In today’s digital-first world, cybersecurity is not only an IT issue. It’s a business issue. However, many organisations mix up risk assessment vs vulnerability assessment. While both are similar, they are also very different.
Understanding the difference allows organisations to better identify threats and make better decisions regarding protecting their data, systems, and people. In this blog, we will look at what each assessment entails, how they work, and where they fit in a solid cybersecurity plan.
What Is Risk Assessment?
Risk Assessment – This is a top level strategy. The process involves identifying your vulnerabilities and threats, assessing the likelihood of these vulnerabilities being exploited and the threat occuring, as well as determining potential harm that could be caused. These threats range from cyber and system threats to third-party threats, to even human error. It aggregates an enterprise perspective that goes beyond technical vulnerabilities to include legal and financial dimensions, regulatory ramifications and operational repercussions. Risk assessments serve to inform decision makes what risks are most critical to their organisation and, in turn, enables them to make risk responses (such as mitigation, acceptance or transference (i.e. cyber insurance).
Worried about unseen vulnerabilities? Go to Qualysec: There are any vulnerabilities on your web application, let us find and fix them first!
What Is Vulnerability Assessment?
The Vulnerability Assessment: more of a techie vulnerability assessment. In simplest of terms, it is a process to scan your systems, networks, and applications looking for known vulnerabilities or weaknesses (e.g. unpatched software, misconfigurations) that an attacker can exploit. A Vulnerability Assessment is often carried out using automated tools, vulnerability scanners and manual testing methodologies. It will automatically prioritize results of the Vulnerability Assessment according to severity for IT teams to take immediate decisions. A VA does not asses BI or the likelihood of exploitation, only points out where you are vulnerable, and it does so fast.
Discover more: Vulnerability Assessment and Penetration Testing (VAPT)
Risk Assessment vs Vulnerability Assessment: Key Differences
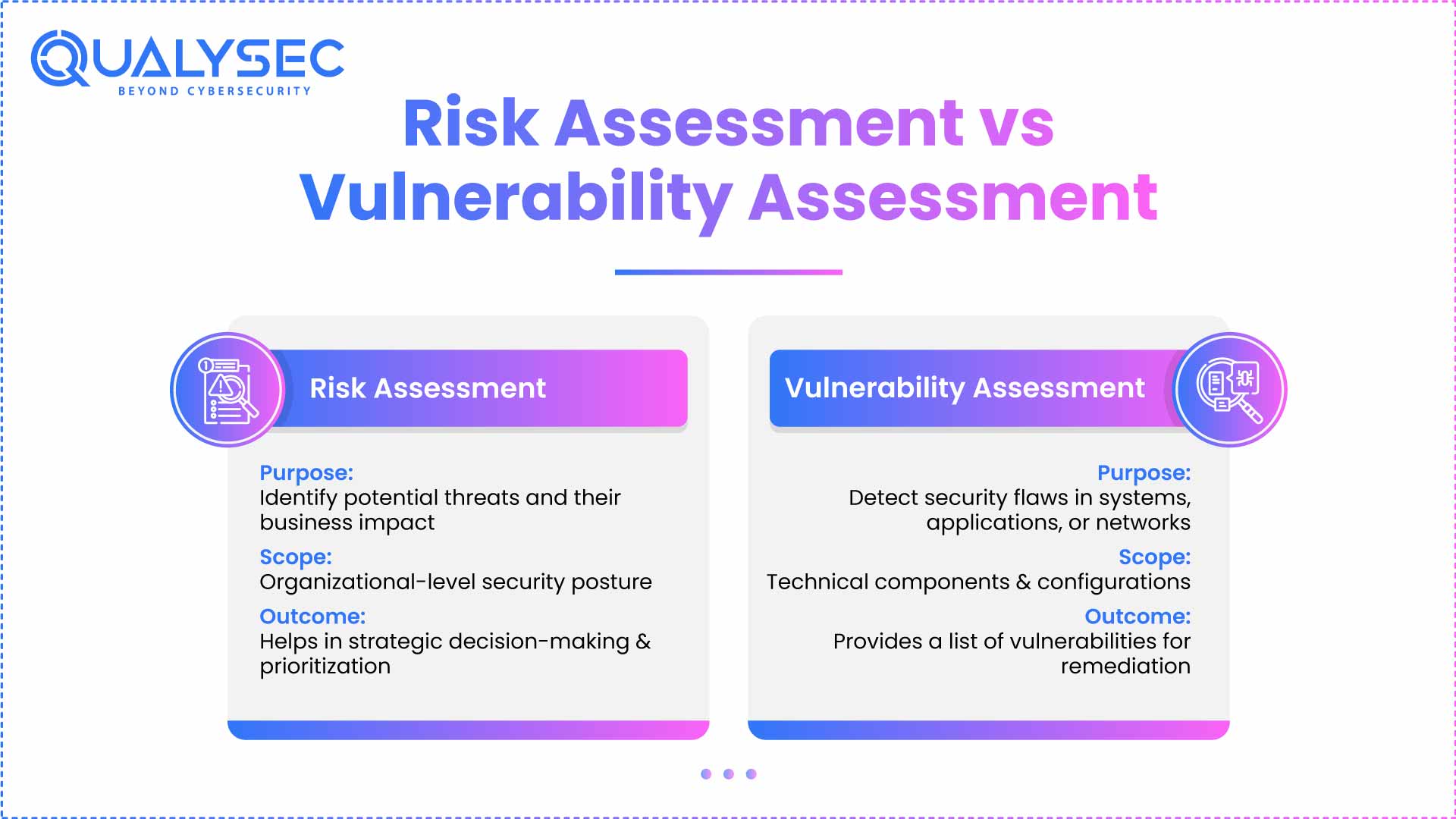
Risk assessment vs vulnerability assessment are frequently mistaken for each other, so often in the cybersecurity world, and they are NOT the same thing. They are related goals, but they each aim to serve a different purpose in protecting your systems. Here are the main differences, how do they help and how this will enhance your security strategy.
| Criteria | Risk Assessment | Vulnerability Assessment |
| Purpose | Identify, assess, and prioritize risks to the organization. | Identify and document security vulnerabilities or technical weaknesses. |
| Scope | Business-wide; encompasses assets, people, policies, third-party vendors, and compliance. | Technical environments, i.e., servers, networks, databases, apps. |
| Focus | Business impact, threat likelihood, and overall risk exposure. | Specific vulnerabilities and organizational concerns. |
| Approach | Strategic and often qualitative or semi-quantitative. | Strategic and often qualitative or semi-quantitative. |
| Tools Used | Risk matrices, interviews, threat modeling, risk scoring frameworks. | Vulnerability scanners, manual tests, CVSS scoring. |
| Frequency | Conducted an annual, bi-annual, or changing at the convenience of the business. | Performed regularly, monthly, quarterly, or continuously. |
| Performed By | Risk managers, compliance officers, and executive leadership teams. | Security analysts, engineers, and IT teams. |
| Outcome | A list of prioritized risks with business context and recommendations. | A report of vulnerabilities found and rated for severity. |
| Decision-Making Level | Executive-level decision on risk treatment plans and budget decisions. | Operational-level fixes, patches, and remediation plans. |
| Relationship to Each Other | Uses data from vulnerability assessment as an input. | It is a part of or input in risk assessment. |
Latest Penetration Testing Report

How Qualysec Can Help
We provide analytics and vulnerability checks to identify risks and help mitigate them. Our team uses advanced tools to identify problems and provide you with actionable ways to improve your security.
Whether you need assistance with compliance issues, securing data, or just want to reduce risk, our range of solutions can support your needs.
And we don’t simply look for risks: we support you through the process of remediating them, and help you protect your investment over the long term. Regular testing, clear reports, and expert support offer you easy-to-understand cybersecurity solutions that you can trust with Qualysec.
Make smarter security decisions with risk data that makes sense.
Conclusion
While risk assessment and vulnerability assessment may sound alike, the two terms serve very different roles in cybersecurity. One provides context for potential risks and threats, while the other identifies operational or technical defects in your organisation’s systems.
When risk and vulnerability assessments are combined, they lay the foundation for identifying, ranking, and reducing security threats. It is critical that every organisation makes use of both disciplines to meet the challenges of an ever-changing threat landscape.
Think your systems are safe? Let Qualysec put it to the test. Get a detailed security assessment now.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
FAQs
1. Is it possible to execute a vulnerability assessment without doing a risk assessment?
Yes, you can, but it isn’t recommended. A vulnerability assessment will highlight technical issues, but without a risk assessment, you may not have a clear understanding of which of those issues matter to your business.
2. How often should I perform a risk assessment vs a vulnerability assessment?
Risk assessments are typically performed annually or after you make major changes, while vulnerability assessments should be run more frequently, monthly, quarterly, or even continuously, depending on your environment.























































































































































































































































































































































































































































































































































































































0 Comments