Network Vulnerability Scanning is emerging as a growing issue to the company in India and across the world. The phenomenon of cyber threats is growing at an accelerating pace all over the world. Thus, organisations require effective security. In addition, Network Vulnerability Scanning will assist in detecting vulnerabilities before they are used by hackers. Cyber attacks have risen by 38 per cent in 2025 than before. Therefore, vulnerability scanning is the area that businesses should focus on in the field of cybersecurity. This guide will make you know all about the Network Vulnerability Scanning and its significance..
What is Network Vulnerability Scanning and How Does It Work?
Network Vulnerability Scanning is the act of determining vulnerabilities to security when it comes to your IT infrastructure. It, in particular, audits networks, systems, and equipment in case it identifies vulnerabilities. Also, this process encompasses all types of components, such as routers, switches, and firewalls. These are some of the elements that are analyzed by network-based vulnerability scanner tools.
The scanning process is in a number of steps. The scanner will first find all the devices in your network. It then scans each device for possible vulnerabilities. In addition, the tool also maps results with an in-depth vulnerability database. Organisations are therefore provided with an in-depth Vulnerability Scanning Report of critical issues.
Network Vulnerability Assessment Checklist typically includes:
- Verifying the old software versions.
- Monitoring incorrect security configuration.
- Discovery of open ports that are not supposed to be open.
- Reviewing weak password policies.
- Status update on patch management.
- Network Vulnerability Scanning Types.
Types of Network Vulnerability Scanning
Various scanning methods are used for a purpose. Hence, the knowledge of all the types assists organizations in selecting the appropriate approach.
| Scanning Type | Description | Use Case |
| Authenticated Scanning | Scans with network credentials | Internal security assessment |
| Unauthenticated Scanning | Scans without login access | External threat simulation |
| External Vulnerability Scanning | Examines perimeter security | Internet-facing assets |
| Host-Based Scanning | Inspects individual servers | Specific system analysis |
| Network-Based Scanning | Checks the network infrastructure | Overall network health |
| Web Application Scanning | Test web applications | Online service security |
Why Do Organisations Need Network Vulnerability Scanning in 2026?
Cyber threats are on a U-turn in India and other countries as well. In the meantime, hackers are evolving more advanced in their mode of attack. Network Vulnerability Scanning has therefore been a necessity to survive. Organisations are exposed to a lot of risks in the absence of appropriate scanning.
Key Benefits of Regular Vulnerability Scanning
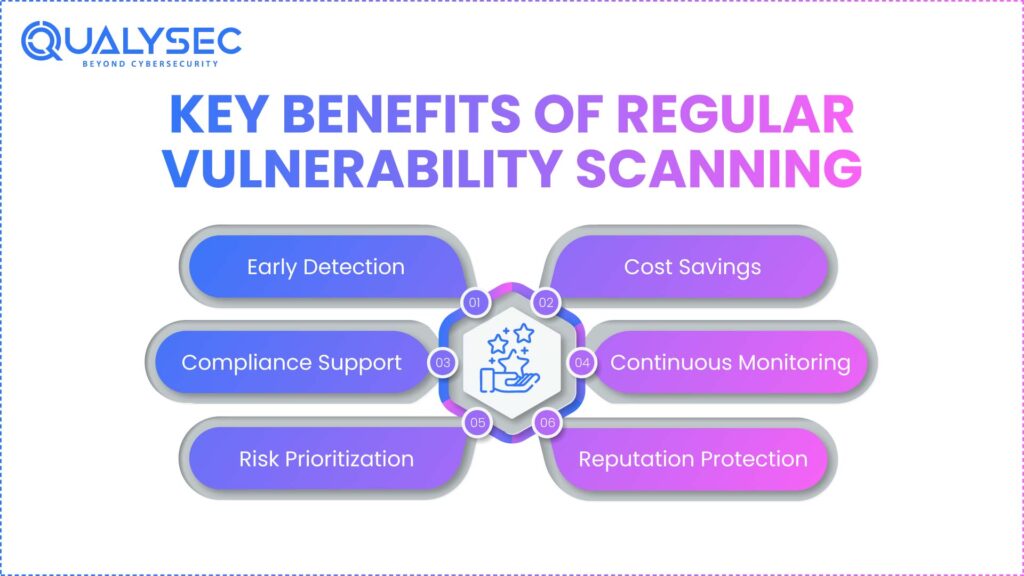
Modern businesses have several benefits that are offered by the use of cybersecurity scanning tools. To start with, they identify security vulnerabilities in advance. Also, they assist organisations in being ahead of threats. In addition, frequent scanning eliminates the risk of data breach considerably.
- Early Detection: Finds vulnerabilities and then exploits them.
- Cost Savings: Averts costly cases of data breach.
- Compliance Support: Adequately responds to regulatory requirements.
- Continuous Monitoring: Delivers uninterrupted security.
- Risk Prioritization: Assists in prioritising the key problems.
- Reputation Protection: Maintains customer trust and confidence
In addition, Network Security Testing identifies concealed security holes. Consequently, IT teams can solve problems in time. In the same regard, automated scanning is very time and resource-saving.
Current Threat Landscape in India
In the year 2025, India will have very special cybersecurity issues. In particular, this year, ransomware attacks have grown by 45 per cent. Also, Indian companies are being targeted by phishing activities every day. Hence, network vulnerability scanning tools are vital in protection.
There are alarming statistics in the world. An example is that 60 per cent of small businesses fail within six months of a cyber attack. In addition, the mean cost of breach of data breach was 4.45 million in the world. It is therefore financially viable to invest in the Vulnerability Scanning Tools.
How to Choose the Right Network Vulnerability Scanning Tools?
It is important to carefully select the network vulnerability scanning tools. To start with, determine the needs in your organisation. The second step is to assess the options on the basis of the most important features. Moreover, scalability and integration should be considered.
Essential Features of Vulnerability Scanning Tools
The current cybersecurity scanners must have extensive functionality. Thus, seek the following critical characteristics:
- A comprehensive database of vulnerabilities that is updated regularly.
- Automated routine scan scheduling.
- In-depth reporting and analytics dashboards.
- Interconnection with existing security infrastructure.
- Backup of the different network devices and systems.
- Risk prioritisation according to the level of risk.
The tool should also offer remedial guidance that is actionable. Besides, it has to be able to support authenticated and unauthenticated scanning modes. On the same note, perimeter security requires an external vulnerability scanning capability.
Popular Network Vulnerability Scanning Tools
There are a number of tools that are prevailing in the market. Still, they are useful for various organisational purposes. Thus, it is possible to make decisions based on their strengths.
Leading tools include:
- Nessus: Enterprise-wide scanning platform.
- Burp Suite: A Web testing-based application is great.
- Nmap: a free network discovery tool.
- Wireshark: Network traffic analysis and troubleshooting
- Metasploit: Advanced penetration testing capabilities
- OpenVAS: Free and open-source vulnerability scanner
However, the choice of tools is determined by the budget, technical skills, and needs. Moreover, most organisations employ the use of numerous tools to cover broadly.
Scan Your Website with Qualysec’s Free Website Vulnerability Scanner.
What Makes Qualysec the Leading Network Vulnerability Scanning Provider Globally?
Qualysec is the best Network Vulnerability Scanning company in India and in the rest of the world. In addition to this, Indian enterprises rely on Qualysec to provide overall security solutions. In particular, their method of work is a combination of high technology and professional human analysis. Thus, the companies are better safeguarded against cyber attacks.
Why Qualysec Excels in Vulnerability Scanning
Qualysec provides the best scanning vulnerability in cybersecurity services. First, their team consists of qualified security professionals with extensive experience. Moreover, they also offer year-round monitoring and support. Also, Vulnerability Scanning Tools offered by Qualysec identify the threats that automated scanners have overlooked.
Key advantages of choosing Qualysec:
- Comprehensive Coverage: Tests all network components thoroughly
- Expert Analysis: Professional pentesters validate findings manually
- Detailed Reporting: Provides actionable insights and remediation steps
- Compliance Support: Ensures adherence to global security standards
- 24/7 Monitoring: Continuous threat detection and response
- Customized Solutions: Tailored approaches for different industries
In addition, Qualysec also has an excellent track record. In particular, they have assisted more than 1000+ companies to improve their security positions. Also, their Network Vulnerability Assessment Checklist has addressed all the critical areas inclusively.
Services Offered by Qualysec
Qualysec offers total security solutions to contemporary businesses. Thus, customers are fully covered in all digital assets. In addition, their services are compatible with the current infrastructure.
Explore all our advanced cybersecurity penetration testing services.
Core services include:
- Security audits and network penetration testing.
- Security testing of the web applications.
- Mobile application security test.
- Cloud security evaluations
- API security testing
- Testing social engineering.
Qualysec also provides Network Security Testing services, whereby vulnerabilities are discovered before the attacks by the attackers. On the same note, their external vulnerability scanning secures internet assets facing vulnerabilities. Additionally, customers receive ongoing post-assessment services.
Location: Qualysec operates in the USA and India. Consequently, they effectively service clients in more than one time zone.
Make a free consultation with Qualysec now and discover how they can strengthen your security posture. Furthermore, download their detailed pentest reports to understand their thorough approach. Contact their experts today for personalized security solutions.
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
Best Practices for Effective Network Vulnerability Scanning
Network Vulnerability Scanning will need strategic planning to implement. To begin with, develop objectives and scope. Then, adhere to best practices in the industry. More so, incorporate scanning in your general security approach.
Establishing a Scanning Schedule
Constant scanning is important in ensuring security. Consequently, develop a thorough scanning program. In addition to this, customise frequency according to your risk profile.
- Critical Systems: Scan daily or after every change
- Production Environments: Conduct weekly scans minimum
- Development Systems: Perform bi-weekly assessments
- All Assets: Execute monthly comprehensive scans
- External Perimeter: Run continuous monitoring
- Compliance Requirements: Follow mandated schedules
Also, perform scans to conduct the following major infrastructure changes. Likewise, conduct emergency scans in case of any new threats. Moreover, scan schedules when there is low traffic to reduce inconvenience.
Key Steps for Successful Implementation
Effective vulnerability scanning in cybersecurity follows structured processes. First, create an accurate asset inventory. Next, prioritise assets based on criticality. Furthermore, assign clear responsibilities to team members.
Implementation checklist:
- Record all network resources fully.
- Set up scanning equipment using reasonable credentials.
- User-configure scan policies of various kinds of assets.
- Non-production testing scanning processes.
- Develop escalation guidelines on findings.
- Develop remediation processes that have timelines.
In addition, train your IT department on scan results interpretation. Further, ensure that the scanning of all activities is well documented. Explore more resources for implementation guidance.
Common Challenges and Solutions
There are numerous challenges that an organisation encounters when carrying out Network Vulnerability Scanning. Nevertheless, these difficulties can be overcome by gaining insight into them. It means that you should plan for standard problems.
| Challenge | Solution |
| False Positives | Tune scanners and validate findings manually |
| Network Performance Impact | Schedule scans during off-peak hours |
| Alert Fatigue | Prioritize based on severity and exploitability |
| Limited Resources | Use managed security services |
| Complex Environments | Segment networks and scan systematically |
| Outdated Vulnerability Databases | Ensure automatic updates are enabled |
Read our latest guide: Network Security Threats and Solutions: How to Protect Your Business
Moreover, notes of lessons acquired at the end of every scan. Equally, constantly engage in process improvement through feedback. Besides, invest in training to develop internal expertise.
Talk with our experts at Qualysec to overcome implementation challenges effectively. Additionally, leverage their experience to optimize your scanning program.
Understanding Vulnerability Scanning Reports and Remediation
The interpretation of the Vulnerability Scanning Report is a key factor in successful remediation. In the first step, learn what rating of the severity of findings is. The second thing to do is to focus on remediation with risk and business impact priority. Moreover, monitor track.
Analyzing Scan Results
Scan reports hold significant data that must be analysed. Thus, concentrate on user-actionable data and not on raw data. In addition, comparable results were obtained in more scans.
Key report components:
- High-level overview and executive summary.
- VPN vulnerabilities descriptions and VPN CVE.
- Critical, High, Medium, Low, or Rating of severity.
- Assets and systems of interest list.
- Suggested intervention measures.
- Assessment of compliance impacts.
Also, the current cybersecurity scanners have risk scores to prioritise. On the same note, they provide remediation schedules in accordance with the severity of threats. Moreover, trending analysis demonstrates an increase in security posture.
Remediation Strategy Development
Remediation needs to be done systematically. To begin with, classify vulnerabilities according to type and severity. Then come up with remediation plans and set timelines. In addition, delegate the responsibility of every identified problem.
- Critical Vulnerabilities: Address within 24-48 hours
- High-Risk Issues: Remediate within one week
- Medium Severity: Fix within 30 days
- Low Priority: Schedule for next maintenance window
- Informational Findings: Document and review quarterly
Further, ensure that remediation was successful by rebasing. As well, to gauge security improvement, track measures. Equally, keep audit trails as a method of compliance.
Schedule a free consultation with security experts to develop effective remediation strategies. Visit Qualysec’s contact page for expert guidance.
Download the Exclusive Pen Testing Report

Conclusion
Network Vulnerability Scanning will still be a vital part of cybersecurity in 2026. In addition, threats are in a constant state of dynamic development in India and the world over. Thus, companies need to provide extensive scanning initiatives. Also, frequent evaluations assist in the identification of the weak points before they are exploited.
In this guide, we have discussed tools and best practices of network vulnerability scanning. Besides, we have talked about the implementation and remediation strategies. On the same note, we have also emphasized the need to have the right security partner.
It is important to note that vulnerability scanning in cybersecurity is not a one-time affair. Therefore, it is important to have constant monitoring and improvement. Furthermore, automated tools with expert analysis are the best to be used to ensure maximum protection.
Take action today to strengthen your security posture. Download comprehensive pentest reports from industry leaders. Additionally, implement Network Security Testing regularly. Most importantly, partner with experienced providers like Qualysec for superior protection.
Frequently Asked Questions (FAQs)
1. What is Network Vulnerability Scanning?
Network Vulnerability Scanning refers to the automatic technology of detecting security vulnerabilities in network infrastructure. It also analyses the devices, systems, and applications in case they are susceptible to attacks by hackers.
2. Why is Network Vulnerability Scanning Important for Businesses?
Network Vulnerability Scanning assists businesses in identifying security weaknesses before they can be identified by attackers. In addition, it minimises the risk of expensive data breaches and ensures compliance with cybersecurity rules.
3. What Is the Difference Between Vulnerability Scanning and Penetration Testing?
Vulnerability Scanning is an automated process of searching for vulnerabilities in the security of the network using network vulnerability scanning tools. On the other hand, penetration testing entails manual exploitation done by security analysts to confirm vulnerability.
4. What is a common tool for network vulnerability scanning?
Nessus is a popular network-based vulnerability scanner that is used to detect security flaws holistically. Other commonly used Vulnerability Scanning Tools, such as Nmap, OpenVAS, and Burp Suite, are also used for different ends.
5. Does Network Vulnerability Scanning Help with Compliance?
Yes, Network Vulnerability Scanning assists companies in doing what regulatory organizations such as PCI-DSS and ISO 27001 demand. Moreover, routine scanning shows due diligence of the safety of sensitive information and preservation of the standards of security.
6. How Do I Choose the Right Network Vulnerability Scanning Tool?
Choose cybersecurity scanning solutions depending on your network size, budget, and technical needs. In addition, it is important to consider such characteristics as automation capabilities, reporting quality, and compatibility with the current security infrastructure.
























































































































































































































































































































































































































































































































































































































0 Comments