As cloud-based software takes center stage in the modern era, compliance with industry standards and benchmarks such as SOC 2 is becoming the need of the day for SaaS companies. Hence, achieving SOC 2 compliance is more a matter of ‘when’ than of ‘why.’ Keeping that in perspective, here’s an easy-to-use SOC 2 compliance checklist to assist you in planning and initiating your compliance process. In this blog, we will understand what each process under SOC 2 compliance requirements entails and also provide a convenient way to align your SOC 2 with the trust service criteria.
SOC 2 Requirements Checklist
Effectively designed SOC 2 compliance requirements for SaaS will provide step-by-step instructions that organizations can follow to fulfill the wide-ranging requirements of the framework. These requirements are related to security, availability, processing integrity, confidentiality, and privacy that will help companies in achieving SOC 2 compliance.
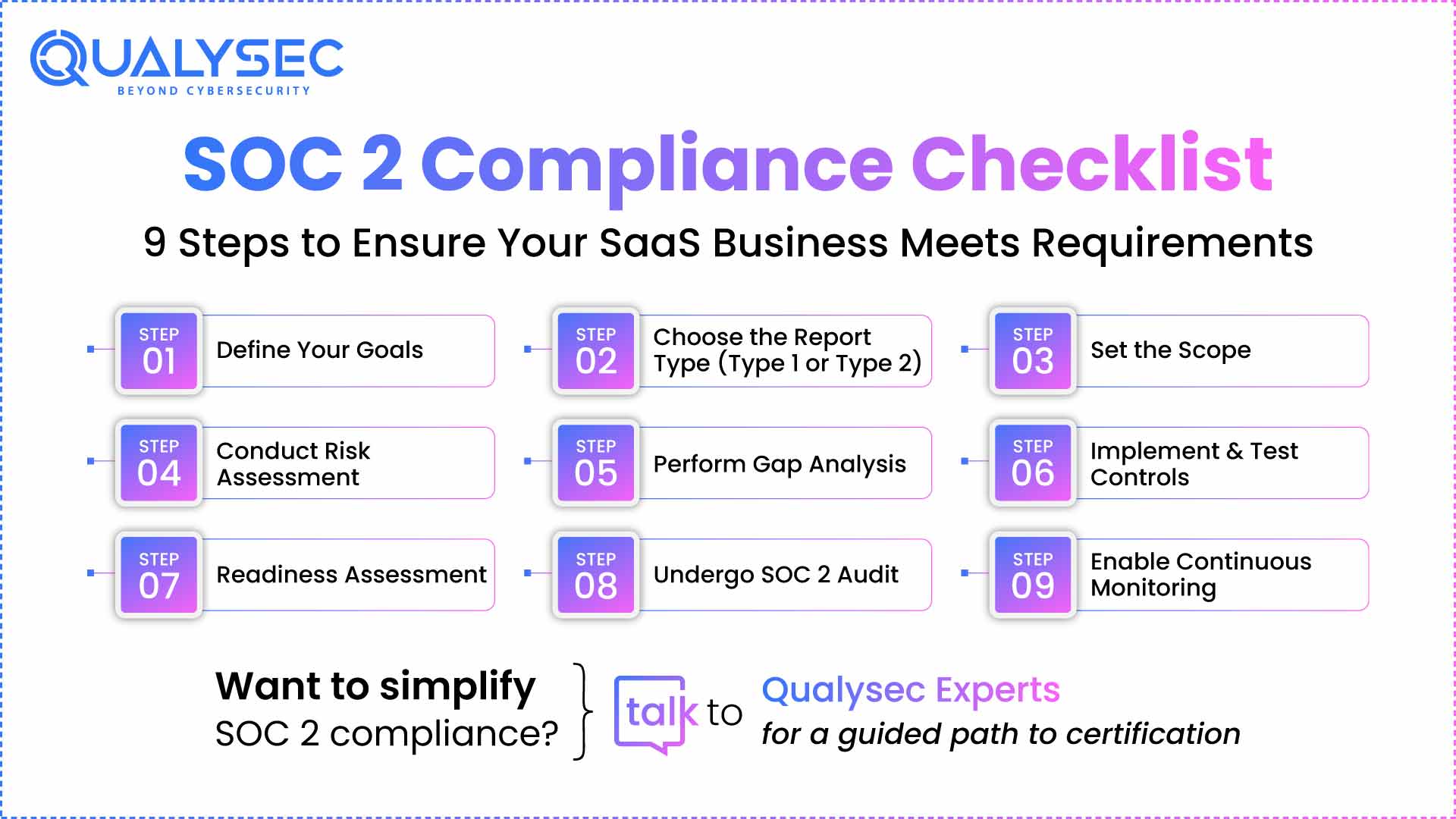
Below is a 9-step SOC 2 checklist:
1. Choose your objectives
The first step of the SOC compliance checklist is to specify for what purpose you want the SOC 2 report. The precise reasons why SOC 2 compliance matters to you would be the final goals and objectives to achieve in your compliance path.
With a clear vision of your goals, you can focus the SOC 2 process on your specific reasons for seeking compliance. This will also help guide decision-making through the determination of scope, building a cross-functional team, control evaluations, auditing, and taking remediation action to fill gaps.
2. Identify the type of SOC 2 report you need
SOC 2 reports are either Type 1 or Type 2. You have to determine which one is suitable for you, depending on your compliance objectives. A Type 1 report takes less time and represents the performance controls at a single point in time, and certifies that you have internal controls.
Type 2 verifies that the controls are performing as predicted when monitored over time, and you will probably be required to generate a Type 2 audit report. It is detailed and requires a monitoring period for the controls that can be up to 6 months, but it gives the complete image of your security controls.
3. Define scope
Defining your scope is important because it will show the auditor that you understand your data security needs according to the SOC 2 compliance checklist. It will also organize your process by removing the criteria that are not relevant to you.
You need to establish the scope of your audit by choosing the TSC that is appropriate for your business based on what kind of data you store or transmit.
Keep in mind that Security as a TSC is required. Compliance needs will also impact your criteria choices. That being said, based on our experience, most SaaS companies will only require Security, Availability, and Confidentiality (or all three combined) as TSC in their SOC 2 journey.
4. Conduct an internal risk assessment
Risk assessment is important in your SOC 2 compliance process. You need to determine all the risks and document the scope of the risk from defined threats and vulnerabilities. Assign a probability and a consequence to each risk that you have identified, and then implement measures (controls) to limit those by the SOC 2 checklist.
After you have listed the risks, assign a score based on their impact and the probability that such a risk scenario will occur. Organizations are often guilty of scoring risks using intuition and not facts. A more effective, auditor-endorsed method of scoring risks is by utilizing industry-grade benchmarks.
A compliance automation platform, such as Qualysec, constructs an accurate, current inventory of assets and provides you with the tools and functionality to delineate risks at an asset level. You can use its detailed risk register to identify risks of your assets.
Suggestions: Security Testing Methodologies: Definitions, Processes, Checklist
5. Perform gap analysis and remediation
You need to review your existing control status and security processes, and how their compliance posture compares with how they comply with SOC 2 compliance for SaaS platforms requirements.
This can be simplified by using a compliance automation tool such as Qualysec, which integrates with your applications and scans the environment for vulnerabilities and control gaps. You can see the status of all controls, risks, and issues that need your attention from a single dashboard. The auditor-friendly dashboard also enables you to gather compliance evidence automatically.
6. Implement relevant controls and test them
After the gap assessment, put in place the controls to address compliance and maintain asset security under review. These could involve changing security processes, adding employee training modules, and developing fresh process documentation, among others. The risk scores (conducted earlier) will guide you in prioritizing controls.
Once you’ve put the controls in place, test them to make sure they are effective. This is an important component of SOC 2 Type 2 because here the auditor checks whether controls are functioning as intended.
Issues you’re likely to encounter at this point are not remediating or not being notified of failing controls promptly, and ignoring issues of non-compliance that expose you to the risk of failing auditor expectations.
You can correct these with an automated tool such as Qualysec that maps risks into compliance criteria and controls automatically, initiates automated testing to validate controls, and tracks their health on a single dashboard.
Once anomalies have been identified, initiate alerts and remediation processes to the respective risk owner. Time-based, context-aware alerts result in timely resolutions across the risk lifecycle, avoiding escalation of issues. Request a demo today to observe Qualysec’s live control dashboard.
7. Undergo readiness assessment
Undertake a readiness test to determine if you have the minimum SOC compliance in place to go through an entire audit.
The following are your areas of focus for the test:
- Gap analysis – It tries to identify gaps and vulnerabilities and create a list of detailed recommendations and steps. It requires 2-4 weeks from initiation to completion.
- Controls matrix – It consists of the objectives map, internal controls identification, and control features.
- Auditor documentation – It includes writing the auditors’ request list and testing procedures.
According to the results of the auditor, correct the areas of weakness by re-mapping some controls or adding new controls. Although technically no company can ‘fail’ a SOC 2 audit, you need to fix discrepancies so that you get a good report.
Readiness assessment entails writing policies, associating checks with appropriate controls, assessing risks without any gaps, and gathering evidence correctly. Performing these manually leaves a wide scope for human error and derails the audit process.
Qualysec assists you in giving momentum to compliance activities by providing pre-configured templates, pre-mapped controls, an automated evidence gathering system, and an exclusive auditor dashboard.
Read more: What is a Compliance Security Audit?
Become SOC 2 compliant effortlessly. Speak with Qualysec experts today!
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
8. SOC 2 audit
Appoint an independent certified auditor to finish your SOC 2 audit checklist and produce a report. Although the cost of SOC 2 compliance may be a main consideration, select an auditor with credentials and experience auditing companies similar to yours. During your Type 2 audit, you can anticipate a protracted sharing of information with the auditor as you respond to their inquiries, produce evidence, examine your internal samples, and identify non-conformities.
Generally, SOC 2 Type 2 audits can take anywhere from two weeks to six months, depending on the number of corrections or questions your auditor has. Type 2 has a required three to six-month monitoring period. A Type 2 report, then, provides greater insights into your company’s controls and its efficiency. Here are some of the questions the auditor can ask:
- Can you provide evidence to prove that your entire staff goes through background verification?
- Can you provide evidence of how you guarantee that the modifications in your code repositories get peer-reviewed before being merged?
- Can you prove with evidence that you revoke access to emails and databases immediately after an employee leaves your company?
- Can you provide evidence that you conduct background checks on all your employees?
Can you provide evidence of how you ensure endpoint security for all systems?
The Type 1 audit, by contrast, doesn’t involve an observation period, isn’t as invasive, and asks you to provide a snapshot (with documentation) of the different checks and systems (read: controls) you have implemented to satisfy the SOC compliance checklist. Be aware that once you pass your SOC 2 Type 1 audit, you will need to undergo an observation period of three months before applying for Type 2.
Also Read: A Comprehensive Guide to SOC 2 Penetration Testing.
Latest Penetration Testing Report

9. Establish continuous monitoring practices
Obtaining your SOC 2 compliance report is not a single incident. The report is only the beginning because security and compliance are ongoing processes. It is worth building a strong, continuous compliance monitoring practice because SOC 2 audits need to occur annually.
Ongoing compliance simplifies your future audits and increases the scope of compliance. If you work with the confidence of compliant practices, you can introduce more frameworks without impacting the practice or the org in general.
Your practices of monitoring should scale to expand with your business, make evidence collection easier, not impede employee productivity, notify you about non-compliant activity, and give you an accurate view of an entity-level, granular overview of your infosec health at any given time.
Manually monitoring IT infrastructures, in the absence of proper tools, leaves gaps, consumes bandwidth, and yields last-minute surprises.
Steer clear of these traps and realize audit success by continuously, automatically, and thoroughly monitoring your assets for compliance with Qualysec. Book a meeting with our cybersecurity experts now for free.
Aligning Your Checklist with SOC 2 Trust Service Criteria
During a SOC 2 audit, the AICPA’s five Trust Service Criteria (TSC) will be used to rate your organization. You have to look over your internal processes and controls to ensure that they meet each of the following requirements so you may adequately prepare.
The following are some guidelines on how to align your SOC 2 for SaaS readiness checklist with the TSC:
1. Security
It should be in scope for all SOC 2 audits and is thus known as the common criteria. It needs you to turn on access control, network firewalls, and other governance/operations controls to shield your applications and data. Turn on entity-level controls that define basic security policy.
2. Availability
Requires you to show that your systems adhere to operational uptime and performance requirements. So, put monitoring on system uptime and performance in place. Have disaster recovery and incident response mechanisms in place, too.
3. Confidentiality
Demonstrates how you protect sensitive information during its life cycle. Put access controls in place so that only approved users have access to data.
4. Processing Integrity
Have quality assurance tests to ensure the accuracy and reliability of data processing. Keep systems under control to process data in a timely manner and achieve the desired effects. It encompasses quality assurance processes and SOC tools to track data processing.
5. Privacy
Asks you to safeguard Personally Identifiable Information (PII) against breaches and unauthorized access by implementing strict access controls, two-factor authentication, and encryption.
Our experts at Qualysec have helped secure fintech, SaaS, and enterprise systems across 25+ countries. Manual + Automated Pentesting. No false positives. Actionable reports.

Conclusion
Even once compliance has been reached, work does not cease. SOC 2 demands strict, constant internal control audits in order to maintain SOC 2. With high standards to uphold, the journey to becoming compliant is hardly easy. For companies that work with sensitive customer information, though, the effort is well worth it to build trust and prove security commitments. With the SOC 2 automation platform, you can automate the entire process to avoid repetitive manual work.
Discuss with Qualysec’s specialists to learn more about SOC 2 automation and more.
FAQs
1. What is SOC 2 compliance, and why is it important for SaaS platforms?
Under the five trust criteria, SOC 2 compliance confirms SaaS solutions’ protection of consumer data. Establishing trust, meeting regulatory obligations, and acquiring corporate customers all depend on it.
2. What are the main SOC 2 compliance requirements for SaaS companies?
SOC 2 demands safeguards for confidentiality, processing integrity, availability, security, and privacy. To meet these standards, SaaS companies must document procedures, audit systems, and show regular operating practices.
3. How long does it typically take for a SaaS platform to become SOC 2 compliant?
Usually, SOC 2 compliance takes between three to twelve months, depending on a company’s existing infrastructure, preparedness, and whether they go with a Type I or Type II report.
4. What are the common challenges SaaS platforms face during SOC 2 compliance?
Typical problems include hazy security controls, insufficient monitoring tools, inability to map operations against trust principles—especially for startups with restricted resources or experience—and poor internal documentation.
5. How can SaaS companies prepare for a successful SOC 2 audit?
SaaS companies must conduct a gap analysis, implement mandated controls, document policies, educate staff, use automatic monitoring solutions, and involve qualified auditors or consultants to get ready.



















































































































































































































































































































































































































































































































































































































































































































0 Comments