IT Vulnerability Assessment
The primary means of ensuring that companies are not vulnerable to cyber attacks in the year 2025 is through IT vulnerability assessment. The threats are increasing at a high rate, and the losses around the globe are increasing. Analysts believe that cybercrime will amount to 10.5 trillion dollars in 2025 and even 15.6 trillion by 2029. In the first half of 2025 alone, more than 23,000 additional CVEs (Common Vulnerabilities and Exposures) had been discovered.
Approximately 72 percent of companies in the world indicate that their cyber risk has increased this year. The company is increasingly being tightened on what it needs to report, test, and repair by rules like ISO 27001, GDPR, or the Australian APRA CPS 234. Over 160 critical weaknesses are being struck by the attackers- nearly 50 of them can be remotely accessed without any form of login. Due to this reason, companies cannot solely depend on traditional security practices. They require proactive and stepwise IT vulnerability testing to remain resilient and comply with regulations.
Book a verified IT vulnerability test with Qualysec Technologies and secure your company against any threats of tomorrow!
What Does an IT Vulnerability Assessment Mean?
IT vulnerability assessment examines every aspect of a company’s digital environment, such as network, applications, devices, and cloud accounts, to identify weaknesses, rank them, and categorize them. It demonstrates the points at which misconfigurations, available unpatched programs, outdated applications, weak passwords, or open ports exist. The evaluation offers a clear picture of risks and offers a plan to resolve issues, comply, and mitigate the risk in general. Risk management is mandatory and necessary in regulated sectors in which digital trust is of importance.
Important IT Vulnerability Testing
- Network vulnerability testing – Concentrate on routers, firewalls, switches, and services. They discover open ports, machines that are not supposed to be, and ill settings.
- Application vulnerability tests – Review web and mobile applications against attacks such as SQL injection, cross-scripting, and weak authorization.
- Cloud vulnerability testing – Scan virtual servers to identify compliance weaknesses, improperly configured access, and risk of data leakages, particularly with the trend where companies are shifting to the cloud.
- Endpoint and mobile device testing – Verify outdated operating systems, malware applications, and lax device policies. These are easy targets of malware and ransomware.
- Database vulnerability checks – Defend the most sensitive information by examining its storage practices, configuration, and security controls.
Explore more about What is Vulnerability Testing in Cyber security & How Does It Work?
IT Vulnerability Assessment Process
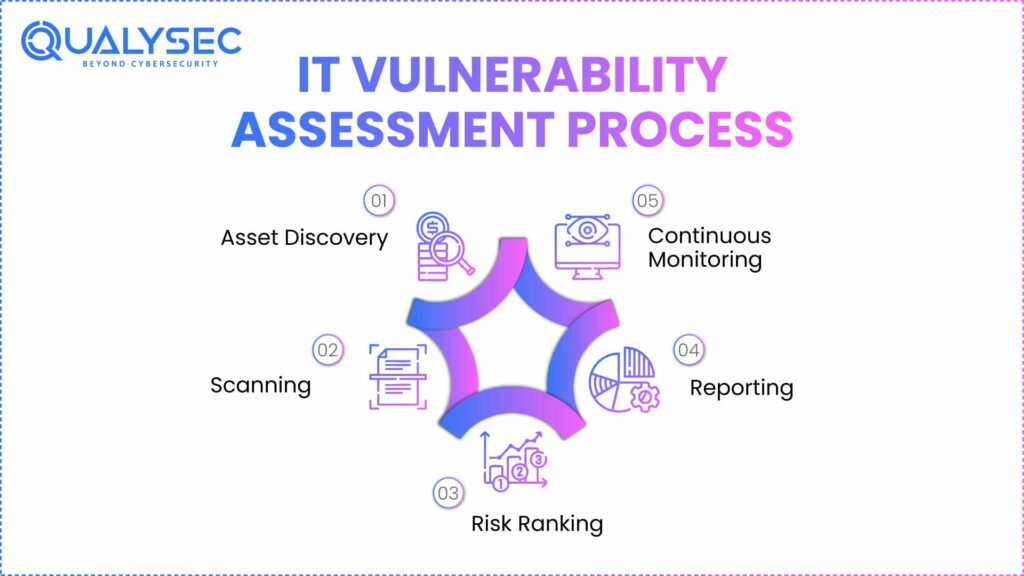
- Asset discovery and classification – Find all critical systems, apps, and devices that require protection.
- Vulnerability scanning – Nessus, Burp Suite, or Qualys, and also, manual testing can identify weaknesses, outdated software, and dangerous configurations.
- Risk assessment and ranking – Prioritize risks based on the magnitude of impact that might occur and ease of usage. After this, the fix is according to the areas of greatest risk.
- Reporting and remediation – Provide clear, actionable reporting that clarifies how to patch, reconfigure, or upgrade the security. Correcting the issues enhances compliance.
- Ongoing observation – Perform routine scans and real-time scans since new threats are continuously emerging and the system is ever-evolving.
Get your compliance-ready vulnerability report with Qualysec Technologies – contact our certified experts and schedule a tailored IT vulnerability assessment today!
Latest Penetration Testing Report

Top Tools to Use in IT Vulnerability Assessment
Nessus, OpenVAS, Rapid7 InsightVM, Qualys VMDR, and Burp Suite provide automated scanners that are broad and fast scanners of numerous layers. Penetration testing tools such as Metasploit, ZAP, and custom scripts replicate real attacks, and this helps prove that controls are resilient to real threats.
Dashboards consolidate findings in a single location and draw attention to the most important things. The automation accelerates the work. But human hands analyze the situation, remove false alarms, and customize fixes.
IT Vulnerability Assessment and Penetration Testing
| Aspect | IT Vulnerability Assessment | Penetration Testing |
| Methodology | Automated tools and manual inspection; broad scope | Manual attack simulation; focused, deep-dive analysis |
| Output | Risk-ranked vulnerability list and remediation guidance | Exploit evidence, business impact, prioritized fixes |
| Frequency | Regular (weekly to quarterly or after major changes) | Periodic (such as annually or after critical changes) |
| Goal | Identify and prioritize weaknesses for resolution | Assess system resilience against real-world threats |
Both are important. Evaluation reveals the areas of problems and prioritizes them. Vulnerability testing demonstrates the possibility of an attacker breaking in and assists in modelling actual attack tactics.
IT Vulnerability Assessment Best Practices

- Undergoes a scan of all essential assets and scans more frequently than after modification.
- Have a very strict patch schedule. Patch known bugs as fast as possible, especially after a new release of CVEs or proof-of-concept attacks.
- Educate trainers on security. Minimise human-related threats such as phishing and poor passwords.
- Check third-party suppliers and cloud providers to identify supply chain loopholes.
- Be aligned with the major standards like ISO 27001, GDPR, and SOC 2 to gain the confidence of the industry and audit preparedness.
The Vulnerability Assessment with Qualysec Technologies
About
Qualysec Technologies provides a structured, established methodology of IT vulnerability evaluation and hacks that is globally regarded as the benchmark of thoroughness, accuracy, and entrepreneurial survivability.
Services
Vulnerability assessment and penetration testing, cloud security, mobile and web applications testing, cyber security review, and incident response, all done both manually and automatically.
Why Qualysec Technologies is The Best Choice
- Each task is modeled using a proven workflow combining the best automated technologies and professional manual proves, uncovering human nature issues that scanners would not detect.
- Reports – Qualysec provides easy-to-understand compliance-ready reports that meet ISO 27001, GDPR, APRA CPS 234, SOC 2, and others. In both reports, you can see precise remediation measures and risk priorities in business terminology.
- Fixes – The strategy addresses risk on both the technical level, process, and policy levels, and ensures that clients are safe because the threats are increasing. Companies receive an option that is compatible with local regulations and compliance requirements, sealing security vulnerabilities of any regulated industry and start-ups developing at a high pace.
- Client-first – Qualysec serves customers with evaluation and post-test guidance, which is of the highest quality. The outcome is hardening, audit-ready compliance, and reduction of risk to finance, utilities, government, healthcare, among other sectors across the globe.
See Why Clients Trust Qualysec — Read Our client Reviews.
Conclusion
The future role of cyber risk management in 2025 is based on IT vulnerability analysis. It offers the necessary visibility, assists in compliance, and establishes operational resilience at the moment of threats and scrutiny at an unprecedented level. Hackers vary in tricks, patches have to be more timely, and the online world continues to grow. Conducting regular IT security threat assessment, through professional assistance of reputed partners such as Qualysec, is now the only means of having a safe business.
Don’t Wait for a data breach — Talk to Our Cybersecurity Specialists Today.
Our experts at Qualysec have helped secure fintech, SaaS, and enterprise systems across 25+ countries. Manual + Automated Pentesting. No false positives. Actionable reports.

FAQs
1. What is an IT vulnerability assessment?
An IT vulnerability assessment is an active and scheduled test that seeks vulnerabilities in computer systems, software, and networks. It identifies and prioritizes these security gaps such that a company can close them before attackers leverage them. This enhances cyber defenses and also ensures that the organization is adhering to the evolving security regulations.
2. What is the ISO 27001 vulnerability assessment?
Part of the ISO 27001 standard is an ISO 27001 IT security threat assessment. It causes a company to continue searching and remedying the lapses in the security of its information systems. Through regular scans, reviews, and corrections of issues, the company ensures that its data is not lost, damaged, or inaccessible at any time as per the international standards of security.
3. What are the three types of vulnerability assessments?
There are three primary cyber security vulnerability assessment, which include –
- Network-based – Verifies the infrastructure against issues.
- Application-based – Identifies vulnerabilities in web and mobile applications.
- Cloud-based – Identifies vulnerabilities in the cloud environments and access controls.
The two of them comprise a majority of digitized assets.
4. What is the difference between an IT audit and a vulnerability assessment?
An IT audit is a check on the policies, controls, and general compliance of a company. It is centered on the way things are done and whether they abide by the rules. A cyber security vulnerability assessment seeks actual technical deficits in systems and networks. It provides very precise steps to address those vulnerabilities and reduce cyber threats.
5. What should be the frequency of IT vulnerability assessment?
An IT vulnerability assessment should be undertaken by the companies at least every three months. In case it is a high-risk company or one with highly imposed rules, then it might require monthly or even weekly checks. Additional scans are also required whenever in major system changes or a software update.
6. Which industries are most appropriate for vulnerability assessments?
Finance, health care, government, utilities, technology, and critical infrastructure are some of the sectors that benefit. These areas contain sensitive information and execute key systems. This is why frequent scans reduce the risk and contribute to the fulfillment of the regulations and enhancement of cyber safety.
7. Does Qualysec provide vulnerability assessment services globally?
Yes. Qualysec Technologies provides custom IT vulnerability testing and penetration testing. Our organized system addresses the local compliance requirements and provides a complete security overview to ensure companies enhance their cyber protection and remain abreast of regulations.
Ready to secure your business? Schedule your next IT vulnerability assessment with Qualysec Technologies now!























































































































































































































































































































































































































































































































































































































0 Comments