Introduction
Modern cybersecurity cannot be without penetration testing programs. Organisations worldwide face increasing cyber threats daily. That is why it becomes important to develop strong security. This is a complete guide on how to develop and sustain effective penetration checking schemes in your company.
The cybersecurity threats keep changing. Therefore, organisations must stay ahead of potential attackers. Penetration testing systems assist in vulnerability identification before it can be used by malicious individuals. Moreover, security posture is a useful insight that is given by these programs.
A properly organised pentest program entails organised testing, reporting, and remediation. In addition, it needs continuous improvement and adaptation. The article encompasses all requirements to make penetration testing programs successful. In addition, we discuss the maintenance strategies that guarantee the long-term effectiveness.
What Are the Essential Components of Penetration Testing Programs?
To learn about the penetration testing programs, it is necessary to learn their main features. To start with, organisations need to have clear objectives. Then they require good structures of governance. Also, the testing methodologies need to be spelled out.
Building Your Program Foundation
The penetration testing programs begin with strong underpinnings. First, organisations ought to measure their present security posture. They can then be able to know vital assets that need protection. In addition, the creation of governance guarantees the maintenance of stability in the oversight within the lifecycle of the program.
The best penetration testing programs are based on the technical security assurance framework. Moreover, this framework has several testing settings. Security architecture and security monitoring services are also encompassed. Thus, organisations have to take time to configure appropriately.
Key Program Elements:
- Management and control by the structure of governance and responsibility.
- Technical security framework with capabilities of monitoring and vulnerability assessment.
- Testing procedures that matched the industry standards and organisational requirements.
- Remediation processes ensure vulnerabilities are addressed promptly and effectively.
This is based on a study conducted by the CREST Penetration Testing Guide, where structured approaches are seen to be of great help to organisations. In the meantime, ad-hoc testing tends to fail to identify significant vulnerabilities. Thus, the systematic penetration testing programs are more effective.
Defining Testing Objectives
A pentest program has clear objectives that guide it. To start with, the organisations need to decide what they intend to accomplish. After that, they are supposed to match testing with business objectives. Also, testing goals are usually motivated by compliance requirements.
Regulatory compliance requirements are some of the common reasons behind penetration testing programs. Moreover, organisations are usually prompted by recent security incidents. There are also major changes in the IT infrastructure that necessitate testing. Therefore, the context of such drivers enables the prioritisation of testing activities.
Significant Subtraction: Organisations must not consider penetration testing as a one-time check box activity. Rather, constant testing is a guarantee of up-to-date security. Additionally, threat landscapes are evolving, and it is necessary to update the assessment regularly.
How Do You Establish Governance for Penetration Testing Programs?
This is through governance structures that make penetration testing programs effective. First, companies have to establish monitoring committees. These teams then organise testing processes. Besides, sound governance can help maintain the uniformity of quality in all tests.
Creating Management Frameworks
Management commitment is needed to have an effective pentest program governance. First, the top management should assist in security programs. Then, proper budgets should be provided. Also, talented resources require adequate training and equipment.
The management and technical personnel should be involved in the governance team. Moreover, they should be allowed to make decisions. In addition, direct access to high-level management is important. Thus, an organisation needs to be keen on the choice of the members of the governance team.
Governance Roles and Responsibilities Table:
| Governance Role | Key Responsibilities | Required Skills |
| Program Manager | Oversees entire program, coordinates activities, reports to leadership | Project management, security knowledge, and communication |
| Technical Lead | Defines testing methodologies, reviews findings, and validates remediations | Deep technical expertise, penetration testing experience |
| Compliance Officer | Ensures regulatory requirements are met, maintains documentation | Regulatory knowledge, audit experience, and documentation |
| Risk Manager | Assesses vulnerabilities, prioritises remediation, and tracks metrics | Risk assessment, business acumen, analytics |
Coursera courses on penetration testing planning emphasise the importance of governance. In the meantime, those organisations that are poorly supervised usually fail. This is why early governance avoids complications that may arise in the future.
Scope and Change Management
The best penetration testing programs have good scope definition. Organisations first identify target systems. They then rank in terms of criticality. In addition, change management processes will make sure that new systems are tested accordingly.
All key systems within the firm should be included. Nonetheless, attention is paid to the critical infrastructure. On top of that, special attention should be given to sensitive data handling. This means that organisations have to strike a balance between holiness and feasibility.
What Testing Methodologies Work Best for Penetration Testing Programs?
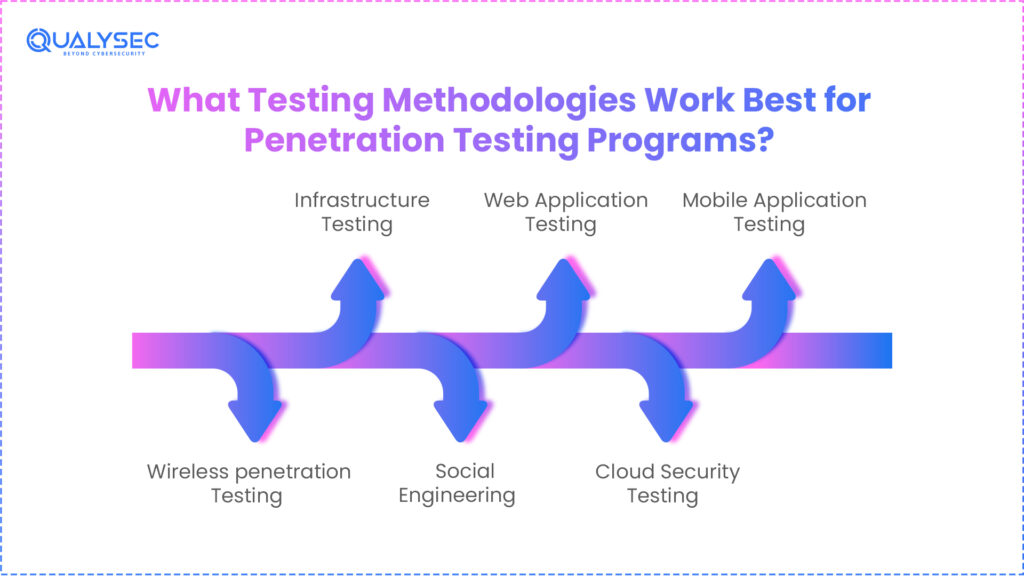
Proper choice of methodologies is a deciding factor in the effectiveness of penetration testing programs. To begin with, the organisations should be aware of various testing methods. After that, they select some approaches that suit them. Also, several methods can be combined, which usually brings the most positive outcomes.
Testing Styles and Approaches
There are testing styles used in penetration testing programs. Black box testing is an attack that simulates attacks. Meanwhile, the white box testing gives comprehensive information about the system. Moreover, grey box testing presents an intermediate way.
All the testing styles have varied functions in pentest program structures. Perimeter security is tested effectively by black box tests. On the other hand, white box tests are effective in detecting deep vulnerabilities. Thus, organisational leaders ought to employ several styles strategically.
Common Testing Types:
To secure complex environments, read our Advanced penetration testing program
- Infrastructure Testing: Examines servers, firewalls, and network components for vulnerabilities
- Web Application Testing: Identifies coding flaws and configuration issues in applications
- Mobile Application Testing: Assesses the security of iOS and Android applications
- Wireless Testing: Evaluates WiFi and wireless network security controls
- Social Engineering: Tests human factors through phishing and manipulation attempts
- Cloud Security Testing: Verifies cloud infrastructure and service configurations
These methodologies are taught in courses of Practical penetration testing courses. In addition, experience is invaluable. Hence, security teams must be effectively trained in organisations.
Testing Frequency and Scheduling
Regular testing schedules are provided as the best penetration testing programs. Baseline security tests are offered through annual tests. The quarterly testing is, however, more protective. Moreover, post-significant testing is also very important.
Assets of less importance should be tested less often than critical systems. Also, minimum testing frequencies are commonly determined by compliance requirements. Further, risk analysis assists in setting the right schedules. Therefore, organisations have to balance completeness and a lack of resources.
How Can Organisations Maintain Effective Penetration Testing Programs?
The penetration testing programs need to be maintained with constant efforts. To start with, organisations have to monitor testing results. They then bring about improvements in a systematic manner. Also, a periodic review of the program will ensure further efficiency.
Remediation and Follow-up
Remediation is necessary for the successful maintenance of the pentest program. Portfolio vulnerability should be first prioritised based on the severity. Thereafter, remediation plans are made. In addition, verification testing is used to ensure that fixes are done correctly.
Organisations must not treat symptoms, but root causes. In addition, it is also necessary to monitor remediation progress. Moreover, timelines that are realistic can be used to ensure they are accomplished. Consequently, vulnerability is stopped through structured remediation processes.
Remediation Best Practices:
- If there were critical and high-severity vulnerabilities, then act on them first.
- Give assignments of ownership and accountability to each of the remediation tasks.
- Have realistic yet strict deadlines depending on the risk levels.
- Fixes can be verified by retesting before vulnerabilities are closed.
- Prepared Lessons Learned and revised security standards.
- Measures of remediation effectiveness with time.
The comprehensive penetration testing lab guide describes realistic remediation strategies. In the meantime, organisations acquire knowledge through the testing cycle. Thus, the culture of continuous improvement is inculcated into security.
Measuring Program Success
The penetration testing programs require quantifiable standards of success. KPIs monitor program effectiveness. Moreover, measures reflect worth to stakeholders. Besides, the trend analysis indicates a security improvement with time.
The most frequent metrics are vulnerability discovery rates and remediation times. Also, it is possible to track repeat vulnerabilities to find out whether processes are effective. In addition, the comparison of test results between the years indicates improvement. As a result, data-based solutions improve the work of pentest programs.
Key Performance Indicators:
- The number of critical vulnerabilities found in each test cycle.
- Mean time to fix vulnerabilities by the severity of the vulnerability.
- Share of systems that are being tested on time every year.
- Repeat the vulnerability of successive tests.
- Comparison of the cost per test with the cost of a breach that may occur.
- Staff score improvement on security awareness.
Why Is Qualysec the Best Company for Penetration Testing Programs in the USA?
In the selection of the appropriate partner, it is important when it comes to consider the implementation of penetration testing programs. Qualysec is one of the leading cybersecurity firms that focuses on full penetration testing schemes. Moreover, they have experience in industries and testing procedures.
Qualysec has the best penetration test programs that are provided by certified professionals and established procedures. Additionally, they are aware of specific issues that are experienced by US organisations. Also, they have a worldwide presence that guarantees uniform quality of all their interactions.
Qualysec’s Unique Strengths
Comprehensive Service Offerings: Qualysec offers end-to-end penetration testing programs such as web application testing, network infrastructure testing, cloud testing, mobile testing, and API testing. What is more, they provide the exercises of the red team and security code review.
Certified Expertise: The Qualysec staff are certified professionals in the industry, with such credentials as OSCP, CEH, and CISSP. Furthermore, the ongoing training will make them abreast with new threats. Hence, customers are provided with advanced security tests.
Proven Track Record: Qualysec has been able to provide penetration testing programs to Fortune 500 companies, financial institutions, health institutions, and government organisations. Also, they retain their clients at a rate of more than 95%. This, in turn, portrays a quality and value delivery.
Compliance Support: Qualysec is an expert in assisting organisations that need to comply with PCI DSS, HIPAA, SOC 2, or ISO 27001. Moreover, their reports are compliant with the requirements of an auditor. They also offer continuous consultations on compliance.
Advanced Methodologies: Qualysec has some of the best frameworks, such as OWASP, PTES, and NIST. Further, they tailor strategies to the individual needs of clients. Thus, the testing is in-depth but realistic.
Ready to Strengthen Your Security?
Arrange a no-charge consultation with the penetration testing specialists at Qualysec. Learn how thorough penetration testing solutions safeguard your company against computer attacks.
Make a free consultation with Qualysec now by visiting
The focus on excellence at Qualysec makes them the perfect partner for those organisations that aim at bestpenetration testing programs. Moreover, they are transparent in their communication so that the stakeholders can be able to understand findings. Also, executive summaries and technical analysis are provided in comprehensive reporting. Thus, actionable insights are obtained by both the management and technical teams.
Visit Qualysec’s Resources page for free penetration testing guides, whitepapers, and industry insights that help organisations build stronger security programs.
Conclusion
The development and sustenance of penetration testing programs is a process that must be planned and committed to. First, organisations have to develop clear goals. This is followed by governance that makes it performed regularly. Besides, frequent testing and cure prevent the changes in threats.
The implementation of a program starts with the knowledge of the needs of an organisation. Moreover, it is important to choose the correct penetration testing methodologies and the frequency of tests. Also, success is quickened by collaborating with seasoned providers such as Qualysec. Hence, the penetration testing programs should be viewed by organisations as ongoing security investments.
The cybersecurity environment keeps changing at a fast pace. As a result, the best penetration testing programs become dynamic. Organisations where systematic testing is given primary importance benefit greatly. Meanwhile, the ones that do not take security seriously are getting threatened more and more. In this way, the introduction of penetration testing programs is becoming a key to contemporary business success.
Take Action Today! Don’t wait for a security breach to reveal vulnerabilities. Start building your penetration testing program now with expert guidance from Qualysec. Talk with our penetration testing experts
Frequently Asked Questions (FAQs)
Q.Why is a penetration testing program needed?
A penetration testing program will find the security vulnerabilities before they are exploited by the attackers. The pentest programs should be structured in a way that the organisations would be assured of the security of all their systems at all times.
Q.How often should pentesting occur?
Tests on critical systems through the best penetration testing programs are at least once a year. Nonetheless, quarterly testing is more protective, and organisations ought to test right after making major changes to their infrastructure.
Q.Is penetration testing required for compliance?
Numerous requirements require penetration testing initiatives, such as PCI DSS, HIPAA, and SOC 2. Thus, the organisations should apply routine testing in order to keep the standards acceptable and prevent terms.
Q.How is ROI measured?
ROI of the pentest program is gauged by lowering breach cost, compliance maintenance, and efficiency in vulnerability remediation. Organisations estimate the costs of potential breaches that have been stopped by proactive penetration testing programs.





















































































































































































































































































































































































































































































































































































































































































































0 Comments