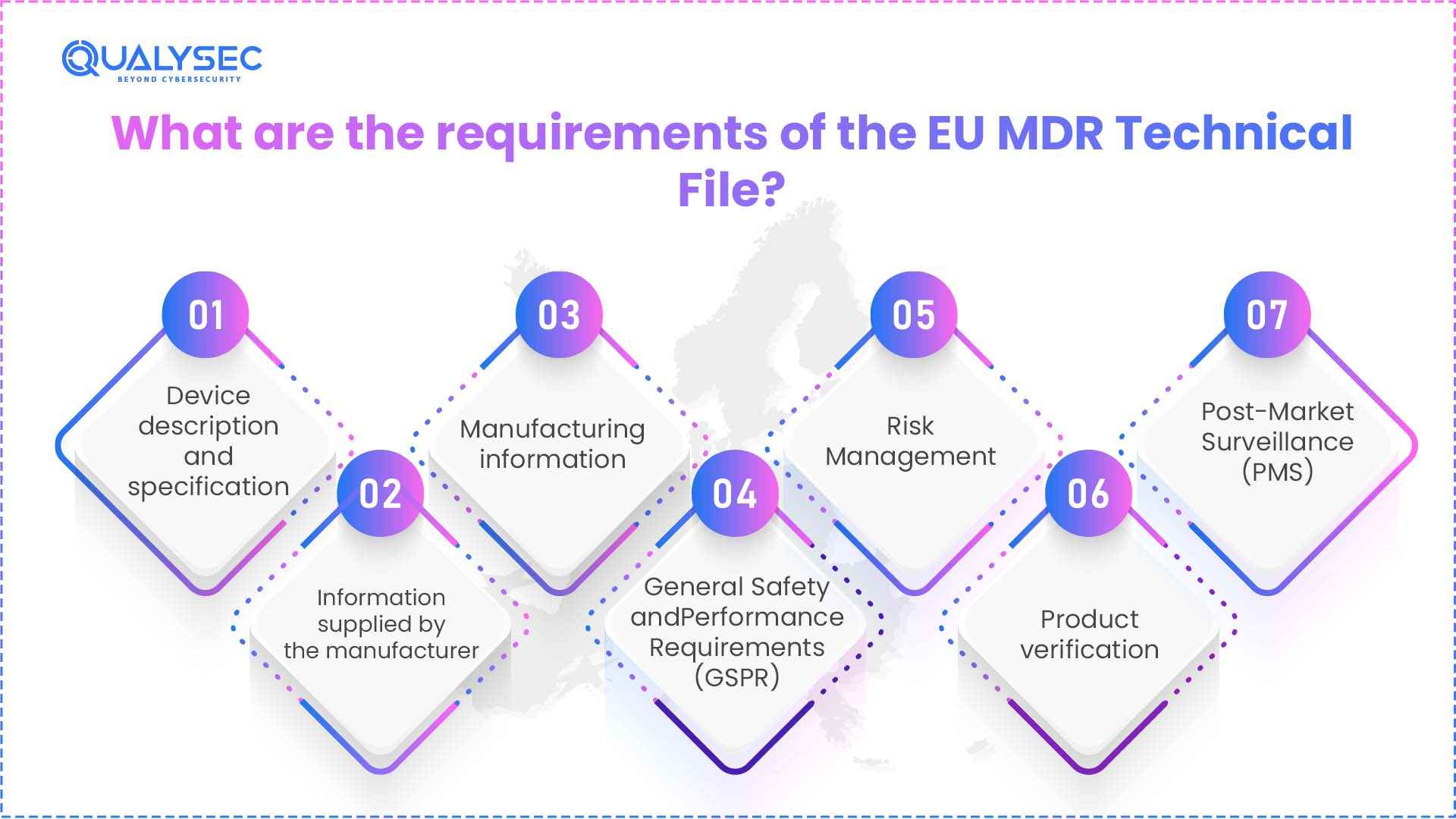
Under the EU Medical Device Regulation (MDR) 2017/745, the regulation mandates manufacturers of medical devices to maintain Technical Documentation, which must include the following:
1. Device description and specification
Clear explanation of the device, its functions, and its intended medical purpose. This includes identifying the target patient group and includes a special identification code (Basic UDI-DI) so the device can be tracked.
2. Information supplied by the manufacturer
Manufacturers include all materials provided to the end-user here, such as final product labels, packaging, and the Instructions for Use (IFU). They must ensure that the IFU is available in the official languages of the EU member states where the device is sold. Furthermore, very clear safety warnings and instructions must align perfectly with the clinical data presented in the file.
3. Manufacturing information
Everything from the entire creation process, from initial design concepts to final production. Including detailed blueprints, schematics, and a description of manufacturing processes or software development.
4. General Safety and Performance Requirements (GSPR)
The GSPR checklist shows how the device meets the safety standards set out in Annex I of the MDR. For digital products, GSPR 17.2 specifically requires evidence of protection against unauthorised access. Every feature of the file must be mapped against the requirements and supported by test results.
5. Risk Management
Any vulnerabilities are identified and mitigated in a Risk Management File, which must now include cybersecurity-specific threats. It includes every possible risk against the clinical benefits provided to patients to prove that the device is “safe by design.”
6. Product verification
It shows that the device is safe and effective. It includes results from laboratory testing, such as electrical safety, biocompatibility, and software stability. For digital products, penetration testing (VAPT) is commonly expected where relevant to demonstrate the effectiveness of security controls. The Clinical Evaluation Report (CER) is also included to provide scientific proof of performance.
7. Post-Market Surveillance (PMS)
As the technical file is a living document, the PMS plan shows the planning for monitoring the device in the real world, including tracking new cyber vulnerabilities (CVEs). Higher-risk devices require a Periodic Safety Update Report (PSUR) to make sure that the device is capable of handling risks over time.
Discover how manufacturers successfully met EU MDR technical file security requirements. Read our case studies.
See How We Helped Businesses Stay Secure

Cybersecurity Evidence in the Technical File
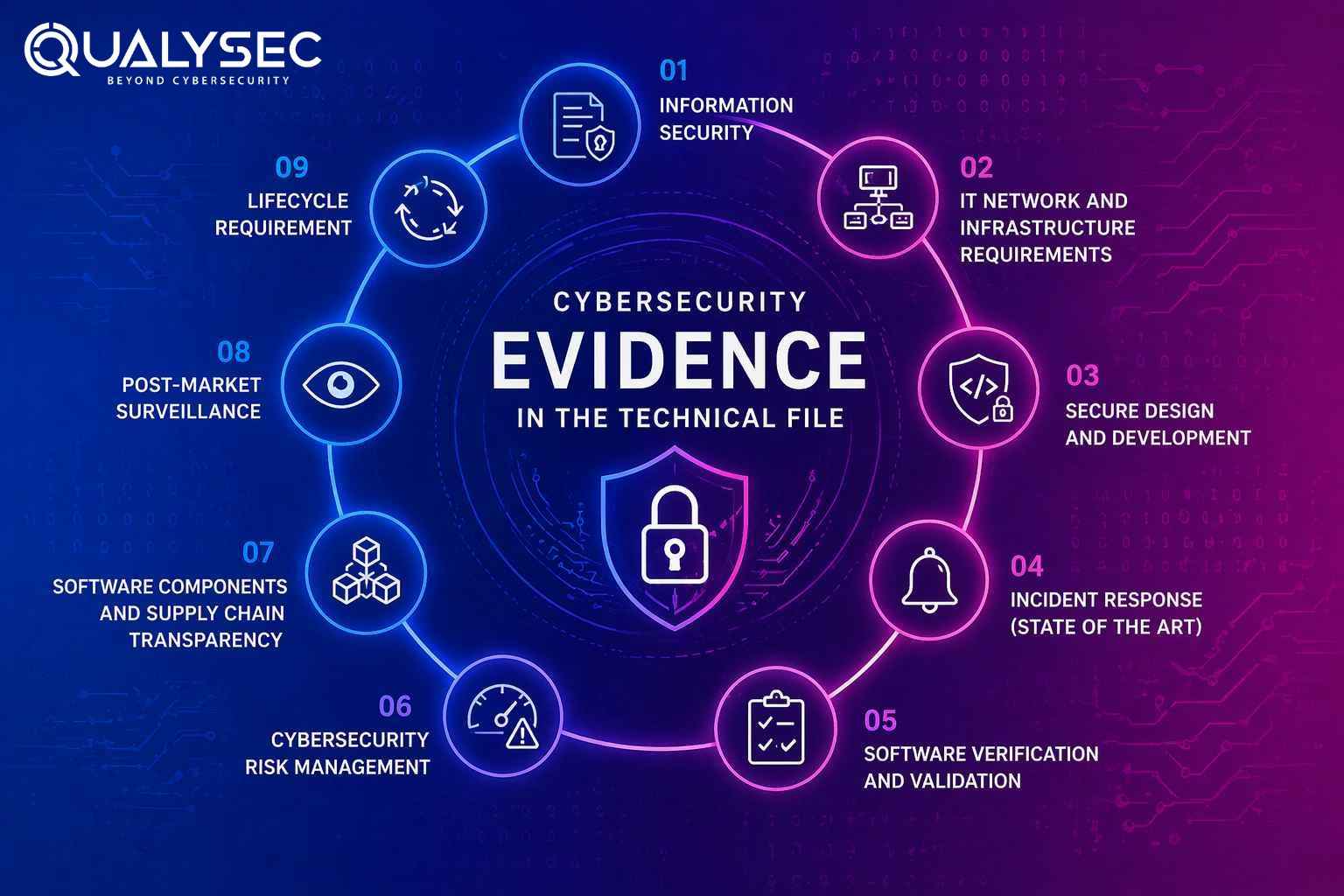
In order to address the cybersecurity requirements of the EU Medical Device Regulation (MDR) 2017/745, manufacturers should demonstrate objective evidence that they design their device with security in mind and manage it throughout its life by ensuring that:
1. Information Security
Providing security against unauthorised access with technical measures including encryption, secure boot, authentication, and access control mechanisms. Protection against tampering or data breach that would invalidate the intended medical use of the device and provide confidentiality, integrity, and data availability.
2. IT Network and Infrastructure Requirements
The Instructions for Use clearly define and communicate the requirements of minimum hardware and IT network needed to operate safely. This includes firewall settings, port restrictions, network segregation, and anti-malware settings to provide a secure deployment environment.
3. Secure Design and Development
Demonstrate that the State of the Art principle is appropriately integrated and that software is being developed according to the principle. Indications of secure coding practices, threat modelling, attack surface reduction, and security-by-design principles must also be provided since the inception stage.
4. Incident Response (State of the Art)
Adopting procedures to determine, report, evaluate, and remediate vulnerabilities, and coordinate disclosure activities. Establish incident response measures to guarantee prompt execution against cybersecurity threats.
5. Software Verification and Validation
Cybersecurity professionals use data from testing, including vulnerability scanning, fuzz testing, penetration testing (VAPT), and software validation. This ensures that implemented security controls are working in line with identified and predictable vulnerabilities.
6. Cybersecurity Risk Management
This is the system of cybersecurity risk management, which involves considering the cybersecurity risks as part of the overall risk management system, in which we identify vulnerabilities continuously. Assess the effects of the vulnerability on patient safety, and implement measures to mitigate risk as much as possible.
7. Software Components and Supply Chain Transparency
Keep comprehensive records of all software components, such as third-party and open-source (usually presented as a Software Bill of Materials (SBOM), to provide information on vulnerability tracking, impact assessment and continuing security measures over the lifecycle.
8. Post-Market Surveillance
Have clear procedures on how to monitor cybersecurity threats and vulnerabilities continuously. It includes security incident analysis and communicating the results to the post-market surveillance system.
9. Lifecycle Requirement
Continuously update and maintain the Technical Documentation with new risks, vulnerabilities, mitigations, and changes to make sure the cybersecurity is an active and continuous process.
Watch Now to See How Medical Device Testing Aligns with EU MDR Requirements.
What do Notified Bodies expect from the manufacturers?
- Clear traceability: Each cyber threat listed in the risk file maps to a specific security control, and the team documents the corresponding test result that confirms the control works.
- Clinical impact explained: Describes how a cybersecurity issue, such as a breach or system compromise, could lead to real patient harm like treatment delays or incorrect dosing.
- State-of-the-art principle justification: Explains why the selected security measures, such as encryption methods, reflect current industry practices instead of outdated approaches.
- Independent VAPT reports: Provides penetration testing results from a qualified third party that is independent of the development team.
- SOUP / third-party software review: Covers risk assessments for any external or open-source software used in the device.
- Machine-readable SBOM: Increasingly expected as best practice, especially in machine-readable formats like CycloneDX or SPDX
- Ongoing vulnerability monitoring: Shows how teams continuously track vulnerabilities using tools and public databases, along with records of that monitoring.
- Defined time to patch: Defined vulnerability handling and remediation processes based on risk
- Coordinated vulnerability disclosure: Includes a link in the technical documentation or company website to a dedicated vulnerability disclosure page, where external security researchers can report issues through a defined and monitored channel.
Pro Tip
Notified Bodies in 2026 are increasingly expecting elements like SBOMs and evidence of active vulnerability monitoring.
How can Qualysec Help in EU MDR Technical File Security?
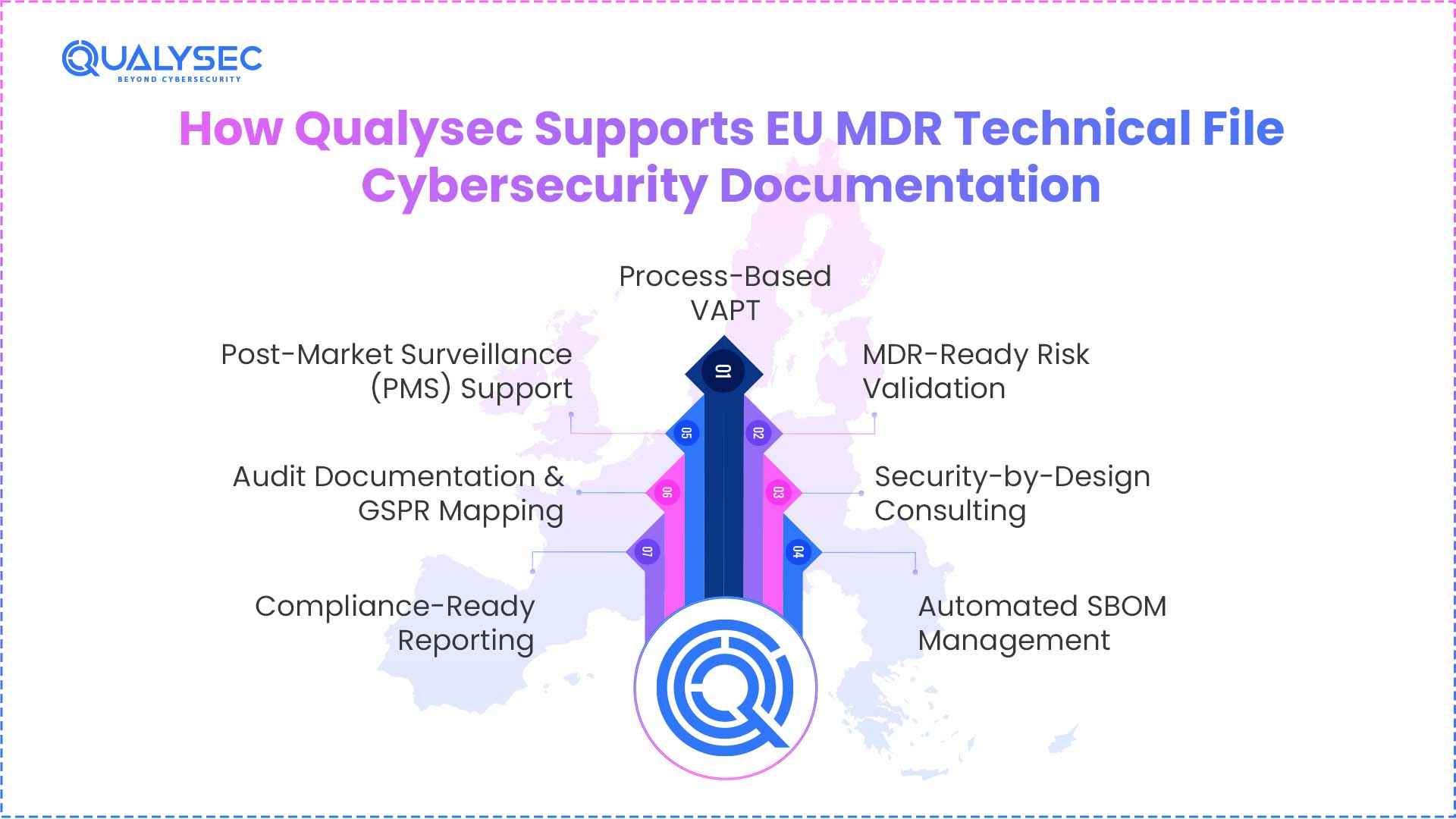
Qualysec is your cybersecurity partner, simplifying the intricate landscape of EU MDR compliance into a seamless, audit-ready technical defence. It goes beyond standard checklists to deliver:
- Process-Based VAPT: Independent, hacker-style testing that delivers the objective verification of the reports in accordance with the EU MDR requirements to make sure all security controls are sound and efficient.
- MDR-Ready Risk Validation: Support with threat modelling and ISO 14971 risk assessments, focusing on how cybersecurity gaps could affect patient safety in real-world use.
- Security-by-Design Consulting: Encryption, secure boot, and access controls throughout the software development lifecycle to meet GSPR 17.2 mandates.
- Automated SBOM Management: Generation of machine-readable Software Bill of Materials (SBOM) to track third-party and open-source dependencies, enabling rapid response to global supply chain vulnerabilities.
- Post-Market Surveillance (PMS) Support: Continuous vulnerability monitoring and CVE tracking services that ensure the Technical File remains a “living document” through the device’s entire lifecycle.
- Audit Documentation & GSPR Mapping: Structural support to align technical evidence with Annex I, II, and III requirements, providing the traceable “thread of evidence” auditors expect.
- Compliance-Ready Reporting: Detailed, high-integrity reports that link technical findings to regulatory requirements, specifically designed to withstand the scrutiny of Notified Body interviews.
Conclusion
Cybersecurity as part of the EU MDR is no longer a choice; manufacturers must treat it as an expectation and integrate it into design, design validation, and post-market activities. MDR technical documentation practices ensure that teams identify risks at earlier stages, control them, and monitor them continuously. In the case of the manufacturers, it is necessary to align the security of CE mark technical files with the MDR Annex II security documentation to show compliance and audit preparedness. Properly developed medical devices’ cybersecurity documentation not only meets EU MDR technical file security requirements but is also created to foster trust among regulators and users. A cybersecurity strategy led by a lifecycle eventually enhances both approval and practical device security.
Talk to our expert to align your EU MDR technical file security with regulatory expectations and business goals.
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
Frequently asked questions (FAQs)
1. What cybersecurity documents are required in the MDR technical file?
Risk management file, software documentation, verification and validation reports, IT environment specifications, post-market surveillance plan, and security-related instructions for use. The evidence needs to align with Annex I, II, and III of the EU MDR regulation.
2. Does the technical file require penetration testing reports?
Annex II (Section 6.1) requires evidence of software verification and validation. When penetration testers use their assessments to show that security controls are working as intended, organisations can include the results in the technical file as supporting evidence.
3. How do manufacturers document cybersecurity controls?
Cybersecurity professionals document controls through risk management (Annex I, Section 3), design and development information (Annex II), and verification and validation records (Annex II, Section 6.1). Controls must be linked to applicable GSPRs, especially those related to software and protection against unauthorised access.
4. What cybersecurity evidence do notified bodies review?
Notified Bodies examine a range of documents to understand how they handle cybersecurity. This list includes risk management files, software documentation, and evidence that the system has been properly tested and validated. They also review post-market surveillance data to see how teams monitor and manage risks over time.
5. How often should technical file security documentation be updated?
The Technical Documentation is a “living document” as per EU MDR. Therefore, teams must keep it up to date at all times. They must make updates whenever something changes, such as design updates, newly identified risks, or findings from post-market activities. They must reflect any change that could affect compliance with the GSPRs in the documentation.

























































































































































































































































































































































































































































































































































































































0 Comments