The Therapeutic Goods Administration (TGA) is essential to the safety and effectiveness of medical devices in Australia. Under the TGA medical device regulations, with the increasing incorporation of software into devices and increased connectivity through networks, security against cyber threats is one of the most important considerations for medical devices. One way to protect them is through penetration testing to identify vulnerabilities before they can be exploited.
Understanding the TGA Medical Device Regulations in Australia
As part of the TGA medical device regulations outlining the safety and performance requirements for medical devices before they can be sold. The TGA states that medical devices must be secure against cyber threats or cyber risks.
They require that devices are designed to, where possible, mitigate risks to patients. Therefore, manufacturers must demonstrate safety processes that include clear protection of devices against cyber threats to comply with the regulations imposed by the TGA.
Explore our penetration testing services for the healthcare industry to address industry-related regulations.
Why Penetration Testing Is Essential for TGA Compliance
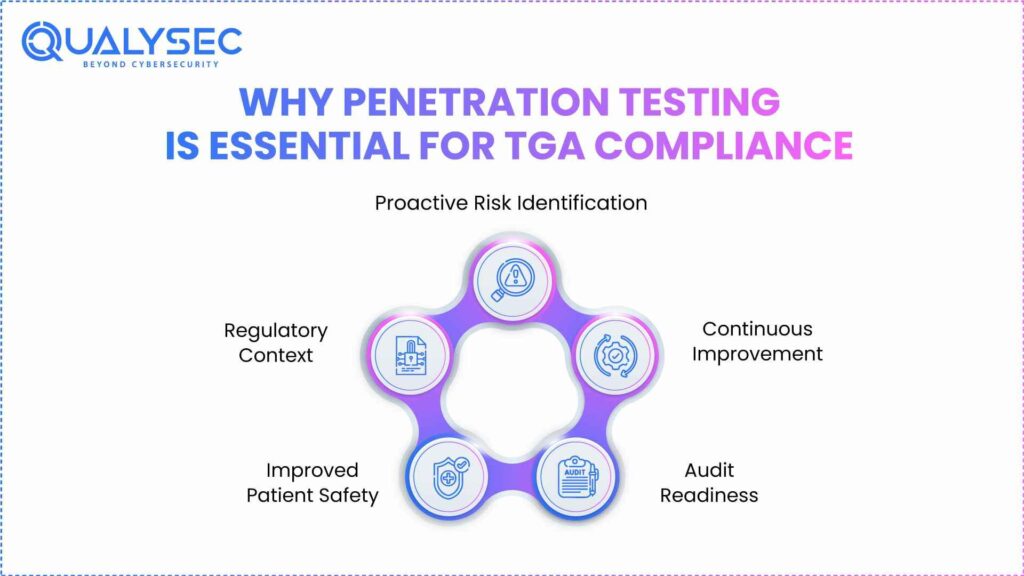
Vulnerability testing is a crucial aspect to illustrate that medical devices comply with the cybersecurity obligations of the Therapeutic Goods Administration (TGA). Taking this proactive approach means that vulnerabilities can be discovered and remediated before they are exploited, thereby protecting patients and avoiding regulatory non-compliance.
1. Risk Identification
Testing vulnerabilities works by putting simulated real-world attacks on medical devices to ascertain vulnerabilities, followed by remediation efforts. Organisations that utilise testing procedures earlier in the device’s life cycle create better protective strategies to prevent data theft. This earlier identification is more aligned with the TGA’s focus on ongoing risk identification and evaluation, which are a part of the device lifecycle.
2. Regulatory Context
The TGA medical device regulations require that medical devices demonstrate compliance with identified Essential Principles, some of which apply to safety and performance. Carrying out regular security testing used in medical devices shows that the organisation has demonstrated compliance with Essential Principles that apply to risk management and cybersecurity. While the TGA does not stipulate how it is done, testing and validation are commonly accepted in the industry.
3. Improved Patient Safety
Medical devices frequently process sensitive patient data and perform essential functions. A security breach could result in unauthorised access to personal health information or modify device functions that endanger patient safety. A penetration test will assist with the discovery and remediation of these vulnerabilities, in turn, reducing risk to patients.
4. Audit Readiness
Regulators require manufacturers to show compliance with cybersecurity standards. Completing penetration tests regularly creates safe documentation that can be utilised and presented during an audit to facilitate this verification. This documentation acts as documentation of due diligence and safety commitment to the users.
5. Continuous Improvement
Cybersecurity is in a constant state of evolution, and new threats are always emerging. Conducting penetration testing periodically will help determine the effectiveness of your current cybersecurity measures, and with any luck, you will find some new vulnerabilities. Regular penetration testing will help ensure the device is secure for its entire lifecycle and meets TGA obligations.
Schedule a Meeting to Ensure Your Medical Devices Meet TGA Compliance
Talk to our Cybersecurity Expert to discuss your compliance needs and how we can help your business.
Types of Penetration Testing Performed on Medical Devices
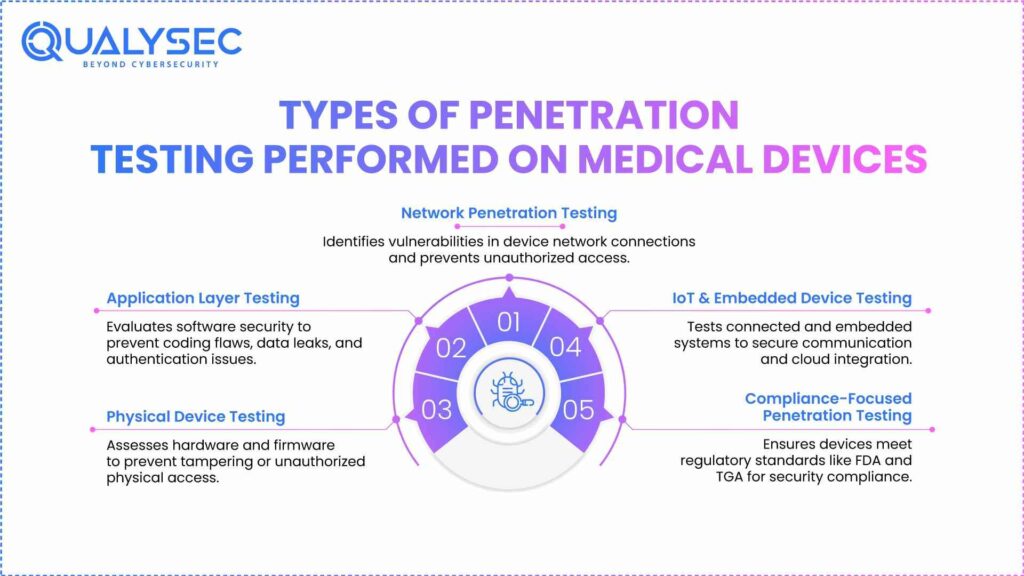
Penetration testing is an important phase to verify that medical devices are secure and meet their safety requirements for the TGA medical device regulations in Australia. Because medical devices are complex and tend to have increased connectivity, it is necessary to conduct various types of testing to assess vulnerabilities across all components of a medical device.
1. Network Penetration Testing
Network penetration testing assesses a device’s security posture based on its connection to networks. It simulates an attack on the device to determine if there are points of unauthorized access. As devices become more connected to the network, network testing is critical to ensure you are aware of the risk of hacking and are able to keep the device in compliance with safety requirements.
2. Application Layer Testing
Application layer testing specifically focuses on determining the security of the software applications for medical devices, such as mobile applications or cloud-based applications. This testing provides opportunities to identify vulnerabilities due to insecure coding, data leakage, and authentication issues, never leaving the device as a vector for a malicious cyberattack, demonstrating both patient data protection and the device’s integrity.
3. Physical Device Testing
Physical device testing involves assessing the device’s hardware components to discover any potential physical vulnerabilities in medical device security. This also includes scrutiny of ports, interfaces, and firmware to prevent access through physical means. Because access to the physical components of medical devices can enable serious compromise of security, this testing will help protect a medical device when performed thoroughly.
4. IoT and Embedded Device Testing
With the abundance of Internet of Things (IoT) devices in healthcare, testing the IoT-connected systems is critical to the security of these medical devices. IoT penetration testing identifies the security of embedded hardware, wireless communication, and cloud integration in a medical device system. This testing helps to identify vulnerabilities and the potential for exploitation of devices in the integrity of the healthcare ecosystem to operate devices.
5. Compliance-Focused Penetration Testing
Compliance-focused penetration testing satisfies testing that meets specific regulatory requirements, such as the Therapeutic Goods Administration (TGA) in Australia or the Food and Drug Administration (FDA) in the United States. This type of testing involves performing assessments on the manufacturer’s process of meeting industry standards and/or regulatory guidelines, along with documented evidence of compliance.
Download our Sample Penetration Testing Report to understand how we report and mitigate vulnerabilities.
Latest Penetration Testing Report

Best Practices for Penetration Testing in Medical Devices
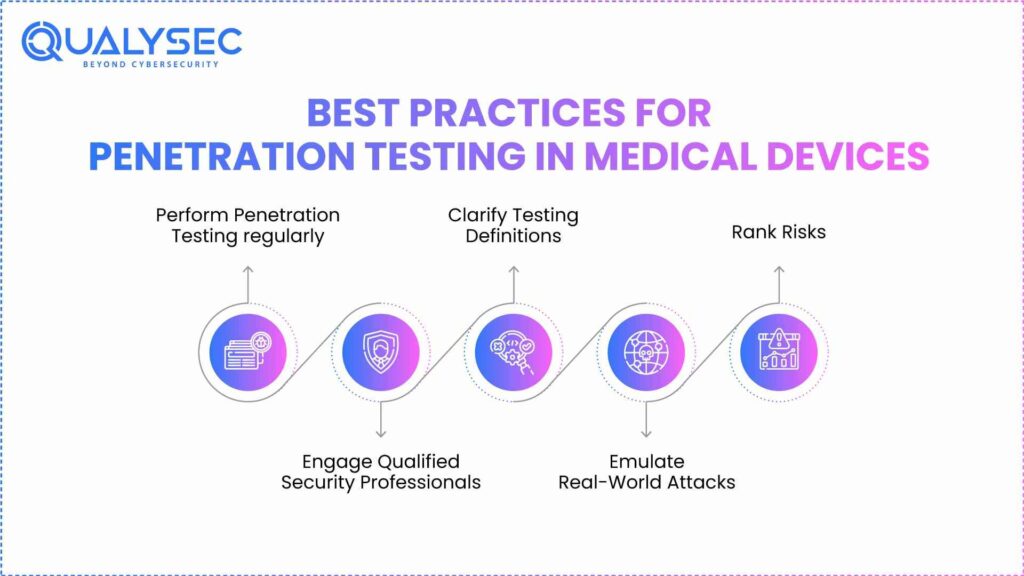
Penetration testing is a critical element of securing medical devices. As devices continue to evolve and grow in complexity and connectivity, simple security assessments are no longer sufficient. Adhering to best testing practices helps identify and rectify vulnerabilities while protecting patients and maintaining regulatory compliance.
1. Perform Penetration Testing regularly
Testing should be performed regularly to address any potential vulnerabilities proactively. The healthcare industry has shown proficiency in responding to major vulnerabilities. However, as with most industries, addressing any vulnerabilities occurs relatively slowly and is time-consuming within the healthcare industry. Continuous penetration testing helps to identify deficiencies more quickly and improve device security.
2. Engage Qualified Security Professionals
Testing should be completed by individuals who have expertise in both medical devices and cybersecurity. These professionals are likely to uncover issues that a novice tester may overlook and also ensure that testing conforms to industry guidelines and standards.
3. Clarify Testing Definitions
Before testing, it will provide clarity as to what will be assessed. The scope of assessment includes device hardware, software, and networking. Defining the boundaries of testing will generate assurance that we encompass all critical components in testing and omit nothing of significant consequence.
4. Emulate Real-World Attacks
Testing should simulate actual cyberattacks, which will give insights into how the device would respond. This allows for the discovery of genuine vulnerabilities and how an attacker may attempt to take advantage of weaknesses in the device.
5. Rank Risks
Some vulnerabilities are more significant than others. When vulnerabilities are discovered, they must be ranked based on their probability of being exploited and the severity of the consequences. This then allows for prioritisation of remediation so resources can focus upfront on the highest-risk vulnerabilities.
Discover how leading companies secure medical devices – Explore Our Case Studies!
Conclusion
Penetration testing is a crucial aspect of both the development and ongoing maintenance of medical devices, not merely a regulatory mandate under the Australian TGA Medical Device Regulations, but also a foundational aspect of patient safety, device quality, and consistency within a medical device’s device design history file.
Manufacturers who identify and remediate cybersecurity weaknesses and knocks before they become an issue otherwise known as ethical hacking. Theses are following best practices and ensuring compliance with some of the TGA legislation.
Ongoing (and preferably, regular) penetration testing is an important part of maintaining the security and integrity of a medical device in a world where connected health is becoming an increasingly prominent part.
Talk to Our Cybersecurity Experts to see how we can help you meet Australia TGA medical device security standards.
Our experts at Qualysec have helped secure fintech, SaaS, and enterprise systems across 25+ countries. Manual + Automated Pentesting. No false positives. Actionable reports.

FAQ’s
1. What is the Therapeutic Goods Act for medical devices?
The Therapeutic Goods Act 1989 is an Australian law that governs the safety, quality, and performance of therapeutic goods, including medical devices. It provides assurance that manufacturers, importers, and exporters supply medical devices in Australia to the highest standards to protect public health.
2. What is regulation 4J of the Medical Device Regulations 2002?
Regulation 4J requires medical device manufacturers to develop and implement a risk management framework that includes measures to ensure the medical device is safe, effective and meets compliance with essential principles. It also states the need to conduct an ongoing proactive risk assessment process during the medical device lifecycle.
3. What regulations apply to medical devices?
Medical devices in Australia are governed by the Therapeutic Goods Act 1989 and the TGA Medical Device Regulations 2002. These regulations encompass essential principles, risk management, and codes for manufacture and surveillance.
4. What are the three main categories of therapeutic goods?
The three main categories of therapeutic goods include medicines, which encompass drugs and pharmaceuticals; medical devices, covering instruments, apparatus, or software used for medical purposes; and biologicals, which consist of products derived from living organisms, such as vaccines, blood products, and tissues.
Got Questions About Australian Therapeutic Goods Medical Devices Regulations 2002? Chat Instantly with Our AI Chatbot!

























































































































































































































































































































































































































































































































































































































0 Comments