Cybersecurity in Indian banking is no longer a technical topic limited to the IT department. It is a serious matter that concerns regulatory accountability. Over the past few years, the Reserve Bank of India (RBI) has intensified its focus on cybersecurity governance via the RBI Cybersecurity Framework.
These frameworks serve as essential standards that demand financial institutions protect their systems, detect breaches, and report incidents. Financial institutions must recognize that security is now mandatory, and they need to document and demonstrate compliance through their actions.
That explains why penetration testing has emerged as a critical requirement for the RBI cybersecurity framework. It transforms policies and configurations into measurable evidence. RBI’s directives emphasise periodic, risk-based vulnerability assessments and penetration tests to ensure that institutions identify weaknesses before threats exploit them.
In this blog, we break down the RBI Cybersecurity Framework, its key pillars, and how penetration testing serves as an essential tool for compliance for Indian banks.
Talk to our BFSI security specialists for compliance guidance.
What is the RBI Cybersecurity Framework?
The first unified guideline towards consolidating cyber governance in the financial sector in India was the RBI cyber security framework in Banks, which was published in June 2016. It has established the basis of systemic cyber resilience, and every regulated financial institution should have solid, board-approved prevention, detection, and response mechanisms. Knowing the RBI cybersecurity framework checklist helps a great deal.
The RBI cybersecurity framework outlines expectations around:
- Developing a cyber risk management board to be in charge and accountable.
- Developing an integrated IT and cyber security RBI-favored policy that is business relevant.
- Preventing any uninterrupted surveillance of systems and critical assets via a Security Operations Centre (SOC).
- The reporting of all the incidents to the Cyber Security and Information Technology Examination (CSITE) cell of RBI as soon as possible.
- Performing periodic Vulnerability Assessment and Penetration Tests (VAPT) to test technical capabilities of defence.
Though the 2016 framework was originally targeted at banks, later the 2023 IT Governance Direction and the Outsourcing of IT Services Direction extended its core principles to NBFCs, CICs, and fintech entities.
Explore our article on Cybersecurity in Banking Sector for expert insights.
Pillars of RBI Cybersecurity Framework
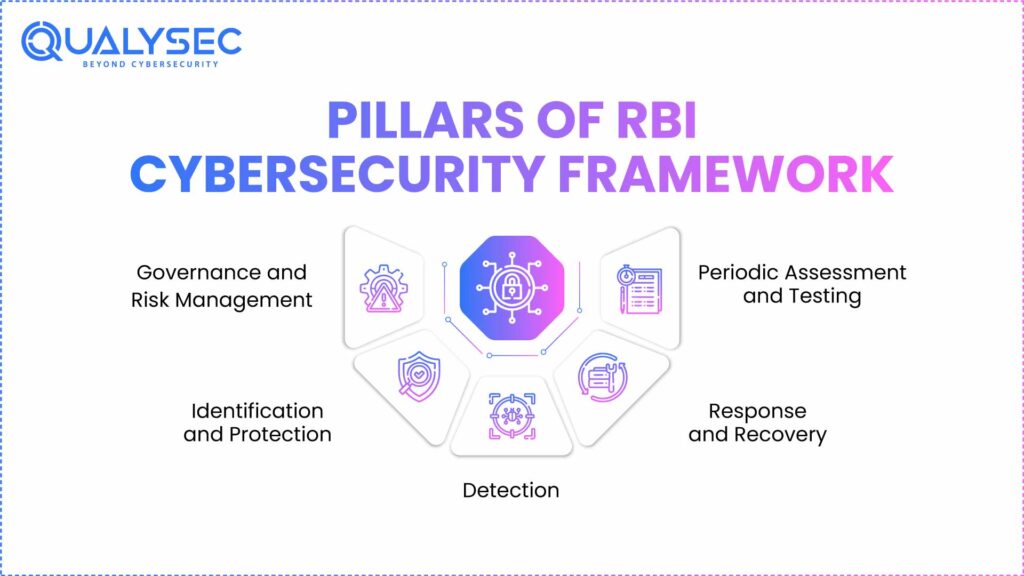
RBI Cybersecurity Framework is based on a layered structure. A combination of principles, which are fundamental, ensures certain governance, resilience, and accountability.
1. Governance and Risk Management
Cybersecurity begins at the top. RBI places boards and senior management with direct responsibility for cybersecurity. All institutions should appoint a Chief Information Security Officer (CISO) and come up with a formal governance structure on how cyber risks are identified and mitigated. This pillar supports the fact that web protection is not an IT operation; it is a governance operation.
2. Identification and Protection
Financial organizations need to have full visibility of their digital resources, such as hardware, software, and data streams. RBI anticipates a current IT inventory of assets, effective access control policies, and safe configuration baselines. This pillar is concerned with such proactive actions as patching, encryption, network segmentation, and endpoint hardening.
3. Detection
Timely identification is the disparity between a small-scale incidence and a significant violation. Institutions should run or outsource a Security Operations Centre (SOC) that will continuously monitor systems 24/7, correlate logs, and detect suspicious patterns. RBI expects institutions to implement automated alerting, log management, and threat intelligence integration for early warning.
4. Response and Recovery
The response should be systematic, recorded, and traceable when they happen. Banks and NBFCs must develop an Incident Response and Recovery Plan (IRRP) that outlines the escalation procedures, communication procedures, and business continuity procedures. The RBI also mandates that all major cyber incidents be reported to its CSITE division within defined timelines.
5. Periodic Assessment and Testing
This is the validation layer, the one that verifies whether the other four pillars truly works. To test the robustness of the defences under realistic conditions of attack, RBI requires Vulnerability Assessment and Penetration Testing (VAPT) and Red Team exercises. The testing has to be risk-based, periodic, and conducted by qualified personnel.
Explore our guide on Cybersecurity for Financial Services.
RBI Cybersecurity Framework: Exploring the Baseline Controls
The RBI’s 2016 circular includes an Annexure of Baseline Cybersecurity Controls. It is a set of technical and procedural safeguards every regulated entity must implement. These controls serve as a minimum operating standard to ensure consistency across the sector.
| Control Area | Objective | Relevance of Penetration Testing |
| Asset and Configuration Management | Maintain an up-to-date inventory of hardware, software, and network assets. | PT identifies unlisted or misconfigured assets that expose vulnerabilities. |
| Network Security | Protect data in transit, segregate internal networks, and implement perimeter defence tools like firewalls and IDS/IPS. | PT simulates external and internal intrusions to verify if network segmentation holds. |
| Application Security | Integrate security into the software development lifecycle (SDLC) and conduct secure code reviews. | Manual PT uncovers logic flaws, input validation errors, and exploit chains missed by automated scanners. |
| Access Control and Identity Management | Enforce least privilege, strong authentication, and periodic access reviews. | PT validates whether privilege escalation or credential compromise is possible. |
| Patch and Vulnerability Management | Ensure prompt patching and version updates across OS, databases, and applications. | PT helps verify patch effectiveness and identify unpatched critical systems. |
| Incident Detection and Response | Maintain structured incident handling processes and escalation workflows. | Red Team exercises test the organisation’s detection speed and response maturity. |
| Third-Party and Vendor Management | Assess the security posture of vendors with IT system access. | External PT validates the security of vendor-exposed assets or integrations. |
Discover our guide on security compliance in India.
Download a Sample Pen Testing Report

Compliance with RBI Cybersecurity Framework
RBI compliance must demonstrate through evidence. The Cyber Security Framework in Banks (2016), reinforced by the IT Governance Direction (2023), makes it clear that institutions must establish a system of ongoing verification, documentation, and review of their cybersecurity posture.
Regulated entities must maintain audit trails showing that they have implemented and reviewed every required control. RBI expects the following governance structure to exist and function –
- Policy and Oversight – The board approves the Cybersecurity policy, conducts a yearly review of the policy, and the CISO establishes clear ownership of the policy.
- Risk Management Framework – A list mapping every asset, system, and process, and their corresponding risk and control.
- Testing and Validation – Routine vulnerability testing, penetration testing, and red-team testing of all critical systems.
- Remediation Governance – Closure of vulnerabilities within accepted timeframes and checking to ensure the vulnerability is fixed.
- Incident Reporting and Learning – Documented incident response reports submitted to RBI’s CSITE division within mandated timeframes.
- Third-Party Assurance – Due diligence checks, right-to-audit clauses, and vendor testing aligned with the Outsourcing of IT Services Directions (2023).
Learn more about penetration testing for BFSI.
How can Qualysec help in complying with the RBI Cybersecurity Framework?
At Qualysec, we understand compliance is much more than meeting deadlines. It’s more about evidence-backed assurance. We designed our penetration testing to help financial institutions align directly with the RBI cybersecurity framework.
Check out our in-depth guide on Security Compliance for Financial Institutions.
We follow OWASP, NIST, and PTES frameworks while integrating RBI’s control categories. Each assessment is mapped against the Annexure baseline controls. This enables clients to demonstrate a direct linkage between RBI cybersecurity expectations and technical testing activities.
Apart from that, our audit-ready reports include an executive summary, a list of the technical findings, and remediation guidance. We also offer end-to-end assistance for our clients worldwide.
With extensive experience in core banking, digital payments, fintech platforms, and NBFC infrastructures, we understand the security dependencies that most generic testing vendors overlook. We test environments exactly as RBI examiners expect them to be validated.
Schedule your RBI-aligned penetration test with Qualysec.
Conclusion
The RBI Cybersecurity Framework marks a shift from policy-based assurance to evidence-based governance. Institutions are now expected to demonstrate their cybersecurity strength through regular, documented testing and remediation.
At Qualysec, we help financial institutions align directly with RBI’s cybersecurity and IT governance directives through structured, audit-ready penetration testing.
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
FAQs
1. What is the RBI Cybersecurity Framework, and who must comply?
RBI published the Cyber Security Framework in June 2016 to enhance cyber governance, resilience, and accountability in the Indian financial industry. It provides requirements that are mandatory in the area of governance, risk management, incident response, and periodic testing of security, such as Vulnerability Assessment and Penetration Testing (VAPT).
2. Why is penetration testing important for banks and fintechs under RBI guidelines?
Penetration testing is the validation mechanism that proves whether security controls work as intended. RBI’s framework calls for periodic, risk-based penetration testing to simulate real-world cyberattacks and uncover exploitable weaknesses before they can be used by malicious attackers.
3. How often should financial institutions conduct penetration testing as per RBI?
RBI does not recommend a single fixed frequency for penetration testing. However, institutions should conduct tests at least annually for critical internet-facing systems.
4. What types of vulnerabilities can RBI-mandated penetration testing uncover?
The penetration testing as mandated by RBI is aimed at discovering technical and logical vulnerabilities that would lead to a breach of confidentiality, integrity, or availability of financial systems. Such vulnerabilities are application flows, configuration errors, access control vulnerabilities, network-level vulnerabilities, and exposures to third parties.
If you have any questions, please check out our fintech industry case study.
























































































































































































































































































































































































































































































































































































































0 Comments