Introduction
Your company should guarantee that the critical software can withstand both a real attack and an audit conducted using a checklist. The security departments are expected to face a 30% increase in attacks using automated means to demonstrate the effectiveness of their solutions in a real-world scenario. Modern hackers are tech-savvy and would even take the time to wait. They are going to do more than just search for bugs; they will discover astonishing ways to use technology. The question of agentic penetration testing vs manual penetration testing has been raised.
Manual penetration testing still has the edge over automated and agentic solutions in terms of depth, accuracy, and context, despite their speed and large coverage area. It is a slightly different issue: we are talking about whether a proficient human attacker could not only beat your defenses but also be able to access what is most important to you.
Why Manual Penetration Testing Still Matters In 2026
The financial risk has never been greater. The IBM Cost of a Data Breach Report 2025 shows that the average cost of a global breach exceeds $4.4 million. One method has the potential to reduce legal and other associated costs, while another entails a long court battle and could even result in a loss. This course will examine the relationship between different security testing methods and pricing. We will not only discuss the technical mechanism, business ROI, and the hybrid future of security evaluations, but also take you through different scenarios for 2026.
In upcoming chapters, we will realize together that no one can expand pure human testing to fulfill the contemporary DevOps demand, but at the same time, we will show the reason why human ingenuity is still the main factor in complicated reasoning. Moreover, we will illustrate cases in which one testing method outperformed the other and build the case for the necessity of both. Security Expert in-depth or CISO in ROI, this is your primary source of reference.
AI is the new frontier of security. Protect your machine learning models from prompt injections and data poisoning with Qualysec’s cutting-edge AI/ML penetration testing services!
What Is Manual Penetration Testing?
Manual penetration testing entails a series of steps, which is the work of the ethical hacker; the professional hacker will perform the security evaluation hands-on. The human tester discovers a system using a mix of lateral thinking, creativity, reasoning, and outstanding technical knowledge, rather than merely scripts or automated tools that follow a preordained path. Not only do they look for a single entrance, but they also mimic a real enemy, figuring out how to use a hole to get the crowns’ information. This method relies on human ability to comprehend context and intent, which machines generally do not account for.
Manual penetration testing, as one of the extreme examples of the red teaming concept, will be the focus of our discussion: the use of any method to bypass security measures as the objective. Social engineering, complicated exploitation chaining, and physical security assessments could all be ways to go about it. The tester’s ability to ask what if and why during the process is the major benefit; that is, to investigate the obscure parts of your architecture that automated systems assume are safe because they comply with a known pattern.
How Manual Penetration Testing Operates
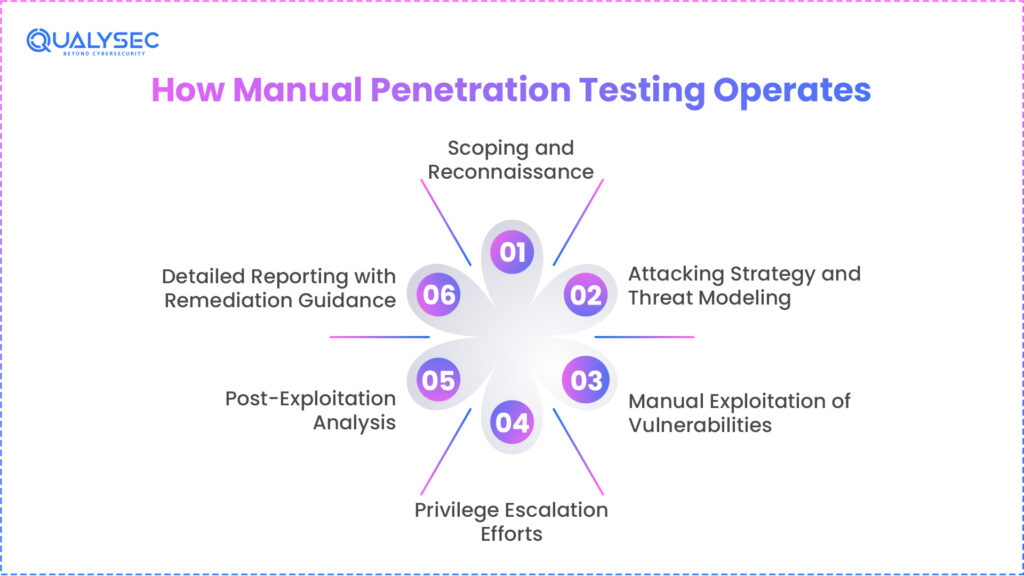
Scoping and Reconnaissance
Hence, scouting and reconnaissance are the first steps in which the human interviewer gathers data on the target company. A human, as opposed to a bot, deliberately searches for compromised credentials on the dark web, leveraging threat intelligence, studies the company’s LinkedIn for employee patterns, and maps the digital footprint. An understanding of the reasoning behind the infrastructure’s existence reveals the most probable entry points.
Attacking Strategy and Threat Modeling
Human testers create an attack plan that is uniquely suited to the application’s corporate logic. Furthermore, they anticipate which route a truly skilled threat actor would take to reach the most sensitive, specific information. By this time, the planning phase has ensured that the testing accurately reflects the company’s risk profile.
Manual Exploitation of Vulnerabilities
The tester generally needs to exploit the discovered weaknesses using specially developed tools tailored to the specific environment during web application pentesting. Attackers can bypass Web Application Firewalls (WAFs) by altering request headers in ways automated tools cannot mimic, revealing a flaw that is highly practical rather than just theoretical.
Privilege Escalation Efforts
A manual tester, using escalation-of-privileges techniques, attempts to advance from a visitor or low-level user to a super administrator as soon as they find a starting point. It is a complex task that may involve kernel hacking or exploiting a misconfigured service account. Being aware of this stage helps determine the blast radius of a potential infraction and what the attacker might do within it.
Post-Exploitation Analysis
The tester confirms which data may have been taken and for how long they could have remained unnoticed after the hack. This appropriately depicts the business’s detection and response capability. It addresses the fundamental question: If we were hacked today, how much actual harm would occur before we became aware of it?
Detailed Reporting with Remediation Guidance
The final result is a thorough report that prioritises risks by business impact, not just CVSS ratings, with remediation guidance. It follows a well-defined pentesting framework. In the framework of your particular code base, a person discusses how to solve the problem by providing customized guidance that helps developers address the problem without disrupting other features.
“Automated scans miss what humans can see. Leverage the ‘Human Element’ with Qualysec’s expert-led manual testing to uncover complex business logic flaws and protect your crown jewels!”
Key Strengths of Manual Penetration Testing
The depth and precision manual penetration testing offers make it still essential. Its major advantages are listed below, together with thorough explanations.
- Locates Complex Business Logic Flaws: People know how systems are meant to function. This helps testers spot logical abuse situations, including price tampering, workflow bypassing, or permission voids. Seldom detected by automated tools, these flaws cause many of the most expensive breaches.
- Detects Chained Vulnerabilities: Manual testers are particularly good at connecting high-impact exploits with low-severity issues. A little misconfiguration, together with poor access controls, might cause complete system compromise. Automated security testing tools usually list these problems separately without noting the cumulative danger.
- Adapts to Unusual Architects: Automated scanners often get bewildered by hybrid systems, older systems, and custom programs. Human testers are able to swiftly adjust, evaluate unreported behavior, and examine corner cases that tools miss.
- Mimics Advanced Persistent Threats: Manual penetration testing reflects the modus operandi of more advanced attackers. Testers can simulate actual adversaries rather than scripted threats by pausing, pivoting, and altering strategies mid-test.
- Offers Contextual Risk Evaluation: Every discovery is assessed within the company’s unique context as part of a broader risk-based security testing approach. Manual testing helps you understand not only what is exposed but also why it is important to your company.
Limitations of Manual Penetration Testing
Manual penetration testing has drawbacks that companies must fully appreciate despite its advantages.
- Time-Consuming Implementation: Several weeks can be needed for complete manual penetration testing. This renders it inappropriate for situations with fast deployment cycles or frequent code modifications.
- Increased Cost Per Involvement: Manual testing requires highly competent experts, thereby increasing costs. Although the value is great, conducting physical inspections across all assets regularly might not be practical.
- Less Frequent Testing: Manual penetration testing is typically performed once a year or after significant modifications as part of a red team assessment due to budgetary and time constraints. This produces gaps between test sequences.
- Dependent on Expertise Tester: The tester’s expertise and skill significantly affect the quality of the findings. Unstable knowledge can produce unequal results.
- Not Scalable for Continuous Testing: Large, active settings that alter daily cannot be kept pace with by manual testing. Rather than continuous monitoring, it works best for focused, high-risk evaluations.
Manual Penetration Testing: The Critical Pros & Cons
To balance our previous examination of Agentic AI, we must approach the Old Guard with the same thoroughness.
The Strategic Advantages (Pros)
- Unmatched Accuracy & Zero False Positives: Because a human expert verifies every single result before it arrives on your desk, you never squander time on ghost vulnerabilities. Unmatched Accuracy and Zero False Positives
- Creative Exploit Chaining: Humans can combine three low-severity faults to generate a single critical exploit, thereby chaining creative exploitation. For instance, utilizing a minor information leak to locate a username, taking over the account using a weak password reset flow, and thereafter utilizing a wrong admin panel to dump the database.
- Business Logic Expertise: Only a human knows that, even though the code generating the invoice is technically safe, User A shouldn’t be able to see User B’s statement.
The Inherent Limitations (Cons)
- The Point-in-Time Problem: A manual examination is only a snapshot. Your verified security posture is potentially obsolete the day following the test, the instant a developer modifies a single line of code. Learn about Cybersecurity Posture Assessment.
- High Cost of Expertise: You are paying for the years of expertise and the specialized hacker approach. This elevates manual testing as a premium service, not possible daily.
- Human Scalability: Over a 40-hour workweek, a human staff can only test so much. A purely manual approach becomes a stumbling block to the company’s expansion from 10 to 1,000 applications.
Download the complete Manual Penetration Testing Report to see detailed findings, risk assessments, and recommendations for protecting your security posture.
Get a Free Sample Pentest Report

What Is Agentic Penetration Testing?
Agential penetration testing comes after automated security development. Agentic artificial intelligence strategies plan and carry out multi-step threats utilizing autonomous agents, generally powered by Large Language Models (LLMs), even if classic scanners have a rigid, linear checklist. Imagine it like this: a metal detector; a typical scanner buzzes when it detects something. Like a robotic archaeologist, an agentic artificial intelligence finds a clue, decides to dig deeper, and modifies its tools as it uncovers more.
The system’s capacity to run on its own depends on its agential character. Rather than merely pointing out a fault, these agents research. If they reach a login page, they might search for associated usernames based on the website or try basic password changes. Able to follow the phases of an attack, far more deadly and so far more useful for testing than a simple vulnerability scanner.
How Agentic Penetration Testing Operates
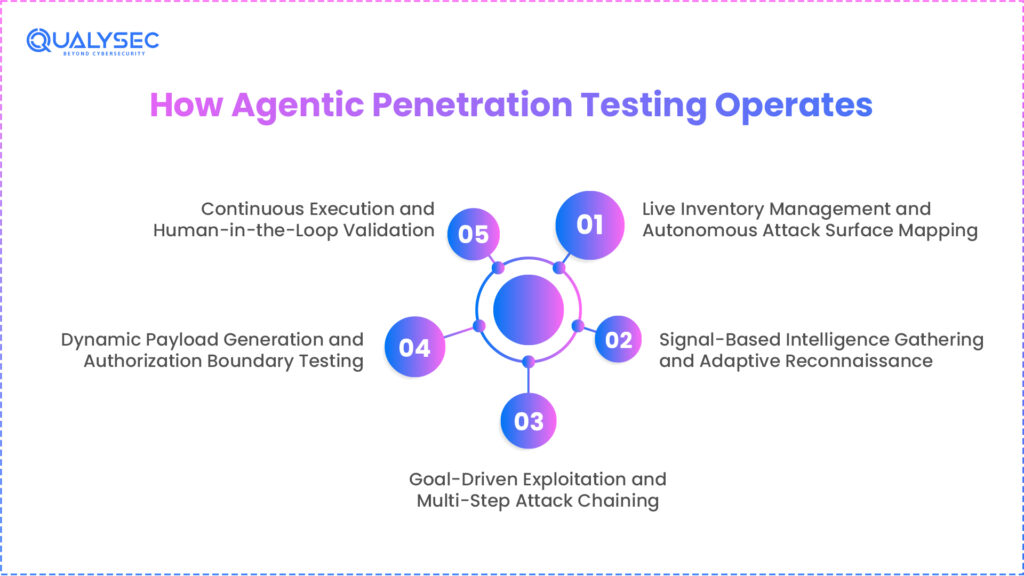
Live Inventory Management and Autonomous Attack Surface Mapping
Starting with a real-time constant reconnaissance engine mapping domains, subdomains, and cloud assets for autonomous attack surface mapping and live inventory management, agentic penetration testing. Unlike static scans, the agent searches for fresh services appearing in CI/CD pipelines, hence ensuring that the testing coverage remains up-to-date. This lets the system identify and approach newly revealed services or shadow IT long before a manual scoping process would even begin. Read about AI in cybersecurity.
Signal-Based Intelligence Gathering and Adaptive Reconnaissance
Deep endpoint and API schema enumeration helps the system identify specific defense layers, such as WAFs, and other technologies via adaptive reconnaissance and signal-based intelligence gathering. Beyond just collecting data, it looks at contextual clues, including response patterns and error message subtleties, to produce intelligence for the upcoming assault phase. The agent may avoid filters and modify its strategy to match the target’s specific digital footprint by means of knowledge of the basic infrastructure logic.
Goal-Driven Exploitation and Multi-Step Attack Chaining
Driven by high-level goals like data exfiltration or account takeover, agentic systems give top attention to attack routes leading to crown jewels rather than reporting individual flaws. By linking several low-severity flaws, the agent copies a complex opponent using an information leak to enable API misuse, for example. Should a route be obstructed, the agent automatically draws knowledge from the failure and changes its strategies to look for an alternate way.
Dynamic Payload Generation and Authorization Boundary Testing
Employing a Reason-Act-Observe loop, the agent creates custom, context-aware payloads that change depending on real-time server responses. Known as a part of comprehensive API penetration testing. It methodically investigates authentication pathways to find sophisticated weaknesses such as BOLA or horizontal privilege escalation that conventional fuzzing usually misses. The agent locates the specific point at which security measures fail by changing encodings and request structures, hence offering deep verification of authorization limits.
Continuous Execution and Human-in-the-Loop Validation
Agentic testing runs on a triggered model, re-testing contexts the moment code changes to reduce exposure windows, therefore enabling human-in-the-loop validation. It prioritizes signal-heavy reports based on actual exploitability, hence drawing attention to attacker advancement over hypothetical threats. Ensuring intricate logic errors get human validation, these confirmed paths are then given to human specialists who guarantee the agent manages the recurring work of exploitation.
Key Strengths of Agentic Penetration Testing
There are several benefits of agentic penetration testing that help address the constraints of manual-only techniques. Every real power mentioned below is explained.
- Permanent Security Verification: Agency systems are always in operation; hence, continuous permanent security verification is required. This means that developers identify flaws directly from code changes, configuration drift, or cloud scaling events, rather than months later during scheduled testing. When attackers use exposure windows lasting hours rather than weeks, continuous verification is vital.
- Faster Vulnerability Discovery: Agentic penetration testing reduces the gap between spotting a vulnerability and really recognizing it. Helps in bridging the gap between vulnerability assessment and real-world exploitation. Often, hours are required to find what would take weeks in a manual engagement. This pace lets security officers handle problems before attackers exploit them.
- Great Scalability throughout Assets: Agents powered by artificial intelligence can simultaneously evaluate thousands of APIs, domains, IPs, and cloud resources. This works for major companies using agentic penetration testing across different infrastructures. Manual testing just cannot scale to this level without incurring significant time and expense.
- Lowering Human Reliance on Low-Level Results: Agentic systems manage repeated abuse of already known flaws. This lets human testers concentrate on hazardous situations and complex analysis rather than simple checks.
- Easy CI/CD Integration: Agentic penetration testing can be simply added to CI/CD pipelines. This lets DevSecOps teams run security tests automatically with every deployment, without slowing down development teams.
Learn more about conducting a cloud security assessment to evaluate your APIs, domains, and cloud resources.
Limitations of Agentic Penetration Testing
Although agentic penetration testing is powerful, it has significant drawbacks that companies must understand to avoid excessive reliance.
- Constrained Knowledge of Business Logic: Artificial intelligence agents find it difficult to grasp understated corporate processes. Though they could spot technical flaws, they failed to recognize how the hidden use of real workflows is possible. Still, offering a field where human judgment is quite critical are errors in corporate logic.
- False Positive Risk Without Tuning: In challenging or poorly recorded environments, agentic systems can generate false positives. This can load development and security teams if not appropriately set up and confirmed.
- Cannot Totally Replace Human Creativity: AI sees patterns that have been gathered. It has the same lack of creativity or intuition as humans do. Uncommon instances of abuse and new threat methods could go unnoticed.
- Developing Requirements for Security Procedures: Companies lacking strong asset inventories, governance, and incident response processes may find it challenging to benefit from agile testing. Instead of clarity, automation without process maturity can lead to ambiguity.
- May Miss Complex Leverage Networks: While agentic systems can link flaws, they may overlook subtle blends that rely on situational awareness or non-obvious user behavior.
The Rise of Agentic Penetration Testing
Pros and Cons of Agentic Penetration Testing
Agentic penetration testing signals a change in philosophy from static automation to dynamic autonomy. Thanks to artificial intelligence agents, companies can now replicate complex attack paths that were previously only conceivable through human effort. Still, this technology comes with some compromises that every CISO must consider.
The Advantages (Pros)
- Continuous Security Verification: Unlike point-in-time manual tests, agentic systems operate continuously. The way they find flaws the minute a developer submits code to production makes them perfectly compatible with the DevSecOps movement. Read about Continuous Penetration Testing.
- Great Scalability: Agentic artificial intelligence enables simultaneous testing of thousands of microservices, APIs, and endpoints over a global reach. Particularly important for contemporary companies with extensive cloud architectures that no human team can manage in person.
- Rapid Speed to Discovery: Results are delivered in hours rather than weeks, enabling faster discovery. This speed helps security teams stay ahead of zero-day attacks and autonomous botnets seeking vulnerabilities online.
- Lower Long-Run Costs: By automating the detection of low-hanging fruit and repetitive tasks, agentic testing reduces long-run expenditures and frees up resources for more in-depth manual evaluations, lowering overall cost per found vulnerability.
The Strategic Limitations (Cons)
- Lacks Creative Vision: While artificial intelligence agents have difficulty with out-of-the-box human reasoning, they are very good at pattern detection. They might miss unusual business logic flaws that require either awareness of human purpose or of corporate structure.
- Privacy and Governance Risks: Strict administration is required when sensitive infrastructure data is fed into artificial intelligence systems. To prevent data leaks, groups must ensure their artificial intelligence testing partners comply with ISO 27001 standards.
- Partial Business Context: With the same urgency as a client-facing database, an artificial intelligence might detect a flaw in an interior staging server and address it. It often lacks the context to know which assets belong to a particular company as its crown jewels.
- Technological Hallucinations: Like all LLM-based technologies, agentic systems can occasionally hallucinate, producing incorrect positives or ridiculous threat routes that require human supervision to filter.
Contact us to know how agentic penetration testing can accelerate vulnerability detection, enhance security accuracy, and support a hybrid security approach for an organization.
Contact us for faster vulnerability detection

Manual Vs. Agentic Penetration Testing: Core Differences
You can make a fast decision by looking at how these two ideas diverge in reality. Though both Manual vs Agentic Penetration Testing hope to reveal weaknesses, their methods and outcomes vary dramatically.
Key Strategic Distinctions
- Testing Approach: Manual penetration testing is basically imaginative. Finding the one small fault that affects the entire house requires the hacker’s intuition and years of experience. Agentic penetration testing is scientific and algorithmic. It uses enormous computational horsepower to examine every conceivable attack combination at a pace beyond human capability.
- Frequency and Speed: Manual testing is too sluggish if you have to test a fresh ability you are launching right now. Agentic testing provides the nearly instantaneous feedback required for modern CI/CD pipelines. If you’re doing an annual audit for a billion-dollar merger, though, the constant, exacting approach of manual testing is precisely what you need.
- Depth vs. Breadth: Human testers go deep into a single application, uncovering flaws in how a user might use a shopping cart to get free stuff. Before a botnet does, agentic agents go wide, scanning 5,000 IP addresses in your global footprint to identify which ones have an unpatched MoveIt or Log4j vulnerability.
- Cost of Construction: Because you are paying for the time of very competent people, manual testing has a high floor price. Though the initial technological setup for an agentic platform requires significant investment, agentic testing lets you spread the cost over time, enabling more scans per dollar.
A Comparative Overview of Manual vs Agentic Penetration Testing
| Feature | Manual Penetration Testing | Agentic Penetration Testing |
| Primary Driver | Human Intelligence & Expert Intuition | AI-Driven Autonomous Agents & LLMs |
| Execution Speed | Weeks (Highly Intensive) | Hours to Days (Rapid Execution) |
| Frequency | Periodic (Annual/Quarterly/Major Releases) | Continuous (On-demand/Trigger-based) |
| Accuracy | Extremely High (Verified by Humans) | High (But requires initial calibration) |
| Complexity | Handles deep business logic & social engineering | Handles complex attack paths at a massive scale |
| Cost Basis | Per Engagement / Project-Based | Subscription / Asset-Based |
| Ideal For | High-risk apps, Compliance (SOC2/HIPAA) | Rapid Dev Cycles, Large Cloud Surfaces |
You might like to know more about Manual Pen Testing vs Automated Pen Testing.
When To Choose Which: Use Cases & Strategy
When Manual Penetration Testing Makes Sense
For high-assurance environments, manual penetration testing still comes out on top. Testing with this is ideal for high-risk applications where a single breach could harm a company’s reputation. Industries such as government, healthcare, and banking rely on manual testing because it provides the human verification needed for absolute certainty.
- Assessing Difficult Company Logic: Only a human can determine whether someone may misuse your app’s complex processes, such as multi-user rights or financial transactions.
- Compliance and Regulatory Audits: Some standards, like PCI DSS 4.0, require human-led penetration testing to ensure that security measures are not just present but also effective against a thinking adversary.
- Review of Possible Violations: Manual testers must conduct a deep dive following an incident to determine exactly how an intruder entered and any backdoors they may have left open.
When Agentic Penetration Testing Makes Sense
Agentic penetration testing is best suited for contemporary, fast software companies. It is for situations in which the attack surface changes frequently.
- Assisting DevSecOps Channels: In a world where new releases happen daily, agentic testing provides the always-on gatekeeper that standard manual testing cannot.
- Monitoring Growing Attack Surfaces: Agentic artificial intelligence gives organizations managing thousands of IP addresses and cloud assets a bird’s-eye view of risks across the whole worldwide footprint.
- SaaS and Startup Environments: Rising platforms that must demonstrate continuous security to corporate clients without the $100,000 monthly cost of human audits fit these environments.
The Business Impact: C-suite ROI Analysis
Penetration testing is an economic strategy rather than merely a technical checklist for a CISO or CTO. The question in 2026 is how well we are lowering financial risk rather than whether we are secure. Rather, the return on investment is critical for company continuity when you balance the cost of proactive testing against the awful repercussions of a breach.
The IBM Cost of a Data Breach Report 2025 indicates the average global expense of a data breach is $4.44 million. For businesses working in the United States, that number, however, hit a record high of $10.22 million per event. The return on investment (ROI) is not only good; it is crucial to business continuity when you assess the cost of proactive testing versus the severe consequences of a breach.
The Bottom Line: Cost of a Breach vs. Cost of Testing
Based on Ponemon Institute research and industry averages, the table below illustrates the big gap between the money invested in Manual vs Agentic penetration testing and the possible losses from a single security failure.
| Metric | Manual Penetration Testing | Agentic Penetration Testing | The “No Testing” Reality |
| Typical Investment | $15,000 – $100,000+ per engagement | $2,000 – $10,000 per month (SaaS) | $0 upfront |
| Primary Financial Goal | “Insurance” against logic breaches | Operational efficiency & scale | Immediate budget savings |
| Potential Breach Cost | $4.44M (Global Avg) | $4.44M (Global Avg) | $10.22M (U.S. Avg) |
| Recovery Time | Days to Weeks | Hours to Days | 241 Days (Avg Lifecycle) |
| Regulatory Fines | Minimized via expert compliance | Supports ongoing governance | $250,000+ per violation |
ROI for Decision Makers
- Manual Testing as High-Value Insurance: Consider manual penetration testing as an insurance policy against severe brand damage. Although the initial cost is higher, human specialists identify the business logic flaws that lead to the most costly violations. Spending $50,000 to avoid a $10 million intellectual property breach offers an ROI of over 20,000%.
- Agentic Testing as an Efficiency Play: Agentic Penetration Testing is an investment in speed. In contemporary DevOps systems, waiting weeks for a manual report creates a bottleneck that costs thousands of dollars in developer inactivity. Organizations employing artificial intelligence and automation extensively in security saved on average $1.9 million in breach expenses.
- Mitigating “Shadow AI” Risks: One of the most recent and costly risks in 2026 is Shadow AI employees using unsanctioned AI tools that leak corporate data. 29. Uniquely suited to finding these unlawful artificial intelligence endpoints and misconfigured APIs, which added an average of $670,000 to breach charges this year, agentic testing.
Request a custom pricing quote to learn how our solutions translate into real business value.
See our pricing, then talk with an expert to choose the best solution for your organization.

Why Most Organizations Need Both (Manual vs Agentic Penetration Testing) Approaches
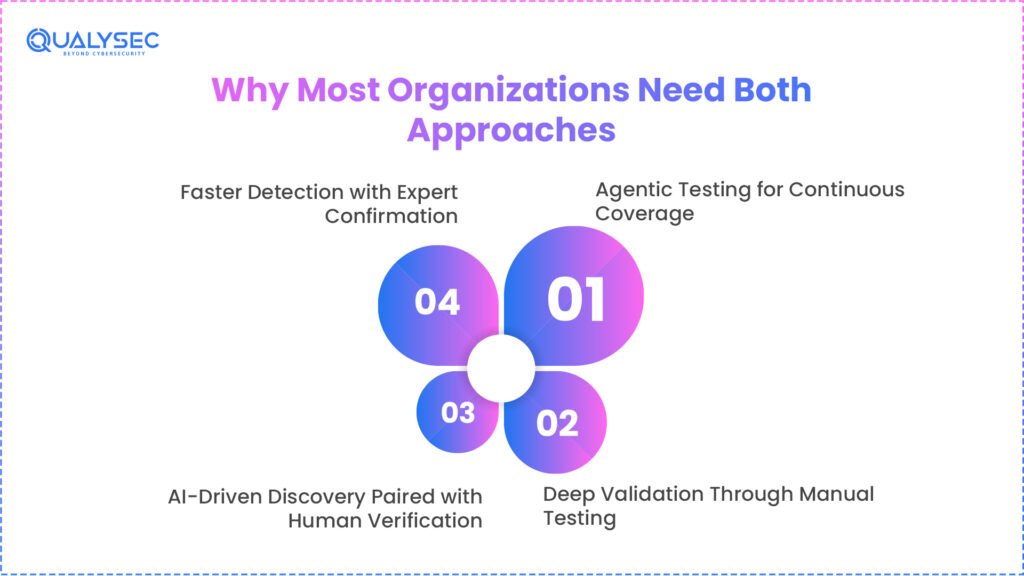
The argument on manual penetration testing vs agentic penetration testing is not about picking a victor but rather about creating a thorough ecosystem. Relying on one approach in 2026 is a strategic danger. Attackers employ automated bots for reconnaissance and human ingenuity for the final exploit; they are not limited to a single tool. Your defense needs reflect this truth.
I. Agentic Testing for Continuous Coverage
Code is released daily in a modern CI/CD setting. This velocity is beyond the manual testing’s capacity to keep up. Acting as your digital sentry, agentic AI offers continuous coverage. It guarantees that a Tuesday introduction of new functionality won’t unintentionally create a huge gap that goes unnoticed until the next handbook audit six months later.
II. Deep Validation Through Manual Testing
Although artificial intelligence can identify the open window, a human tester grasps the reasons for leaving it open and what it leads to. Manual testing explains the why behind the what. Validating that complicated security measures like multi-factor authentication or cross-departmental permissions are truly operating as planned under pressure is only possible by this means. This is critical for AI network security, where lateral movement and interconnectivity are complex.
III. AI-Driven Discovery Paired with Human Verification
This marks the zenith of the hybrid approach. Agentic artificial intelligence identifies 1,000 potential problems and maps the vast attack surface. Human experts next pare these down to the ten major vulnerabilities that pose the greatest danger. This does rid most security teams of the alert fatigue they suffer.
IV. Faster Detection with Expert Confirmation
The hybrid model lowers your Mean Time to Detect (MTTD) by cutting your Mean Time to Detect (MTTD). The human expert provides an instant remediation plan, while the agentic system detects an anomaly in seconds. This alliance guarantees that your developers are addressing actual problems rather than chasing machine fantasies.
Look at how AI cybersecurity threats can be detected and managed effectively by both Agentic and manual pentesting processes.
Common Myths Regarding Agentic Penetration Testing
Agentic penetration testing, like any other revolutionary technology, is rife with misconceptions that could cause poor executive-level decision-making. For a realistic security strategy, these fallacies must be cleared.
Myth 1: AI Might Completely Substitute Human Testers
This is maybe the most hazardous lie in the field. Rather than replacing the human brain, artificial intelligence is a force multiplier. Though artificial intelligence is good at analyzing large amounts of data, it lacks adversarial empathy, that is, the capacity to foresee how a human hacker would abuse a particular business process.
Myth 2: Agentic Testing is Simply Automatic Scanning
Conventional scanners resemble a metal detector; they beep when they detect a recognizable pattern. Agentic systems dynamically modify their strategies; they are like robot archaeologists who discover a clue and then try to interpret it. It is the gap between an automatic decision-making system and a stationary checklist.
Myth 3: Manual Testing Is Obsolete
Conversely, manual testing is becoming more focused. Human testers are free to focus on the most complex, high-impact flaws that machines will likely never detect, since artificial intelligence handles the low-hanging fruit (like basic SQL injection or unpatched software).
Compliance And Regulatory Considerations in Agentic vs Manual Penetration Testing
To an auditor, not every test is made equal. Most worldwide standards have changed their language as of 2026 to reflect the rise of artificial intelligence, but human-led validation remains a cornerstone of trust.
- PCI DSS 4.0: PCI DSS 4.0 expressly requires penetration testing for both internal and external environments, in accordance with the latest Payment Card Industry standards. Though agentic testing is a great way to meet the standard for testing demand, the annual high-level audit still requires a report signed by a trained human expert.
- ISO 27001 & SOC 2: These two frameworks focus on risk management. Auditors hunt for due diligence. A purely automated scan usually signifies due care, whereas a manual penetration test provides the evidence of a thorough inquiry that auditors need to grant certification.
- HIPAA & GDPR: For medical and data privacy, the context of the data is everything. An artificial intelligence is unaware of the legal ramifications of a patient record as opposed to a public image. Manual testers offer the impact analysis that shows regulators you appreciate the sensitivity of the data you protect.
Don’t let a failed audit slow down your growth. Qualysec provides globally accepted, compliance audit-ready reports that help you meet SOC 2, HIPAA, and PCI DSS requirements with ease! Talk to an expert to get started.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Challenges Teams Face When Choosing Between The Two
Despite a strong knowledge of the advantages, CISOs encounter major obstacles when applying these techniques or deciding between Manual vs Agentic Penetration Testing.
- Budget Distribution: It can be hard to justify the steep initial cost of a manual test when an automated cybersecurity solution appears less expensive on paper. The difficulty is justifying that ten times the price of the test itself might result from a single missed business logic flaw.
- Tool Sprawl: Many companies end up with 10 separate security tools that don’t interface with one another, creating tool sprawl. The objective is to find a partner who combines these into a single source of truth.
- Shortages in Competencies: There is a global shortage of millions of cybersecurity professionals. Agentic testing closes the gap by handling the grunt work, but you still need access to premium human talent for the last 5% of intricate exploits.
- Integration Difficulties: Without the right partner, integrating an agentic agent into a legacy on-premises infrastructure can be a nightmare. It demands a smooth transition between ancient, basic systems and current artificial intelligence.
Why The Future Is Hybrid
Past the Manual vs Agentic penetration testing argument are the most advanced security teams in the world. They have adopted a unified security nervous system.
Agentic artificial intelligence will manage the repetitive, high-speed scanning and initial exploitation of known weaknesses across the entire worldwide attack surface in the future. This works as a filter, clearing out the simple targets and the noise. This lets your elite special troops, the manual testers, concentrate their great intellectual energy on the most difficult, deep-seated faults no machine can detect. In an age of AI-driven warfare, this is the only means to defend a company; it is not simply a better means of testing.
Explore more about: AI Application Penetration Testing and Its Importance
Beyond The Tool: How Qualysec’s Hybrid Approach Redefines Penetration Testing
We at Qualysec feel that the argument of manual penetration testing vs agentic penetration testing is a false choice. You require the surgical precision of a human intellect combined with the tireless speed of an automated agent to navigate the 2026 threat environment. We offer a synergy rather than simply a tool; this guarantees every stone is turned.
Our method-driven approach monitors your attack surface around the clock using cutting-edge agentic technologies. It is always guided by an AI security audit checklist. As your developers send new code, this real-time capture of low-hanging fruit and developing weaknesses is caught. Still, we do not end there. These results help us to power our elite team of ethical hackers so that they may concentrate their efforts where they would be most effective: the deep-seated, sophisticated business logic no machine can really grasp.
Why choose Qualysec for your security roadmap?
- Context-Aware Testing: We get your company’s risk, not just find bugs. Our human testers translate the findings of our agentic scans to let you know precisely how a vulnerability affects your revenue and customer loyalty.
- Compliance Excellence: Our reports are prepared for auditors. Qualysec offers the human-verified documentation required by regulators, whether you are going for SOC 2, HIPAA, or PCI DSS.
- Zero Noise, All Action: Human verification helps us guarantee your engineers never waste a single minute on a false positive. Every vulnerability we submit is prioritized, verified, and practical.
Explore more about Advanced Penetration Testing Services.
Conclusion
The fight between agentic penetration testing vs manual penetration testing is not a zero-sum game; rather, it is a development of your toolkit. Depth, precision, and logic-based security assurance still depend on manual testing as the benchmark. It is your Special Forces group for your most valuable resources. Agentic testing, meanwhile, is changing the game by offering the speed, scale, and ongoing protection that human teams previously couldn’t maintain. Both methods help to identify AI application security risks.
Staying absolutely secure in 2026 calls for a combination of both in your approach. You need the creative, surgical accuracy of a human expert to protect the vault and the relentless, always-on vigilance of artificial intelligence to guard the gates. Adopting a hybrid approach not only reveals additional weaknesses but also fosters a secure culture that safeguards your brand, your information, and your bottom line.
Secure your digital future with the white-hat heroes of security. Whether you need a one-time deep dive or a continuous validation partner, Qualysec delivers zero-false-positive results that protect your business!
Find Your Perfect Security Partner

Frequently Asked Questions (FAQS)
1. Is Agentic Penetration Testing better than automated scanning?
Yes, quite so. Traditional automated scanning is static; It looks for a signature and then goes on. Agentic penetration testing uses artificial intelligence to think and change. Just as a human hacker would, but at machine speed, if an agent discovers a possible vulnerability, it may switch and try several methods to verify the exploit.
2. Can AI completely replace human penetration testers?
Not in the next few years. Agentic artificial intelligence has great scale, but it lacks the human intuition needed to detect errors in business logic. AI has difficulty grasping the purpose behind a series of events. For instance, while a human would realize they could alter the recipient’s ID in the background to send money, an AI might observe a Transfer Funds button to function flawlessly.
3. Which one is better for SOC 2 or HIPAA compliance?
Most compliance systems still favor or need manual penetration testing. Auditors want evidence of due diligence, which usually calls for a signed statement from a trained human expert. One great way to show auditors that you maintain your security posture between annual audits is to use agentic testing for continuous monitoring.
4. How often should I perform these tests?
The 2026 sector norm is leaning toward a continuous testing model. To detect immediate regressions, you should perform agentic testing daily or weekly (incorporated into your CI/CD pipeline). At least once or twice a year, or whenever you make a significant structural modification to your system, you should conduct manual penetration testing.
5. What is the most common vulnerability found by manual testers that AI misses?
Finding IDOR (Insecure Direct Object Reference) flaws and elaborate authentication bypasses is much better done by human testers. Usually based on the exact flow of a business process (such as the order of stages in a checkout), these flaws often arise because the code itself is not broken. AI often reads this as typical behavior.
If you have any queries about Manual vs Agentic Penetration Testing, our AI assistantis here to help. Ask now!






















































































































































































































































































































































































































































































































































































































0 Comments