The Singapore Monetary Authority (MAS) penalised six banks and three other financial institutions a total of $27.45 million ($21.5 million) on Friday in relation to the country’s biggest ever money laundering scandal in 2023.
The case involved more than S$3 billion ($2.2 billion) in illicit assets seized after 10 foreigners were busted in a series of simultaneous raids in August 2023.
It is important to understand that with the massive growth in the banking sector of Singapore, threats have become more advanced. Banks in Singapore have faced an average of 1,830 cyberattacks per week over the past six months, as per the Threat Intelligence Report of CheckPoint from December 2024.
Financial institutions are expected to demonstrate not only that they understand the TRM framework but also that they can produce evidence that proves resilience in practice. MAS’s expectation is that technology risk management must be treated as a board-level priority, not just an IT function.
In this blog, we delve deeper into MAS TRM guidelines, what they mean, their importance, and best practices for the financial sectors.
What is MAS TRM?
The MAS Technology Risk Management (TRM) Guidelines are a comprehensive set of principles issued by MAS to help financial institutions identify, address, and manage technology risks. The primary aim is to improve how financial institutions safeguard IT systems, customer data, and services. Together, the TRM Guidelines and the new FSM Notices provide a layered security framework.
Impact of not being MAS TRM Compliant
Failing to comply with the MAS TRM Guidelines and the binding Notices (FSM-N05 and FSM-N06) isn’t just a matter of regulatory red tape. The consequences are very real:
- Regulatory scrutiny and penalties – MAS has powers under the Financial Services and Markets Act to take enforcement actions. These include financial penalties, restrictions, or even revocation of licenses for severe breaches.
- Financial losses from disruptions – Non-compliance with MAS technology risk management guidelines often means unpreparedness. Inadequate recovery testing or weak cyber hygiene can lead to prolonged downtime. For example, FSM-N05 requires critical systems to recover within four hours, and failing to meet that requirement can cause direct revenue loss and customer attrition.
- Data breaches and reputational damage – Singapore’s PDPA requires organisations to report significant breaches. MAS anticipates that the financial institutions will handle cyber incidents promptly and transparently.
- Higher operational costs in the long run – Control gaps lead to reactive firefighting, including emergency updates to the system, rushed audits, and costly cleanup operations that are so much costlier than proactive compliance would have been.
MAS TRM: Key Domains Covered
The MAS TRM Guidelines are broad and extensive. However, they can still be broken down into several core areas. These are:
1. Governance & Oversight
- Technology risk is under the board of directors and senior management.
- They must set a clear risk appetite and review risk reports regularly.
2. Technology Risk Management Framework
- The institutions have to determine, evaluate, and address risks in an organized manner.
- This involves maintaining the current risk registers and periodical reviews.
3. System Development & Change Management
- Security must be embedded in the SDLC (software development lifecycle).
- MAS expects secure coding, security testing, and change approval processes.
4. Cybersecurity Measures
- Use powerful access controls, authentication (with MFA), auditing, and cryptography.
- Always comply with FSM-N06, which establishes minimum cyber hygiene.
5. Third-Party & Cloud Risk Management
- The presence of outsourcing of important services does not eliminate responsibility.
- Institutions need to check vendors, keep an eye on them, and add risk provisions in contracts.
6. Operational Resilience
- The critical systems should address availability and recovery objectives.
- MAS expects disaster recovery testing and the ability to restore critical services within four hours of disruption (FSM-N05).
7. Incident Response & Reporting
- Institutions should have strategies to identify, react, and recover after cyber attacks.
- Major incidents are to be reported to MAS (in line with MAS Notice 658).
Challenges in Implementing MAS TRM Guidelines
Even the most well-funded and resourceful financial institutions might face challenges while implementing the MAS TRM Guidelines.
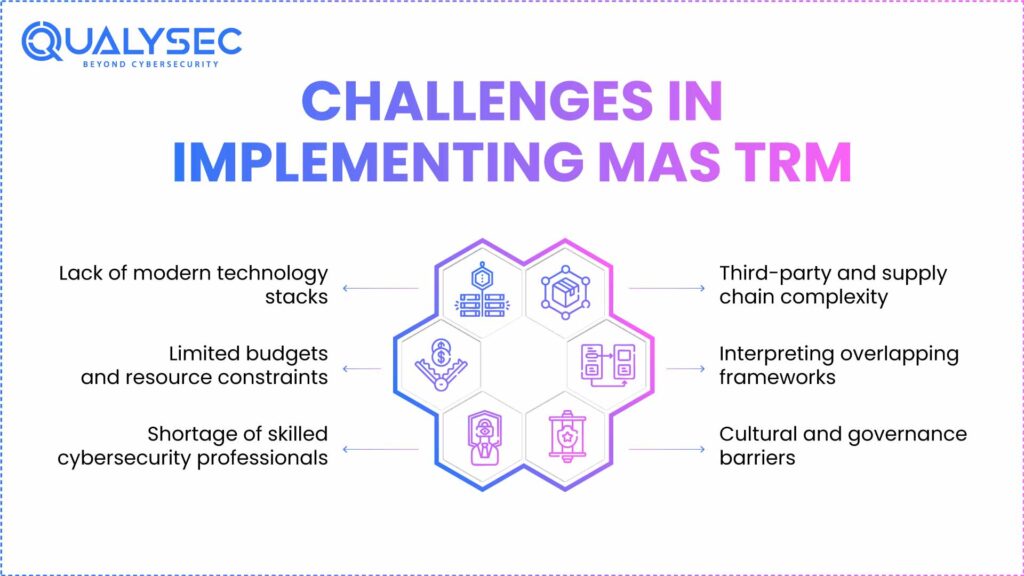
Take a look at these common challenges with MAS technology risk management guidelines:
Lack of modern technology stacks
A lot of banks and insurers have old systems that have not been built considering the current cyber resilience. They are time-consuming and expensive to upgrade or replace, and patching them frequently poses a risk to the operational process.
Limited budgets and resource constraints
Most fintech startups and payment service providers are smaller financial institutions that may not have special compliance or cybersecurity departments. It may be hard to juggle between meeting MAS expectations and the day-to-day operations.
Shortage of skilled cybersecurity professionals
Singapore has been experiencing a shortage in talent in areas of cyber risk and compliance, like most financial centers around the world. Hiring and retaining professionals who specialize in TRM spheres is a significant obstacle on a regular basis.
Third-party and supply chain complexity
Outsourcing IT services to cloud security services, financial institutions are extremely reliant on external vendors. It is also difficult to ensure that these partners satisfy MAS TRM requirements, especially when they are involved in more than one jurisdiction.
Interpreting overlapping frameworks
The compliance with either the ISO 27001, SOC 2, or PCI DSS has already been achieved in many organisations. It takes effort to comprehend how those frameworks fit (or do not fit) MAS TRM, and with the wrong assumptions, gaps in compliance may occur.
Cultural and governance barriers
In some organisations, technology risk is still viewed as an IT department issue rather than a board-level responsibility. This undermines the governance emphasis MAS places at the top of the TRM Guidelines.
Our experts at Qualysec have helped secure fintech, SaaS, and enterprise systems across 25+ countries. Manual + Automated Pentesting. No false positives. Actionable reports.

Top 5 Solutions To Maintain MAS TRM Guidelines
Once compliance is achieved, the bigger challenge is sustaining it. MAS supervisors expect financial institutions to embed TRM principles into daily operations, not treat them as a one-off project. Here are five practical solutions:
1. Adopt risk-based testing cycles
Instead of ad-hoc checks, establish a structured testing programme. Focus on the high-risk systems and high-risk services to undergo annual penetration testing, vulnerability testing, etc.
2. Automate monitoring and reporting
Automate the process of patching, account security, and system availability. Automation decreases human error and makes MAS-mandated controls over cyber hygiene (FSM-N06) operative.
3. Integrate compliance into the SDLC
Code inspection, automated testing, and pre-implementation testing must be done to confirm that applications can perform as per TRM (Technology Risk Management) expectations.
4. Strengthen vendor and third-party risk management
Standardise vendor evaluation procedures, particularly for cloud computing providers and outsourced information technology. Attach MAS TRM requirements to the contracts and ask the providers to provide evidence of compliance.
5. Invest in training and awareness across all roles
Compliance is not the IT team’s burden alone. Board members, senior managers, and frontline staff should all receive regular training on their roles in technology risk governance.
Schedule a Meeting Now. Discuss your TRM MAS compliance roadmap with our specialists.
Need a compliance-ready security assessment?
Implementation Roadmap: How to Achieve MAS TRM Compliance
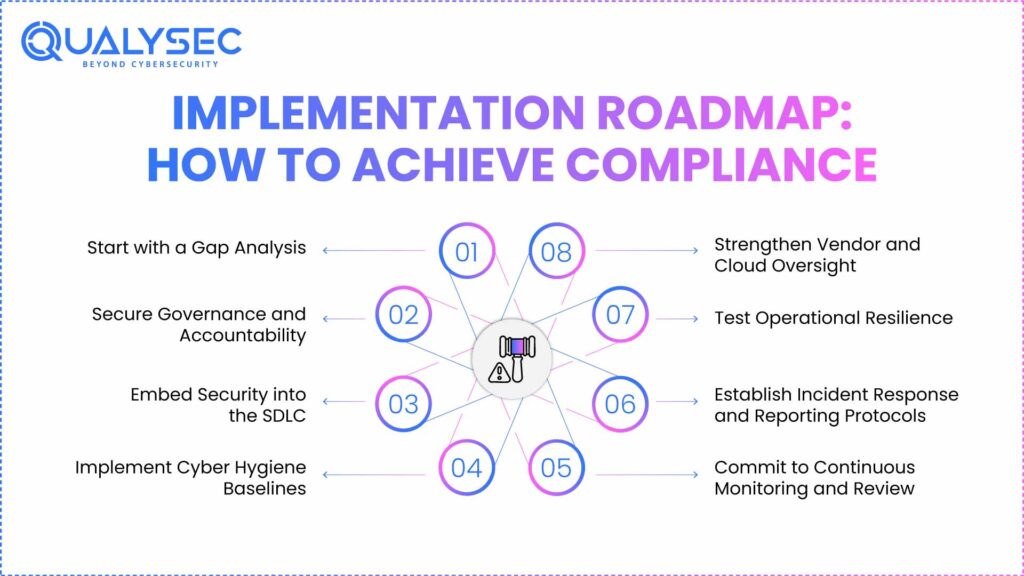
The MAS TRM Guidelines and binding Notices (FSM-N05 and FSM-N06) set a high bar. But compliance doesn’t have to feel overwhelming if approached systematically. Here’s a roadmap that institutions in Singapore can follow to move from intent to execution:
1. Start with a Gap Analysis
The first step is to understand where you currently stand. Conduct a comprehensive review of your existing controls, policies, and systems against the MAS TRM guidelines checklist and the mandatory requirements in FSM-N05 and FSM-N06. A well-documented gap analysis is not just an internal tool. Rather, it serves as evidence that your institution is taking a structured approach to compliance. Learn more about: Security Compliance for Financial Institutions.
2. Secure Governance and Accountability
MAS places strong emphasis on governance, making it clear that technology risk is not just an IT concern but a board-level responsibility. Institutions should assign clear roles, define risk appetite statements that explicitly cover technology risk, and ensure senior management regularly reviews technology risk reports.
3. Embed Security into the SDLC
To meet TRM expectations, systems and applications must be secure from the ground up. Security should be integrated directly into the software development lifecycle (SDLC), not bolted on as an afterthought.
4. Implement Cyber Hygiene Baselines
The requirements in FSM-N06 form the minimum security posture expected of any regulated institution. They are patch management, anti-malware protection, good privileged account controls, and multi-factor authentication.
5. Strengthen Vendor and Cloud Oversight
One of the most urgent issues of MAS is the third-party risk that is growing more and more because of the increased use of cloud providers and outsourced IT services by financial institutions. Before engaging vendors, institutions need to assess them, put MAS TRM requirements in contracts, and monitor vendor performance constantly.
6. Test Operational Resilience
The core of FSM-N05 requires that critical systems come back online within four hours after their disruption. To fulfill this criterion, institutions need to run frequent disaster recovery exercises and model cyber attacks to test the response capacity.
7. Establish Incident Response and Reporting Protocols
Incidents will be experienced in even the most mature organisations. The concern of MAS is the speed of detection, response, and recovery of institutions to them. Escalation paths, communication channels, and roles in the various scenarios need to be defined in a clear incident response playbook.
8. Commit to Continuous Monitoring and Review
Adherence to TRM is not a singular occurrence. Financial institutions are advised to come up with a recurring cycle of penetration testing, vulnerability testing, staff training, and governance reviews.
How can Qualysec help?
Qualysec supports financial institutions by providing:
- Penetration Testing Across Environments
Comprehensive cybersecurity assessments of web, mobile, API, and cloud platforms to identify vulnerabilities before attackers can exploit them. - Secure Code Reviews and SDLC Integration
Technical reviews to detect flaws early in development, helping organisations embed security into their processes, as MAS expects. - Compliance-Ready Reporting
Detailed reports aligned with MAS TRM requirements that can be shared with auditors, risk committees, and regulators as evidence of testing and remediation. - Gap Assessments and Remediation Support
Independent reviews to highlight gaps against TRM domains and the FSM-N05/FSM-N06 Notices, along with practical remediation guidance.
Schedule your MAS TRM compliance assessment today!
Consult with our cybersecurity experts
Discuss your unique security requirements and discover how we can help your business.
Conclusion
The Singapore MAS TRM Guidelines are not merely a reference user regulation. The practices are the best in enhancing the cybersecurity of the financial institutions. Integrating governance, cyber hygiene, secure development, and operational resilience with MAS expectations can help financial institutions in Singapore to decrease risk, inspire consumer confidence, and demonstrate responsibility to regulators.
In Qualysec, we help financial institutions with penetration testing, code reviewing, gap assessment, and reporting that is compliance-ready and directly aligned with MAS technology risk management guidelines and FSM Notices.
FAQs
1. Is MAS TRM mandatory?
The MAS technology risk management (TRM) guidelines are in themselves guidelines; they are best practices outlines, but not legally binding. MAS, however, anticipates that regulated financial institutions will be in line with them.
2. What is the MAS 658 guideline?
MAS 658 is based on MAS Notice 658 on Reporting of Cyber Incidents, which obliges financial institutions to report to MAS about cyber incidents immediately. It goes hand in hand with the TRM Guidelines, as it provides transparency and accountability in case some incidents happen.
3. Is TRM related to cybersecurity?
Yes. TRM (Technology Risk Management) is also synonymous with cybersecurity, but it is more general. TRM guidelines MAS include governance, system development, system operations, resilience, vendor management, and cyber hygiene.
4. What is TRMG?
TRMG stands for Technology Risk Management Guidelines. It is the official MAS publication that sets out principles for managing technology risks across the financial sector.























































































































































































































































































































































































































































































































































































































0 Comments