The number of attacks on cloud systems of companies increases by 47 percent each year, with approximately 1,925 attacks per week already observed in the companies. Over 83 percent of companies had at least one cloud security issue in 2024, and ransomware attacks increased by 126 percent in the first quarter of 2025 alone. Amazingly, 32 percent of cloud assets are not monitored, with each having an average of 115 known security holes. These statistics indicate the need to have cloud security strategy services that will evolve with emerging risks and evolving cloud conditions.
In the context of businesses in Singapore, a digitally changing hub with the extensive adoption of 5G and multi-cloud computing, cloud workload protection, including AWS security strategy, requires an intelligent and proactive security approach. In the region, almost 90 percent of the companies have many cloud systems, and the exposures are greater due to misconfigurations and poor identity and access controls.
Definition of a Cloud Security Strategy
Cloud security strategy services are a complete list of measures, policies, and tools, as well as checks that are implemented to ensure cloud systems are not threatened, vulnerable, or unprotected during their lifetime. In contrast to the more traditional security that may simply be concerned with data, it is the 2025 secure cloud plan where the cloud is launched, used, and the hard settings are dealt with, including identity rules, data integrity, and cloud security compliance.
This strategy applies continuous monitoring, threat detection, and prompt response, with AI applications and automation to ensure the cloud is secure. Effective cloud security strategies indicate how companies should do things, such as apply the zero-trust concept, encrypt and decrypt data, implement access control, and be ready to handle incidents to combat modern advanced attacks.
Now is the best time to protect your cloud both in the present and future, assuming your company desires to protect it. Contact Qualysec Technologies to get professional services for cloud security!
Cloud Security Services – What are These?
Cloud security strategy services provide special assistance and instrumentation to establish, monitor, and retain the safeguards demanded by a cloud security plan. Key cloud security services include –
- Threat spotting and incident response, AI.
- Cloud Security Posture Management (CSPM).
- Identity and Access Management (IAM) software.
- Key control and data encryption.
- A weakness check and a configuration check.
- Automatic compliance check and reporting.
- Secure design compliant with the concepts of zero-trust.
- Assistance and verification of safe cloud migration.
- Periodic audit and test of weaknesses.
The collaboration between the cloud security strategy services forms a defensive layer that secures all the cloud components as safe, regulation-compliant, and resilient in a rapidly evolving threat environment.
Discover expert-approved steps, techniques, and a real-world cloud penetration testing report used by top cybersecurity teams.
Download a Sample Pen Testing Report

The 4 Pillars of Cloud Security
There are four fundamental principles of good cloud security, which ensure environments are safe –
- Data Safety – When Data is in storage and when it is in motion, it must be kept safe through strong encryption (such as AES 256) and secure protocols (such as TLS).
- Identity and Access Management – Use least privilege, two-factor authentication (MFA), and role-based access control (RBAC).
- Protecting the threats – Automatic detection, AI analysis, and fast responses can be used to minimize the risk.
- Compliance and Governance – Adhere to laws and rules (e.g., in Singapore, PDPA), be prepared to undergo checks, and maintain policies in force at all times.
The 4 C’s of Cloud Security
Cloud security strategy services are the most successful when they have the 4 C’s –
- Cloud Infrastructure Security – Investigate networks and compute resources.
- Cloud Data Protection – Secure databases and storage through encryption and back-up.
- Cloud Application Security – Shield the cloud-deployed applications.
- Cloud Visibility and Monitoring – Keep an eye on everything and identify suspicious activity and unauthorized interventions.
The 4 Categories of Cloud Security
Forms of cloud security are in line with how cloud is established and utilised, like AWS security strategy, and they are –
- Infrastructure Security – Secure virtual machines, networks, and storage.
- Application Security – Protect SaaS and bespoke cloud applications.
- Data Security – Encrypt and determine the people who view cloud data.
- Endpoint Security – Secure the devices that utilise the cloud to prevent breaches.
The 6 Pills of Cloud Security
An extended level of cloud security solutions is based on 6 pillars –
- Confidentiality – Data should be visible only to authorised users.
- Integrity – Prevent the unauthorised manipulation of data.
- Availability – Keep cloud services operational.
- Authentication – Check identities.
- Authorisation – Authorise what users can do.
- Auditability – Making records and tracking to ensure that everyone understands what has occurred.
If you’re unsure about hidden risks in your cloud setup, a short gap assessment can help -schedule a meeting to talk to an expert.
Qualysec’s cloud pentest gives you results—no endless emails, no digging through PDFs, no guesswork.

10 Actions to Take to Enhance Your Cloud Security Strategy Services
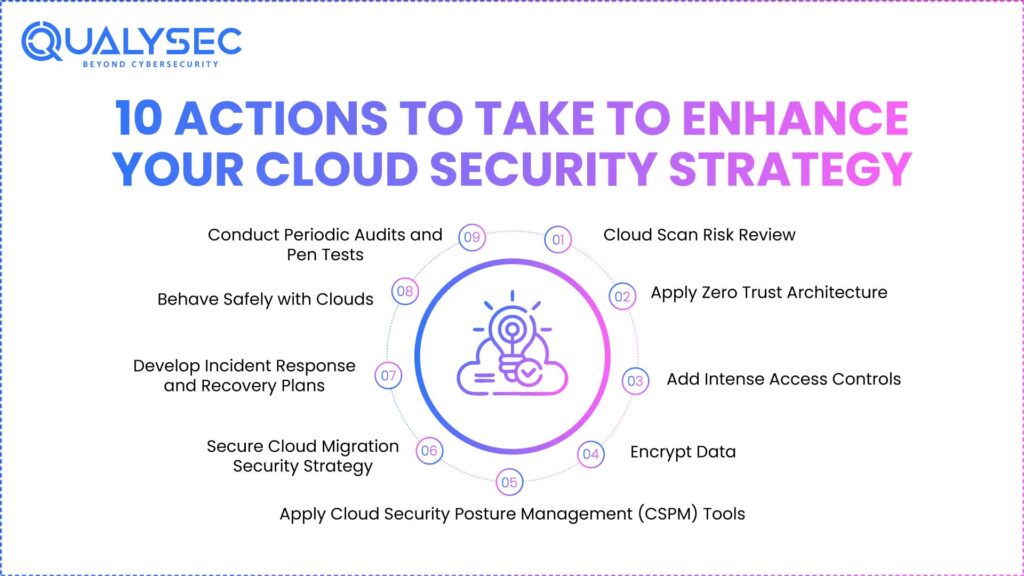
These steps should be in your cloud security strategy roadmap to maximize the value of your cloud protection –
- Cloud Scan Risk Review – Cloud vulnerability scanner scans all cloud components, settings, and access points to identify areas of vulnerability and rule loopholes.
- Apply Zero Trust Architecture – Assume everything is unsafe until proven safe. Reduce the attack surface by use of strict identity checks, split networks, and least-privilege access.
- Add Intense Access Controls – RBAC, MFA, as well as on-demand permissions, can be used to reduce insider abuse.
- Encrypt Data at rest and in motion, use AES-256 to store data, and TLS to transfer data, such as API and remote access.
- Apply Cloud Security Posture Management (CSPM) Tools – Network processes automatic checks and remedies of weak settings in various clouds.
- Apply AI Threat Detection and Fast Response – Install AI-based tools that can identify suspicious activity, provide warnings, and react promptly to attackers.
- Secure Cloud Migration Security Strategy – Prepare a migration plan that checks the cloud server security, verifies the settings, and verifies the rules before and after migration.
- Develop Incident Response and Recovery Plans – This is a strategy to minimize the harm caused by a cloud incident, such as a ransomware attack, data breach, and downtime.
- Behave Safely with Clouds – Educate employees to be mindful of newly emerged threats, how to dodge phishing, and how to utilize the cloud safely to reduce human error.
- Conduct Periodic Audits and Pen Tests – Periodically, perform penetration tests on your cloud defenses with tests and fake attacks so that you can identify and correct issues as soon as possible.
Select Qualysec Technologies to upgrade your cloud security plan with the best thoroughness, accuracy, and foresight tailored to Singaporean firms – Talk to an Expert!
How Qualysec Technologies Can Help You
Qualysec Technologies is specialised in cloud security strategy services. We also help businesses with an exclusive, tested program to ensure that their cloud is inaccessible to the increasing cyber threats. We apply deep tech expertise and mix it with intelligent automation and AI to verify security continuously and maintain the cloud in good condition.
Services
- Qualysec assists in strategy planning, risk assessment, cloud relocation security strategies, CSPM architectures, identity access support, automatic testing of hacks, and incident planning.
- Verified Process – The difference between Qualysec and other providers is our own verifiable process that scans your cloud on demand. We have continuous testing of multi-cloud and hybrid environments, unlike normal audits. It is in problems such as mis-setting, exposure, and gaps in regulation that we find. This strategy allows firms to enhance their security prior to a breach occurring.
- Custom Services – Qualysec is aware of the security issues that are unique to Singapore’s fast digital environment. Our team creates road maps to match how you operate and what the regulations indicate, and your secure cloud strategy decreases risk and further accelerates business and development.
- Human + AI Testing – Threat spotting with hands-on experts on the newest AI means that we identify weak spots that do not get identified by auto-only tools. The integration provides complete coverage and trusted results that allow your security teams to work with confidence.
You might like to know more about Cloud Penetration Testing in Singapore, AWS, Azure & GCP
Conclusion
The cloud security strategy roadmap of 2025 must have numerous layers, sophisticated tools, and an active approach. Cyber threats are increasing, the systems become complicated, and the rules create pressure on companies throughout the world, particularly in the digital scene in Singapore. Qualysec Technologies particularly commits to the cloud security strategy services by providing verified process checks that ensure that your security is current and operational.
Contact Qualysec Technologies to begin the process of going to a safer cloud for your business today!
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
FAQs
1. What is a cloud security strategy?
Cloud security strategies are an entire plan that explains how a business maintains its cloud information, applications, and resources free of cyber attacks. It involves the review of risks, implementing controls, such as encryption and access controls, attentively monitoring the data at all times, and applying regulations to ensure the information is accurate, confidential, and accessible at all times in changing cloud environments.
2. What are the cloud security services?
Cloud security services refer to a group of technologies, such as threat detection, incident response, identity and access management (IAM), data encryption, exposure check, rule monitoring, risky cloud migration security strategy, and security system design. They secure the cloud by placing rules in and managing rules at each point of cloud usage.
3. What are the 4 pillars of cloud security?
Cloud security has four pillars –
- Data Security – store data in an encrypted and well-written form.
- Identity and Access Control – provide only necessary authorisation and multi-factor log-in.
- Threat Protection – automate turn-on and response systems.
- Compliance and Governance – continue to adhere to and maintain policies.
4. What are the 4 C’s of cloud security?
The 4 C’s of cloud security emphasise Cloud Infrastructure Security, Data Protection, Application Security, and Visibility and Monitoring.
5. What are the four types of cloud security?
There are four categories of cloud security strategy services, namely –
- Security of infrastructure – secure virtual machines, networks, and storage.
- Application Security – custom cloud applications and secure SaaS.
- Protection of Data Security – encrypt and restrict data access.
- Endpoint Security – protect devices extending to the cloud.
6. What are the 6 pillars of cloud security?
Cloud security has six pillars, which are: Confidentiality, Integrity, Availability, Authentication, Approval, and Auditability.
























































































































































































































































































































































































































































































































































































































0 Comments