Introduction
Cloud security breaches pose one of the most pressing issues in organizations worldwide, as companies rapidly transition to cloud infrastructures. By 2026, cybercriminals will still be developing innovative techniques to exploit flaws in cloud environments. According to recent statistics, 83 percent of organizations have experienced a minimum of a single case of security breach in the clouds in the past 18 months, proving the essential issue of being conversant with these risks.
Cloud Computing has complicated the security issue, giving rise to new avenues of attack that are not necessarily covered by traditional methods of security. Knowledge about the kinds of security breaches and Cloud Computing Vulnerabilities is vital, as they allow an organization to come up with countermeasures to shield its vital information against evil players. In this guide, we will analyse six severe forms of cloud security breaches that organisations are likely to experience in 2026 and how to go about preventing them, and also reduce the risk of data leakage in cloud computing.
The Rising Threat Landscape of Cloud Security
The situation with the cloud security breaches in 2026 is an unmatched challenge to organizations. The medium of cloud technologies has been faster than the security measures, making it susceptible to abuse by cybercriminals.
Current State of Cloud Security Breaches
The statistics surrounding security breaches in cloud computing paint a concerning picture:
- 45% of all data breaches now occur in cloud environments, officially surpassing on-premises incidents
- 82% of cloud security breaches are attributed to human error and a lack of proper visibility
- 25% of organizations fear they may have experienced an internal security breach in cloud computing without awareness
- Companies face 2,300 cyberattacks weekly, with cloud-focused attacks increasing 13% annually
Key Contributing Factors
Several serious factors facilitate the heightening of cloud security breaches:
- Misconfiguration crisis: 23 percent of incidents are a misconfiguration of the cloud done by humans, and 82 percent of these are human errors
- Visibility gaps: 32 per cent of cloud assets are unmonitored and have around 115 identified vulnerabilities each
- Multi-cloud complexity: 79% of the respondents are utilizing the services of multiple cloud providers, and 56 percent of them have data protection issues
- Skills shortage: 45 percent of companies do not have qualified cybersecurity personnel in key positions
6 Critical Types of Cloud Security Breaches in 2026
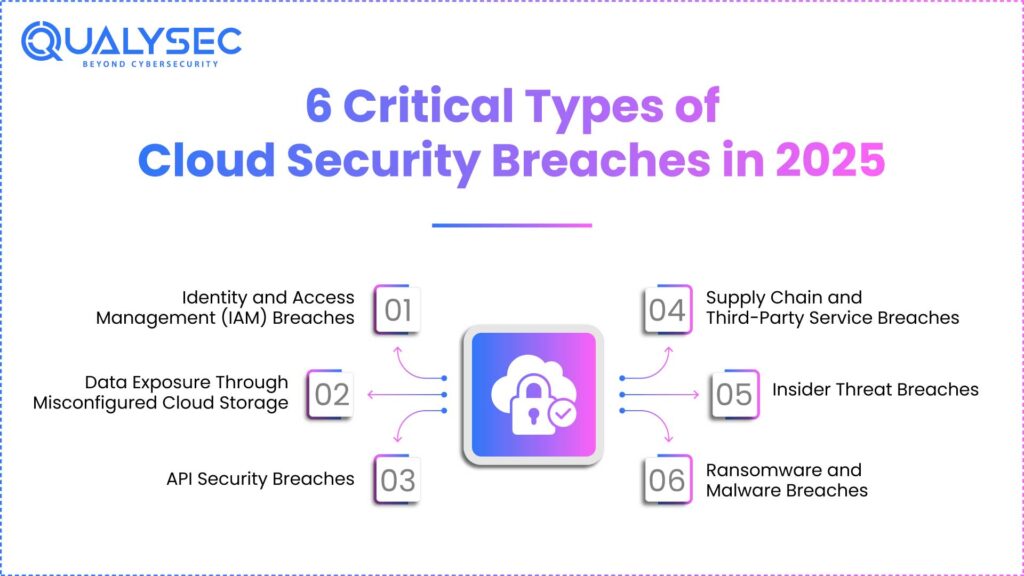
1. Identity and Access Management (IAM) Breaches
Identity and access breaches are the most common form of cloud security breach in 2026, acting as the biggest source of attack by cybercriminals on cloud use.
- Credential theft mechanisms: Attackers employ slick phishing campaigns, social engineering tricks, and credential stuffing attacks to search for cracked user accounts and acquire introductory access to cloud environments.
- Privilege escalation techniques: Attackers who gain access to cloud infrastructure systems exploit weaknesses in cloud infrastructure security, using excessive access privileges and poor access controls to travel across cloud infrastructure and gain access to sensitive information.
- Federated identity vulnerabilities: Hybrid cloud systems present a wide variety of trust relationships between on-premises and cloud infrastructures, and this diversity leaves the attacker with a variety of vectors of attack.
- Multi-factor authentication bypasses: Threat actors use smishing, SIM jacking, and malware to bypass the use of multi-factor authentication.
2. Data Exposure Through Misconfigured Cloud Storage
Data breaches in cloud computing security remain a primary point of concern due to misconfigured cloud storage, as organizations end up exposing sensitive data to illegal access.
- Public storage containers: Unsecured S3 buckets, Azure Blob storage, and Google Cloud Storage boxes in the open leave terabytes of sensitive data, such as customer records and intellectual property, exposed.
- Default security settings: It has been observed that most often organizations use standard configurations within cloud services, which do not offer maximum protection because they customize them with the view of increasing accessibility rather than the safety of the information concerned.
- Overpermissive access controls: Permission levels set during the initial configuration remain unchanged and allow the wrong people to gain sensitive information.
- Automated discovery by attackers: Malicious actors have automated ways of scanning publicly available cloud storage containers, increasing the efficiency of the discovery of vulnerable data.
“Read also: Infrastructure Security in Cloud Computing.“
3. API Security Breaches
Security threats to APIs have become a significant source of vulnerability as organizations continue using APIs to integrate their cloud services and communicate.
- Authentication vulnerabilities: Weak authentication of APIs via poor API keys and API token verification allows attackers with ready access points.
- Injection attacks: SQL injection, NoSQL injection, and command injection attacks via API parameters enable an attacker to manipulate cloud databases and services.
- Rate limiting bypasses: Malicious network actors intentionally abuse inherited and ineffectively designed rate-limiting mechanisms to deliver smelly denial-of-service attacks that can overload cloud-based facilities
- Data exposure risks: APIs tend to expose too much data, placing attackers in a position to derive sensitive information if they acquire access during the legitimate uses of the APIs.
“Read our complete guide on API Security Testing.“
4. Supply Chain and Third-Party Service Breaches
Attacks on the supply chain targeting cloud instances have blown up, and the effectiveness of being able to compromise one vendor to reach several destinations is understandable to the attacker.
- Vendor account compromises: Hackers seek out the compromises of third-party service providers who manage to access numerous environments, thus exposing data breaches in cloud computing to many companies
- Malicious software dependencies: Attackers compromise the dependencies and libraries in cloud applications, giving themselves a backdoor to infiltrate sensitive systems and data.
- CI/CD pipeline infiltration: An adversary gains access to continuous integration and deployment pipelines in order to add malicious code to cloud applications during the development cycle.
- Inadequate vendor oversight: The companies fail to assess the security of cloud service providers adequately, and this forms a blind spot within the security positions of the organisations.
“Explore our blog on Third-Party Penetration Testing.“
5. Insider Threat Breaches
The challenges of insider threats in cloud environments are different, as more usual monitoring and restriction of access capabilities are not adequate to observe suspicious or foolish insider activity.
- Privileged user misuse: Users with higher access privileges can misuse them and steal sensitive information or crash the cloud services without being detected for a long duration
- Negligent data handling: Even the best employees can, out of negligence, cause data leakage in cloud computing in an unauthorised manner, misconfigure, and/or maintain insufficient security procedures
- Compromised insider accounts: Insider attacks are normally through employee accounts or insider access, which have been compromised to deny original access to the security systems
- Inadequate offboarding processes: There is no system to revoke access to the systems by ex-workers, and it takes a long time before they are completely out of access to cloud systems, creating chances of either deliberate or unintentional security breaches
” Learn how to safeguard your business from Cloud Security Threats in 2026.”
6. Ransomware and Malware Breaches
Ransomware attacks on the cloud have advanced, and attackers have come up with cloud-oriented strategies to inflict maximum losses and ransom payments.
- Cloud-native ransomware: The new types of ransomware are specifically organized to attack cloud storage, databases, and virtual machines, and encrypt the data concurrently with several cloud services.
- Backup system targeting: Attackers specifically target cloud backup systems so that there is no other option or method to recover, so they have to pay off the ransom demands.
- Double extortion tactics: Cybercriminals can lock up data with data theft, demanding a ransom by threatening to publish superior information in case of failure to pay the ransom.
- Lateral movement techniques: Inside cloud environments, the ransomware operators leverage the allowed cloud security tools to move throughout the infrastructure easily, and it is hard to detect and encapsulate them.
| Breach Type | Attack Vector | Primary Impact | Detection Difficulty | Average Cost |
| IAM Breaches | Credential theft | Unauthorized access | Medium | $3.8M |
| Storage Misconfiguration | Public containers | Data exposure | Low | $4.1M |
| API Security | Authentication bypass | Data manipulation | High | $3.2M |
| Supply Chain | Third-party compromise | Multi-org impact | Very High | $5.1M |
| Insider Threats | Privileged abuse | Data theft | Very High | $4.7M |
| Ransomware | Malware deployment | Business disruption | Medium | $6.2M |
Latest Penetration Testing Report

Advanced Prevention and Detection Strategies
Zero-Trust Architecture Implementation
Zero-trust has been important when it comes to avoiding security breaches in cloud computing.
- Identity verification: All users and devices should be verified before gaining access to cloud resources.
- Micro-segmentation: Isolation of zones of the network restricts the consequences of a breach and blocks lateral transitioning.
- Continuous monitoring: Anomalies in the behavior patterns can be identified by minute analysis of the current changing behavior patterns.
- Policy automation: The controls in cloud services are maintained by automation, and verify similar security controls.
Comprehensive Security Framework
Organizations should embrace comprehensive models that would deal with every dimension of cloud security breaches:
- Risk assessment: Periodical assessment of the chain and discontinuities on cloud-based assets is required to prioritize security investment
- Incident response: Cloud-specific procedures lead to speedy containment of data breaches in cloud computing in cloud computing
- Security training: Training programs minimize human error-related incidents.
- Vendor management: There are stringent reviews that avoid breaches of the supply chain.
” Read how Cloud Security Testing mitigates cloud vulnerabilities “
Cloud Security Monitoring and Analytics
Real-Time Threat Detection Systems
Regular monitoring facilities are needed to identify cloud security breaches as early as possible before serious damage is done.
- Behavioral analytics: Machine learning is also used to examine past trends and determine behavior that could indicate intrusion activity or internal security breaches in cloud computing.
- Network traffic analysis: Deep analysis identifies command messaging, data exfiltration, and horizontal movement.
- Log aggregation: On any central system, security events are instruments used to collect attack patterns.
Advanced Analytics and Machine Learning
AI integration significantly enhances the detection of sophisticated data breaches in cloud computing:
- Anomaly detection: Statistical models identify deviations from normal behavior patterns
- Predictive modeling: Systems analyze historical data to predict future attack vectors
- False positive reduction: AI-powered analytics filter benign activities and focus on genuine threats
- Attack attribution: Advanced analytics identify patterns for threat actor attribution
Security Information and Event Management (SIEM)
The current SIEM solutions offer end-to-end visibility and incident response:
- Multi-cloud integration: Platforms aggregate data to be monitored across various providers on a single platform
- Compliance automation: Automated reports meet regulatory requirements
- Threat hunting: Analysts look to hunt compromise indicators proactively.
- Tool integration: SIEM solution incorporates security tools to provide an end-to-end response.
Performance Metrics and KPIs
Organizations must establish metrics measuring cloud security monitoring effectiveness:
- Mean time to detection (MTTD): Measuring incident detection speed assesses monitoring capabilities
- Mean time to containment (MTTC): Tracking containment times optimizes incident response
- False positive rates: Monitoring rates helps fine-tune tools and reduce alert fatigue
- Coverage metrics: Assessing monitored asset percentages identifies blind spots
Why Qualysec is the Best Cloud Security Company
“Learn more about leading Cloud Security Provider Companies in our blog.“
Qualysec Technologies leads the industry in offering comprehensive cloud security breaches when addressing security breaches in organizations that are affected by cloud security. It has more experience, more skills, more abilities, skills across both AWS, Azure, Google Cloud, and so on, and therefore will offer unrivalled security against all six major types of security breaches in cloud computing that are described in this guide.
Qualysec has a full-scale plan containing sophisticated penetration testing, vulnerability wrap-ups, and constant monitoring solutions that have been customized to cloud environments. Their certified security professionals have the knowledge of cutting-edge complexities of cloud infrastructure and will offer customized solutions that evaluate the unique security requirements an organization may have. The demonstrated practices of the company have helped in thwarting many data breaches in cloud computing across industries.
Qualysec is special because it takes an end-to-end security stance, a blend of state-of-the-art automated prevention methods, as well as heavy human involvement. Their consultants operate in close collaboration with the clients to come up with tailor-made security approaches to meet the industry demands and regulatory compliance. This tailored solution makes sure that every customer gets the best security solution with regard to cloud security breaches, as well as ensuring that their operations run efficiently.
The service that Qualysec offers includes identification and access management audits, application programming interface security testing, configuration tests, and insider threat detection programs. They have evolved their threat detection with 24/7 incident response services that protect against emerging threats.
Schedule a Free Consultation with Qualysec Today to discover how their expert team can strengthen your cloud security posture.
Regulatory Compliance and Cloud Security
Companies should make cloud security initiatives meet regulatory demands, as the latter would impose compliance punishments. The shared responsibility model also brings out the need to have clear security responsibility between the providers and the customers. The important frameworks are SOC 2 Type II, ISO 27001, GDPR, HIPAA, and PCI DSS. Security audits are conducted regularly to ensure costs incurred in compliance begin at USD 10,000 per year.
Conclusion
Cloud security breaches that are considered crucial, along with being most likely, are known to take place in the six types identified that relate to digital asset protection and business continuity in the year 2025. Whether it is IAM breaches, misconfigured storage, API weaknesses, or ransomware attacks, every threat has to be addressed with particular prevention and mitigation solutions.
The figures lend greater weight to the evolution of highly detailed cloud security initiatives. As per 82 percent attributed to human error, 45 percent of data breaches are found in cloud environments, and therefore, organizations would be required to focus on security education, automated monitoring, and effective incident response systems.
The lessons learned are that zero-trust architecture should be implemented, continuous monitoring should take place, and adequate configuration management should be ensured, along with strong identity controls. Cloud security entails the cooperation between vendors, security vendors, and in-house teams.
As threats are changing, it is still important to remain updated about the new security breaches in cloud computing and invest in superior protection mechanisms to make a business succeed. Contact Qualysec’s security experts to develop a comprehensive strategy tailored to your organization’s specific needs and risk profile.
Proactive efforts, ongoing innovation, and professional advice are the main assurances to future cloud security by the trusted partners with knowledge of modern cloud environment complexities.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Frequently Asked Questions (FAQs)
1. What are the most common causes of cloud security breaches in 2025?
The most common causes of cloud security breaches in 2025 include human error (82% of incidents), misconfigured cloud services (23% of incidents), and compromised identity management systems. Lack of visibility into cloud assets and inadequate monitoring also contribute significantly to security incidents.
2. How can organizations detect internal security breaches in cloud computing?
Organizations can detect internal security breaches in cloud computing by implementing user behavior analytics, continuous access pattern monitoring, and anomaly detection systems. Regular access reviews, comprehensive audit log analysis, and data loss prevention tools help identify suspicious activities before significant damage occurs.
3. What is the average cost of a data breach in cloud computing?
The average cost of a data breach in cloud computing is USD 4.35 million, varying based on organization size, industry, data sensitivity, and response time. Organizations implementing zero-trust security models can save over USD 1 million per incident through improved detection capabilities.
4. How often should organizations conduct cloud security audits?
Organizations should conduct comprehensive cloud security audits at least annually, with quarterly reviews of critical configurations recommended for high-risk environments. Download Qualysec’s Cloud Security Assessment Report for detailed guidance on audit frequency and scope.
5. What role does encryption play in preventing cloud security breaches?
Encryption plays a crucial role in preventing cloud security breaches by protecting data at rest, in transit, and in use. Currently, 21% of organizations have encrypted over 60% of their classified cloud data, while 55% use comprehensive key management tools, significantly reducing unauthorized access impact.
Ready to secure your cloud infrastructure against advanced threats? Talk with Qualysec’s Expert Security Team to implement comprehensive protection strategies tailored to your organization’s unique cloud security requirements.

























































































































































































































































































































































































































































































































































































































0 Comments