In today’s digital landscape, organisations in Saudi Arabia face an increasing array of cyber-risks. A vulnerability assessment service in KSA helps you identify weaknesses before an adversary can exploit them. As digital transformation takes shape in the Kingdom through Vision 2030 and heavy investments into technology, robust and resilient cyber defences have never been more necessary.
Many companies and government organisations are now required to conform to new security standards that have been put forth by the National Cybersecurity Authority (NCA). Looking to 2025, it will be a new set of threats and a more advanced adversary landscape as a backdrop for the long-standing objectives of security and security risk management.
In this guide, we aim to take a fresh, current look at vulnerability assessment service in KSA. Whether you are a part of an SME (small and midsize enterprise), large enterprise, or public sector, we believe you will find some useful information in this guide. Let’s get started.
What Is A Vulnerability Assessment?
A vulnerability assessment is a structured approach to discovering, analysing, and reporting on the weaknesses in your IT systems, networks, or applications. It is not exploiting weaknesses (that is, penetration testing) but rather identifying weaknesses, enabling you to fix them. The aim is to know what vulnerabilities exist, how serious the grounds (risk) are, and what to do. It includes software bugs, misconfigurations, missing patches, insecure settings and weak protocols. Once the scan + analysis is complete, you receive a report with the findings and recommended fixes. In KSA, where compliance/risk management is critical, a vulnerability assessment is foundational security for any organisation, regardless of size.
Why Vulnerability Assessment Matters In KSA (2026 Perspective)
Saudi Arabia is swiftly undergoing a digital transformation – from smart cities to e-government services. Not without risk, however, cyber-threats are on the rise. A recent report noted 2025 saw growing ransomware, dark-web sell-offs of Saudi corporate/government data, and targeted attacks on infrastructure.
1. Expanded threat landscape
More digital services, more cloud use, more apps, and more endpoints all result in a larger potential attack surface. Within the Kingdom, organisations stretch across sectors (finance, oil & gas, healthcare), each holding a large attack surface. A VAPT assessment can help you map and shrink that attack surface.
2. Increasing compliance and regulation pressures
The NCA’s frameworks, like the revised Essential Cybersecurity Controls (ECC‑2), outline minimum expected behaviours for cybersecurity controls in Saudi Arabia. To meet these minimums often means committing to regularly reviewing your vulnerability assessment, and leaving it unaddressed can incur penalties, loss of contracts, or reputational damage.
3. Risk to national & business assets
Critical national infrastructure, large private firms, and even smaller businesses are all at risk. Risks that have not been modelled or remediated could lead to data loss, service availability, or financial costs. A strong vulnerability assessment allows you to identify issues before they turn into incidents.
4. Competitive & trust advantage
In KSA’s fast-moving and competitive market, demonstrating that you take cybersecurity seriously could open up business opportunities. Once a vulnerability assessment is carried out on a repeat basis, it will demonstrate proactiveness and build trust with partners, customers, and regulators.
Learn the key differences between Risk Assessment vs Vulnerability Assessment.
Types of Vulnerability Assessment Services
Various assessments fulfil different needs, and selecting the appropriate form ensures the right risks are examined.
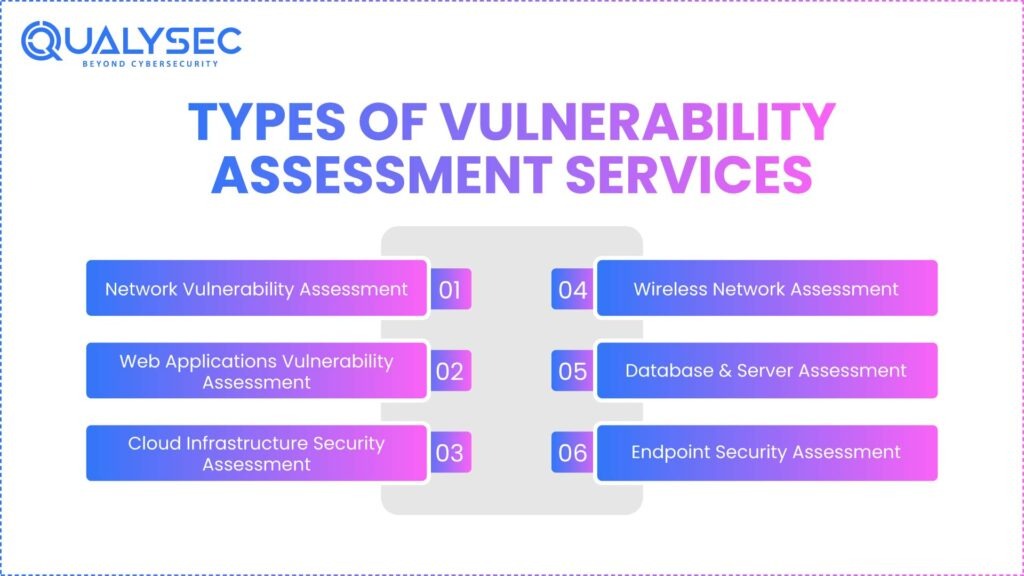
1. Network Vulnerability Assessment
Network vulnerability assessments are performed on your network infrastructure – firewalls, switches, routers, and servers – to assess issues like open ports, misconfigurations, unpatched vulnerabilities, or use of insecure protocols, etc. A good assessment will identify points of weak entry for attackers’ movement inside the network.
2. Web Applications Vulnerability Assessment
Web applications (both public-facing and internal) have lists of vulnerability checks, such as SQL Injection, XSS, insecure APIs, session management issues, etc. Because many businesses in KSA provide web services, web application assessments are equally critical. Read more about Web Vulnerability Assessment.
3. Cloud Infrastructure Security Assessment
Given the global trend toward greater use of both public, private, and hybrid clouds in KSA, cloud security assessments consider misconfigured cloud storage, insecure identities, improper access controls, and other shared risks for resources. Cloud security is particularly critical in light of current regulatory environments and standards. Explore more about Infrastructure Security Assessment.
4. Wireless Network Assessment
Wireless channels are frequently ignored. This assessment focuses on WiFi networks, guests, remote access, weak encryption, and rogue access points. Wireless risk is especially true in offices and multi-site organisations, and true in Saudi Arabia. Read more about Network Security Assessment.
5. Database & Server Assessment
Databases are often the repository of critical/sensitive data. In a Security Assessment, this evaluation focuses on insecure user accounts, weak passwords, missing patches, and misconfiguration of settings. Servers hosting applications, files, or databases could be compromised with a vulnerability.
6. Endpoint Security Assessment
Endpoints – laptops, desktops, mobile devices, IoT – represent a common attack vector. This Endpoint Security assessment focuses on unpatched systems, outdated software, insecure configuration, and removable media risk. For an organisation in KSA, endpoint risk is meaningful in context, since many staff work remotely or have mobile access.
The Vulnerability Assessment Process (Step-by-Step)
Here is a typical process, and each step provides accountability and an expected outcome that is equally important.
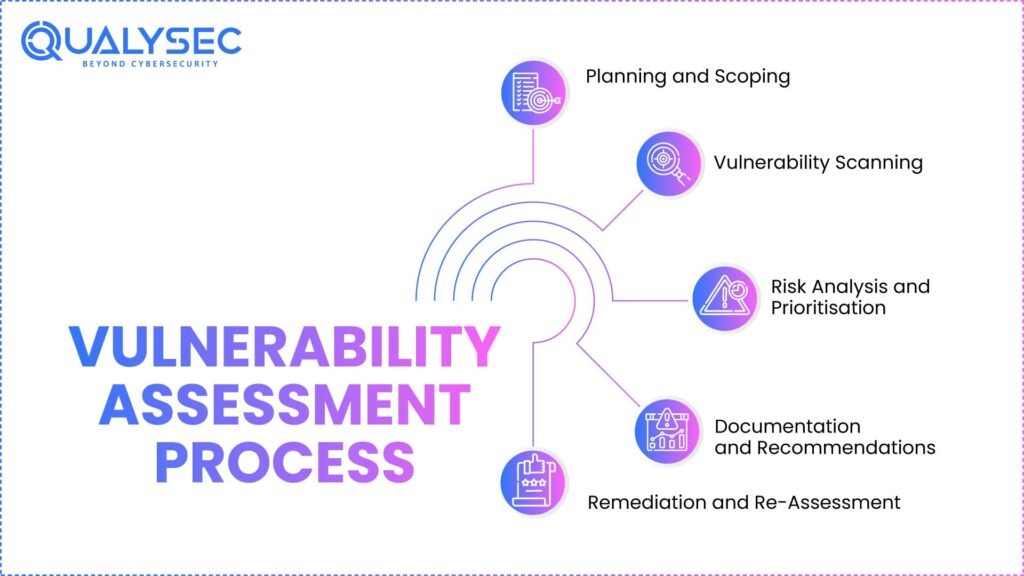
Step 1: Planning and Scoping
You define the scope of the assessment (the systems, networks, applications), who will do the assessment, timing, and constraints. When you make the scope, it is especially helpful to sync with the compliance requirements (i.e., NCA controls) right from the beginning in KSA.
Step 2: Vulnerability Scanning
Using automated methods (and sometimes manual tests), the assessment scope is scanned for known vulnerabilities – missing patches, weak configs, etc. This process of Vulnerability Scanning provides raw output for the next phase.
Step 3: Risk Analysis and Prioritisation
Not all vulnerabilities are equally risky. You will analyse based on impact (how bad if the risk occurs) and likelihood (how easy it is to perform). You then prioritise which ones are fixed first. This is especially relevant in Saudi Arabia because of the more constrained resources.
Step 4: Documentation and Recommendations
Once you have completed the analysis, you will produce a report that outlines the vulnerabilities uncovered, ratings of each vulnerability, and a recommended set of actions (supporting patching, changing configurations, or eliminating a risk). Good reports will have an executive summary and recommendations for actions congruent with your business.
Step 5: Remediation and Re-Assessment
Finding the vulnerabilities is only half of the work; then you have to remediate. Once remediation has been performed, you will re-scan to see if the vulnerabilities were remediated. After patching vulnerabilities, you should assess at least quarterly or semi-annually to stay ahead of emerging threats.
Download our Latest Vulnerability Assessment Report to secure your business from cyber threats.
Download a Sample Pen Testing Report

Benefits of Regular Vulnerability Assessment
Conducting assessments on a regular basis instead of as a one-off is significant.
1. Early identification of security vulnerabilities
When you assess regularly, you can identify weaknesses and vulnerabilities prior to them being exploited by an attacker. Being proactive is effective in reducing your risk and is often less expensive than responding to a breach.
2. Enhanced risk management
Regular assessments provide you visibility into your actual risk posture: which systems are riskier, what your largest exposure is, how vulnerabilities are trending, etc. That intelligence and information can assist in putting together a sharper budget and assessment of where to focus your efforts.
3. Compliance assurance
In Saudi Arabia, for example, frameworks like ECC-2 (among many others) require any company to have solid controls and constant monitoring. Having regular assessments provides evidence that you are indeed in control of your regulatory obligations, and you are audit-ready at the time of your assessment.
4. Improved preparedness for incident response
When you know your vulnerabilities, you can work on response plans and better reduce the time to detect, contain, and recover. This is a strategic advantage in an increasingly hostile cyber-landscape.
5. Increased consumer and stakeholder trust
By showing you care about security (through regular assessments), you build trust with customers, partners, investors, and regulators. KSA is a business environment where reputation matters.
Get a free Vulnerability Assessment and Penetration Testing consultation now.
How to Choose the Right Vulnerability Assessment Service Provider in KSA
Choosing a service provider can make the distinction between a mere compliance exercise and a worthwhile investment in security.
Experience & local presence
Choose a provider with experience and presence in the Saudi market who understands the regulatory environment, language, and local risks. With local experience or presence in KSA, the provider will be familiar with NCA, as well as ECC-2, and local business contexts.
Certifications & methodology
Verify the provider is reputable and that they use standards and recognised tools (CVE databases, trusted scanning tools, etc). How they approach security is equally as important; do they simply run scans, or do they offer manual validation, prioritisation, and actionable reporting?
Tools & automation
What tools do they use – automated scanning, manual review, dashboards, risk prioritisation features. A service provider using updated tools and scanning methodology is better prepared to address the complexity required to mitigate threats related to 2026 and beyond (cloud, AI, supply-chain, etc).
Effectiveness of reporting & remediation assistance
The report must be straightforward, clear, and prioritised. It should not simply be a long list of issues. Ask if they offer remediation action support and if they follow up to ensure fixes have been made.
Compliance & regulatory alignment
The provider should be knowledgeable about KSA’s regulations (such as NCA’s ECC-2) and be able to tie their findings and recommendations to regulatory requirements. This makes your life easier when it comes time for audits and government contracts.
References & value for money
Check references: other customers in Saudi Arabia, by industry sector. Evaluate the cost in relation to value, too – you are not just paying for a scan, you are paying for insight and safer operations.
Discover top-rated VAPT Service Providers in your region.
Conclusion
As we approach 2026 and Saudi Arabia enhances its digital infrastructure and moves ahead with its ambitious projects, organisations are going to have to adjust to constantly changing cyber-threats. A vulnerability assessment service in KSA is no longer an option, but a necessity.
By scanning your systems frequently, identifying vulnerabilities, focusing on what vulnerabilities should be fixed first, and aligning with the National Cybersecurity Authority’s frameworks, such as ECC-2, you can protect your assets, gain trust, achieve compliance, and facilitate growth.
Whether you are a government agency, a major corporation, or a developing SME, the right service, combined with standards and best practices, together with security as a major part of your culture, will pay off. Start today – identify your vulnerabilities, remediate them – and plan to stay ahead. Your digital future in the Kingdom depends on it.
Talk to Qualysec experts to plan your next Vulnerability Assessment today.
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
FAQ’s
1. What does a vulnerability assessment service mean in KSA?
A vulnerability assessment service is a type of service available in KSA that aids organisations in the identification and investigation of security weaknesses, or vulnerabilities, present in their IT systems, networks, and applications. It helps ensure that threats may be acted on before cyber threat actors can utilise them.
2. Why is a vulnerability assessment important for a business in KSA?
With the rapid digital transformation of Saudi Arabia, expedited by Vision 2030, the number of cyberattacks has also increased. Conducting a vulnerability assessment regularly helps businesses safeguard their sensitive data, maintain compliance with the NCA framework standards, and avoid costly breaches.
3. What are the different kinds of vulnerability assessments in KSA?
Organisations and businesses have the option to choose from network vulnerability assessment, web application vulnerability assessment, cloud vulnerability assessment, wireless vulnerability assessment, database vulnerability assessment, and endpoint vulnerability assessment. Each type of vulnerability assessment helps target and identify specific security vulnerabilities in different areas of the IT environment.
4. What are the advantages of the vulnerability assessment service in KSA?
Vulnerability assessment services can identify risks proactively, bolster overall cybersecurity resilience, fulfil compliance with national legislation, and build patron trust. These services can assist in mitigating downtime or financial losses resulting from cyber events.
5. Who delivers vulnerability assessment services in KSA?
There are many cybersecurity companies and managed security service providers that offer vulnerability assessment services in Saudi Arabia. These may include local providers who specialise in NCA compliance, as well as larger, international companies with global expertise.
6. What is the cost of a vulnerability assessment in KSA?
Cost objectives vary with respect to an organisation’s profile, the complexity of its network, and the extent of an assessment. In KSA, average starting costs for vulnerability assessments for small networks begin at around SAR 5,000 to above SAR 50,000 for larger enterprises with multiple systems.























































































































































































































































































































































































































































































































































































































0 Comments