Undoubtedly, there has never been a higher adoption of cloud computing in India. It is observed that Indian companies are shifting quickly to a public and hybrid cloud platform to achieve cost savings, scaling, and agility. But this expansion is associated with some major risks, and data security in cloud computing has become a crucial foundation for the business. Data security in cloud computing is now a high-level priority. It is no longer enough to assume that cloud service providers alone will protect your data. The shared responsibility model makes it clear. While providers secure the infrastructure, businesses are accountable for protecting their applications, identities, and sensitive data.
In this blog, we explore the real meaning of data security in cloud computing, why it matters, the most pressing risks, and practical solutions that businesses can implement.
What is Data Security in Cloud Computing?
Data security in cloud computing can be defined as policies, processes, and technologies that protect digital data that is stored, processed, or transmitted within a cloud environment.
Here, we attempt to safeguard the Confidentiality, Integrity, and Availability (CIA) of information. Cloud environments are highly dynamic, multi-tenant, and API-based, unlike traditional IT.
Learn how Infrastructure Security in Cloud Computing protects your business.
Why is Data Security Important?
Data security in cloud computing is not only a technical issue but a question of the survival of the business. A single infringement can ruin trust that can lead the organisation to pay fines to the authorities and ruin necessary business operations.
With the emergence of the Digital Personal Data Protection (DPDP) Act, 2023, security is not only a highly recommended practice but also a mandatory one. Organisations should protect personal data and notify the Data Protection Board about any violation and follow the privacy principles.
To the business, successful data security in the cloud equals:
- Resilience: it does not stop or reduce operations even during an attack.
- Compliance: meets DPDP, CERT-In, ISO/IEC 27017 and 27018.
- Customer trust: confidence that sensitive information, including financial, health, and personal identifiers, will be handled sensibly.
Top Data Security Risks
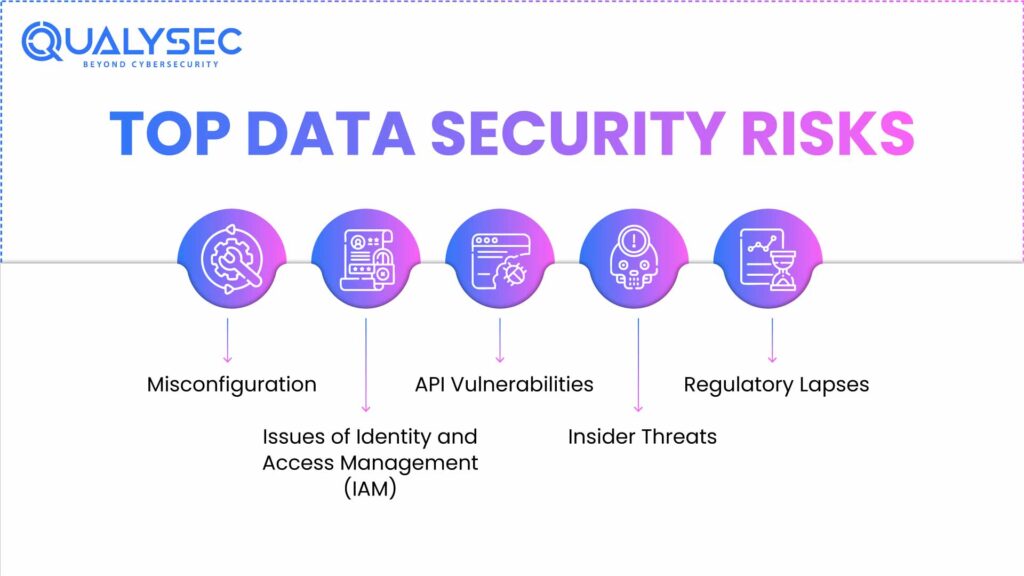
Cloud environments bring flexibility and scale, but also unique risks. Here are the top data security risks organisations face today:
- Misconfiguration: It is among the most common causes of cloud breaches. Open storage buckets, overly permissive IAM roles, and unencrypted databases are some examples.
- Issues of Identity and Access Management (IAM): Stolen credentials and privilege escalation are the drivers of numerous cloud attacks. It should be mentioned that unsecured multi-factor authentication (MFA), weak passwords, and dormant accounts are easy targets.
- API Vulnerabilities: Cloud security services are API-based, and insecure or exposed APIs are a favourite target. The threats are poor authentication, injection, and rate limiting.
- Insider Threats: Both intentional and unintentional errors (i.e., misuse of access rights) may expose sensitive data to harm, as do malicious insiders.
- Regulatory Lapses: The non-observance of regulatory laws (DPDP Act or CERT-In) may lead to financial penalties. What must be understood is that compliance is a responsibility that is shared between the business and the cloud provider; it is not the sole responsibility of the cloud provider.
Learn more about common Security Risks in Cloud Computing.
Data Security Regulations
It is advisable to note that cloud data security is more than just a technical challenge. It is also a compliance requirement.
Let’s take a look at the key data security regulations:
1. Digital Personal Data Protection (DPDP) Act, 2023
This privacy law in India requires organisations to protect personal data, reduce the usage of personal data, and disclose breaches to the Data Protection Board of India. Non-adherence will lead to a heavy fine; therefore, active security is a necessity.
2. CERT-In Directives
The Indian Computer Emergency Response Team makes it a requirement that some cyber incidents be reported within six hours. To cloud adopters, this implies having monitoring and logging systems that are powerful enough to identify and escalate problems in a short amount of time.
3. International Standards
The global best practice in data protection is ISO/IEC 27017 (cloud-specific controls) and ISO/IEC 27018 (cloud privacy). They are often associated with Indian organisations that want to get international customers or certifications.
Check out our Article on Data security Compliance
Top Data Security Solutions
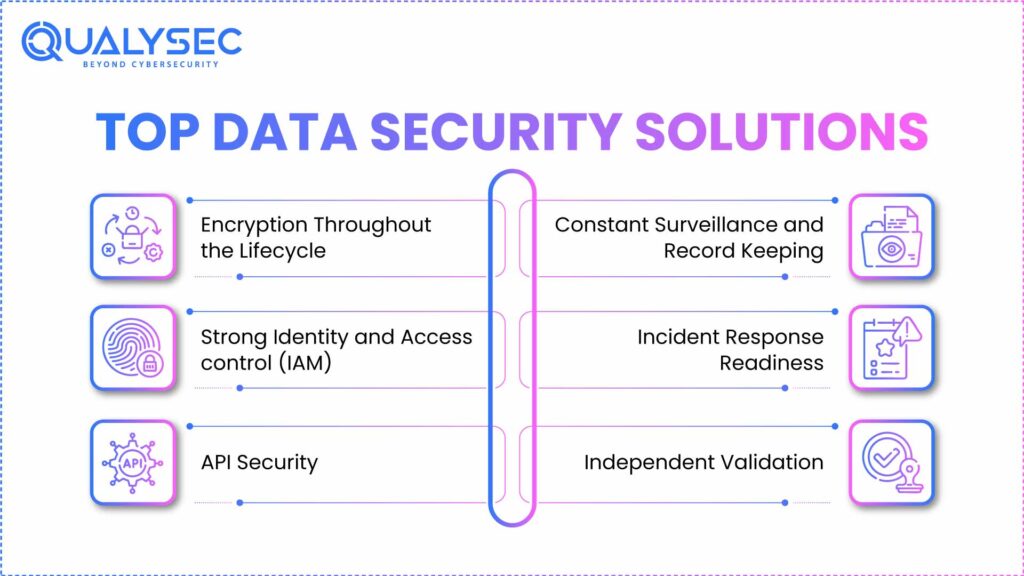
Protecting data in cloud computing requires more than just adopting cloud-native tools. Organisations need a layered security strategy that addresses both technical risks and governance requirements. The following solutions form the backbone of effective cloud data protection:
1. Encryption Throughout the Lifecycle
Encrypt data in rest, transit, and processing. Strong encryption means that should unauthorised access be executed, the data will not be read without the keys. Customer-managed key Key Management Services (KMS) is an added level of assurance.
2. Strong Identity and Access control (IAM)
Since one of the leading causes of a cloud breach is a stolen or abused credential, it is essential to enforce role-based access control, Multi-Factor Authentication (MFA), and access review. IAM policies need to be audited continuously to remove privilege creep.
3. API Security
As cloud services are highly API-oriented, APIs need to be secured. This involves authentication, authorisation, schema validation, and rate limiting. The API gateways offer centralised visibility and security against typical exploits.
Check out our related article on API Security Testing
4. Constant Surveillance and Record Keeping
Live tracking offers the chance to identify abnormal activity at its initial stages. In addition to improving visibility, centralised logging assures compliance with CERT-In’s six-hour incident reporting rule in India.
5. Incident Response Readiness
Preparation is the basis of breach resilience. Playbooks on cloud-specific incident response (IR), tabletop exercises, and process automation of escalation contribute to organisations responding expeditiously.
6. Independent Validation
Tools alone cannot guarantee security. Independent cloud penetration testing, application testing, and retesting provide evidence that controls are working effectively and demonstrate accountability to auditors and regulators.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Data Security Best Practices
Building a secure cloud environment requires disciplined practices applied consistently. Take a look at these best practices businesses can adopt for data security.
1. Encrypt Data
With encryption, attackers or anyone who accesses your storage or intercepts network traffic cannot read the data because they do not have the keys. One should also make encryption the default setting on all storage (databases, object storage, backups). In addition, all in-transit data should be encrypted with TLS 1.2+.
2. Strengthen Identity and Access Management (IAM)
As per the latest reports, credential abuse remains one of the top causes of cloud breaches. It is critical to apply the principle of least privilege (users only get the access they truly need). Enforcing Multi-Factor Authentication (MFA) is an excellent step.
3. Secure APIs
APIs drive cloud, and unsecured endpoints are where attackers typically access the cloud. Secure APIs via gateways that authenticate and authorise. Protected APIs can also be validated against gateways that perform authentication and authorisation.
4. Audit and Monitor Continuously
Breaches are inevitable if issues go unnoticed. Without monitoring, you cannot comply with India’s reporting mandates. It is essential to enable and centralise logging for all cloud resources. You can also deploy anomaly detection systems to flag unusual activity.
Get a complete cloud security audit from Qualysec.
Conclusion
Securing data in cloud computing is no longer optional. It is the backbone of trust, compliance, and business continuity in today’s digital-first India. With regulations such as the DPDP Act, 2023, and CERT-In’s directives, organisations are expected not only to adopt cloud technologies but also to demonstrate that they can keep sensitive data safe.
Businesses can minimise the exposure to threats by implementing best practices. At Qualysec, we opt for transparent methodologies and detailed audit-ready reports.
Book a cloud penetration test with Qualysec today.
Latest Penetration Testing Report

FAQs
Q1. What is data security in cloud computing?
Data security in cloud computing is the set of technologies, policies, and procedures that ensure sensitive information in cloud environments. The intention is to retain the data and eliminate the special risks.
Q2. Why is data security important in cloud computing?
Cloud platforms are becoming part of modern business, and they store all customer records, financial data, etc. Devoid of reliable safeguards, these assets can be easily hacked, misconfigured, and abused.
Q3. What are the main threats to data security in the cloud?
The threats most often are:
- Misconfigurations (buckets left unguarded, loose permissions).
- Weak identity and access control (IAM) (credential theft, privilege exploitation).
- Unprotected or insufficiently validated interfaces (insecure APIs).
- Insider threats (malicious insiders or accidental abuse).
- Non-compliance by regulation (non-conformance to DPDP, CERT-In, or ISO standards).
- What are the benefits of AI and machine learning to cloud data security?
Q4. How do AI and machine learning improve cloud data security?
AI and machine learning can be used to improve the security of the cloud because cloud security threat detection is quicker and more precise than manual surveillance. For example, it could easily detect suspicious logins, access to data, and network traffic. It is also capable of blocking suspicious activity or isolating systems that are compromised.
Q5. What is the future of data security in cloud computing?
The next trend in data security in cloud computing will be on automation, Zero Trust, and continuous validation. Zero trust means that any access request will be verified, and automated compliance tools will be used to check compliance with various laws. Artificial intelligence-based defence mechanisms will change dynamically to emerging threats, yet consistent verification and audit of the cloud data security measures by an independent team of experts remains critical.

























































































































































































































































































































































































































































































































































































































0 Comments