Cyber threats become more advanced every year, and businesses don’t have the luxury of waiting for a breach to happen. Enter penetration testing. Suppose you are asking yourself how to perform a penetration test. In that case, it’s the process of safely replicating an attack in the real world to find existing vulnerabilities before a malicious hacker can exploit them.
This proactive approach to cybersecurity will strengthen company defences, protect sensitive data, and ensure compliance with industry standards. With the rise of AI-driven threats coming in 2025, penetration testing is more important than ever. So, let’s simplify the process and start understanding how to do penetration testing.
How to Do Penetration Testing: Step-by-Step Process
Penetration testing has a distinct gathering process that is conducted safely for identifying vulnerabilities. The penetration testing process begins with planning and ends with remediating the vulnerabilities discovered. Newer trends include AI tools and continuous testing to respond to and adapt to threats.
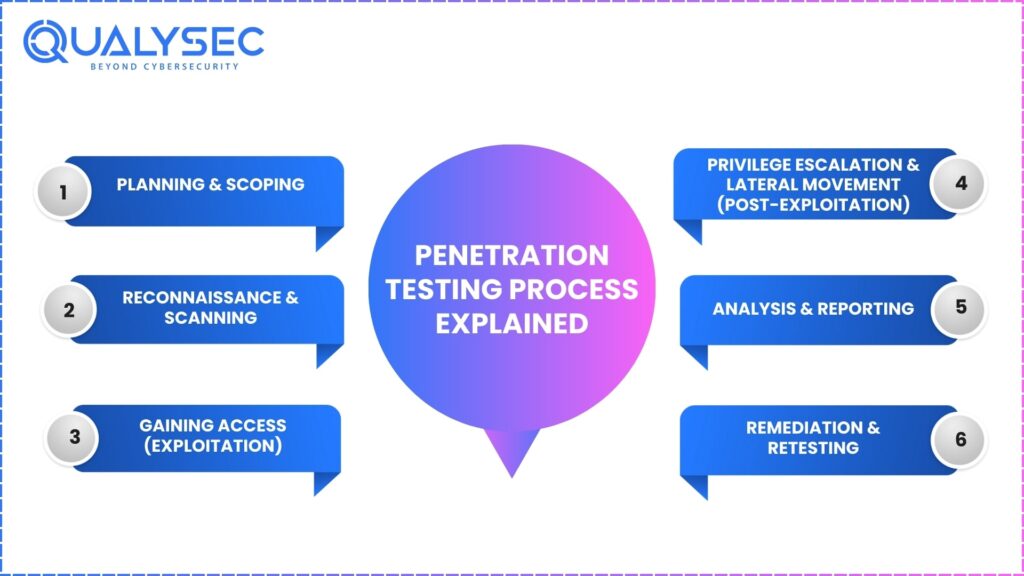
Here’s the breakdown:
Step 1: Planning & Scoping
First, determine the appropriate scope for testing, ensuring you are clear on what (specific servers, applications, or networks), and make sure you have approval to test the scope. Essentially, you’re establishing ground rules, goals, and scope so no one crosses the lines.
Step 2: Reconnaissance & Scanning
Now that you have your scope, it can be a search for information within that scope. You will want to use both passive reconnaissance, such as searching for domain information, and active scanning – directly probing the network with tools such as Nmap to map the network and identify the open ports.
Step 3: Gaining Access (Exploitation)
You can now use scan results to perform simulated attacks. Tools like Metasploit or Burp Suite can be very effective at breaching the system to clearly show the tactics, techniques, and procedures (TTPs) an attacker could use.
Step 4: Privilege Escalation & Lateral Movement (Post-Exploitation)
Once inside, explore the possibilities for privilege escalation – obtaining administrative access, as well as lateral movement to get access to other systems and resources. At this point, it is valuable to look for attack paths a criminal actor may take after making initial access.
Step 5: Analysis & Reporting
Provide recommendations, document the findings, including what you’re finding and how it was obtained. The findings should be easy to read and straightforward, with recommended actions to fix. NOTE: Your legal team and company executives will want to know what exists and how severe the issues and resolutions are. Request a free pen testing quote now!
Step 6: Remediation & Retesting
After providing findings, your team can remediate vulnerabilities discovered in the previous phase or exploit all vulnerabilities as intended. You will want to test your areas again post-remediation to ensure respective areas are secure. Rinse and repeat as needed.
Download a sample pentesting report here.
Latest Penetration Testing Report

How to Do Pentesting: Best Practices
The greatest value from penetration testing is achievable by treating it as a continuous security activity rather than a one-off project. Identify ways to leverage automation with a skilled human penetration tester.
This combined approach provides the level of analysis and speed you require. Ensure your penetration tests are customised to the systems you use and any third-party services such as cloud, API or IoT.
When you are ready to present your findings, ensure you clearly document your findings and explain them to others, both technical and business leaders, so everyone understands the findings and recommended actions.
Continuous testing will be an industry standard in 2025, and will be led by automation and AI-trained tools, which will identify risks at speeds that will eclipse human strengths. Focus your penetration testing on business objectives, rather than simply meeting compliance checklists, if you want your security budget to improve risk exposure.
Security teams should become familiar with guiding the outcomes from red, blue and purple teams to ultimately provide the effectiveness and resiliency required to mitigate risks against evolving threats.
Cyber threats don’t wait—neither should you. Partner with Qualysec to stay one step ahead. Schedule a meeting today!
How Can Qualysec Assist?
Qualysec is a penetration testing company that provides advanced services to helps organisations discover and remediate potential security gaps before adversaries can exploit them. Their team of certified ethical hackers uses a combination of manual testing and automation tools to help identify vulnerabilities in a wide range of systems, including web apps, mobile apps, networks, application programming interfaces (“APIs”), and cloud systems.
In addition to identifying security issues in security tests, Qualysec produces a thorough report with well-documented, step-by-step instructions to fix any problems. This Level of Reporting is able to be understood by both the technical team and the executive team.
Qualysec has also adopted artificial intelligence-driven testing in 2025 to make their assessments quicker and with increased accuracy.
Qualysec has worked with companies of all sizes, so no matter if you are a startup or an enterprise company, with its assistance, you can ensure that your organisation’s systems are compliant while reasonably protected from real threats. By working with Qualysec, an organisation can effectively improve its security posture, minimise its risk, and build trust with its customers.
Check Our Affordable Pricing Packages.
Qualysec helps you find and fix vulnerabilities before they become costly breaches. Start now.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Conclusion
Penetration testing is not just about safety; it’s an investment in your business’s reputation. As cyber attacks become faster and wiser (especially in the age of AI), testing from a proactive stance means you take charge.
By adopting AI-supported tools, enhancing your approach to continuous testing, and situating pen testing in the context of real risks, you can stay on the front foot. Ultimately, testing is not a one-off activity- it is part of an overall resilient and proactive security mindset.
Don’t wait for hackers to test your defences—let Qualysec do it first. Secure your business today.
FAQs
Q: How is penetration testing done?
Pen-testing starts by defining your goals and scope. Then, experts gather intel, scan systems, try to exploit vulnerabilities, and try to go deeper. Finally, they report their findings and retest after fixes to make sure everything’s secure.
Learn this Technical Guide to Information Security Testing and Assessment.
Q: What are the 5 steps of penetration testing?
The classic five are:
1) Reconnaissance (info gathering),
2) Scanning (finding weak spots),
3) Gaining Access (exploitation),
4) Maintaining Access or covering tracks, and
5) Reporting. Plus, modern approaches add remediation and retesting.
Q: Can AI do pentesting?
Yes! In 2025, AI tools are playing big roles—automating scans, prioritising risks, and even simulating attacks via AI agents. Startups like RunSybil show how AI “agents” can act like skilled hackers at machine speed.
Q: How long does a PenTest take?
It depends on size and complexity. Small apps might take a week; mid-size setups around 2–4 weeks; more complex systems up to 6 weeks total for test plus planning/reporting.

















































































































































































































































































































































































































































































































































































































































































































0 Comments