In an era where vehicles function as connected digital platforms, automotive safety now encompasses both physical crashworthiness and cyber resilience. In this blog, we will examine why automotive security testing counts, how penetration testing (pen-testing) functions for cars, the main problems, and how businesses can get ahead.
Why Automotive Security Matters
Modern automobile systems are more connected, complex, and software-heavy than ever. Deloitte reports that a premium car can have “70 to 100 small computers (Electronic About 100 million lines of software code. With the growing complexity, the call for solid automotive device security to keep vehicle parts, onboard systems, and connected features safe from new cyber threats became a must.
Modern automobiles offer a “large and sophisticated attack surface” during the shift to software-defined vehicles (SDVs), according to Arm Limited. This matters because every new connection, Bluetooth, WiFi, cellular, V2X (vehicle-to-everything), or OTA (over-the-air) update, presents possible vulnerabilities.
Hackers could gain access, elevate privileges, and possibly control or sabotage vehicle systems (brakes, steering, gateway ECUs) by exploiting poorly secured modules or weak gateways. Include the regulatory element. For instance, the standard ISO/SAE 21434, “Road vehicles – Cybersecurity engineering,” was unveiled in 2021 to address such problems.
Discover how Qualysec’s automotive penetration-testing solutions enable your car or part to satisfy cybersecurity needs and guarantee trust.
What Is Penetration Testing for Vehicles?
Often known as pen-testing, penetration testing is the technique whereby real-world threats are simulated under carefully managed conditions to identify flaws before the hacker does. As Deloitte notes, “Penetration testing is considered one of the most efficient techniques to verify if the cybersecurity controls in place” in the automotive context.
Thus, how does it vary for cars?
Testing starts at different tiers: components (ECUs), subsystem networks (CAN, FlexRay, Automotive Ethernet), backend/cloud services, mobile applications, and the general vehicle. The hacker mindset is adopted: looking for misconfigurations, weak authentication, insecure communications, side-channel leaks, insufficient isolation between functions, insecure OTA update paths, etc.
Time is of utmost importance as automobiles are frequently still in development when testing starts; Qualysec emphasises the need to include pen-testing early in the development process.
Set up a consultation with Qualysec to create and apply a penetration-testing plan customised to your ECU/subsystem architecture.
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
How Penetration Testing Helps Keep Vehicles Safe
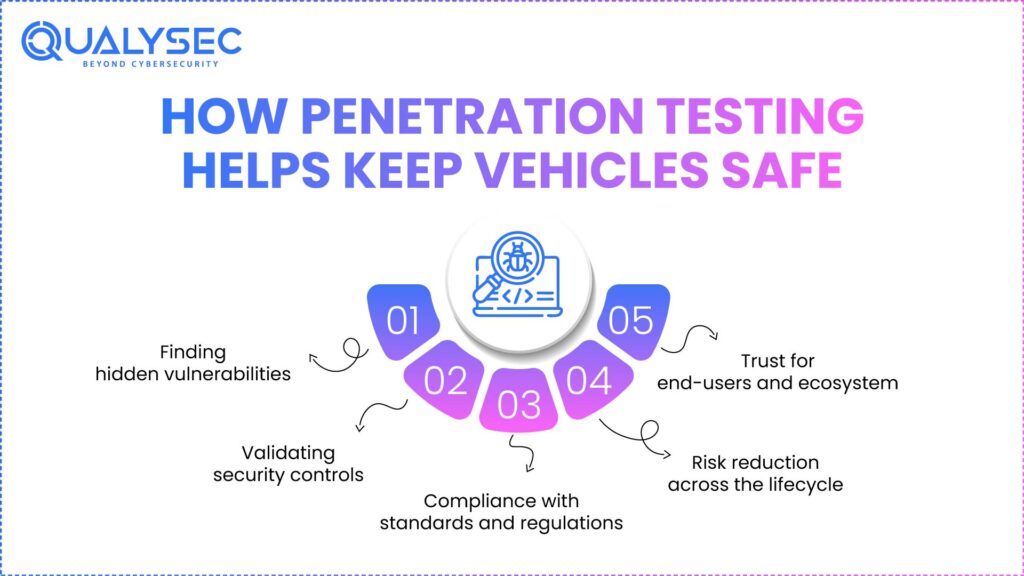
Pen-testing has major advantages in automotive security; here is how it helps to foster trust and safety:
1. Finding hidden vulnerabilities
Vulnerabilities can be found in different locations since cars include hardware, firmware, integrated software, communication buses, and external networks. Vulnerability and Pen-testing find those problems before they can cause harm.
2. Validating security controls
Simply possessing encrypted communications, secure boot, firewalls, or secure OTA updates is insufficient; it’s important to verify if they are executing well through penetration testing. For example, Arm notes that secure boot, enabled by a secure enclave, protects communication between untrusted components.
3. Compliance with standards and regulations
Standards like ISO/SAE 21434 recommend penetration testing as a key validation activity. Through pen-testing, manufacturers and suppliers gather proof of risk management and due diligence.
4. Risk reduction across the lifecycle
Vehicles have long lifespans; flaws discovered after production can be lethal or financially serious. Early identification of problems by means of effective pen-testing programmes lowers brand damage, liability, recall risk, and hazardous conditions.
5. Trust for end-users and ecosystem
Connected cars interacting with mobile devices, infrastructure, and cloud systems guarantee a strong cybersecurity in the automotive industry by means of pen-testing, thereby increasing trust in the brand, the vehicle, and the ecosystem.
Download a sample penetration testing report to know more about vehicle vulnerabilities and how to prevent them.
Download a Sample Pen Testing Report

Challenges in Automotive Security Testing
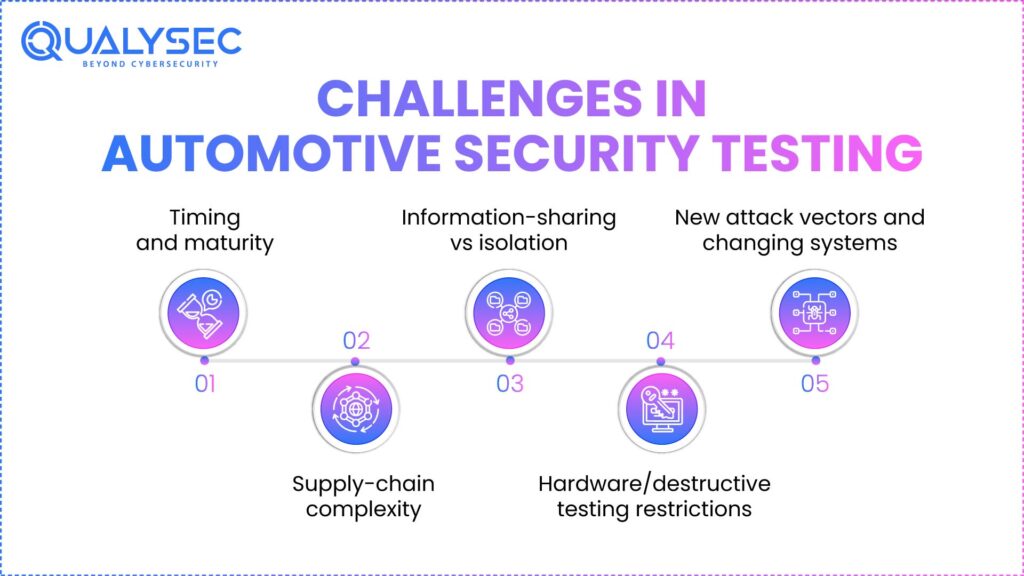
Although it is quite important, automotive network security testing faces some serious difficulties specific to it:
According to Deloitte notes, there are many ECUs, several in-vehicle bus types (CAN, LIN, FlexRay, Automotive Ethernet), and software/hardware availability, hence complicated system architecture.
- Timing and maturity: Many vehicle projects have a strict timeline. If penetration testing begins too late, there’s often not enough time or hardware maturity to address the findings. Deloitte emphasises the importance of starting early.
- Supply-chain complexity: Parts from many suppliers may be reused. Responsibility for security testing and controls may be distributed across OEMs and suppliers. Clear definitions of responsibility are needed.
- Information-sharing vs isolation: To work effectively, testers require adequate understanding (message catalogues, signal definitions), but excessive sharing could risk security or IP.
- Hardware/destructive testing restrictions: Some hardware-level tests include destructive techniques or thorough physical access, hence complicating the procedure.
- New attack vectors and changing systems: Over-the-air updates, V2X communication, and SDV architectures are expanding the automotive attack surface. Arm points to growing software complexity and connectivity as major risk factors.
Early pen-testing, a committed trained staff, labs with appropriate access, and defined processes across OEMs, suppliers, and testers all help to meet these issues.
Best Practices for Automotive Penetration Testing
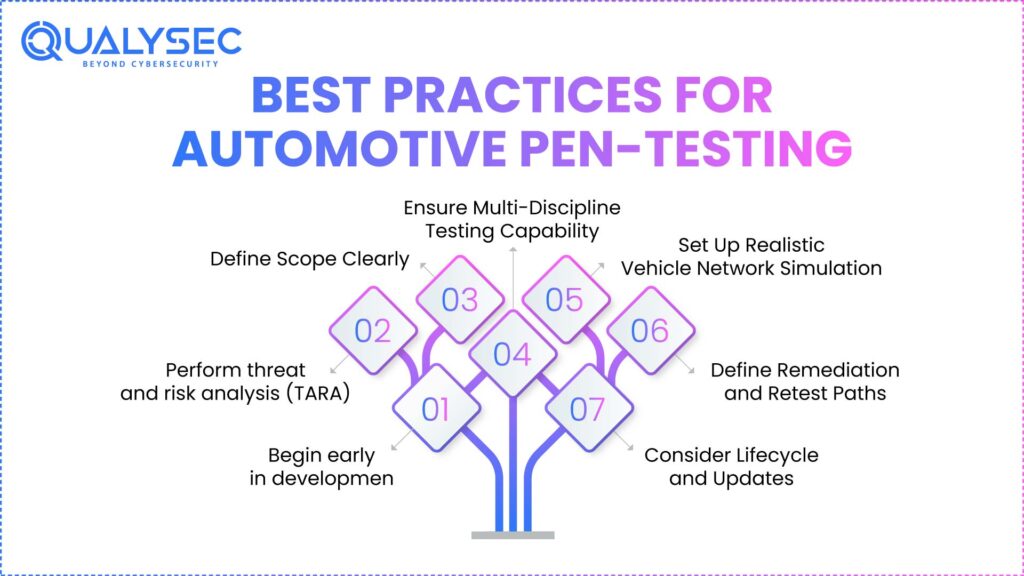
These are the concrete best ways to run a good car pen-testing programme:
- Begin early in development: Integrate pen-testing during the design and development phases, not just before production.
- Perform threat and risk analysis (TARA): This helps to determine the highest risks (safety-critical ECUs, V2X interfaces, OTA update paths) and therefore gives penetration testing services priority.
- Whether it’s a complete car, a component of a system, or a functionality change (differential testing), define scope clearly: assign roles, duties, test targets, hardware readiness, and interfaces.
- Make sure multi-discipline testing ability is present: The team has hardware hackers, embedded software testers, wireless/communications testers, cloud/mobile interface professionals, etc.
- Realistic vehicle network simulation, bus access (CAN, FlexRay, Automotive Ethernet), rest-bus simulation, hardware test benches, etc., establishing labs and test infrastructure.
- Define clearly remediation and retest paths: Findings have to inform development; solutions must be tested via retesting; leftover dangers must be monitored.
- Lifecycle and update consideration: Given OTA updates and extended vehicle lives, pen-testing should be an ongoing programme rather than a one-off event.
Schedule a live demonstration of Qualysec’s automotive pen-testing skills to see how we replicate real-world threat situations on ECUs, networks, and vehicle systems.
Conclusion
The automotive sector is changing dramatically. Connectivity, electrification, autonomy, and software-defined vehicles provide great possibilities but also cyber risks affecting safety, compliance, and trust. Emerging as a basic defensive tool, penetration testing helps to verify security measures, find flaws before they turn hazardous, and back standards like ISO/SAE 21434.
Still, the path of Automotive security testing is not easy. Challenges come from complexity, supply-chain dependencies, time constraints, and ever-changing threat surfaces. Better positioned to provide safe, secure cars will be companies that include thorough pen-testing programmes, use best standards like TISAX compliance, and interact with seasoned partners.
Now is the time to act if you are an automotive OEM, tier-supplier, or mobility start-up wanting to improve your vehicle cybersecurity posture and vehicle-specific testing capabilities. rather than wait for an event.
Take the next step toward safer, more secure auto vehicles: chat with our AI assistant today.
Chat with our intelligent AI Assistant and get tailored insights in seconds.

FAQs
1. What is automotive security?
Automotive security involves ensuring the safety of vehicles and their hardware, software, networks, and information from unauthorised access, interference, and malicious attack. Automotive cybersecurity includes the firmware of an ECU and secure OTA updates, as well as the safety of V2X communications.
2. What is the best security for your car?
The factors such as vehicle type, connection, and location will determine the “best” security. But manufacturers (and aftermarket providers) should typically include multi-layer defence: secure hardware root of trust, robust authentication/authorisation, encrypted communications, intrusion detection, secure update mechanisms, and ongoing security testing/validation (including manual pentesting). Instead of just one control, defence-in-depth is what makers should use.
3. What is the ISO standard for automotive security?
The primary standard is ISO/SAE 21434, covers the procedures for managing ISO cybersecurity automotive risk. throughout the car’s life cycle. In many countries, criteria like UNECE R.155 (Cyber Security and Cyber Security Management System).
4. What are the four main types of security?
Although “types of security” can have varying definitions depending on the context, a generally accepted approach is:
- Physical security is the preservation of real property (vehicle structure, keys, sensors) from theft or vandalism.
- Network and communication security safeguards data in transit (CAN bus, Ethernet, wireless links, OTA updates) against interception, eavesdropping, and tampering.
- Protecting ECUs, embedded systems, sensors, and gateways against exploitation, tampering, and side-channel threats is known as endpoint security.
- Securing firmware, operating systems, mobile apps, and cloud services from vulnerabilities guarantees software and application security. Therefore, developers ensure safe development and patching.
Need Help Understanding Vehicle Security Risks? Get a free 30-minute consultation with our security experts to help you evaluate the right partner for your business.
























































































































































































































































































































































































































































































































































































































0 Comments