The NIS2 Directive is the new legislative package that Europe intends to introduce to enhance cybersecurity levels in essential industries. The NIS2 directive EU is insisting on more tangible and verifiable defenses as the digital systems become more complex and cross-border attacks are on the rise. This means that NIS2 penetration testing is an essential part of compliance.
NIS2 EU compliance can also be required even to other companies based in the UK in case they provide services to EU citizens or operate digital services in any of the member states. The directive not only considerably expands on NIS1 but also includes more stringent controls, more rapid reporting of incidents, and even new governance and technical risk assessment needs.
The report has shown that more than 68 percent of organizations questioned via the EU had at least one incident involving cybersecurity that had a service impact or data leak, as well as surfaced within the past 12 months.
In this blog, we will describe what the NIS2 Directive is, what it means to businesses in the UK and EU, and why NIS2 security testing is necessary to test the security of your systems through structured penetration testing to be compliant and resilient.
What is the NIS2 Directive?
The current cybersecurity law in the European Union is the NIS2 Directive (Network and Information Security Directive,) replacing the previous NIS Directive of 2016. It is to be applied in January 2023, and member states must implement it in national law by October 2024. NIS2 aims to enhance the collective EU cybersecurity by creating consistent and aggressive risk-focused security standards in each of the essential and critical sectors.
Key Objectives of NIS2:
- Enhance cybersecurity of the government and the corporate.
- Minimize the fragmentation of cybersecurity requirements within the EU member states.
- Enhance the exchange of information and collaboration amongst nations and the concerned authorities.
- Establishing the minimum guidelines of incident response, supply chain security, and risk management practice.
Industries Affected:
EU NIS 2 directive significantly expands the scope of the original directive. It now covers more sectors and companies, categorizing them into:
- Essential Entities: Energy, transport, banking, healthcare, drinking and wastewater, digital infrastructure, public administration, and space.
- Important Entities: Postal services, food production, chemicals, waste management, digital providers, and manufacturing of critical products.
Key Requirements:
- Put in place effective technical and organizational protection against cybersecurity.
- Prepare in advance, conduct periodic risk assessment, and incident response planning.
- Report Cyber incidents not later than 24 hours.
- Safe channels of supply and third-party services.
- Have a team or individual who oversees compliance with NIS2.
The directive enforces higher accountability by introducing administrative fines for non-compliance, which can reach up to €10 million or 2% of global annual turnover, whichever is higher.
Looking for a partner that combines deep manual expertise with advanced tooling?
Qualysec’s Advanced Penetration Testing Services are purpose-built for critical sectors covered under NIS2. It offers high-impact simulation, threat modeling, and custom remediation support mapped to your industry risk profile.
Is NIS2 Applicable to UK-Based Businesses?
In the UK, even though it is outside the EU, NIS2 still may apply to businesses based in the UK, who provide services in the EU or to customers based in the EU. You might have NIS2 obligations, in case your company is in the category labeled as either essential or important according to the directive (e.g., cloud services, financial services, telecom, energy, logistics, etc.).
Scenarios Where UK Businesses Must Comply:
- You own digital infrastructure or services that are used by EU users.
- Your activities or affiliates are registered in any of the EU branches.
- You are a strategic supplier or third-party provider of an essential organization in the EU.
To sustain business in the market and ensure they do not suffer legal consequences, most UK companies are actively matching their own security policies and controls to the requirements of NIS2 even in the absence of direct voluntary obligation.
Unsure if NIS2 applies to your UK-based business? Get clarity with a detailed compliance readiness assessment from Qualysec. Explore Qualysec’s Compliance Services to map out your NIS2 cybersecurity obligations and stay audit-ready.
How Penetration Testing Supports NIS2 Compliance
NIS2 requires technical and organizational measures to be implemented by organizations to deter, detect and respond to cybersecurity threats. Penetration testing service have a direct bearing on fulfilling these requirements by providing physical evidence that your systems have been tested to determine their weak points before the attackers initiating their initial exploits.
Why Penetration Testing Matters for NIS2 Requirements:
- Proactive Risk Identification: Pen tests are a simulation of the activity of an actual attack exposure of flaws in infrastructure, software and settings. This is essential in achieving the NIS2 risk-based approach.
- Supports Article 21 Obligations: Article 21 (Article 21 NIS2) puts an obligation on conducting regular tests that comprise vulnerability management as well as cybersecurity hygiene. The best practice used to show due diligence is pen testing.
- Incident Readiness: Penetration testing assists in constructing the threat models and enforcing the response procedures. This enhances your capability in controlling or curbing probable incidents, which is one of the backbones of NIS2 conformity.
- Audit Trail and Documentation: Pen testing reports facilitate the effectiveness of audit-based audits of compliance for evidence of threat exposure analysis and steps to mitigate them. This is needed in the NIS2 reporting requirements.
Contrary to simple vulnerability scans, NIS2-aligned penetration tests are customized to the risks and dependencies of each sector, as well as sensitivity of the data involved. While penetration testing is vital to meeting NIS2’s expectations, it’s just as important to understand the specific security testing requirements laid out in the directive.
Download our Sample Penetration Testing Report to understand how vulnerabilities are reported and mitigated.
Latest Penetration Testing Report

NIS2 Security Testing Requirements
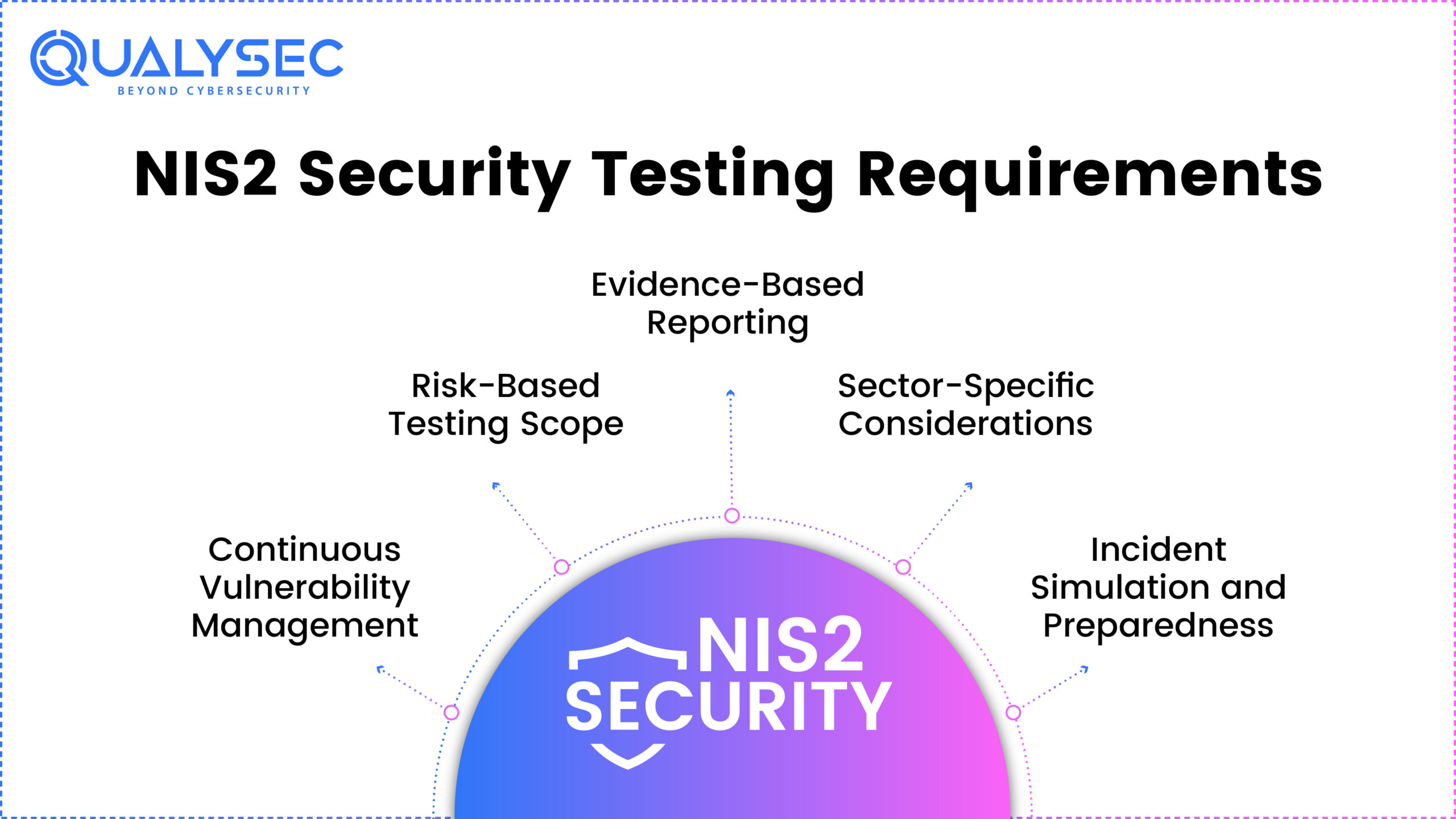
In addition to all-purpose security requirements, NIS2 specifies technical controls and their verification in the form of testing. They are not some indicative suggestions, but quantifiable requirements that the regulated organizations ought to follow.
- Continuous Vulnerability Management: The companies have to establish the systems that determine, evaluate, and settle shortcomings continually. These are timely patching and risk prioritization.
- Risk-Based Testing Scope: Security assessments should examine the threat landscape of an organization. We anticipate testing those systems that handle critical infrastructures, individual data, or civic services to a greater scale and more consistently.
- Sector-Specific Considerations: NIS2 acknowledges the fact that risk varies in industries. Organizations in energy, healthcare, finance, or digital services need a customized approach to their testing according to their operational dependencies and third-party integrations as well as the sensitivity of the collected data.
- Incident Simulation and Preparedness: Security testing needs to be stronger than simple scans and should consider red team exercises or simulation of breaching mechanisms or business continuity testing.
- Evidence-Based Reporting: A NIS2-compliant testing is required to yield well-organized documentation. Reports must show the scope, methodology, findings, exploit paths, and recommended mitigation in line with the checkpoints of compliance.
Need help aligning your cybersecurity strategy with NIS2?
Qualysec’s experts specialize in NIS2-aligned penetration testing that goes beyond basic scans. We combine sector-specific risk analysis, manual testing, and audit-ready reporting. Talk to Our Experts and get a tailored roadmap to compliance.
- Combines manual & automated testing for accurate results
- Runs 200+ industry-standard test cases
- Zero false positives – all findings are manually verified
- CI/CD integration for smooth DevSecOps workflows
- Get a real-time dashboard to track and manage vulnerabilities
- Receive developer-friendly reports with clear remediation steps
- Share publicly verifiable pentest certificates
- Supports compliance with SOC2, ISO27001, PCI-DSS, HIPAA, and more
- Trusted by startups to enterprises in Fintech, SaaS, Healthcare, and beyond

Common Pitfalls That Risk NIS2 Non-Compliance
NIS2 has technical expectations that many organizations do not achieve even after they have implemented them. The following are the most common and impactful gaps that arise during the penetration testing and audits:
- Incomplete Asset Discovery: Shadow IT or unmanaged endpoints or unmonitored APIs are often ignored by businesses. Such hidden assets will be a huge threat with regards to the visibility and risk assessment imposed by NIS2.
- Unpatched Systems and Legacy Applications: Several critical and important entities also deal with outdated software stacks. NIS2 requires vulnerability fixes fast, but old technology is not typically included in active patching programs.
- Weak Supply Chain Security: Companies fail to test the security posture of third-party vendors. Even when a supplier fails, you will still be accountable under the nis2 directive in cases where the businesses are mutually dependent.
- Lack of Multi-Factor Authentication (MFA): Access control failures that lack MFA or incorporate stale credentials is a red flag during the audits of NIS2, especially when it occurs in a remote or hybrid arrangement.
- One-Time or Superficial Testing: Yearly checkbox tests or automated scans only are not enough. NIS2 aims to conduct regular but realistic evaluations, usually simulating real-life threats, and thus requires both manual and automated patterns.
Struggling with hidden vulnerabilities or inconsistent compliance practices?
Even well-intentioned security efforts can fall short of NIS2 expectations. Qualysec’s IT Security Compliance Services identify blind spots, assess supply chain risks. And ensure that your systems meet both technical and governance-level mandates.
Best Practices for NIS2-Aligned Penetration Testing
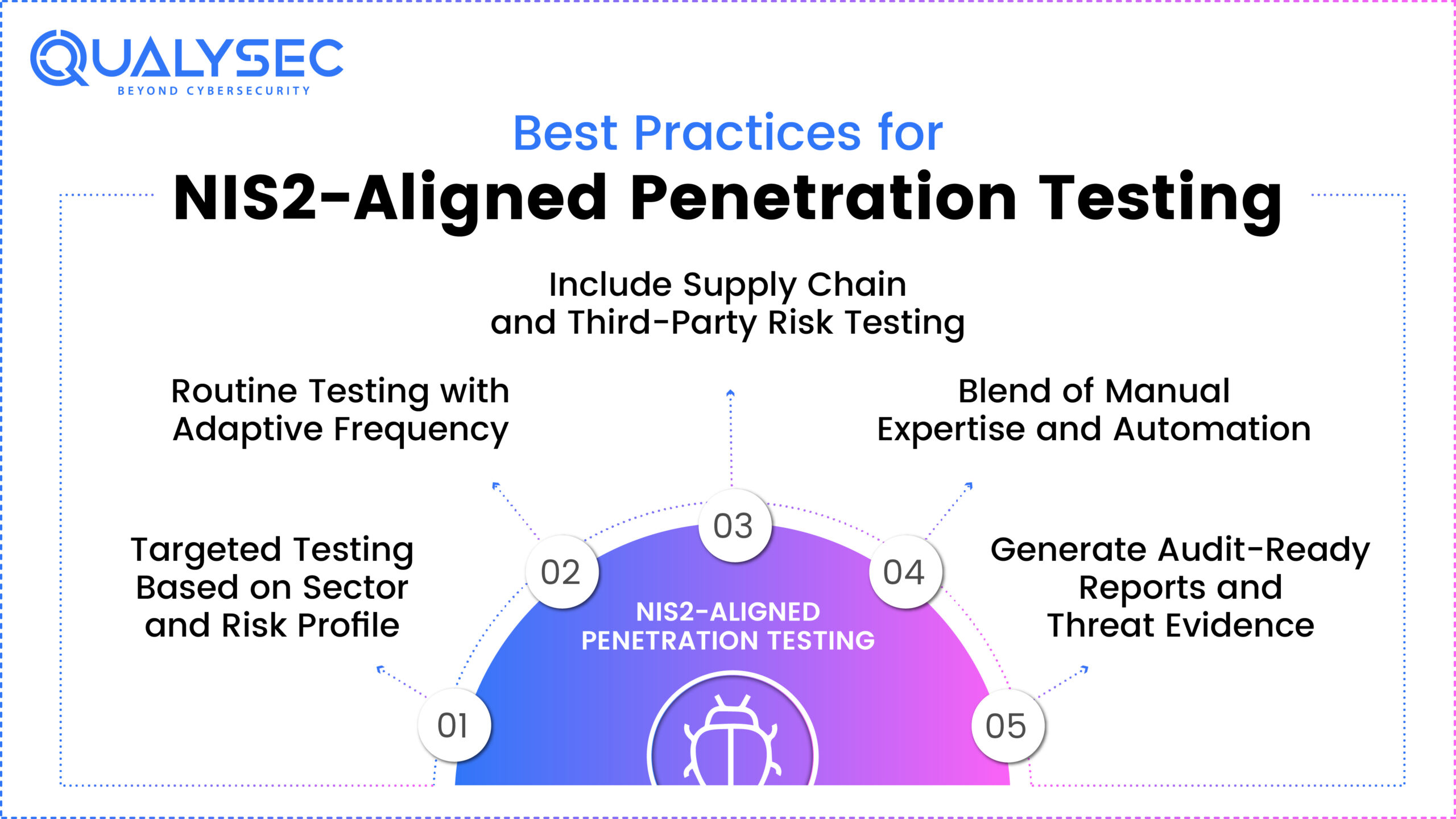
Issuing a framework to keep penetration testing in line with NIS2 is not a box of regulations. It is a positioning decision to reinforce actual-life online security. The following are the best practices that would be undertaken to conform to NIS2 anticipations:
- Targeted Testing Based on Sector and Risk Profile: Crucial and vital entities must scope tests on highly sensitive systems regarding data, open access systems, or those that have a bearing on the system operations. Pick health facilities, power plants, financial institutions, and other regulated areas.
- Routine Testing with Adaptive Frequency: Instead of annually-, default-testing, such a cycle should be dynamic and consider recent events, technology stack shifts, and risk coverage. There could be an assessment of critical infrastructure every quarter.
- Blend of Manual Expertise and Automation: Automated scan programs can find only surface-level problems and usually fail to identify chained vulnerabilities and flaws in business logic. Efficient testing teams, such as Qualysec, integrate automated solutions with extensive manual testing to achieve the high technical challenge required in NIS2.
- Include Supply Chain and Third-Party Risk Testing: NIS2 focuses on accountability by vendors and service suppliers. The second one is to make sure that your test scope addresses integrations, APIs, and third-party platforms where potential vulnerabilities may occur.
- Generate Audit-Ready Reports and Threat Evidence: Reporting should be provided in detail with the use of highly structured reports that provide exploit routes, business impact, and mapping to NIS2 framework controls. Such reports aid inspection, reporting incidents, and compliance checking.
Looking to engage an organization that has expertise in NIS2-aligned testing? Qualysec testing approaches are aligned with EU compliance frameworks and critical infrastructure resilience-aligned.
Conclusion
The NIS2 Directive brings about an overall demanding cybersecurity environment in the EU, particularly for essential actors that do business in critical sectors. NIS2 also lies under the realm of business requirement by UK firms that have EU clients or work with EU legal jurisdiction. Delivering on the requirements of the directive necessitates an organized and provable process of cybersecurity management. One of the most consistent approaches to accomplishing the same is cream cracker testing.
Qualysec is an important application to guide businesses through the needs of NIS2. Their pentesting services relative to NIS 2 are not limited to automatic tests. They provide hybrid test driven results, which are performed with a combination of manual, human-led testing and automation to provide high impact and precise findings. All the tests are compliant with NIS2 Article 21, including vulnerability identification, incident preparedness, and documentation needed to trace audits.
With Qualysec, there is also sector-specific testing tailored to businesses in the energy sector, banking sector, healthcare sector, transportation sector, and any other regulated industry, as well. Their reports do not only stand as a technical document but are compliances ready assets mapped against NIS2 expectations. Then it is easier for a company to answer an auditor or regulator with confidence.
Want to know how ready your organization is for NIS2? Contact Qualysec today to schedule your NIS2 penetration testing consultation and get a custom roadmap to compliance.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Frequently Asked Questions (FAQ)
Q. What is NIS2 in the EU?
Ans: The NIS2 Directive is the new European cybersecurity law that will replace the first one, the EU NIS Directive. It brings out more stringent security requirements, expanded sector scope, and high-quality punishment for noncompliance. Its core mission is to enhance the cybersecurity position of critical organisations of EU member states.
Q. Is NIS2 applicable in the UK?
Ans: Yes, although the UK has ceased to be a member of the EU, NIS2 can be valid even to businesses based in the UK. But which serve customers in the EU or have installed infrastructure in the EU territory. In case your enterprise is regarded as essential or significant per NIS2, you are supposed to respond to its security standards.
Q. Do I need to comply with NIS2?
Ans: As long as your business delivers digital services or infrastructure to the customers in the EU, manages sensitive data or integrates into an EU supply chain. It is probable that NIS2 applies to you. A NIS2 readiness assessment or advice of cybersecurity specialists such as Qualysec may help to clarify your compliance requirements.
Q. What is the difference between NIS and NIS2?
Ans: NIS2 greatly builds on the initial regulation on NIS by enhancing the range of sectors included. It also decreasing the degree of fragmentation between member states. And adding obligatory deadline conditions of notifications of incidents and the specifications of more serious stipulations. It further includes greater requirements in the supply chain and governance.























































































































































































































































































































































































































































































































































































































0 Comments