In the modern age of digitization, the issue of application security in cybersecurity has become an important subject of interest to Indian businesses across all sectors. With the ongoing development of cyber threats targeting software applications more than ever, organisations must realise the need to protect their digital assets. Application security in cybersecurity is a comprehensive strategy to protect software applications against various cyber threats throughout their entire lifecycle.
The Indian online economy is soaring high, and millions of firms use web applications, mobile apps, and software programs to serve their customer. Yet, with that digital transformation comes some serious security challenges, as well. Hackers are continually seeking weaknesses in applications to steal confidential information, disrupt or cripple business processes, or gain unauthorized access to business systems.
Learning about cybersecurity means that you are likely interested not only in safeguarding technological assets but also in protecting your business reputation, customer trust, and financial position. This paper will discuss the importance of application security, its significance to your business, and how to provide adequate application security.
What Is Application Security and How Does It Work?
Application security in cybersecurity is the act of securing computer programs against external threats and vulnerabilities. It entails invoking various aspects of security measures, tools, and processes to ensure the application’s safety throughout the development, deployment, and maintenance processes.
Understanding the Basics
The application security operates by incorporating several security levels into the product lifecycle of an application. This involves employing secure coding techniques, conducting frequent vulnerability tests, and maintaining constant monitoring. The aim will be to identify vulnerabilities that malicious users can exploit before they are even discovered.
Various techniques are adopted to ensure the protection of software systems in cybersecurity applications:
- Authentication and Authorisation: Make sure that only allowed users have access to particular resources in an application
- Data Encryption: Encryption of sensitive information so that it won’t be understandable to unauthorised individuals
- Input Validation: Ensure that malicious code has not infiltrated the user inputs.
- Security Testing: Regular assessment of applications for vulnerabilities
- Access Controls: Managing who can access what resources within the application
- Monitoring and Logging: Continuous tracking of application activities for suspicious behaviour.
How Application Security Functions
The application security process begins at the application development stage and continues throughout the application’s life cycle. Security is established at the developer level through safe coding methods, as well as regular assessments by security teams, which are performed using customised cybersecurity apps and tools.
| Security Phase | Key Activities | Tools Used |
| Development | Secure coding, code reviews | SAST tools, IDEs with security plugins |
| Testing | Vulnerability scanning, penetration testing | DAST tools, security scanners |
| Deployment | Configuration security, access controls | WAFs, monitoring tools |
| Maintenance | Updates, patches, monitoring | SIEM systems, vulnerability management |
Contemporary cybersecurity application security utilizes automated tools that can easily detect vulnerabilities and provide guidance on how to repair them. These devices are used in conjunction with human expertise to create an all-encompassing security system.
“Discover the best Application Security Testing Tools here.
Why Is Application Security Critical for Indian Businesses?
Indian businesses are exposed to special cybersecurity issues, which render application security in cybersecurity more important. The high rate of digitalization in business processes and the evolving cyber threat form a deadly combination, whose resolution must include robust protection mechanisms.
Growing Cyber Threats in India
India has witnessed a significant rise in cyberattacks on business applications. All kinds of organisations, whether small startups or large enterprises, are not immune to these threats. Cybersecurity web application attacks are a concern due to their exposure via the internet and the sensitive transfer and accessibility of customer information that they entail.
The loss related to the security breach is crippling to the business of India:
- Direct Financial Losses: Covers ransom payments and the cost of recovery and time spent with a system out
- Regulatory Penalties: A backlog of heavy fines has been imposed on those who fail to comply with laws governing data protection.
- Reputation Damage: This includes the consequences of losing the trust of your customers, which can impact the long-term growth of your business.
- Operational Disruption: Security Incidents can lead to the paralysis of a company’s activities for days or even weeks.
- Legal Consequences: A breach of data may lead to lawsuits against the individuals who are impacted.
- Competitive Disadvantage: When security incidents occur, it may lead to competition in the market.
Regulatory Compliance Requirements
Indian businesses are required to adhere to several regulations that necessitate intensive application security controls. The Information Technology Act, 2000, and the Personal Data Protection Bill outline obligations that an organization must meet to provide sufficient protection for sensitive data.
Its role in compliance requires businesses to deploy cybersecurity, enabling them to develop apps for cybersecurity, so that they can implement automated monitoring and reporting, as well as management capabilities for vulnerabilities. Consistent security evaluation and reports go a long way in ensuring the company is compliant with regulatory bodies.
“Learn more about What is Application Security Compliance.“
Customer Trust and Business Reputation
Customer trust is a crucial component in the competitive Indian market. A single security breach has the potential to destroy years of building the brand and relationships with the customers. Having adequate application security as part of your cybersecurity practices will demonstrate your commitment to addressing security concerns related to customer data and privacy.
Schedule a free consultation with Qualysec to understand how application security can protect your business reputation and customer trust.
What Are the Different Types of Application Security Testing in Cybersecurity?
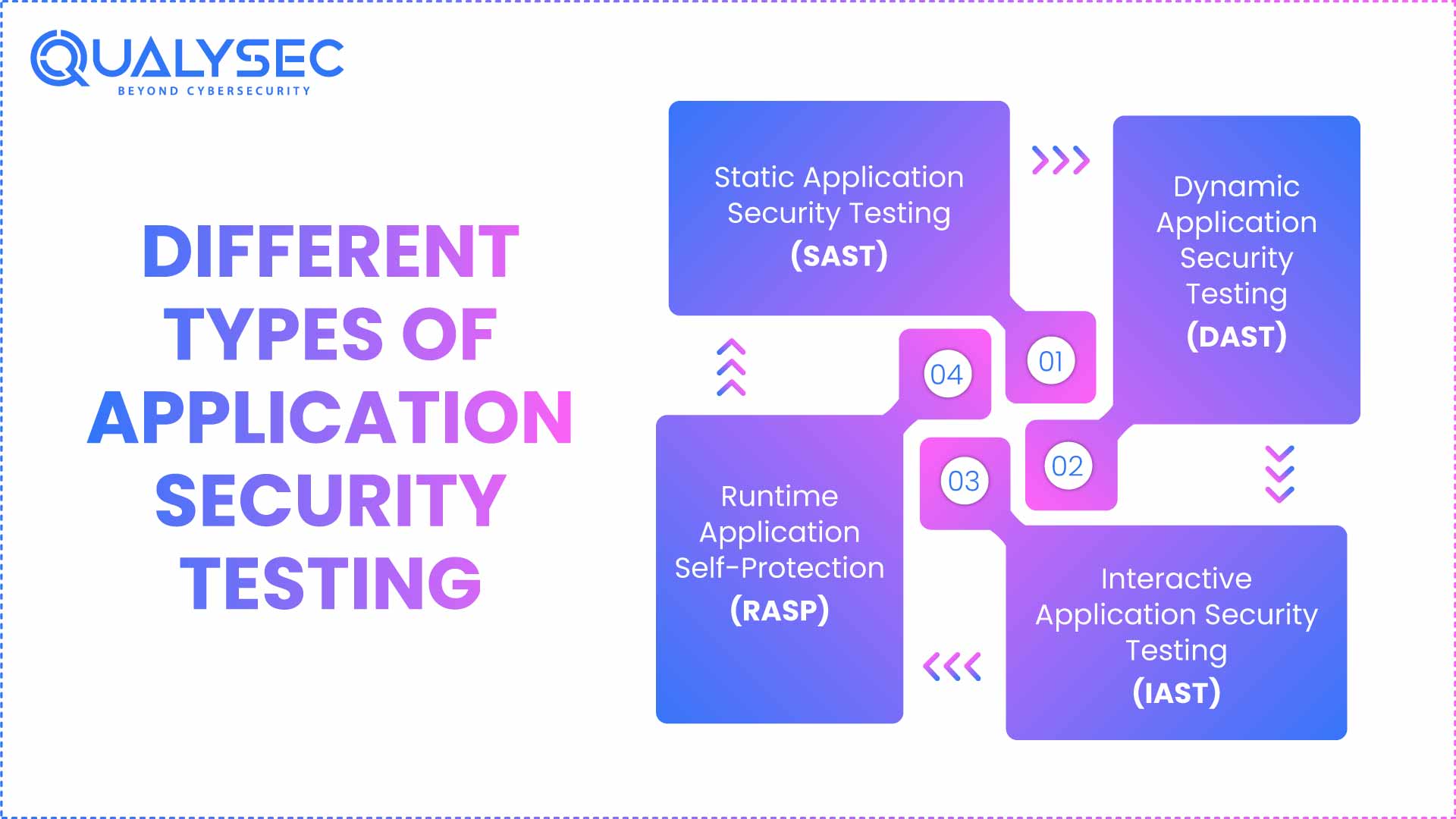
Learning about the various forms of application security tests is crucial in developing a comprehensive application security strategy. The two different testing methods are relevant in other contexts and provide information about the security status of your application in their own unique ways.
Static Application Security Testing (SAST)
SAST examines the source code without running the program. This white-box testing can help detect security flaws at an early stage of development. The best apps for cyber security tend to have SAST functionalities that can spot weaknesses such as SQL injection, cross-site scripting weaknesses, and buffer overflow.
The main advantages of SAST include:
- Early detection of vulnerabilities during development
- Comprehensive code coverage analysis
- Integration with development environments
- Reduced the cost of fixing security issues
“Explore more about Static Application Security Testing.“
Dynamic Application Security Testing (DAST)
DAST tests applications that are running and detects vulnerabilities that are unidentified in the static analysis phase. This is a black-box testing procedure that models real-life attacks on live applications. DAST cybersecurity apps can find problems at runtime, such as authentication, server settings, and injections.
“Explore more about Dynamic Application Security Testing.“
Interactive Application Security Testing (IAST)
IAST combines elements of both SAST and DAST by analysing applications from the inside during execution. This approach provides real-time feedback on security issues as the application runs. Cybersecurity application security companies that include IAST capabilities offer more accurate vulnerability detection with fewer false positives.
Runtime Application Self-Protection (RASP)
The RASP technology is directly embedded within the applications to protect them against attacks as they occur. In contrast to conventional security systems that operate on the exterior, RASP is more in-depth, and the system can automatically block malicious behavior.
| Testing Type | Execution Method | Key Benefits | Limitations |
| SAST | Code Analysis | Early detection, comprehensive coverage | May miss runtime issues |
| DAST | Running application | Real-world attack simulation | Limited code visibility |
| IAST | Runtime analysis | Accurate results, low false positives | Requires instrumentation |
| RASP | Integrated protection | Real-time blocking, continuous monitoring | Performance impact |
Download our comprehensive penetration testing report to understand how different testing methods can be applied to your applications.
Latest Penetration Testing Report

Why Choose Qualysec as Your Best Application Security Partner in India?
When it comes to application security in cybersecurity, choosing the right partner can make all the difference for your business. Qualysec stands out as India’s leading cybersecurity company, specialising in comprehensive application security solutions that protect businesses across various industries.
Comprehensive Application Security Services
Qualysec offers a complete range of application security services designed specifically for Indian businesses. Our team of certified security professionals utilizes advanced cybersecurity applications and methodologies to identify vulnerabilities and provide actionable recommendations.
Our application security services include:
- Web Application Penetration Testing: Comprehensive evaluation of applications programmed, such as web applications, for security issues.
- Mobile Application Security Testing: Testing of iOS and Android Apps in depth.
- API Security Testing: Analysis of API endpoints and security controls.
- Source Code Review: Manual and automated source code analysis of applications.
- Cloud Application Security: Specialised testing for cloud-deployed applications
- DevSecOps Integration: Seamless integration of security into development processes
Advanced Security Testing Methodologies
Qualysec employs cutting-edge apps for cybersecurity and proven methodologies to deliver accurate and comprehensive risk assessments. Our approach combines automated tools with manual testing expertise to identify both common and complex vulnerabilities.
We use industry-leading security testing tools and frameworks:
- OWASP Testing Guidelines
- Advanced vulnerability scanners
- Custom security testing tools
- Manual penetration testing techniques
Proven Track Record with Indian Businesses
With several years of experience serving enterprises, startups, and government organisations in India, Qualysec is aware of the type of security that hampers enterprises in India. Our team has won successfully in different sectors, which include:
- Banking: Banking solutions, fintech systems, payment gateways
- E-commerce: Internet shop, trade applications
- Medical: patient management systems, medical applications
- Government: citizen services portals, administrative systems
- Technology: SaaS, enterprise apps
Expert Team and Certifications
Our security experts are certified with globally accepted credentials, including CEH, CISSP, OSCP, and GIAC. Such knowledge gives you confidence that applications have undergone the best quality security tests with the best apps for cybersecurity.
Localized Support and Understanding
Qualysec is an Indian firm, and thus, it has knowledge about the business practices of the area, the regulatory environment, as well as the cultural nuances. We support local languages and also adapt flexible models of engagement that can fit Indian business requirements.
Location: Multiple branches in leading Indian cities such as Mumbai, Delhi, Bangalore, and Pune
Services: End-to-end lifecycle management of application security
Talk with our security experts today to discuss your application security requirements and receive a customized security assessment plan tailored to your business.
Conclusion
Application security in cybersecurity is no longer an option to be considered by Indian businesses, but a need to be addressed. Cyber threats have become increasingly sophisticated and now target software applications more than they did in the past years. The organisation should thus ensure that adequate security safeguards are put in place to defend against the susceptibility of these digital assets, customer details, and business processes.
Effective app security will involve greater knowledge of the different methods of security testing, the implementation of correct security measures, and collaboration with experts in the security field. By investing in cyber security applications and adhering to the best practices, companies can hugely reduce the scope of the risk exposure level and nurture the confidence of the customers.
Keep in mind that application security cannot be eliminated once and for all. Correspondence evaluation, update, and scanning are applicable at a high security level. However, the amount of money spent to take the necessary precautions is never proportional to the possible outcomes of a security incident.
Take action today to secure your applications and protect your business. With a proactive mindset and consultation with a security professional, you can design an application security system that will evolve with the company and adapt to shifts in threats.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Frequently Asked Questions
1. What is application security in cybersecurity?
Application security in cyber security is the entire process of protecting software applications against all cyber threats throughout their life cycle. It entails the deployment of security standards, tools, and procedures to identify vulnerabilities and curb unauthorised access to applications. This would entail using safe coding methods, conducting consistent security testing, and maintaining constant monitoring of the applications to ensure they remain protected against evolving cyber risks.
2. What is the difference between application security and cyber security?
This is not a new concept in cybersecurity; however, in the realm of cybersecurity, application security is a unique aspect that deals specifically with matters of application security. Cybersecurity encompasses application security, network security, endpoint security, data security, and infrastructure protection. Application security, in particular, involves protecting web applications, mobile applications, and software systems against vulnerabilities and attacks that exploit application-layer weaknesses.
3. Which application is used for cyber security?
Various cybersecurity apps are employed to protect and evaluate application security. These include Static Application Security Testing (SAST) tools, such as SonarQube and Checkmarx; Dynamic Application Security Testing (DAST) tools, including OWASP ZAP and Burp Suite; and all-purpose cyber security applications, such as the Qualysec security testing platform. The best apps for cyber security typically integrate multiple methodologies to maintain overall application protection and vulnerability management.
4. What are the common application security threats?
Database attacks, cross-site scripting (XSS), broken authentication, insecure direct object references, and security misconfigurations, among others, are common application security threats. Cyber security web applications are both susceptible to cybersecurity attacks since they can be accessed over the internet. The other threats include injection vulnerabilities, broken access control, and inadequate logging and monitoring, which can be effectively addressed by implementing appropriate cyber security application security practices and conducting routine security testing.





















































































































































































































































































































































































































































































































































































































0 Comments