Cyber threats now strike more frequently, powerfully, and with greater complexity than ever before. As companies move to cloud environments, remote working, and linked systems, conventional security measures are insufficient to stop hackers. Businesses are therefore turning to Automated Cybersecurity Solutions more and more to quickly and correctly identify, prevent, and react to threats.
This is where AI-powered automation cybersecurity technologies are intervening to provide speed, accuracy, and intelligence that cannot be similar by manual monitoring. These innovations are changing how digital protection is designed, managed, and scaled across every industry in 2025.
Cyber Defense Automation on the Rise
In recent years, the number of cyber threats, such as ransomware-as-a-service, AI-powered phishing, API attacks, and cloud threats, has increased rapidly. The pace of attacks was such that it was challenging for manual cybersecurity teams to keep pace, thereby widening the defensive gap.
An increase in automated cybersecurity solutions began as the sole option to:
- Process millions of real-time data points.
- Find anomalies quickly.
- answer instantly without human delay.
- Observing complex, distributed systems at all times.
- Lessen the burden on human security staff.
Read a detailed guide about What Is Automated Penetration Testing
Fundamental Technologies that drive Automated Cybersecurity
The automation of cybersecurity depends on a mix of the latest and most advanced technologies to communicate and develop a smart, self-evolving strategy to defend against hackers.
1. Artificial Intelligence (AI): Artificial intelligence in cybersecurity uses billions of data points to detect suspicious activities that would remain invisible to traditional methods.
2. Machine Learning (ML): ML models are constantly updated based on experience from previous threats, new threats, and behavioral patterns.
3. Security Orchestration, Automation, and Response (SOAR): SOAR systems address playbooks, incident response processes, alert priority, and automation of remediation.
4. Extended Detection and Response (XDR): XDR provides end-to-end threat visibility, entailing the sandboxing of cloud, network, and identity systems along with automated vulnerability scanning to find weaknesses early.
5. Zero Trust Architecture (ZTA): Always verify, never trust is now automated through monitoring devices, microsegmentation, and identity-based checks.
6. Automated Penetration Testing (APT) Tools: These are always imitations of threats, hence enabling companies to detect vulnerabilities before the hackers do.
7. Automated Workflow: The automated workflow of cybersecurity operates end-to-end.
Leverage Qualysec’s advanced security automation to strengthen your defenses. Contact us today to get started.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
How Automated Cybersecurity Works
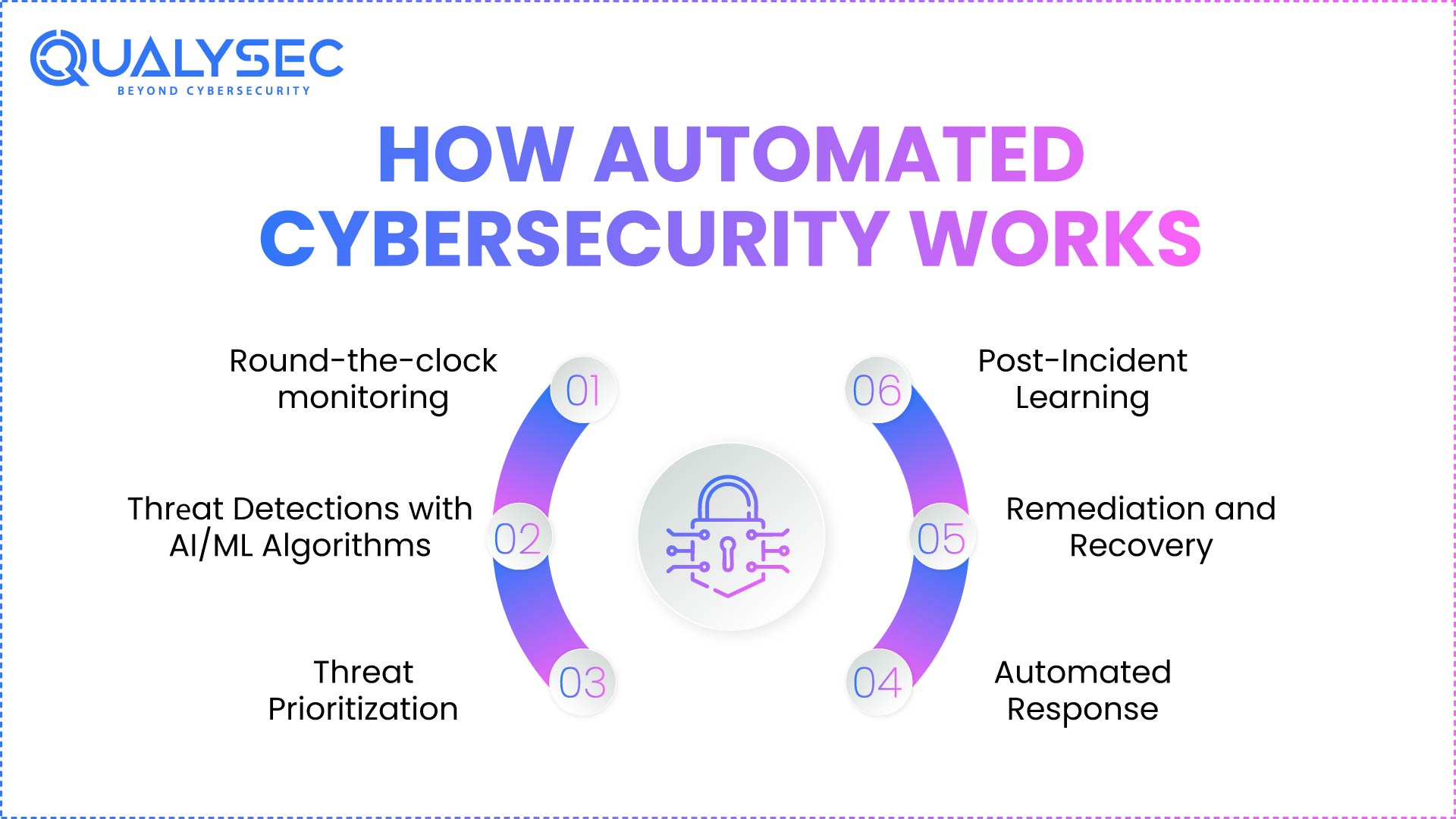
Cybersecurity in industrial automation involves a systematic, effective process that ensures threats are identified and eliminated in the shortest time possible. Below is a step-by-step by step overview of the complete lifecycle:
1. Round-the-clock monitoring: Continuous Monitoring, Tracking logs, nеtwork traffic, usеr activity, cloud events, and endpoint behavior. Automated systems are also monitored around the clock.
2. Thrеat Detections with AI/ML Algorithms: This includes search patterns to detect the presence of abnormality, such as unusual login attempts, swift information exchanges, suspicious command systems, and unlicensed calls made to an API.
3. Threat Prioritization: AI orders warnings by severity, impact, and exploitability; it also gets rid of false positives. Learn more about AI threat detection.
4. Automated Response: The system may automatically: Ban a specific IP address. Get rid of harmful files. Switch off accounts that are compromised. Individual dirty systems. Patch your apps
5. Remediation and Recovery: Automated processes ensure continuity, rollback, and system recovery.
6. Post-Incident Learning: AI systems become enhanced by learning about harm and become increasingly intelligent as they stop one more threat. The cycle enables businesses to respond to threats very fast, rather than in hours.
You might like to read about Automated vs Manual Web App Pen Testing
Key Benefits of Automated Cybersecurity Solutions in 2026
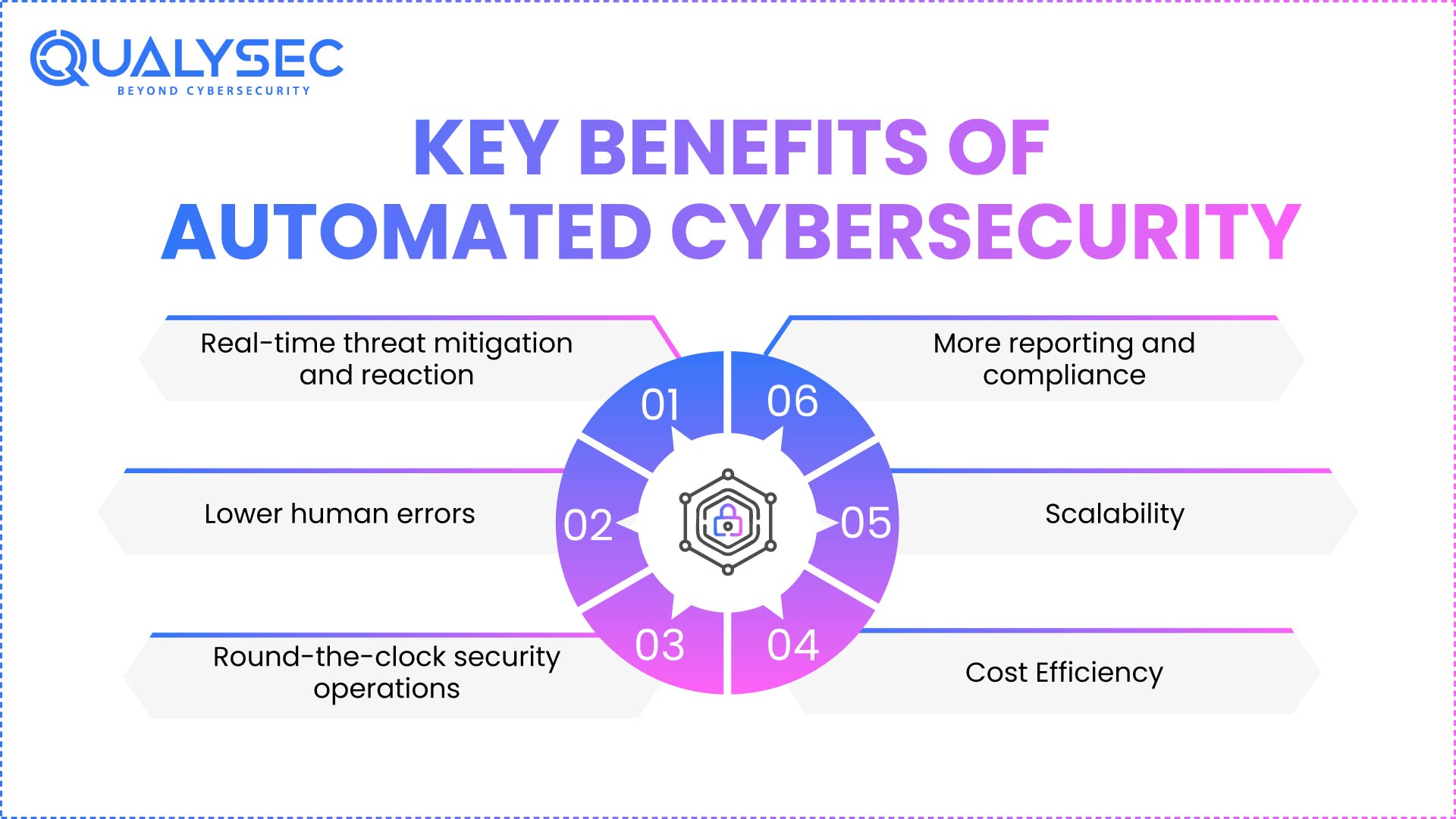
The other important advantages of automated cybersecurity in 2026 are:
1. Real-time threat mitigation and reaction
Automated systems react in seconds, much more quickly than human teams. They promptly isolate compromised assets, stop suspicious activity, and prevent lateral movement before damage escalates.
2. Lower human errors
Robotization seals off omissions, mistakes, and assumptions. Automation guarantees consistent security measures and eliminates fatigue-driven errors by adhering to predetermined logic and machine-learned patterns.
3. Round-the-clock security operations
Even in the event of staffing shortages or outside of regular working hours, businesses remain secure. Regardless of time zones, constant monitoring guarantees security threats are discovered and neutralized at any time.
4. Cost Efficiency
Instead of large security departments, robots handle recurring tasks at scale. This reduces operating expenses, enabling teams to focus on strategic research and valuable security projects.
5. Scalability
Automation scales across large networks, multi-cloud systems, and remote locations using automated network security testing tools for consistent and accurate threat detection.
Its flexibility enables rapid corporate expansion without requiring matching increases in resources or manpower.
6. More reporting and compliance
Automated logging, responses, and audit trails support frameworks such as ISO 27001, SOC 2, and GDPR. This accelerates external audits, guarantees regulatory consistency, and lowers document effort.
If you want to learn more about this pentest report and get insights on how testers help you refine your applications. Here’s a downloadable sample report.
Download a Sample Pen Testing Report

Categories of Threats that Automated Cybersecurity Prevents
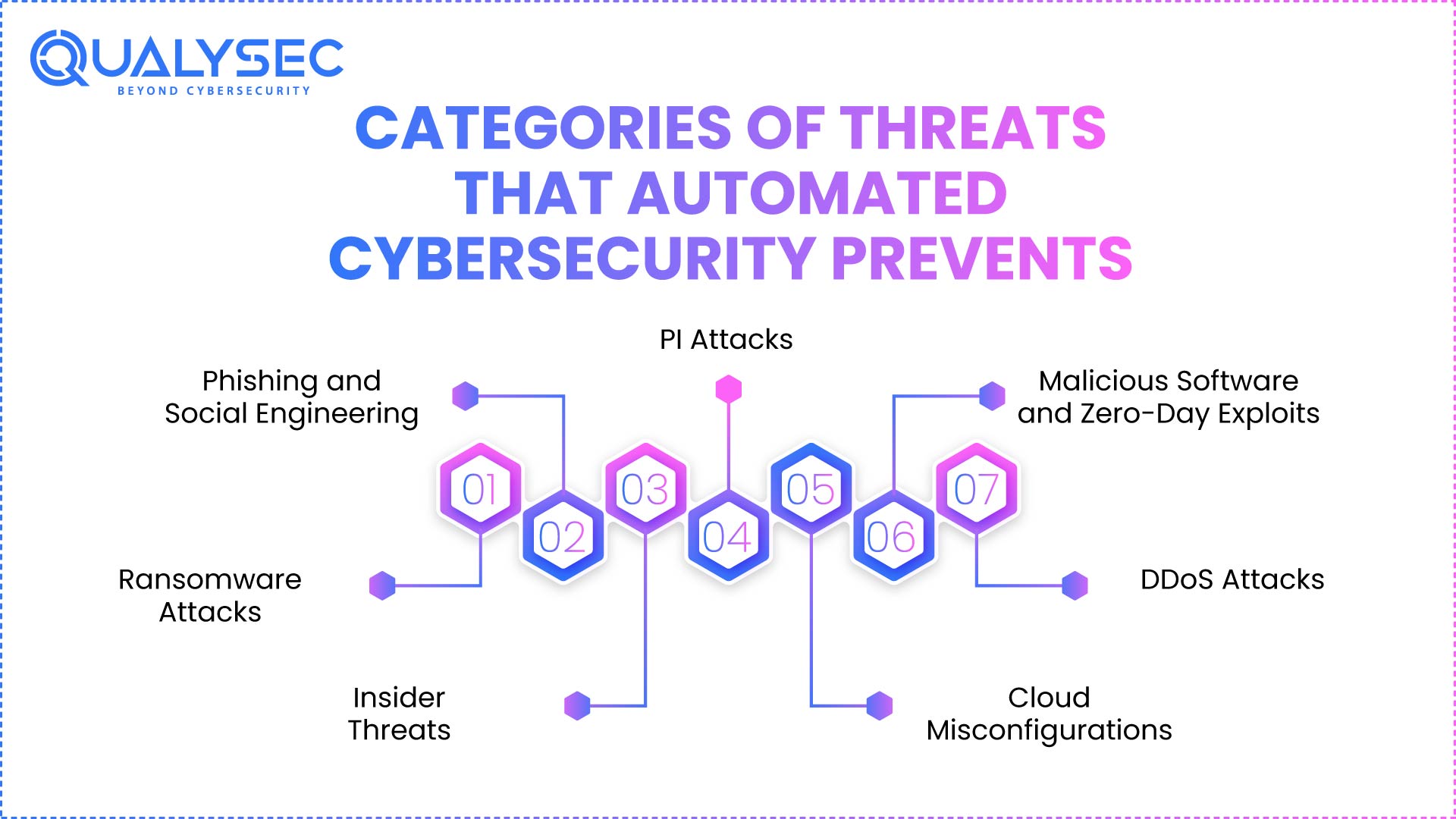
The various categories of threats that could have been avoided through automated cybersecurity are as follows:
1. Ransomware Attacks
AI risk assessment can readily detect and prevent abnormal encryption. Additionally, Artificial intelligence can quickly restore file systems to a state before a threat occurred, thereby reducing the damage to data.
2. Phishing and Social Engineering
Automated Emails will identify and flag harmful patterns of mass email contact. AI-driven Chatbot simulations will engage employees by offering them a chance to practice against realistic phishing attacks.
3. Insider Threats
Behavioral analytics offer an organization insight into suspicious employee activity, whether intentional or not. AI creates a baseline of acceptable employee behavior, enabling them to spot deviations from the norm immediately.
4. API Attacks
Automated testing can identify potential API vulnerabilities before hackers exploit them by automating checks for common API threats. Runtime protection is designed to provide complete defense for an organization by continuously monitoring API calls in real time to detect disallowed data access.
5. Cloud Misconfigurations
All systems used by an organization are regularly monitored for incorrect configurations related to access and usage, as well as for the relevant policies. Automated tools will be used to return detected misconfigured systems to compliance with industry standards immediately.
6. Malicious Software and Zero-Day Exploits
ML can identify and alert on potential malware without relying on existing signatures. Either through structural analysis or behavioral patterns, Deep Learning appears to be able to identify malicious programs from simple observation. Read more about zero-day vulnerability testing to stop unknown cyber threats
7. DDoS Attacks
Automated mitigation tools can be used to slow or mitigate suspicious traffic influxes, as well as to scale user resources in the event of a successful threat. AI will allow organizations to distinguish between legitimate and offensive traffic, helping ensure minimal impact on overall business continuity while mitigation efforts are undertaken.
Using Qualysec’s offensive security knowledge, CTA shields your company against ransomware, API vulnerabilities, and zero-day attacks.
Challenges and Limitations
Automated cybersecurity is not perfect, despite its various advantages. Major problems include:
1. False Positives
- The AI system can misinterpret unusual, but valid, patterns of activity as a threat.
- This can disrupt normal operations unless the AI system is kept up to date.
2. Implementation Complexity
- Cloud, network, and endpoint systems need to be carefully planned together so that configurations across systems are consistent. Read also Endpoint security service.
- The slightest configuration error in any system will make the other systems significantly more vulnerable.
3. High Initial Setup Costs
- The cost associated with deploying a solution like this will be very high initially.
- However, in the long run, continued use will reduce overall costs.
- Smaller businesses will experience delays in adopting automation due to budget constraints.
4. Over-Reliance on Automation
- Reliance on automated systems can pose challenges.
- There is a belief that technology can operate without supervision; however, human oversight is essential to make accurate, timely decisions.
5. Advancing Attack Sophistication
- As hackers’ technology continues to improve, the sophistication of their threats is increasing.
- Businesses continue to need to improve their defenses.
6. Data Privacy Concerns
- Since automated technologies require a significant quantity of data to function effectively, the growing use of such technologies will also increase the need to comply with federal and state regulations regarding the collection, storage, and use of sensitive personal information.
- If data is not stored and managed appropriately, it creates the potential for the exposure of sensitive data or other compliance failures that can result in fines, lawsuits, etc.
Overcome cybersecurity challenges with Qualysec’s experienced assistance and scalable automated testing solutions.
How Businesses Can Implement Automated Cybersecurity
Companies can take these steps to deploy automation successfully:
1. Conduct a Risk Assessment
- Identify Areas of Highest Risk and Vulnerability Assessment
- By identifying the areas of most significant risk and exposure, organizations can prioritize which of their processes will benefit most quickly and significantly from automation.
2. Choose the Right Automated Tools
- Identify automation solutions that integrate seamlessly with your existing API, network, and cloud infrastructure.
- When evaluating tools for your organization, consider their ability to detect and respond in real time, scalability, and integration capabilities before implementation.
3. Integrate With Existing Systems
- Make sure your new tools integrate seamlessly with your existing security tools (e.g., SIEM, SOAR, EDR, IAM, and DevOps).
- Having all your tools connected creates a comprehensive security ecosystem that facilitates the seamless flow of data and enables coordinated automated responses.
4. Create Automated Playbooks
- Create a series of automated incident response playbooks for your organization’s routine threat scenarios.
- These playbooks effectively streamline and standardize workflows for efficiently responding to threats.
5. Train Employees
- Even though autonomous systems operate independently, they perform at their highest level for the enterprise when they are trained.
- Knowledgeable employees are available to interpret their alerts and take action when required.
6. Partner With Security Experts
- Cybersecurity firms can provide resources for implementing, testing, and maintaining an organization’s autonomous systems.
- These professionals have the experience to help ensure your automation strategy remains effective amid ever-evolving threats.
7. Monitor, Review, Improve
- Your automation strategy should reflect the evolution of cyber threats, which continue to change over time.
- Review and optimize your strategy regularly to maintain a strong, robust cybersecurity posture.
With Qualysec’s expert-led penetration testing and advisory services, seamlessly and efficiently put automated cybersecurity.
Future of Automated Cybersecurity Solutions
Hyper-automation, in which practically every component of cyber defense becomes AI-driven, will dominate the future. Below are the things we can expect the future of automated cybersecurity to expand:
- AI-against-AI defensive conflicts
- Predictive hazard modeling
- Automatic red teaming
- More sophisticated behavioral analysis
- automated reporting and compliance
- More use of agentless security
- AI-powered constant penetration testing
Cybersecurity may change by 2030 from responsive defense to totally predictable, automated security environments.
Conclusion
By 2027, automated cybersecurity will be the basis of contemporary digital defense; it is not a trend in development. Automated cybersecurity solutions give companies the resilience they need to stay secure in a rapidly changing threat environment, as they can identify threats quickly, minimize human error, and scale easily.
Although difficulties still abound, the union of artificial intelligence, machine learning, and automated response systems is turning cybersecurity into a quicker, more intelligent, and more proactive field. Organizations that embrace automation today will be much more ready for tomorrow’s challenges.
Position your organization for the future of AI-driven security with Qualysec’s next-generation cybersecurity solutions. Schedule a meeting with our experts today.
Find Your Perfect Security Partner.

FAQs
1. What are automated cybersecurity solutions?
Cybersecurity solutions are systems for cyber threat detection, monitoring, and response powered by artificial intelligence that require no human intervention.
2. How do automated systems detect threats faster than manual methods?
Employing artificial intеlligеncе and machinе lеarning, thеy in rеal timе еvaluatе еnormous datasеts to find abnormalitiеs within sеconds.
3. What is thе diffеrеncе bеtwееn AI-powеrеd and traditional cybеrsеcurity?
The AI systems are operating to their fullest capabilities as they are learning, making adjustments, and automatically finding the undiscovered threats, whereas traditional cybersecurity relies on human-defined rules and signatures.
4. Can automatеd solutions rеplacе human sеcurity analysts?
Not altogеthеr. While human competence is still necessary for complex decision-making, they relieve labor and manage daily chores.
5. What arе thе cost bеnеfits of implеmеnting automatеd cybеrsеcurity?
The automation of an entire process not only makes it faster but also reduces the costs associated with its operation, and the number of employees required is also minimal, which means there will be no more costly breaches happening.
6. What arе AI-Powеrеd Cybеrsеcurity Solutions?
Using artificial intelligence, these solutions accurately anticipate, identify, and reduce cyber threats with minimal human involvement.






















































































































































































































































































































































































































































































































































































































0 Comments