A cybersecurity assessment is an urgent assessment exercise that examines the digital security posture of your organisation. Organisations are increasingly pressured to deliver sensitive information and operational resiliency in the UK, where cyber threats are changing faster than ever. Cybersecurity assessment is a systematic means to discover vulnerabilities, evaluate threats, and enhance security in your online environment.
The UK digital environment has undergone significant changes, and firms are becoming increasingly reliant on technology in their day-to-day activities. This e-change has its prospects and threats. UK organisations are facing increasingly complex attacks by cybercriminals, and periodic security assessments are crucial. A detailed security assessment helps organisations understand their current security posture and develop effective defence mechanisms.
UK organisations in all sectors are finding the need to be proactive in security. Whether healthcare providers operate with patient data on one hand or financial institutions on the other, all organisations require frequent security reviews. The IT security risk assessment process enables a business to stay ahead of current threats and meet regulatory compliance requirements.
What Does a Cybersecurity Assessment Include in the UK Context?
An essential cybersecurity risk assessment in the UK is a multifaceted framework that aims to assess the security stance of your organisation using a variety of elements. A comprehensive security picture is provided through the assessment process, which evaluates the technical infrastructure, human factors, and organisational processes.
The technical assessment involves analyzing network architecture, system configurations, and application security checks. Under the network security assessment, security professionals investigate firewalls, intrusion detection systems, and encryption implementations to ensure optimal security. Such a technical review identifies potential points of entry that cybercriminals may use.
Core Components of UK Cybersecurity Assessments
- Infrastructure Analysis: Examination of network architecture, server configurations, and endpoint security measures.
- Policy Review: Analysis of current security policy, procedures, and governance structures.
- Compliance Verification: Evaluation in accordance with UK laws, such as the GDPR, NIS Regulations, and other industry-specific regulations.
- Human Factor Analysis: Review of employee training, awareness programmes, and security culture.
- Incident Response Planning: Evaluation of current response procedures and crisis management capabilities
- Third-Party Risk Evaluation: Assessment of vendor security practices and supply chain vulnerabilities
The data classification, data handling procedures, and protection mechanisms are the areas of the information security risk assessment component. Organisations in the UK need to demonstrate that they have adhered to data protection rules while maintaining efficiency. This balance requires close consideration of the flow of data, access control, and monitoring systems.
Risk assessment is an important component of assessment. Security professionals define potential threats, analyze their risk, and determine the possible impact on the business. This risk assessment for cybersecurity assists organisations in prioritising investment in security and managing resources.
Read also: Cybersecurity Risk Assessment Report: What It Is?
Our experts at Qualysec have helped secure fintech, SaaS, and enterprise systems across 25+ countries. Manual + Automated Pentesting. No false positives. Actionable reports.

How Do Cybersecurity Assessments Benefit UK Organisations?
The information security risk assessment aspect involves data classification, handling processes, and protection measures. Organisations in the UK are required to demonstrate their adherence to data protection laws while ensuring operational efficiency. This balance entails a close consideration of data flows, access controls, and monitoring systems.
Assessment involves the assessment of risk. Security professionals identify potential threats, assess their likelihood, and evaluate the potential business impact. This Cybersecurity risk management process assists organisations in placing security investments as a priority and resource allocation.
Key Benefits for UK Businesses
Systematic assessment processes make regulatory compliance achievable. UK organisations are subject to different security regulations based on their sectors and operations. The process of cybersecurity assessment services guarantees compliance with:
- GDPR Requirements: Data protection and privacy regulations
- NIS Regulations: Network and information systems security measures
- Financial Services Regulations: Sector-specific security requirements
- Healthcare Standards: Patient data protection and system security
- Government Standards: Public sector security frameworks
- Industry Guidelines: Sector-specific best practices and standards
The identification and closure of security gaps lead to better business continuity. A comprehensive network security assessment identifies potential areas of interruption and enables proactive mitigation. When appropriate assessments are applicable in guiding the preparation processes, organisations in the UK can continue their operations even in the event of a security incident.
Customer trust and reputation protection emerge as significant benefits. UK consumers increasingly value data security and privacy protection. Organisations that demonstrate a commitment to security by conducting regular assessments develop a stronger relationship with their customers and gain competitive advantages.
Insurance benefits are usually based on a complete security examination. A significant number of UK insurance providers offer discounted premiums to organisations that demonstrate good security practices. The documentation of the information security risk assessment supports insurance applications and claims.
You might like to read about Application Security Risk Assessment -Step By Step Guide.
What Are the Essential Steps in Conducting a Cybersecurity Assessment?
The cybersecurity assessment is systematic to achieve thorough analysis and a response plan. UK organisations have the advantage of adopting set methodologies that are in line with national security frameworks and industry best practices.
The first planning and scoping form the basis of the assessment. This step establishes goals, identifies resources to analyze, and outlines a schedule to be followed during the evaluation. UK organisations need to take into account the regulatory demands, business goals, resource constraints and the importance of investing in cybersecurity during the planning process.
Step-by-Step Assessment Process
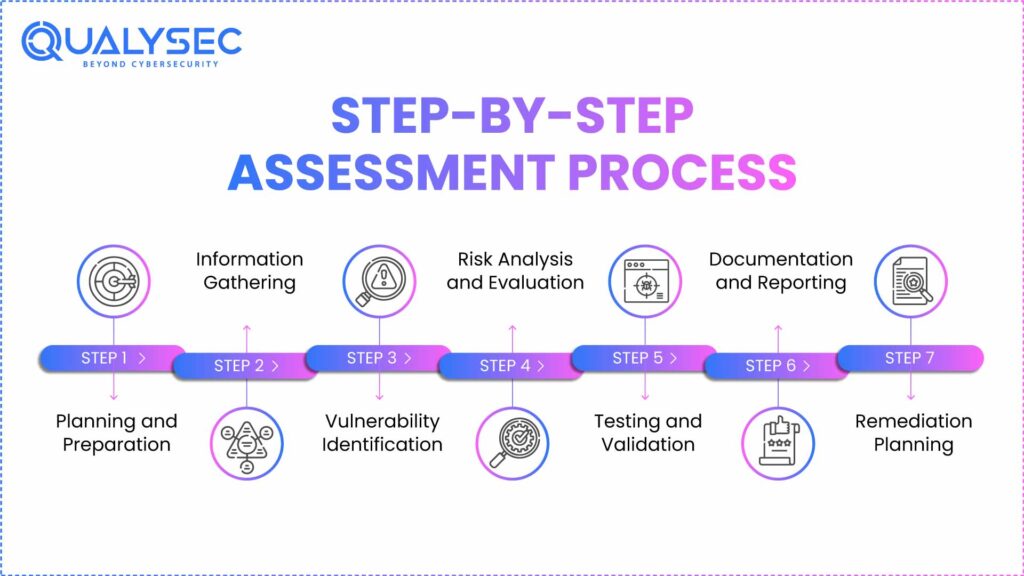
Step 1: Planning and Preparation
The assessment team defines scope, objectives, and success criteria. This involves determining the critical assets, systems, and data that must be evaluated. The planning is informed by UK-specific regulations/compliance requirements.
Step 2: Information Gathering
The security professionals will gather technical documentation, policy information, and system configurations. This scanning phase of cybersecurity risk assessment involves conducting interviews with key staff and evaluating the current security systems.
Step 3: Vulnerability Identification
Technical scanning and manual testing are conducted to identify potential security vulnerabilities. The network security assessment element examines the vulnerabilities of the infrastructure, while application testing helps identify risks in the software.
Step 4: Risk Analysis and Evaluation
Identified vulnerabilities are evaluated and analyzed to determine their potential business impact. This risk assessment for cyber security takes into account threat probability, asset value, and current controls.
Step 5: Testing and Validation
Penetration testing and control vulnerability validation are proven. The UK assessment standards should be tested adequately so that appropriate results and recommendations can be made
| Assessment Phase | Duration | Key Activities | Deliverables |
| Planning | 1-2 weeks | Scope definition, resource allocation | Assessment plan, methodology |
| Information Gathering | 2-3 weeks | Documentation review, interviews | Asset inventory, current state analysis |
| Vulnerability Assessment | 3-4 weeks | Technical scanning, manual testing | Vulnerability report, risk matrix |
| Risk Analysis | 1-2 weeks | Impact evaluation, risk scoring | Risk assessment report |
| Testing & Validation | 2-3 weeks | Penetration testing, control validation | Test results, proof of concepts |
| Reporting | 1 week | Report compilation, recommendations | Final assessment report, action plan |
Step 6: Documentation and Reporting
Comprehensive reporting presents findings, risk levels, and remediation recommendations. UK organisations are provided with comprehensive documentation to support compliance initiatives and security enhancements.
Step 7: Remediation Planning
Security professionals develop prioritized action plans to address the identified vulnerabilities. The result of this information security risk assessment informs resource allocation and the implementation schedule.
Get your Cybersecurity Assessment today and download a sample penetration testing report to see how it works.
Latest Penetration Testing Report

Why Choose Qualysec as Your Cybersecurity Assessment Partner in the UK?
Qualysec is the best option for a cybersecurity assessment services provider in the UK, offering the most expertise and a comprehensive range of evaluations. Our group of qualified security experts is familiar with the special challenges to UK organisations and can provide specific businesses with assessment solutions.
We have a proven track record of navigating UK regulatory frameworks, ensuring your cybersecurity risk assessment meets all relevant compliance requirements. Qualysec partner with organisations in various industries, including financial services and healthcare, with industry-specific knowledge that is unavailable to generic suppliers. We are aware of the threats and regulations in the UK and the business environment in the UK, which gives us a competitive advantage over international competitors.
Qualysec’s approach to methodology integrates state-of-the-art technology and human skills to provide comprehensive network security assessment findings. We employ high-tech scanners, manual testing methods, and our own assessment systems to detect vulnerabilities that other systems may overlook. The method we use ensures full coverage and minimal business interruption during the assessment.
Why UK Organisations Choose Qualysec
- Local Expertise: Deep understanding of UK regulations, threats, and business environment
- Certified Professionals: Team of qualified security experts with relevant UK certifications
- Comprehensive Coverage: End-to-end assessment services covering all security domains
- Tailored Approach: Customised assessment methodologies matching your business needs
- Rapid Response: Quick turnaround times with detailed, actionable reporting
- Ongoing Support: Continuous guidance through remediation and improvement processes
This client-centered nature of our services means that each information security risk assessment is as valuable as possible. Together with your team, we work to understand your business goals, risk preferences, and operational constraints. This partnership brings on board workable proposals that enhance security without compromising business processes.
The reporting from Qualysec provides meaningful information that is practical and can be utilized by both technical and executive teams. We provide our risk assessment for cybersecurity reports, which consists of an executive summary, technical details, and a roadmap of remediation prioritized by risk. This comprehensive documentation supports compliance efforts, insurance applications, and internal security initiatives.
Schedule a free consultation with Qualysec today to discover how our expert team can strengthen your organisation’s security posture through comprehensive assessment services.
Conclusion
Cybersecurity assessment is an essential investment for organisations in the United Kingdom struggling with the changing digital landscape and evolving digital attacks. The evaluation process provides critical information on security posture, as well as additional support for compliance and business continuity planning. Frequent assessments help organisations stay ahead of new threats and keep stakeholders confident.
UK businesses conduct systematic cybersecurity risk assessment operations that promote the identification of vulnerabilities before criminals can exploit them in their favor. The systematic method will also ensure full coverage and provide actionable information that can be used to secure improvements. The professional assessment services offer skills and objectivity of competent evaluation.
The returns on investing in professional cybersecurity assessment services are measurable in the form of prevented incidents, improved compliance, and increased business resilience. UK organisations that decide to adopt holistic assessment strategies position themselves for sustained success in an increasingly digital business world.
Contact our security experts to begin your comprehensive cybersecurity assessment journey and protect your organisation’s future.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
FAQ
1. What is included in a cybersecurity assessment?
A cybersecurity assessment is a thorough examination of the technical infrastructure, security policies, employee training programs, and compliance. The discussion examines app security, network configurations, data security, and the ability to respond to incidents. The cyber security risk assessment also includes vulnerability scanning, penetration testing, and a business impact analysis to provide a comprehensive assessment of the security posture.
2. What are the 5 C’s of cybersecurity?
The 5 C’s of cybersecurity represent core security principles: Confidentiality, Integrity, Availability, Compliance, and Continuity. It is these that fuel the information security risk assessment processes, rendering them comprehensive in their scope of security coverage. These are the principles used to design cybersecurity assessments by organisations in the UK, addressing all significant security spheres while adhering to regulations.
3. What are the 5 steps to a cyber security risk assessment?
There are five essential steps that include
- identification and scope definition of assets,
- identification of threats and vulnerabilities,
- risk analysis and evaluation of the impact,
- creation of a risk mitigation strategy,
- monitoring and review processes.
It is a network security assessment that offers systematic analysis and ultimate improvement. This will be a systematic method of risk assessment for cyber security activities to give the results of the exercise the consistency and dependability it merits.
4. What are the three main types of security assessments?
The three most used tests include vulnerability tests, penetration tests, and compliance audits. Vulnerability testing assists in determining security vulnerabilities, penetration testing ensures that these vulnerabilities exist, and compliance audits verify that regulations are followed. Each of the types is applicable in the comprehensive cybersecurity assessment programmes. In the United Kingdom, organisations are more likely to combine such approaches to address the information security risk assessment.
Schedule a meeting with our cyber security expert to understand advanced assessment methodologies and enhance your security program.























































































































































































































































































































































































































































































































































































































0 Comments