In 2026 the financial institutions are operating in growing pressure. Data leaks, ransomware and supply chain attacks are now hitting the major giants. For every other sector operating upon the bank, insurance companies or financial partner firms are now under heavier responsibility. As the customers believe with their money, identities and their livelihoods. Once something gets breached, the entire belief would be shaken.
The Office of the Superintendent of Financial Institutions introduced basically focuses on the Technology and Cyber Risk Management Resilience. Instead B-13 guideline concentrates on enhancing governance, operational resilience and security controls. And makes it mandatory for Federally Regulated Financial Institutions (FRFIs).
This guide will give you the core principles, a practical compliance checklist, common pitfalls, the shift from B-10 to B-13, measuring process and what this means for FRFIs and the clients who depend on them.
Need help with B-13 requirements? Let our experts guide you.
Understanding OSFI and B-13 Guideline
The B-13 guidelines govern FRFIs (Federally Regulated Financial Institutions) and are primarily in place to help maintain the security and stability of financial systems. B-13 has come into effect as of January 1, 2024 and builds on/updates the previous B-10 framework, with updated and improved guidance around technology and cyber risks. While they apply directly to FRFIs they form an independent best practice point for all firms associated or established within the Canadian financial ecosystem, and specifically cater for institutions handling cross border data flows.
At a high level, the B-13 Guidelines are structured around three fundamental elements: Governance, Risk Management and Response. Firms are required to map all technology assets from legacy and cloud systems, to emergent AI solutions, and identify their respective technology risk (including third party technology risk).
In a year when cyber-attacks are commonplace, B-13 provides a level-headed and structured response mechanism as opposed to a reactive approach.
How OSFI B-13 Is Actually Structured
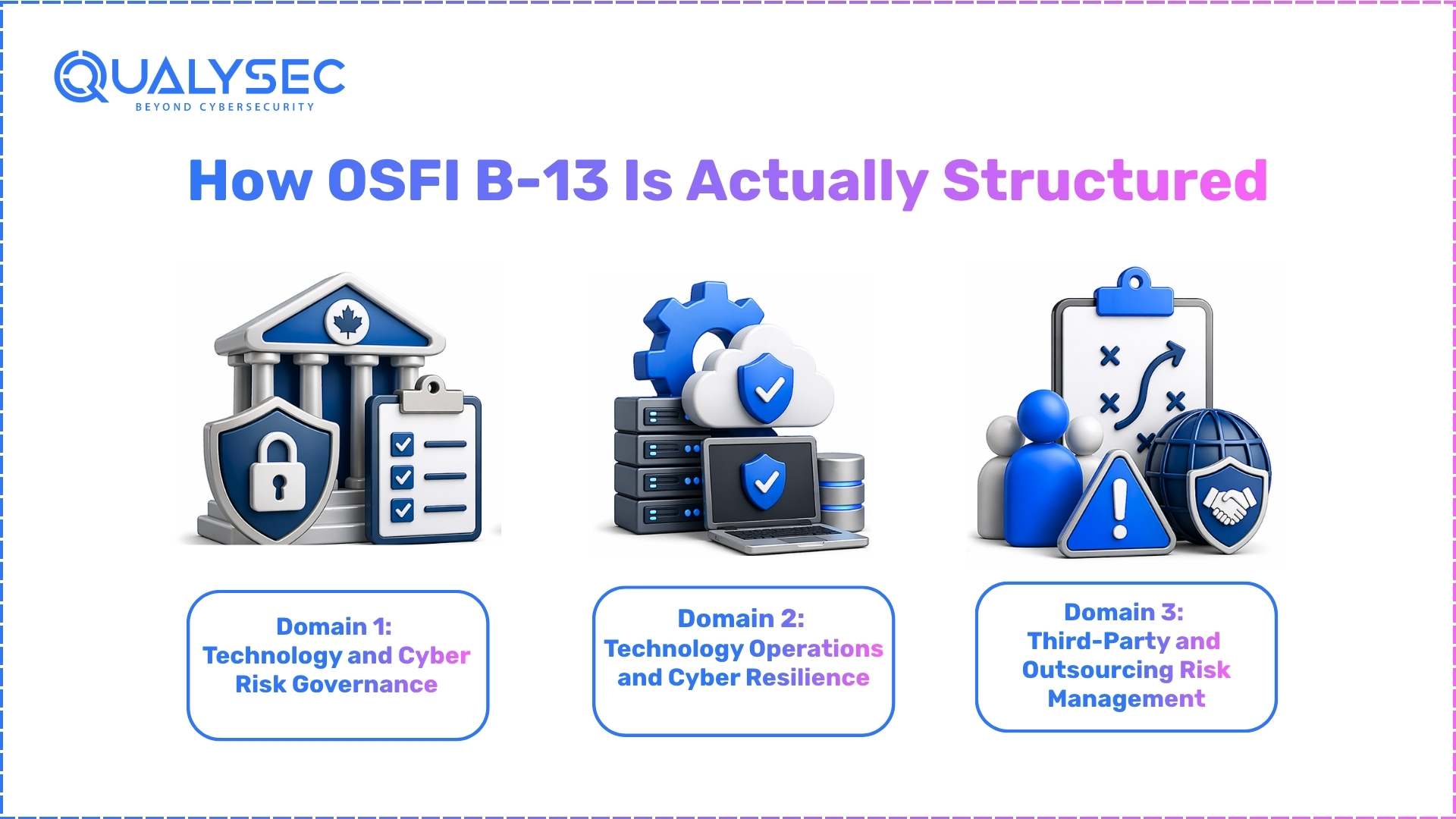
Here’s a quick overview of what actually constitutes OSFI B-13, before delving into what your institution needs to do. The guideline is laid out in three domains and all your institution’s expectations exist within these three categories. In total there are 12 principles contained within those three domains and it’s helpful to have a basic grasp of which category each of your compliance efforts fall under, not necessarily all 12. This is because the self-assessment tool provided by OSFI rates your institutions by domain, rather than by task.
Here’s what each of those domains include:
Domain 1: Technology and Cyber Risk Governance
This domain involves accountability at a higher level within the institution. What that entails is your institution’s ownership of technology and cyber risk from both senior management and the board, where the institution’s risk appetite comes from, how to build out your risk management functions and what the right cyber risk culture looks like, rather than IT being the only ones interested. Four of B-13’s twelve principles belong in this domain and nothing else in your institution’s program will hold up under the microscope without having informed and active oversight by leadership.
Domain 2: Technology Operations and Cyber Resilience
This domain constitutes the main area of work for your institution when it comes to B-13. What that involves is your institution’s technology asset management, how your systems are designed, how change control and project management are handled, daily operations, cyber security controls in place, and the actual resilience of the institution to cyber incidents. Six of the twelve B-13 principles exist within this category and it is the largest of the three domains and often the biggest area of gap for institutions. Asset inventory and resilience testing usually make up the largest proportion of B-13 tasks within this domain.
Domain 3: Third-Party and Outsourcing Risk Management
This domain of B-13 includes anything that comes into your institution through the outside world. What this covers includes vendor, cloud and third party service management, as well as third party incident management and reporting duties. There are two of the twelve principles contained within this domain. Third party risk is consistently the domain institutions misjudge, because the risk doesn’t come from their own system but another and your institution is responsible none-the-less.
Need OSFI B-13 penetration testing? Qualysec can help.
Compliance Checklist: Mitigate Risks Step by Step
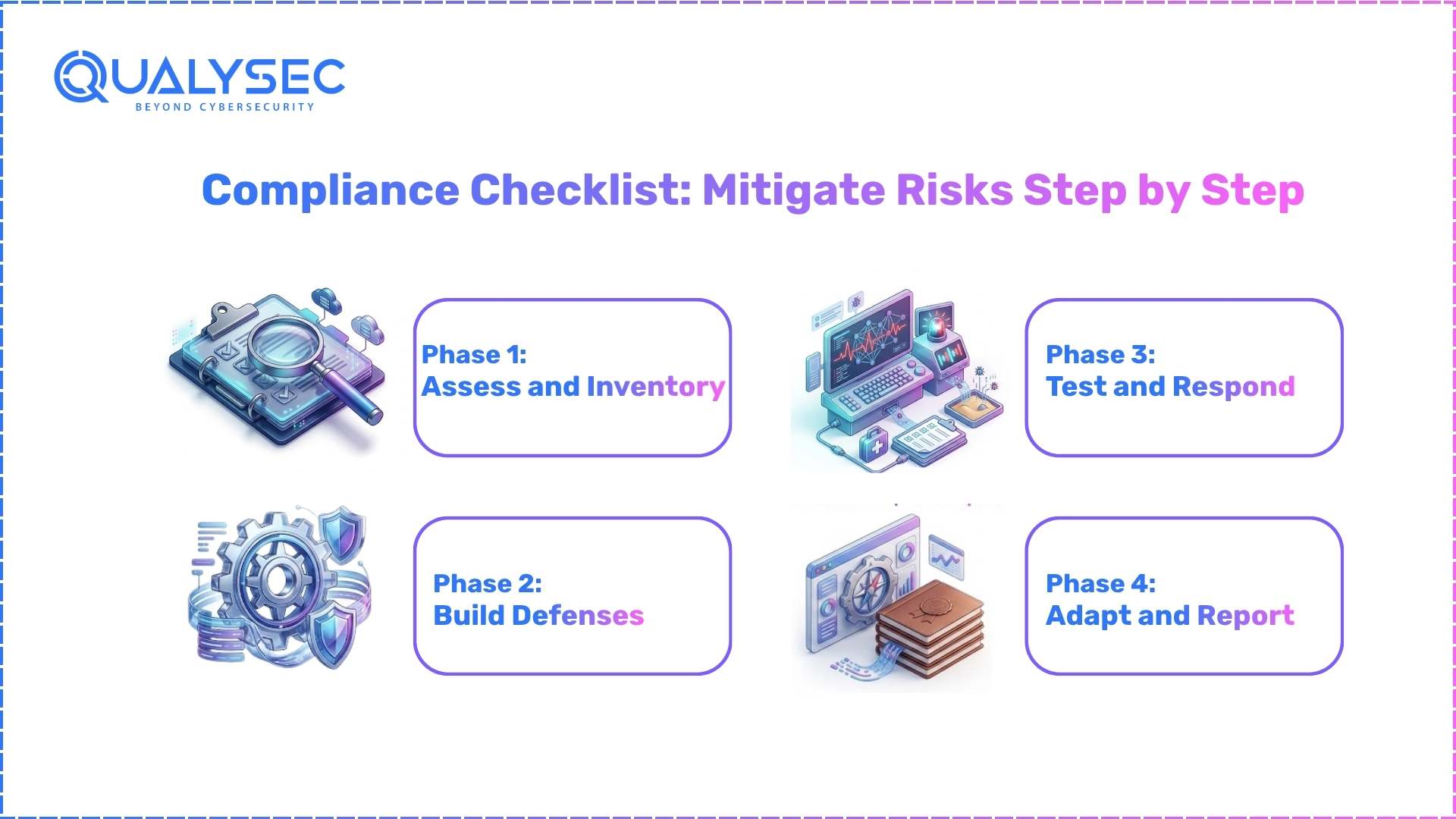
Principles matter only when they become action. These steps are used for the actual implementation of the guideline, they are not part of B-13 domain structure as detailed above. Below is a checklist that you can go through and review quarterly:
Phase 1: Assess and Inventory
- Identify all technology assets in your organization, from hardware and software to cloud to artificial intelligence. Mark which ones are critical.
- Complete a baseline risk assessment. By how likely will each risk happen and its impact
- Review your third parties. The B-13 test should be applied to high-risk vendors first.
Phase 2: Build Defenses
- Identify clear cyber risk steerers, and top it up with quarterly board briefing.
- Implement critical controls including MFA, encryption, and network segmentation.
- Revise vendor contracts to mandate incident notice in a specified time frame, usually 24 hours.
Phase 3: Test and Respond
- Author in-depth playbooks for every incident phase from detection to containment, to eradication, and finally to recovery.
- Run tabletop exercises twice a year and conduct a full-scale test annually.
- Track key metrics like mean time to detect and mean time to respond, aiming for tighter windows each cycle.
Phase 4: Adapt and Report
- Utilize OSFI’s self-assessment tool to gauge the level of maturity achieved against each principle.
- Present to leadership using business-aligned language that relates to risk.
- Update the asset inventory for all major changes, deployments and incidents.
This structured approach fosters disciplined compliance as opposed to a one-off activity.
Stay compliant with advanced penetration testing services.
Common Pitfalls and How to Avoid Them
Even the solid programmes encounter challenges. These are the most common areas where teams falter and practical ways to address them.
- Incomplete Inventories: Unaccounted-for cloud platforms and devices create unmonitored vulnerabilities. Bring the IT, operations and procurement teams together for a detailed discovery process. A little investment here saves many times more later.
- Weak Vendor Oversight: Relying on vendor contracts lacking a breach notification clause leaves the institution open to unknown risks. Revise templates to include stringent breach reporting timelines and mandatory annual audits.
- Skipping Tests: Static playbooks gathered Dust never address a real event. Schedule regular testing of tabletops and full drills just as you would a fire drill.
- Overlooking Proportionality: An overly rigorous approach for smaller organizations is bound to create burnout. Prioritize the program scope according to size and significance, focusing first on the most critical assets.
Practical Insights: What B-13 Means for FRFIs and Clients
B-13 means a more integrated, seamless approach to cyber risk for FRFIs, as it aligns closely with existing operational realities, instead of being another independent initiative. An initial inventory exercise typically highlights unacknowledged growth of cloud adoption, while contract remediation closes gaps that would otherwise represent likely supply chain attack vectors.
Clients enjoy enhanced service due to increased system resilience (reduced transaction delays) and increased confidence their data remains protected as a result of improved vendor oversight.
Faster decision-making is ensured by better governance. B-13 complements other global frameworks (particularly on asset inventories and cyber governance), creating a consistent approach for cross-border entities.
B-13 vs. B-10: What’s New and Why It Matters
B-13 is not just a simple update of B-10. It sharpens the earlier guideline to address current threats more effectively.
Key Upgrades:
- Deeper Third-Party Scrutiny: Increased third party management, B-10 mentioned outsourcing as part of a compliance requirement. In B-13, it’s mandated that institutions will have formal, risk based assessments of all outsourcing, and their contracts will contain cybersecurity controls that align with the requirements of the guideline.
- An expanded inventory: It specifies that all of your IT infrastructure, cloud services, and Artificial Intelligence and Machine Learning systems must be inventoried.
- Mandatory resilience testing: It is no longer good enough to have playbooks and practice annually, or as a best effort. Institutions are expected to test annually, to identify whether their playbooks are reliable. Also, they must document success metrics of their incident recovery.
These updates make sense given the significant increases we have seen in supply chain attacks over the past 24 months, as well as increasing pressure from global regulators for enhanced cybersecurity.
For institutions who currently rely on B-10, the first steps of their compliance efforts are to identify where their current systems and documentation fall short against B-13 guidelines. Typically, this often relates to third party risk management, and visibility into AI/ML and other uncounted technologies.
Measuring Success: Tools and Metrics
Progress must be measured. OSFI’s free self-assessment tool gives institutions a structured way to score themselves across governance, risk management, and response.
Key performance metrics include:
- Assets: The percentage of systems that have been identified, categorized by risk, and documented.
- Incident Response Times: Identifying your mean time to detect, and mean time to respond to threats. A target of less than 24 hours is reasonable.
- Third Party Compliance: The portion of all critical vendors who undergo annual review.
- Test Pass Rate: How well your incident playbooks perform during incident exercises and penetration testing.
- Incident Trends: The decline or increase in specific types of repeated incidents.
Basic dashboards are a good start, but all institutions need to have reviews of performance at a leadership level. The key is to align numbers with actual business metrics like reduction in operational downtime and customer confidence.
Need expert penetration testing for financial institutions? Get a free quote now.
How Qualysec Connects the Dots to B-13 Compliance
Qualysec offers a transparent approach to achieving B-13 compliance without unnecessary confusion. The process involves focusing on outputs as required by the guideline:
- Asset discovery and inventory to provide your institution a full map of the IT infrastructure, cloud and devices that often go uninventoried.
- Risk assessments of your third parties to evaluate each vendor and identify weak points in the system.
- Penetration testing and incident exercises designed to meet resilience requirements of B-13.
- Guidance with OSFI’s self assessment tool, allowing you to generate an accurate score of your performance.
- Quarterly check-ups to ensure that your organization’s program stays up to date as threats evolve.
Step Into Resilience Today
OSFI B-13 guidelines are not just another compliance effort. They provide the practical, yet essential, blueprint necessary for navigating the cyber risks of 2026 and beyond. From detailed inventories to well-practiced playbooks, every component will reinforce the trust institutions and their clients have in the stability of their financial information.
Organizations will find they will differentiate themselves not by the number of cyber incidents they experience, but by their readiness and ability to respond and recover seamlessly.
Begin phase one of this process this week. Download the free OSFI self-assessment tool. If you are ready to accelerate your compliance efforts and need a partner to navigate the intricacies of the guideline, Qualysec is available to offer expert assistance.
Resilience isn’t an overnight achievement. It requires one conscious decision to move forward.





















































































































































































































































































































































































































































































































































































































































































































0 Comments