The financial scene in the Philippines is becoming more advanced. Businesses are looking for faster operation solutions and a larger customer reach. Their demands are increasing with the emergence of internet banking, digital wallets, fintech platforms, and cloud-based accounting systems. As a result, Financial Vulnerability Assessment has become essential, as this digital expansion has also increased the attack surface for hackers.
Financial organizations, corporations, and SMEs are progressively targeted for their money and sensitive data they hold. This data comprises customer identities, transaction records, and proprietary financial data. One ignored security gap can lead to data breaches, financial fraud, legal penalties, and long-term reputational damage.
Here is where financial vulnerability assessment turns into an essential defensive mechanism. Rather than only responding to events once they have happened, companies can proactively spot and fix security gaps before hackers hack them. A deep Vulnerabilities Assessment helps to improve organizational resilience, reinforce compliance initiatives, and enable effective financial risk management.
Financial vulnerability analyses have become a business requirement for companies in the Philippines, where cybersecurity for financial services is increasingly important as the Bangko Sentral ng Pilipinas (BSP) and the Data Privacy Act’s standards are growing stricter.
What Is a Financial Vulnerability Assessment?
A technique of assessing financial risk exposure of any company resulting from operating flaws, technological shortcomings, regulatory non-compliance, and outside threats is known as Financial Vulnerability Assessment. Its goal is to find vulnerabilities that might cause legal repercussions, service disruption, or monetary loss.
A financial vulnerability assessment is progressive, unlike a standard financial audit and compliance review, which is mostly based on historical financial records and regulatory compliance. It assesses the financial state of the firm in light of prospective threats.
This process usually corresponds with:
- Enterprise risk management, which looks at risks throughout departments
- Business vulnerability analysis, which considers operational and technological aspects.
- Financial stress testing assesses resilience under difficult circumstances.
- Small and mid-sized companies especially need an SME financial vulnerability analysis.
Lack of advanced security infrastructure among SMEs makes them easy targets for hackers.
Common Threats Targeting Financial Institutions

Philippine financial institutions face a broad range of risks to their operations as well as in the digital world. The first step in risk reduction is knowledge about these risks.
1. Digital Exploits and Cyber Attacks
Banking systems, fintechs, and accounting programs are frequent victims of hackers via phishing, ransomware, malware, and API exploits. Expired software and outdated authentication systems highly contribute to vulnerability.
2. Financial Fraud and Insider Threats
Insider threats are among the grave risks. Unlimited access can make the employees or contractors unethically change financial records or leak confidential information. Not performing regular Vulnerability Assessment, such threats are normally not addressed.
3. Regulatory and Compliance Breach
Non-compliance with data protection legislation, or PCI DSS standards and BSP guidelines may result in serious sanctions. Poor compliance procedures can create significant financial vulnerabilities.
4. Risks of Third-Parties and Supply Chains
Outsourced suppliers, cloud service providers, and fintech partners could introduce hidden risks. Third-party appraisals must be included in an extensive corporate risk evaluation.
5. Market and Economic Volatility
Financial frailties may be exposed due to inflation, currency fluctuations, and interest rate changes. It is one of the reasons why financial stress testing is compulsory, considering the current financial risk management.
Key Steps in Conducting a Financial Vulnerability Assessment
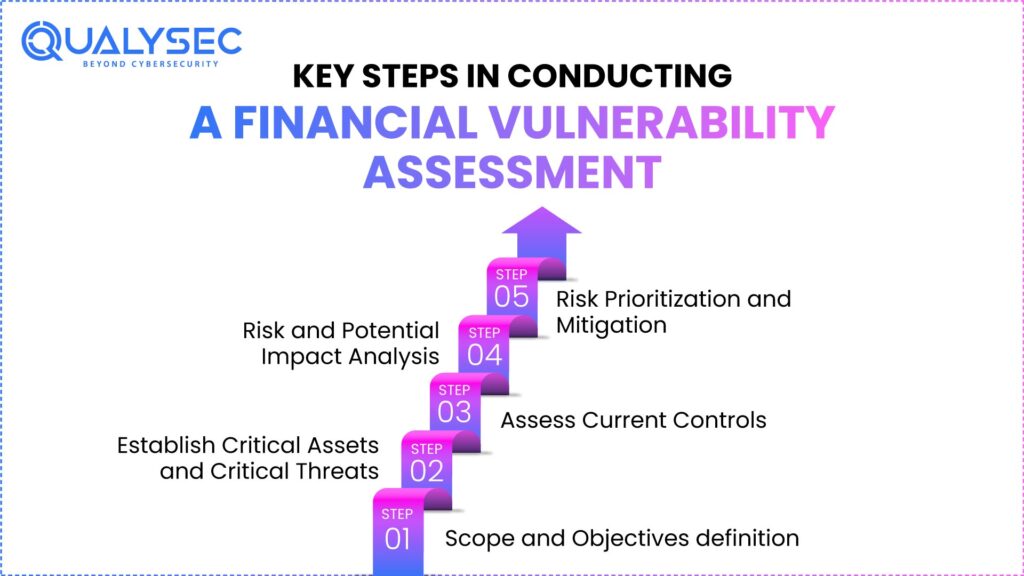
A systematic and repeatable method should be employed to carry out a financial vulnerability assessment to ensure that it is correct and efficient in supporting strong cybersecurity in fintech systems.
Step 1: Scope and Objectives definition
To start with, it is necessary to determine which financial assets, procedures, and systems can be analyzed. This may involve payment gateways, accounting programs, customer databases, and third-party integrations.
Step 2: Establish Critical Assets and Critical Threats
Organizations should include high-value financial assets and potential cyber threats on the list. This stage relates to some extent to a company’s vulnerability assessment strategy.
Step 3: Assess Current Controls
Present protection mechanisms, such as fraud detection, access control, encryption, and audit trails, are checked in order to estimate their effectiveness.
Step 4: Risk and Potential Impact Analysis
All identified vulnerabilities are analyzed through vulnerability testing, taking into account the probability of an incident and its consequences. This is a necessary stage for effective financial risk management.
Step 5: Risk Prioritization and Mitigation
Risks are assigned based on the level of severity, and remediation methods are developed to resolve the vulnerabilities with high impacts.
Take the first step toward a Financial Vulnerability Assessment. Download a sample penetration testing report.
Get a Free Sample Pentest Report

Identifying and Prioritizing Financial Risks
Financial vulnerabilities vary in level of threat. Effective prioritization enables businesses to wisely distribute their resources.
Usually, high-risk vulnerabilities
- reveal sensitive financial or consumer data.
- Turn on unauthorized purchases.
- result in legal fines or service interruption
Though they may still need attention, medium- and low-risk weaknesses can be fixed via phased remediation. This method enhances long-term stability and strengthens enterprise security risk assessment systems.
Tools and Techniques Used in Financial Vulnerability Assessments
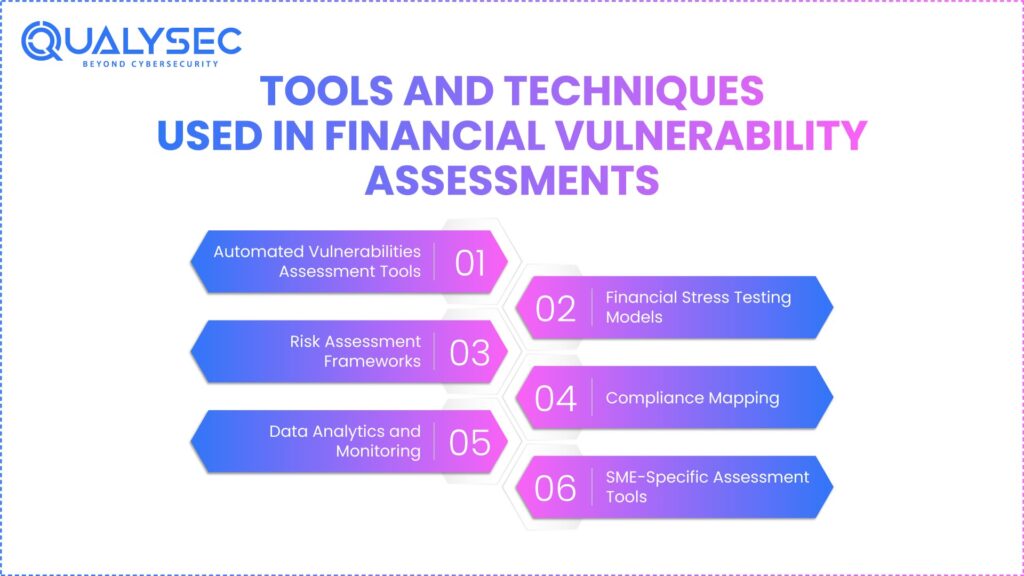
Modern financial vulnerability analyses use a combination of automated technologies and human-driven methods. Including these techniques helps businesses actively tackle threats before they grow into systematic failures.
1. Automated Vulnerabilities Assessment Tools
These systems scour known vulnerabilities, misconfigurations, and old software using these tools. They give real-time insight into the attack surface, therefore guiding security teams in prioritizing the repair of high-risk entry sites. Read to know more about Automated Security Testing Tools.
2. Financial Stress Testing Models
Financial stress testing helps companies assess resilience throughout crises by simulating worst-case economic scenarios. Institutions can use these simulations to determine possible capital deficiencies and modify their liquidity cushions in order to preserve stability during market instability.
3. Risk Assessment Frameworks
Financial security is brought in line with worldwide norms by frameworks including ISO 27001 and NIST. These frameworks guarantee a holistic approach to asset protection and offer a clear language to inform stakeholders of risk levels.
4. Compliance Mapping
Map controls help compliance projects and financial audits by supporting regulatory requirements. Automation in this area lowers the administrative burden of showing compliance with difficult requirements like Sarbanes-Oxley (SOX) or GDPR.
5. Data Analytics and Monitoring
Advanced analytics identify abnormalities, fraud trends, and questionable financial activities. Machine learning algorithms learn from past data to forecast and flag newly developing threat vectors in real time, so further perfecting these procedures.
6. SME-Specific Assessment Tools
Lightweight tools made for SME financial vulnerability analysis provide SMEs with cost-effective risk visibility. These tools give high-impact risks top priority, therefore first directing scarce resources toward the most serious security flaws.
Keep your fintech industry safe from cyber risks. Schedule a thorough security assessment today to identify vulnerabilities and strengthen your defenses.
Get Your Free Security Assessment
The Strategic Role of Penetration Testing in Finance
Although vulnerability scanning reveals possible flaws, penetration testing confirms whether those flaws may be used in real threat scenarios. By mimicking the methods, tactics, and processes (TTPs) used by hackers, it changes the point of view from a theoretical checklist to an active defense strategy.
In difficult financial settings, penetration testing targets crucial high-value goals:
- Online Banking Portals: Simulating cross-site scripting (XSS) and broken authentication to guarantee the security of consumer accounts.
- Payment Systems and API: Testing transaction flow integrity and protecting the digital glue that links modern fintech products to legacy cores via APIs and payment systems.
- Applications within Finance: Recognizing risks like privilege escalation that might let unauthorized employees start fraudulent transfers.
- Cloud-Based Accounting Systems: Searching for misconfigured access permissions and unsafe data storage that could expose sensitive ledgers.
By means of this active attitude, the general vulnerability evaluation procedure is improved. Showing precisely how a hacker might move around the network improves business vulnerability assessment results and gives leaders the proof they need to properly rank security expenditures.
Best Practices for Strengthening Financial Security
By using established best practices addressing both technological and operational flaws, companies in the Philippines can greatly lower their financial exposure. Regular vulnerabilities assessment and penetration testing are critical to find faults in financial systems, programs, and networks before hackers can take advantage of them. These evaluations help businesses correctly rank their remediation activities by offering evident insight into risk exposure.
Putting strict access control systems, including multi-factor authentication and role-based permissions, guarantees that outside parties and staff members only have access to the financial information needed for their roles. This lowers the likelihood of unapproved trades and insider threats. To prevent penalties and retain regulatory trust, equally important is matching procedures with financial security audit and compliance standards like BSP rules and data protection legislation.
Regular financial stress testing helps businesses assess their resilience in tough financial or operational situations, enabling executives to make educated choices amid ambiguity. Employee training also has a great impact; ongoing instruction on phishing awareness, fraud detection, and secure financial practices lessens human-related vulnerabilities.
Including financial risk in corporate governance structures finally guarantees financial security to develop, along with developing hazards by guaranteeing that risk management is a shared duty among management, technology, and operations.
Explore FinTech Cybersecurity Companies to Enhance Financial Security.
Case Studies: Lessons Learned from Real-World Assessments
Case Study 1: Mid-Sized Financial Institution
After a financial vulnerability analysis by a Philippine bank, API security issues were revealed. Early repair avoided possible data leakage and legal consequences.
Case Study 2: SME Fintech Company
Weak third-party access controls were found by an SME financial vulnerability assessment. Strengthening vendor risk management boosted investor confidence and compliance readiness.
Case Study 3: Large Enterprise
A thorough corporate risk analysis revealed flaws in fraud detection systems. Transactions that were fraudulent fell greatly after remediation.
See how our proven cybersecurity solutions help fintech companies protect sensitive data, meet compliance requirements, and stay secure – read the full case study.
See How We Helped Businesses Stay Secure

Benefits of Proactive Financial Risk Management
Proactive financial risk management goes beyond simple survival to strategic optimization to provide long-term company value. Companies avoid expensive data breaches and illicit transactions, otherwise draining capital and operating resources, by spotting and patching vulnerabilities before they use them, therefore reducing financial losses and fraud cases.
- Reduced Financial Losses: Constant monitoring guarantees that companies fulfill exacting industry standards, hence greatly lowering the possibility of hefty penalties and legal consequences from sophisticated worldwide supervision groups.
- Better Regulatory compliance: Showing a dedication to strong security measures comforts customers that their sensitive financial information is secure, so building long-term brand loyalty and a major competitive advantage in the market.
- Improved decision-making by means of risk visibility: Real-time risk data availability enables leadership to properly assign resources and change tactics depending on an accurate, data-driven awareness of the institution’s present threat landscape.
- Improved resilience against economic volatility: A proactive strategy lets companies create robust buffers and contingency plans, therefore guaranteeing their capacity to resist unexpected market shocks and keep operating continuity during world economic crises.
Organizations that actively tackle vulnerabilities constantly outperform those depending on reactive strategies since they spend more on sustainable expansion and less on crisis recovery.
You might be interested in Security Compliance for Financial Institutions.
Why Choose Qualysec for Financial Vulnerability Assessment
For companies in the Philippines, Qualysec is a reliable cybersecurity partner providing sophisticated financial vulnerability assessment solutions.
Significant benefits of Qualysec are:
- Expert-led penetration testing and vulnerability analysis
- Methodologies for financial audit and compliance are consistent with industry
- Customized company risk assessment methods
- Dedicated financial vulnerability assessment solutions for SMEs
- Manageable insights for sustainable financial risk
Qualysec enables businesses to find and reduce financial risks before hackers take advantage of them. Partner with Qualysec to protect your financial services and secure your business today.
Conclusion
Financial vulnerability analysis is absolutely required in a fast-changing digital and legislative environment; it is not free. Organizations in the Philippines have to actively find faults in their financial systems, operations, and governance structures.
Business vulnerability assessment, financial stress testing, penetration testing, and Vulnerability Assessment integrated into a single plan will help companies to protect assets, ensure compliance, and create long-term resilience. Organizations can remain one step ahead of hackers and protect their financial future with Qualysec’s expert assistance.
Talk to our cybersecurity specialists to protect your financial data and digital transactions. Contact us Today!
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
FAQs
1. What is an example of a financial vulnerability?
An online banking system that permits unauthorized financial transfers is a typical instance of poor access control.
2. What is a financial vulnerability check?
It is a procedure that assesses financial systems, controls, and processes to find vulnerabilities that might cause losses or non-compliance.
3. What is an example of vulnerability assessment?
A standard example is doing a Vulnerabilities Assessment on a payment processing system to find exploitable vulnerabilities.
4. What are the five types of vulnerability assessment?
These include assessments based on networks, hosts, applications, wireless, and human factors.
5. What are the 4 types of vulnerability?
Four vulnerabilities exist:
Four main categories are Physical, cyber, operational, and financial vulnerabilities.
6. What are the 5 C’s in finance?
Used to assess financial risk and creditworthiness, the 5 C’s are Character, Capacity, Capital, Collateral, and Conditions.
See what our clients say about how our cybersecurity solutions helped secure their business.






















































































































































































































































































































































































































































































































































































































0 Comments