In South Africa, the situation regarding data protection is different in 2025. The Information Regulator has already passed various infringement notices and penalties for not protecting personal information. The maximum POPIA compliance penalty is R10 million, and criminal prosecution in severe cases is possible.
For South Africa, the message is simple – if your business processes personal information in South Africa, you are legally obligated to comply. The POPIA Act no longer excuses ignorance or delay.
POPIA isn’t a bureaucratic checkbox. It sets clear standards for how organisations collect, store, use, and share personal data. Moreover, the POPIA Act expects proof that your security measures are “appropriate and reasonable.”
The 2025 Amendment Regulations brought that expectation into sharper focus. The Regulator explained that all security compromises were to be reported. In case of a breach of your systems, you should inform the Regulator and the people affected immediately when you are reasonably certain that there has been a breach.
In this guide, we discuss POPI Act compliance in detail, what it is, who it applies to, and how to maintain compliance.
➡️ Get a Free POPIA Gap Analysis—know what you’re missing.
What is POPIA compliance?
The Protection of Personal Information Act (POPIA) is a South African law governing data protection that is comprehensive in nature. The act is similar in a way to the international laws regarding privacy, for example, the EU GDPR. However, this is enforced in the country through the Information Regulator of South Africa.
The POPIA Act applies to both public and private bodies, and to foreign entities that process South African residents’ information through local systems or services.
POPIA compliance: Who does it apply to?
POPIA compliance is broad. It applies to:
- Private and public bodies that collect, store, or share personal data.
- Any organisation that operates outside South Africa and processes the data using the local systems, or provides goods or services to South African residents.
- The third-party vendors and service providers (operators) that process personal information on behalf of a second party.
It covers:
- Customer data – names, contact information, payment details.
- Employee data – HR files, payroll records, medical certificates.
- Supplier and contractor information.
- Online and offline data – collected via websites, emails, forms, CCTV, or recordings done on a call.
➡️ Secure Your Business with our Regulatory Compliance Audit Guide.
Why is POPIA compliance important?
POPIA compliance is a business necessity that shapes trust, risk, and reputation in South Africa’s increasingly digital economy.
1. Legal Protection
Compliance protects your business from severe enforcement actions. The Information Regulator can issue administrative fines of up to R10 million, and, in cases of deliberate non-compliance or obstruction, directors and officers can face criminal prosecution.
2. Customer Trust and Market Reputation
Data breaches make headlines. Consumers today expect brands to protect their personal information as carefully as they protect their money. Demonstrating the POPIA Act shows that your organisation values privacy and integrity.
3. Operational Efficiency
For data security compliance, businesses need to map their data, formalise policies, and define clear roles for accountability. That structure reduces internal confusion, duplication, and accidental misuse of information.
➡️ Avoid costly fines—secure your POPIA compliance now.
POPIA compliance checklist
You don’t need a 50-page policy to start. You need a clear checklist and accountability to achieve POPIA Act compliance. This 2025-aligned list follows the Regulator’s latest guidance and best practices seen across South African industries.
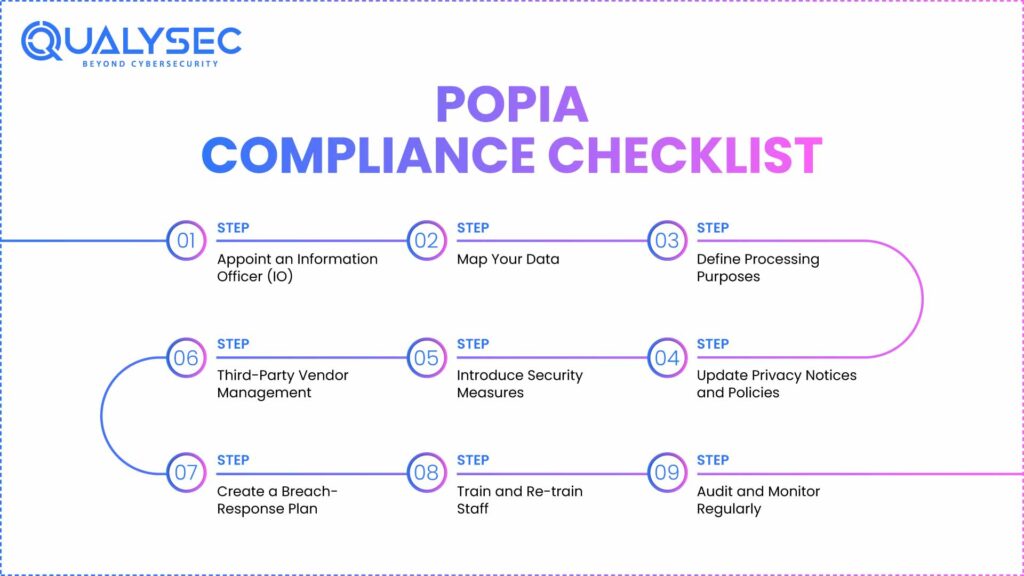
Step 1 – Appoint an Information Officer (IO)
All organisations are required to identify an IO, which is usually the CEO or a representative manager, and have him or her registered by the Information Regulator. The IO is the compliance anchor, responsible for policies, breach notifications, and internal awareness.
Step 2 – Map Your Data
Identify what personal information you collect, where it resides, who has access, and whether it leaves the country.
Step 3 – Define Processing Purposes
Document why each category of data exists. Link it to a lawful basis – consent, contract, legal duty, or legitimate interest. It ensures processing limitation and purpose specification.
Step 4 – Update Privacy Notices and Policies
Draft or revise your privacy policy, website notice, and employee notice. Keep them readable and localised. Transparency satisfies the Openness condition.
Step 5 – Introduce Security Measures
Embrace multi-layered protection, including access control, encryption, frequent patching, and frequent expert penetration testing. Section 19 of the POPIA states clearly that there should be reasonable technical and organisational measures. Those security measures are confirmed by testing.
Step 6 – Third-Party Vendor Management
Analyze deals with processors and service suppliers. Include provisions whereby they are binding themselves to abide by POPIA.
Step 7 – Create a Breach-Response Plan
Document how you’ll detect, contain, and report incidents. Identify roles, escalation contacts, and notification templates. Under the 2025 fact-sheet, all security compromises must be reported as soon as you are reasonably sure, not after full investigation.
Step 8 – Train and Re-train Staff
Carry out phishing, data-handling, and breach escalation awareness sessions. The number-one cause of reported POPIA incidents is human error.
Step 9 – Audit and Monitor Regularly
Schedule annual reviews of data processes and security controls. Maintain records of changes and retesting results.
Download a Sample Pen Testing Report

How to become POPIA compliant?
POPIA compliance may likely become an overwhelming task; however, it will become easier to follow when broken down into a set of organized and actionable steps. These steps are applicable whether you are a developing SME or a big business entity.
Step 1 – Assess and Map Your Data
The first step is to get things in writing about the personal information that your organisation processes, the reasons why you process it, where it is stored, and who can access it. Incorporate electronic as well as paperwork.
Step 2 – Assign Roles and Responsibilities
Formally appoint your Information Officer (IO), and, if needed, associates who are responsible for large or scattered groups. The IO should be a certified Information Regulator. Create responsibilities within the departments, such as HR, IT, Marketing, and Finance, since they all have access to sensitive data and should be the ones responsible for compliance in their respective departments.
Step 3 – Develop and Implement Policies
Draft internal documents for:
- Data protection and processing
- Data retention and disposal
- Breach response and escalation
- Employee access and security use
- Vendor and contractor agreements
The policies should be realistic and easy to understand; they should not be crafted to impress the lawyers but to lead the employees.
Step 4 – Implement Technical and Organisational Safeguards
This is where many businesses fall short. POPIA doesn’t prescribe specific tools, but it expects “reasonable measures” to secure data.
This means:
- Strong passwords and MFA (multi-factor authentication)
- Encryption for stored and transmitted data
- Role-based access controls
- Network and endpoint protection
- Regular vulnerability and penetration testing to perform validation of the defences
Partnering with a security firm such as Qualysec, these security measures will be tested, confirmed, and documented; evidence that the Regulator would lament that they saw following an attack.
Step 5 – Conduct Vendor Due Diligence
Check all third-party processors (IT service providers, payroll providers, CRM vendors, and so on). Revise and update contracts with POPIA requirements, confidentiality, and express breach-disclosure requirements.
Step 6 – Train Employees
The employees are your line of defence as well as the weakest link. Profit awareness programs on phishing, password maintenance, and reporting processes in case of possible data leakages.
Step 7 – Establish a Breach-Response Playbook
Prepare an incident-controlling flowchart. Who will investigate, to whom the IO will know, and how will the Regulator and the data subjects be informed?
Step 8 – Review and Improve Continuously
Adherence does not occur in a single instance. Arrange yearly compliance security audits, quarterly reviews, and system retests. Store all evidence here, including meeting notes, reports, and audit logs in a single central compliance folder.
Find Your Perfect Security Partner

Conclusion
The South African digital economy has increased, as well as the expectations around its data privacy. It is no longer a choice of being POPIA act compliant or not; it is the basis of customer confidence, the survival of business, and brand reputation.
The smartest businesses don’t wait for a breach or regulator warning. They act early, test regularly, and prove that security is part of their DNA to become POPI Act compliant.
That’s where Qualysec makes the difference. Our experts offer reliable vulnerability tests and penetration tests to assist organisations in justifying their compliance. We provide skill-based testing, international procedures, and comprehensive reporting.
➡️ Book your POPIA-ready security assessment with Qualysec today.
FAQs
What is POPIA compliance?
POPIA compliance implies the correspondence of the policies, processes, and technical protections to the Protection of Personal Information Act (Act 4 of 2013). It guarantees the responsible collection, use, and storage of personal data of customer records the employee data.
Who needs to comply with POPIA in South Africa?
All the public and non-public organisations that handle personal data in South Africa, or regarding South African nationals, are obligated to do so. That includes:
- Local businesses, government organizations, and NGOs.
- MNCs dealing with the sale of goods or services to South Africans.
- Processors of data on behalf of others Data third-party service providers (operators).
What are the key requirements of POPIA compliance?
The POPIA compliance is centered around eight conditions for legal processing, including accountability, transparency, limitation of purpose, quality of information, and participation of the data subjects. Core requirements include:
- Hiring and enlisting an Information Officer.
- Developing explicit privacy policies and instructions.
- Staff training as well as checking in on vendors.
- Along with reporting all data breaches to the Information Regulator and individuals.
How can a business achieve POPIA compliance?
Compliance starts with understanding your data.
- Map your information flows
- Assign accountability
- Develop policies and procedures
- Implement strong security safeguards
- Train employees and monitor progress
How can companies get help with POPIA compliance?
A lot of companies collaborate with cybersecurity experts such as Qualysec in order to measure the security outcomes with legal obligations. For instance, conducting penetration testing covering web, mobile, cloud, and API systems.
























































































































































































































































































































































































































































































































































































































0 Comments