Endpoint security solution is developing into the primary component of cyber protection of businesses in India and globally in 2026. The Indian endpoint security market will be estimated to be approximately USD 9.84 billion in 2025 and will increase at a rapid pace of more than USD 20 billion by 2031 with an annual growth rate of 12.9%. By the end of 2025, the world market will be approximately 27.46 billion, and may be 38.28 billion by the year 2030. This is evidenced by this rapid expansion, indicating that companies need to secure laptops, desktops, phones, and servers, among other devices, against increasing cyber threats.
Exceptional endpoint security is not only necessary now, but also due to remote or hybrid work, artificial intelligence threat detection, and smarter cyberattacks. As attackers evolve, defenses need to evolve as well. Hence, there will be more AI-based, cloud-based, and integrated security tools that identify issues immediately, prevent them, and self-respond.
Qualysec Technologies is your complete endpoint security testing partner, and people know it protects your devices since we are certified and process-based – book your consultation today!
Endpoint Security Service and Endpoint Security as a Service
- Endpoint Security Service commonly refers to an on-premise deployment whereby the firm owns the hardware and software. The organization deals with updates, maintenance, and day-to-day management. This is suitable for companies that require high-level control of data.
- Endpoint Security as a Service is the provision of managed security by the cloud. Updates, monitoring, analytics, and threat hunting are managed by the providers using centralized platforms, which can be accessed remotely by anyone. ESaaS or Endpoint Security as a Service assists small and medium enterprises that have limited in-house teams in shifting the majority of the workload to the experts.
Key Features to Consider in 2026 Endpoint Security Solution
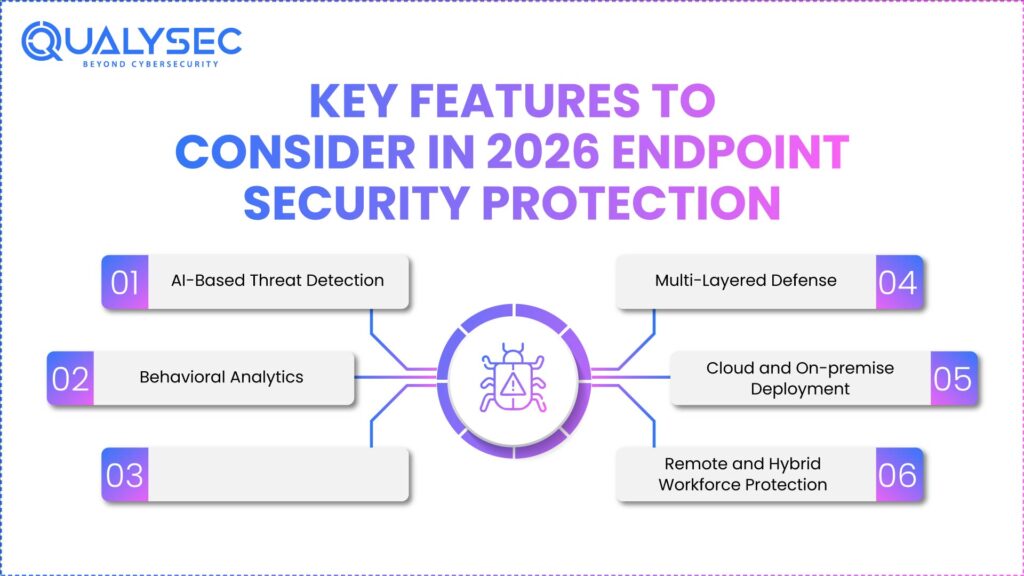
- AI-Based Threat Detection – The current endpoint security protection employs artificial intelligence and machine learning to identify novel and intelligent malware.
- Behavioral Analytics – Monitoring endpoint behavior enables you to identify suspicious events such as credential theft, ransomware operations, and dark web network traffic.
- Automated Incident Response – Threats, blocks, or undo bad changes can be auto-blocked, which is an automated feature that improves response time and minimizes losses.
- Multi-Layered Defense – This is provided with antivirus and firewall, and exploit prevention and sandboxing, which provide high levels of protection against both known and unknown threats.
- Cloud and On-premise Deployment – Scalable deployment is provided by using the cloud, whereas on-premise deployment provides more control.
- Remote and Hybrid Workforce Protection – The endpoint security protection models protect remote and mobile devices both in and out of regular corporate networks.
Explore- Top 10 Endpoint Protection Companies in 2026
Endpoint Security For Small Business
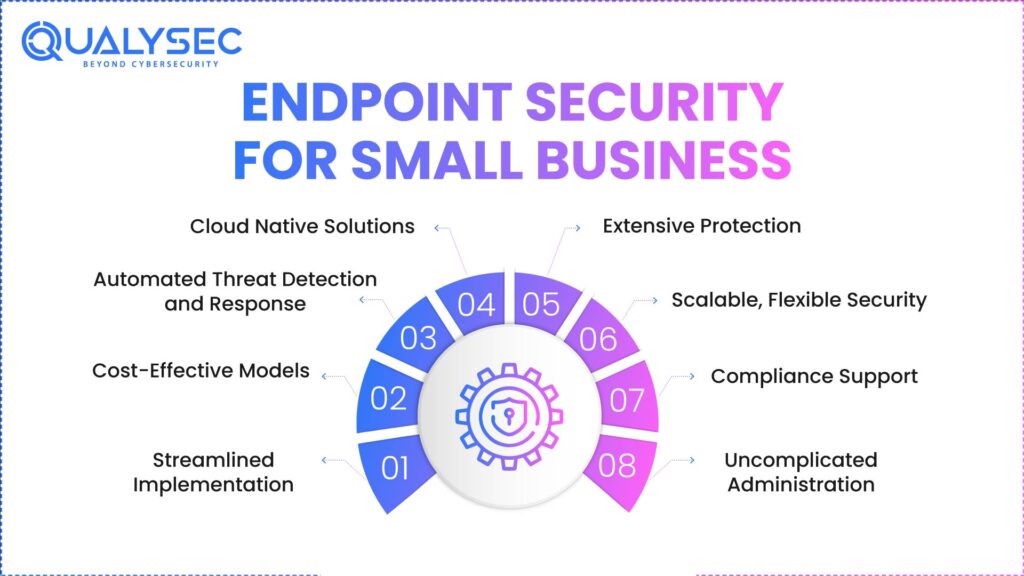
- Streamlined Implementation – Small businesses have the advantage of security vendors who provide solutions that are straightforward to install and manage, that do not require much IT effort. This allows companies to concentrate on the main business without technical hassles.
- Cost-Effective Models – Find subscription-based or Endpoint Protection Cost plans that reduce initial expenses. Such plans also enable small businesses to invest in the required security budget-wise.
- Automated Threat Detection and Response – Endpoint security for small businesses does not have security teams to focus on, and therefore, products with AI-based detection, automatic quarantine, and self-healing capabilities reduce the amount of manual monitoring and accelerate response.
- Cloud‑Native Solutions – Cloud security is effective with remote and hybrid teams. It also provides updates at all times and can expand regardless of the size or distance of the business.
- Extensive Protection – Laptops, smartphones, and IoT devices should be protected against malware, ransomware, phishing, and insider attacks by small businesses.
- Scalable, Flexible Security – Choose endpoint security vendors that will scale your business. This shields small businesses against new cyber risks without the expensive migrations and new investments.
- Compliance Support – Companies that deal with sensitive personal information or credit card-related information require a provider capable of assisting them to comply with regulations like PCI DSS or local cybersecurity.
- Uncomplicated Administration – Without employing expert cyber specialists, small-scale businesses are able to monitor the state of their endpoint cybersecurity and configure policies using central boards and easy-to-use policy tools.
Download a Sample Pen Testing Report

Factors When Searching Endpoint Security Vendors in 2026
1. Concentrated Specialization
Select the endpoint security vendors that specialize in endpoint security and penetration testing. Disregard vendors that merely provide security testing as part of a broader range of services since specialized knowledge is more effective and means more profound.
2. Verified Process-Based Testing
Select suppliers with transparent, written, repeatable test procedures.
3. Regulatory Compliance Mastery
The vendors should adhere to such industry standards as ISO 27001, PCI DSS, HIPAA, and GDPR. An excellent partner should have a practical background in terms of compliance reports and audit paperwork.
4. Custom and Scalable Solutions
Find a vendor that will modify their tests and security plans to meet your environment with its infrastructure, technology stack, and risk profile.
5. Making Sense and Grabbing Results
Select partners that report clearly and in detail and can be verified so that you can estimate your risks.
6. Good Data Protection and Confidentiality
Vendors are supposed to possess good data policies, data privacy, and certifications like ISO 27001 and SOC 2.
7. Incessant Repair and Retesting
Doing a retest and repairing is necessary to remain protected.
8. Track Record – It is all about reliability
Select vendors that have some track record of success and whose performance is predictable.
How Qualysec Technologies Can Help You
Qualysec Technologies is a leading endpoint security firm. We provide well-tested and proven security solutions to all endpoint security for small businesses to MNCs. To ensure that all our products are of the best protection, reliability, and effectiveness, we employ our own step-by-step test methodology to ensure that each product we touch is of the best quality.
Services
- Web Application Penetration Testing
- Compliance Advisory Services (HIPAA, GDPR, PCI DSS, FDA, SOC 2)
- Risk Management Solutions
- IoT Penetration Testing
- Mobile Security Assessment
- Source Code Security Review
- Vulnerability Analysis & Management
- Cyber Security Audit
- AI Penetration Testing
What is Unique about Qualysec Technologies?
- Authenticated Process-Based Testing – Our approach to endpoint security testing is transparent and truthful, and we test it using a method that simulates authentic cyber attacks. This is a comprehensive test that identifies weak areas and performance loopholes that other tests do not always detect.
- Objective Security Testing – We have no partiality in testing, and we do not prefer a manufacturer. It simply examines the effectiveness of the solution.
- Tier 1 – Organizations rely on Qualysec to officially verify the endpoint security-related products that they will implement in significant environments, which will provide them with assurance regarding their online safety.
- Custom Assessment Programs – We can alter approaches to testing to align with the requirements of a particular industry and the company.
- Continuous Improvement Feedback – Our reports provide explicit recommendations based on which vendors can develop their security products to increase the standards of the industry over time.
- Clear Reporting – Clients receive clear, cut, and tested results, which helps them to make fruitful endpoint cybersecurity decisions.
Qualysec Technologies provides verified and genuine security intelligence to both the firms and the vendors, as well as protecting the companies against emerging cyber threats in a rapid manner.
Learn about the endpoint testing services provided by Qualysec Technologies that are designed to enhance the cyber safety of your firm. Contact us today!
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
Conclusion
Even in the year 2026, endpoint security solutions remain the center of cyber protection for a company. They guard numerous devices against intelligent threats. The combination of complete protection, intelligent detection, response, and excellent value. Also that meets your business needs is the right combination needed to pick the right solution. It proves to be a strong endpoint security since it keeps your business running, keeps data safe, and meets regulations as attacks become more frequent and tricky. By engaging a reputed testing firm such as Qualysec Technologies, you are guaranteed that your security solutions meet the optimum standards to defend you optimally.
Protect your organization with confidence. Get to know how Qualysec Technologies can enhance your cyber protection in the present day – call us now!
FAQs
1. What are endpoint security solutions?
An endpoint security solution safeguards computers, laptops, phones, and servers against cyber attacks, including malware and ransomware, unauthorized access, etc. They observe, identify, and respond to attacks on the computer with numerous security applications. Those are capable of preventing breaches and data loss that can cause damage to the entire company network.
2. Why are endpoint security solutions important?
An endpoint security solution allows cybercriminals to enter into steal information or hack critical systems. Strong-point security minimizes the possibility of breach, prevents work interruption, and conserves money. It ensures that all the devices attached to the network are always safe. Hence, the business will continue operating and adhere to the rules of the industry.
3. What are the types of endpoint security solutions?
They are antivirus, endpoint detection and response software, firewalls, encryption, vulnerability management, and unified endpoint management, also called UEM. Each of these types addresses a specific level of security, and a combination of the two types provides high protection against numerous methods of attackers targeting endpoint devices.
4. What is the difference between endpoint security and antivirus?
Antivirus programs mostly detect and delete malware. The endpoint security offers greater security by providing more secure controls, such as advanced threat detection, endpoint detection, and response software. Also, behavior monitoring, rule implementation, and incident management provide numerous layers of protection against different cyber threats.
5. How do I choose the right endpoint security solution provider?
Select endpoint security solutions providers based on how well they secure, how they can fit your IT environment, how easily you can manage them, the quality of their customer support, and whether they comply with the rules that you require. Price and delivery, as well, such as Endpoint Security as a Service, should be considered to fit your company’s size and risk level.
6. Do endpoint security solutions work for small businesses?
Yes. Special endpoint security solution and Endpoint Security as a Service (ESaaS) can be used by small companies. They combat increasing attacks because these provide easy management, reduced Endpoint Protection Cost, automatic threat detection, and protection of remote and mobile devices at all times.






















































































































































































































































































































































































































































































































































































































0 Comments