Companies all over the world are adopting the use of cloud computing as a way of promoting innovation and scalability. But at the same time, such digital transformation requires high-level security measures. GCP Security Services ensure that business clients with their operations switching to the Google Cloud Platform are properly guarded, as they offer advanced security frameworks and tools to defend sensitive data and applications against dynamic cyber threats.
With businesses migrating their workload to the cloud, it is very important to discuss and apply effective workload protection approaches in the Google Cloud. The shared responsibility model implies that Google provides the underlying infrastructure, and the organizations should assume responsibility for providing security to their applications, data, and access controls. This paper explains the necessary GCP Security Services and the steps to follow to implement GCP cloud security best practices.
Understanding Google Cloud Security Architecture
The Foundation of GCP Security Services
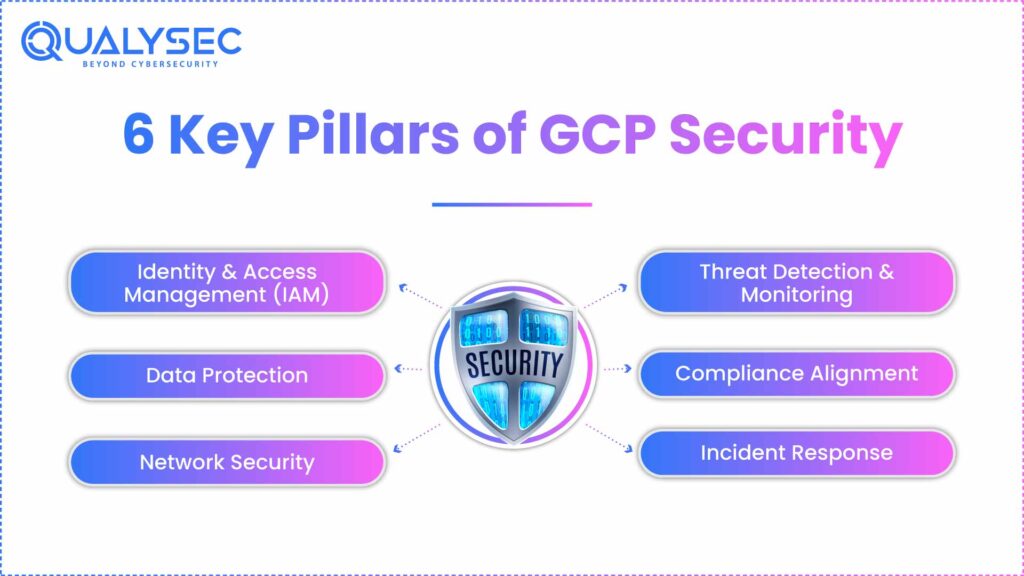
GCP Security Services are built on Google’s defense-in-depth approach, providing multiple layers of protection across the entire cloud infrastructure. This comprehensive security framework encompasses:
- Hardware-level security: Custom-designed servers with Titan security chips for hardware authentication
- Infrastructure protection: Encrypted data transmission between data centers and advanced physical security measures
- Network security: Global private network with automatic DDoS protection and traffic isolation
- Application-level controls: Advanced identity management and access control mechanisms
Key Components of Google Cloud Security Management
The security architecture includes several fundamental elements that contribute to the coherent protection:
- Identity and Access Management (IAM): User and access control to resources on a centralized system.
- Cloud Security Command Center: A Single security dashboard used to monitor compliance and detect threats.
- VPC Service Controls: Security boundaries to keep confidential information impenetrable by outside parties.
- Cloud Key Management Service: A Single point of cryptographic key management to encrypt data.
Read Also: Cloud Penetration Testing | Cloud Security | Cloud Services
Core GCP Security Services for Workload Protection
Identity and Access Management Excellence
Identity and Access Management (IAM) is the building block in Google Cloud workload security, where organizations can use a complex set of controls over access. The service is in the principle of least privilege, and this means that the users and services only have the minimal set of rights they need to execute their assigned roles. Such a tactic greatly limits the attack surface and also the damage that may be done with compromised credentials.
IAM system offers custom roles in addition to standard permission roles; this enables an organization to design exclusive access controls based on its organizational operational needs. Service accounts assist in offering safe authentication of applications and automatic processes with no need to encapsulate credentials in application code. Such service accounts may be further granted particular access levels and periodically changed to ensure hygiene.
Conditional access policies provide one more level of security by taking into consideration the contextual data (the device security state, geographical location, and time of access) during the formulation of the authorization decision. This contextually aware method also makes it possible to achieve adaptive security policies in organizations with automatic responses to varying risk conditions.
Read Also: Cloud Security Solutions: Challenges, Trends, and Best Practices
Qualysec’s cloud pentest gives you results—no endless emails, no digging through PDFs, no guesswork.

Comprehensive Security Command Center
Cloud Security Command Center is one of the centralized methods of Google Cloud security management and maintains its visibility throughout the cloud. This cloud layer automatically finds and inventories all the resources of the cloud and makes sure that the security teams get full visibility of the infrastructure footprint. Discovery is an ongoing process that instantaneously recognizes the new deployed resources and indicates unauthorized or shadow IT resources.
Vulnerability detection abilities utilize machine learning models that detect areas of vulnerability within the infrastructure. Such automated scans register general types of risk such as misconfigurations, exposed databases, and insecure network setups. Its system is the one that offers remediation guidance that is beneficial to making decisions about prioritizing and getting into what needs to be done first in the security teams.
Features in compliance monitoring provide constant assurance that configurations are compliant with regulatory frameworks like CIS benchmarks, PCI DSS requirements, and GDPR compliance frameworks. Automated reporting features produce compliance dashboards and audit reports, and greatly diminish the administrative pressure of remaining in regulatory compliance.
Real-time threat detection analyzes data with the help of advanced analytics and machine learning to alert on a potential security incident through suspicious activity detection. The system links up events within the various sources of the data to avert false positive events whilst maintaining that the true threats are reported and reported as soon as possible and made known to the respective security teams to be investigated.
Advanced Network Security Solutions
The best practices of GCP cloud security are concerned with strong network protection with a set of multi-faceted security services. Cloud Armor delivers DDoS-sophisticated protection capabilities and bot management functionality of the web application firewall (WAF). Various kinds of attacks, such as SQL injection, cross-site scripting, and volumetric DDoS attacks, can automatically be detected and mitigated by the service.
VPC Security allows companies to establish separate network environments having their firewall policies and the ability to network segment. Such isolation makes it possible to make sensitive workloads resistant to external threats as well as lateral movement within the network. Network administrators can do micro-segmentation to restrict the flow of information among various tiers of the applications and services.
Cloud NAT can offer fully protected outbound internet connectivity to the private instances without making the instances accessible via an inbound internet connection. The service enables organizations to implement a highly secure inbound policy, even though they still need essential outbound communications to update their software, call their APIs, and synchronize data.
Private Google Access enables Google Cloud APIs and services to be used by resources in private subnets without the need to assign externally-routable IP addresses. Such an ability guarantees the opportunity to operate sensitive workloads by using cloud services, yet with network isolation and mitigation of exposure to internet-borne threats.
Read Also: Cloud Security Network – Definition and Best Practices
Cloud Security Command Center
This centralized security management platform provides comprehensive visibility into your GCP Security Services posture:
| Feature | Description | Benefits |
| Asset Discovery | Automated inventory of all cloud resources | Complete visibility and asset management |
| Vulnerability Detection | Continuous scanning for security weaknesses | Proactive threat identification |
| Compliance Monitoring | Regulatory standard compliance tracking | Simplified audit processes |
| Threat Detection | Machine learning-powered security analytics | Real-time threat identification |
Take a look at Qualysec’s ratings and reviews on Clutch to see how we help businesses secure their cloud infrastructure. Book a free live consultation to learn more.
Implementing GCP Cloud Security Best Practices
Comprehensive Data Protection Strategies
Data protection is another important aspect of Google Cloud workload protection and will entail encapsulation of the entire data in all states. Google Cloud also encrypts all stored data by default with Google-managed keys in such a way that data would be secured even when physical storage devices are tampered with. This is transparent encryption, meaning that no extra setup is required, and yet it offers strong protection to applications and users.
Google offers Customer-Managed Encryption Keys (CMEK) to provide additional control over its encryption activities: the organization controls the keys themselves according to its rotation policy and key access controls via Google Cloud Key Management Service. This methodology allows an organization to be compliant with regulatory-enforced standards of customer-controlled encryption keys and yet enjoy the secure trust of Google-controlled key management systems.
In cases where the security requirement is high, organizations have ensured the full control of the encryption keys for their entire customers by using Customer-Supplied Encryption Keys (CSEK). Within this model, the encryption keys are never stored by Google, and therefore, the most highly sensitive data receives high levels of security. One of the effects of CSEK is that organizations should put in place intensive key management procedures to guarantee the availability and recovery capability of keys.
FIPS 140-2 Level 3 certified storage of keys and cryptographic operations are provided by HSM integration, where organizations have compliance needs that require the use of hardware-based key protection. This ability is used to perform cryptographic operations to be done on tamper-resistant hardware environments.
Recommended: Cloud Security Services for AWS, Azure & GCP
Continuous Monitoring and Compliance Framework
Continuous monitoring is necessary to enhance effective cloud security management using Google Cloud, which provides a real-time perspective on the security position and compliance. Cloud Audit Logs provide extensive tracing of administration activities and data access operations, creating well-structured audit trails that forensic analysts can use and that meet compliance reporting needs.
Cloud Monitoring provides an up-to-the-minute display of performance and security-related data, including extravagant alerting that can signal security teams of a potential problem happening prior to any influence on business functions. The monitoring tool can be customized with sensors and dashboards that can be tailored to the organizational needs and security models.
Security Health Analytics ensures intuitive support and remediation advice on automated security finding detection that security teams can utilize to address first, the most critical vulnerabilities. The software compares configurations with security best practices and regulatory standards, constantly giving actionable recommendations to improve a configuration as the system is checking it.
Compliance reporting enables the automated outputs of the reports required as part of a number of regulatory standards, such as SOC 2, ISO 27001, and GDPR. Such automated reports will save a lot on the administration expenses of compliance management, as well as ensure that organizations keep pace with compliance status.
Container and Kubernetes Security
With the rise of containerization, securing containerized workloads becomes crucial:
| Security Layer | GCP Service | Protection Provided |
| Image Security | Container Analysis | Vulnerability scanning and policy enforcement |
| Runtime Protection | Binary Authorization | Verified container deployment controls |
| Network Security | GKE Network Policies | Pod-to-pod communication controls |
| Access Control | Workload Identity | Secure service-to-service authentication |
Learn more about cloud penetration testing services offered by Qualysec.
Our experts at Qualysec have helped secure fintech, SaaS, and enterprise systems across 25+ countries. Manual + Automated Pentesting. No false positives. Actionable reports.

Advanced GCP Security Services for Enterprise Protection
Confidential Computing
This innovative approach protects data while it’s being processed:
- Confidential VMs: Secure-boot and secure memory-sensitive workloads.
- Hardware-based isolation: TEE (Trusted Execution Environment) protection
- Verifiable attestation: Workload integrity cryptographic evidence.
- Multi-party computation: Secure collaboration on sensitive data.
Read also: Infrastructure Security in Cloud Computing
Cloud Data Loss Prevention (DLP)
Automated data protection across your entire Google Cloud workload protection environment:
- Sensitive data discovery: Automated detection of PII, PHI, and financial information.
- Classification and labeling: Automatic data grouping according to their level of sensitivity.
- Policy enforcement: Automated redaction and access controls for sensitive information
- Compliance reporting: Detailed analytics for regulatory compliance requirements
Assured Workloads
In highly compliance-oriented organizations:
- Regulatory compliance: HIPAA, FedRAMP, and other standards pre-configured environments.
- Data residency controls: Guaranteed data location and processing restrictions
- Personnel access controls: Limited Google staff access with audit trails
- Encryption key management: Customer-controlled encryption key policies
Why Qualysec Stands Out as Your Premier GCP Security Services Partner
Regarding the application of the complex of GCP Security Services, Qualysec is the pioneer of the sector, and it provides boundless skill and advanced approaches to working out. Being a dedicated cybersecurity firm, Qualysec can unite both profound technical expertise and real-life experience of implementation to provide your organization with an efficient Google Cloud workload protection strategy to suit its needs.
Schedule a Free Consultation with Qualysec Today and discover how our expert team can transform your cloud security posture.
This is not the very basic implementation of Google Cloud security management. Our certified cloud security experts analyze fully, find the risks, and deploy multi-level security models that comply with industry best practices. We acknowledge that each organization has different security needs and thus our approach of tailor solutions in order to meet the defined business need, but in the process support optimum performance and user satisfaction.
Qualysec stands out owing to its comprehensive implementation approach that does not merely cover the technical implementation but extends to governance, risk management, and compliance components of GCP cloud-security best practices. We offer the complete package, including an initial security audit and architecture design, the continuing monitoring service, and incident response services.
Download Our Comprehensive GCP Security Assessment Report to understand how Qualysec’s proven methodologies can enhance your cloud security infrastructure.
Latest Penetration Testing Report

Best Practices for GCP Security Services Implementation
Security Assessment and Planning
Before implementing any security measures, conduct a thorough assessment:
- Risk assessment: Find out possible threats and weaknesses unique to your workloads
- Compliance requirements: Availability of regulatory standards to be applied and certification requirements.
- Current state analysis: Assess the current security measures and identify the gaps.
- Implementation roadmap: Plan implementation path towards security upgrade.
Continuous Security Management
GCP cloud security best practices require ongoing attention and optimization:
- Regular security reviews: Quarterly assessments of security configurations and policies
- Automated compliance monitoring: Continuous validation of security controls and standards
- Incident response planning: Prepared procedures for security event detection and response
- Security training: Regular education for development and operations teams
Integration with DevSecOps
Modern security requires integration throughout the development lifecycle:
- Security scanning: Automated vulnerability detection in CI/CD pipelines
- Infrastructure as Code: Secure configuration management through version control
- Container security: Integrated security scanning and policy enforcement
- Automated remediation: Self-healing security controls and configuration drift detection
Read more: The Ultimate Guide to Google Cloud Penetration Testing
Conclusion
Implement Solid GCP Security Services only with a thorough knowledge of the existing tools, best practices, and organizational needs. This multi-layered Google Cloud workload protection strategy effectively safeguards data against emerging cyber attacks and ensures the efficiency of operations and its regulatory standards.
The key to success in Google Cloud security management is the ability to perceive its distinct capabilities in security with years of experience and systematic improvements in mind to minimize the risks of difficulty. Companies with the right security architecture, round-the-clock monitoring, and frequent evaluation are in a position to realize effective cloud adoption and digital transformation.
This road to the implementation of comprehensive best practice of cloud security under the GCP is a long way that requires knowledge, planning, and continuous dedication. Partnering with a service provider equipped with trained security experts in the sphere of cloud computing, as well as utilizing the latest GCP Security Services, an organization will be able to step firmly in the direction of cloud computing and enjoy the utmost security-rated services.
Talk with our Cloud Security Experts Now to develop a customized GCP security strategy that protects your critical business assets and ensures long-term success in the cloud.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Frequently Asked Questions
1. What are the key GCP security services available?
The primary GCP Security Services include Identity and Access Management (IAM), Cloud Security Command Center, Cloud Identity-Aware Proxy, Cloud Armor for web application protection, and Cloud Key Management Service. These services work together to provide comprehensive security across identity management, network protection, data encryption, and continuous monitoring capabilities.
2. How can I secure my workloads on Google Cloud Platform?
Securing Google Cloud workload protection involves implementing multi-layered security controls, including proper IAM configuration, network segmentation through VPC, data encryption at rest and in transit, continuous monitoring with Cloud Security Command Center, and regular security assessments. Additionally, enabling features like Binary Authorization for containers and Confidential Computing for sensitive workloads provide enhanced protection.
3. What are best practices for managing security in GCP?
Effective Google Cloud security management follows the principle of least privilege, implements defense-in-depth strategies, enables comprehensive logging and monitoring, conducts regular security assessments, and maintains updated incident response procedures. Organizations should also integrate security into DevOps processes, automate compliance monitoring, and ensure proper staff training on GCP cloud security best practices.
4. How does Google Cloud protect data and applications?
Google Cloud provides automatic encryption for data at rest and in transit, implements hardware-level security through custom Titan chips, offers network isolation through VPC controls, and provides advanced threat detection through machine learning analytics. The infrastructure includes physical security measures, global private networks, and integrated security services that work together to protect applications and data comprehensively.
5. What tools help monitor and improve GCP security?
Key monitoring tools include Cloud Security Command Center for centralized security management, Cloud Logging for audit trail analysis, Cloud Monitoring for real-time alerts, Security Health Analytics for automated finding detection, and Asset Inventory for resource discovery. Third-party solutions like SentinelOne’s Singularity Cloud Security platform can also enhance monitoring capabilities with AI-powered threat detection and autonomous response features.
Have any questions? Feel free to ask now—our cybersecurity experts are here to help.























































































































































































































































































































































































































































































































































































































0 Comments