By the end of the year, according to experts, there will be more than 50,000 disclosed vulnerabilities, with approximately 38% of them classified as high or critical. Such an environment demands constant and continuous vigilance that is not limited to periodic scans, and continuous vulnerability assessment is helpful and necessary. It integrates automatic scanning, 24 positioning, and real-time threat identification so that the proactive security approach is maintained. This constant loop process can be used to control vulnerabilities, identify threats as they occur, and protect digital assets before any issues arise.
Continuous vulnerability assessment should be understood and utilised first if you desire your business to have a robust and dynamic security posture.
Contact Qualysec Technologies to know how this solution can transform your security activities. It helps guard your company against ever-evolving cyber threats!
Increasing Need for Continuous Vulnerability Assessment
In contrast to traditional testing, the technique offers continuous automatic scanning, which identifies and corrects security issues near real time. The security of businesses has become something that must be continuously observed, and no gap should be left unmonitored until the next set of tests.
In the modern world, attackers tend to exploit unknown vulnerabilities. This is combated through continuous vulnerability assessment based on real-time threat detection, constant scanning, and intelligent prioritization. This ensures that risk is always visible so that delays that might lead to breaches are avoided.
Some regulators coerce firms to implement end-to-end vulnerability assessment. Regulations like GDPR, HIPAA, the known-exploited-vulnerability (KEV) requirements of CISA, and the PCI DSS now mandate proven continuous security practices that can only be fulfilled reliably through constant practices.
Read more: HIPAA cybersecurity requirementsand PCI DSS compliance to protect sensitive health and payment data.
Difference between Continuous Vulnerability Assessment and Periodic Testing
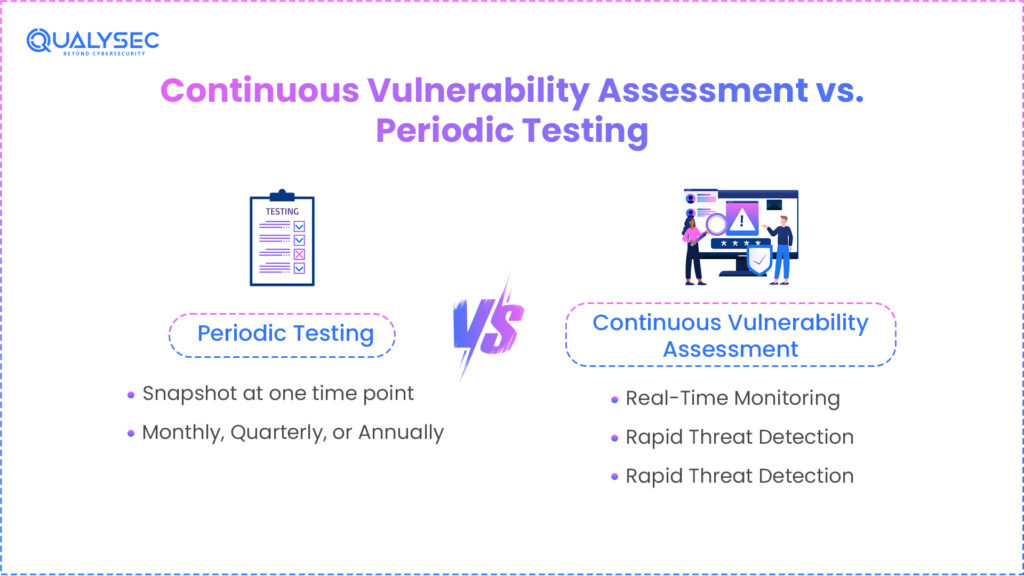
Vulnerability testing conducted monthly, quarterly, or annually provides a snapshot of system security at one time point. It is handy. But it is not fast enough to address the threats today. Continuous vulnerability assessment, in turn, combines automatic scanning with manual checks to maintain a constant security watch.
This is an ongoing process that identifies threats more effectively in real time, reducing the time gap between the identification of a vulnerability and its remedy. It incorporates proactive security strategies into daily operations. It identifies challenging or secret weaknesses that might prove more difficult to detect through a regular scan and makes the process of fixing them faster, reducing the possibility of zero-day attacks.
Major Advantages of the Continuous Vulnerability Assessment
The consistent vulnerability testing presents many strong advantages that improve the contemporary cybersecurity positions –
- Active Risk Management – Detection and rectification of problems immediately reduces the opportunity for attackers.
- Better Resilience – Continuous monitoring allows you to adapt defenses in real time as threats emerge.
- Compliance Guarantee – Ensures that you do not break the rules concerning security and risk.
- Efficiency – Automates scanning and ranks the threats based on the level of seriousness to your business.
- Quicker Reaction – Early detection of problems results in quicker corrections and a reduction of losses.
- Zero-day Defense – This involves identifying threats in real-time and preventing harm before they can damage the system.
Explore: Vulnerability Assessment Methodology.
Best Practices of Continuous Vulnerability Assessment Programs
To make the most out of continuous vulnerability assessment, organizations need to consider several metrics that play important roles in an ongoing vulnerability management cycle –
- Vulnerability Discovery Rate – This is the rate of discovering vulnerabilities per scan.
- Time to Remediation – Monitors the speed of identified vulnerability remediation or mitigation.
- False Positive Reduction – Checks the effectiveness of its detection gain in order not to waste resources.
- Critical Assets Cover – The program scans and monitors all necessary infrastructure and applications.
- Incident Response Metrics – The responsiveness of the team to perceived issues at the time they happen.
These measures allow the security teams to have a clear picture of their risk and continue enhancing their safeguards.
The Reason Continuous Monitoring Security Is Necessary
A good continuous monitoring security applies automated tools, intelligent threat data, and individuals to monitor and scan the system at any given time. This continuous perspective is helpful to identify new issues instantly and switch defenses before attackers can take advantage of these issues.
Combining active measures with continuous monitoring security, organizations will be able to reveal threats earlier and forecast new attack patterns and remain resilient to APTs and ransomware that continue to be popular.
How Qualysec Technologies Can Help You
Qualysec Technologies is a market leader in cybersecurity. We perform sophisticated and confirmed testing. Our services also include the latest vulnerability assessment services that are in tandem with the new cyberspace threats. Our continuous vulnerability assessment services ensure that organizations are ahead of the evolving threats through automatic scans and by hand.
Services
- Ongoing vulnerability testing
- Automated vulnerability scanning
- Advanced Penetration Testing
- 24-hour security surveillance
How We Work
- Qualysec has an established test procedure, which combines automated testing with in-depth manual inspections. This minimizes false alarms and locates real issues correctly. Customers receive easily comprehensible and practical data to reinforce the best proactive cybersecurity strategy. The entire vulnerability management cycle, i.e., the initial step, which is the identification of threats through to their remedies and constant monitoring of these threats, with the security management at the center stage, is under our belt.
- We have a group of cybersecurity professionals who develop individualized plans that resonate with the threat environment and day-to-day requirements of every client. Our list of security issues is quite extensive, including web and mobile apps penetration testing, cloud security, API security, and IoT device security testing. Deciding on Qualysec will allow you to have a reliable partner who is striving to reduce the risk and keep you in compliance in the modern-day, layer-filled threat environment.
- We can depend on and repeat our results, unlike other people in the industry, because we are highly process-based and testing results. We continue enhancing our procedures to incorporate the latest AI/ML-based test tools and introduce ongoing vulnerability testing to the general proactive cybersecurity strategy.
- Concisely, Qualysec does not just identify issues. We assist your organization in establishing powerful, long-term protection against present and future cyber attacks.
Help your business make the step up in the realm of cybersecurity by having the experts of Qualysec Technologies offer you a continuous vulnerability assessment to secure your business – Contact now!
Conclusion
Continuous vulnerability assessment is an essential defense against the rising cyber threats in the world. Experts project over 50,000 vulnerabilities this year alone. This makes it critical for organizations to stay ahead of attackers and reduce zero-day risk. Unlike periodic testing, continuous monitoring provides constant visibility into the security environment. It enables teams to identify and resolve issues quickly. This enhances the vulnerability cycle, reduces attack surfaces, and enhances the general resilience. By adopting the continuous vulnerability assessment, the organization will develop a more adaptable posture over security that will keep pace with the fast-changing tactics used by the attackers, safeguard the essential electronic resources, and remain compliant in the ever-more challenging setting.
Learn how the new continuous vulnerability test provided by Qualysec can save your business effectively and efficiently. Call Qualysec Technologies and increase your security!
Frequently Asked Questions (FAQs)
1. What is continuous vulnerability assessment, and how does it work?
Constant security Vulnerability assessment is an ongoing process that frequently scans the IT systems using automated tools and a review by a human being. It detects, gives priority, and resolves real-time problems. It combines scans and continuous monitoring, and real-time threat detection, reducing the gap time between the discovery of a vulnerability and the application of a patch. This makes organizations stay ahead of the changing threats and reduces the risk at all times.
2. How does it differ from periodic vulnerability testing?
Regularly, periodic testing occurs every month, quarter, or otherwise. It provides a security record of such instances. The process of evaluation never ends. It is automatic and detects and corrects issues instantly. This reduces the time available to the attackers to exploit the weaknesses, enhances real-time detection, and enforces security in the day-to-day operations rather than focusing on the scheduled test.
3. What are the benefits of continuous monitoring in cybersecurity?
The constant monitoring provides free time feedback on threats and weak points. This helps you to identify and respond to emerging risks promptly. It minimizes the downtime and smooths the running of work by eliminating unexpected failures. It aids in remaining rule-compliant and aids in the future-oriented approach to cybersecurity. Continuous monitoring through continuous updating of the vulnerability cycle raises the level of security and reduces the size of the attack surface by fixing critical flaws on time.
4. Can continuous assessment reduce zero-day risks?
Yes. Continuous testing and automated vulnerability scanning eliminate zero-day risk. Unusual behavior is discovered, and new issues are uncovered nearly in real time. Organizations can use temporary fixes or patches to run patches quickly by scanning and monitoring systems to seal huge holes before attackers exploit unfamiliar vulnerabilities. This restricts the time of exploitation of zero-days and keeps business operational even in the context of rapidly evolving threats.
5. What are the key metrics to track in an ongoing vulnerability program?
The program considers key measurements such as the number of discovered vulnerabilities, time to fix, coverage of important assets, false alarms, and the effectiveness of incident response. The rate at which new problems appear measures the speed of discovery. The fix time shows how quickly teams implement solutions. Asset coverage guarantees that the program addresses all essential systems. The program minimizes false alarms, and response monitoring demonstrates its capability to prevent threats over time.





















































































































































































































































































































































































































































































































































































































































































































0 Comments