The Indian digital payments ecosystem is expanding at a rapid pace – it is projected that by 2026, the amount of digital transactions in India can reach over 106+ billion annually. According to studies, card-related cyber fraud has increased by 28 percent annually. According to industry reports, over 75 percent of Indian merchants surveyed find it hard to comply with the PCI-DSS Compliance Requirements. So, robust testing of the PCI-DSS is highly significant. All these facts precondition that PCI-DSS compliance testing is not only necessary but also obligatory for all companies working with payment card data.
Protect your merchant business – begin your testing of PCI-DSS compliance. Call Qualysec to reserve a free consultation!
PCI-DSS Compliance Testing – What Is It?
PCI-DSS compliance testing is an unambiguous, data-based security test that finds out whether organisations receiving and sending payment card information adhere to the Payment Card Industry Data Security Standards (PCI DSS). The aim is to prevent cardholder information breaches by ensuring that all the necessary controls, encryption policies, and process checkpoints exist and that someone tests and validates them.
Technical and administrative tests, including but not limited to vulnerability scans, PCI DSS Penetration Testing Vendor tests, segmentation tests, and risk tests, are done by auditors to address all PCI DSS Compliance Requirements.
Steps in the PCI-DSS Compliance Testing Process
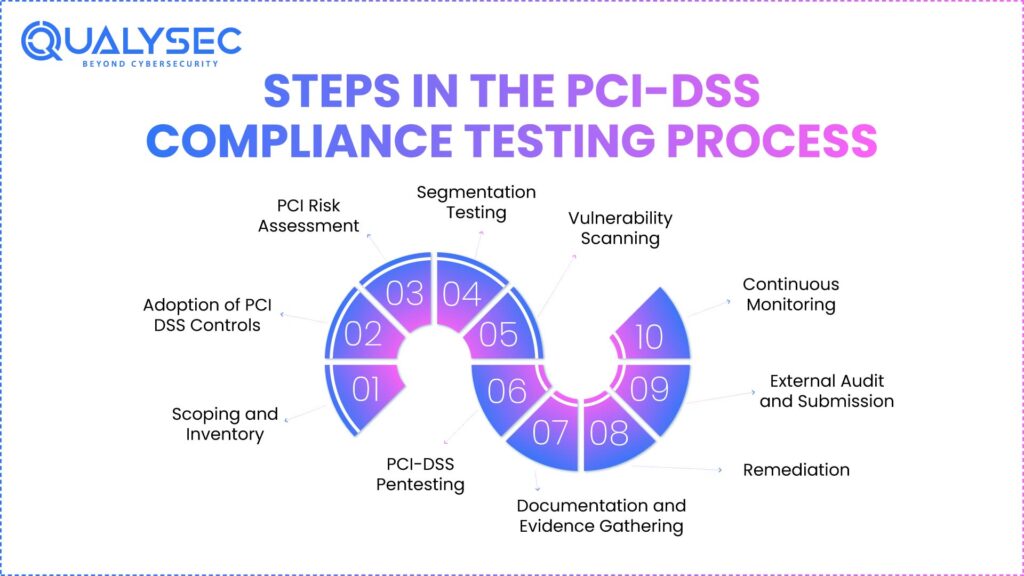
1. Scoping and Inventory
- Begin by charting all assets, systems, processes, and vendors dealing with cardholder data.
- Over 87 percent of data breaches occur due to the fact that companies disregard unmonitored and untracked devices and applications.
2. Adoption of PCI DSS Controls
Bring PCI regulations into real life. These systems should have encryption, multiple methods of verifying identity, and maintain good logs.
3. PCI Risk Assessment
PCI Risk Assessment uses technical and administrative inspections to identify security loopholes.
4. Segmentation Testing
Conduct PCI segmentation tests to ensure that network boundaries are right and prevent unauthorized movement between systems.
5. Vulnerability Scanning
Automated scanning of each month. Check assets, which are highly risky, in the reserve manuals.
6. PCI-DSS Pentesting
PCI-DSS Pentesting is a simulation of attacks in the real world that a PCI tester conducts. Ensure that you do the tests on websites, APIs, servers, and all endpoints.
7. Documentation and Evidence Gathering
- Note down records and traces of every compliance.
- QA logs are the most demanded ones in reviews conducted by a Qualified Security Assessor (QSA).
8. Remediation
Close the holes, tighten the screws, and repeat.
9. External Audit and Submission
- Submit findings to a PCI DSS Penetration Testing Vendor
- Two or more rounds of audit only make merchants compliant.
10. Continuous Monitoring
The plan should be to scan quarterly and penetration test annually.
Tools Used in PCI-DSS Compliance Testing
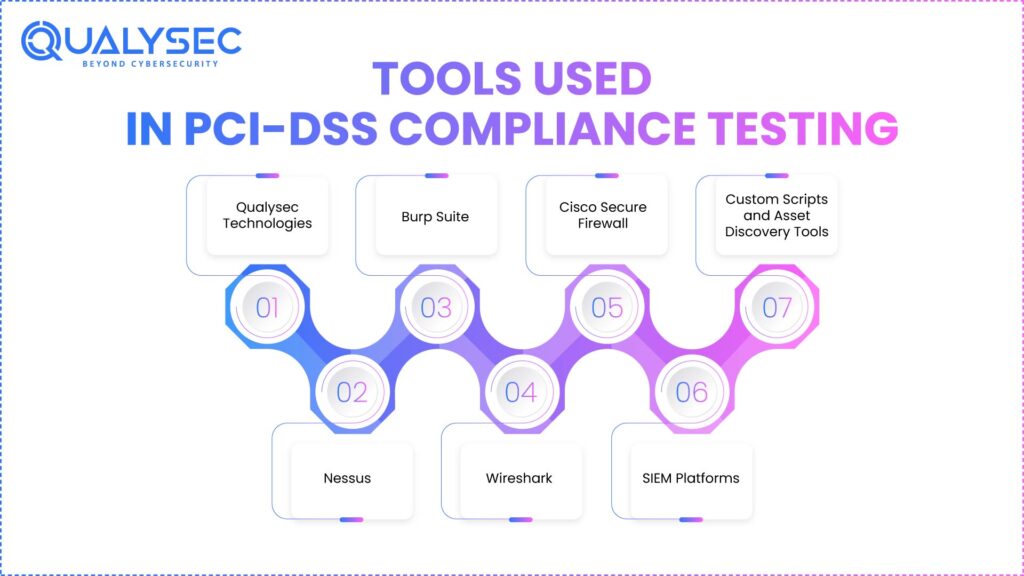
By 2026, both free and paid versions of tools to help with PCI Compliance Test will be available from vendors –
- Qualysec Technologies PCI-DSS Automation Tools – Provide automated audit workflows, reporting, and continuous compliance tracking for PCI DSS Compliance.
- Nessus / QualysGuard – Automatic scanners used in normal vulnerability detection.
- Burp Suite – Commonly used for penetration testing related to vendors, particularly web applications.
- Wireshark – Verifies encrypted data transmissions according to the PCI requirements.
- Cisco Secure Firewall – Checks segmentation controls.
- SIEM Platforms (Splunk, IBM QRadar) – Log analysis and collection of evidence.
- Custom Scripts and Asset Discovery Tools – Automate the risk assessment and discover the unknown assets.
PCI-DSS Compliance Testing Best Practices
1. Periodic and Monthly Examination
Carry out vulnerability scans at least once every 3 months and each time of a significant change in the network. Carry out run penetration tests once a year, or more frequently in case of app or infrastructure changes. Use popular techniques such as NIST SP 800-115 or PTES to identify all the weaknesses that can be exploited.
2. Careful Asset Mapping and Scoping
Maintain a list of all hardware, software, and network resources that store, process, or transmit cardholder information that is up to date. It is good scoping that indicates which sections fall within the Cardholder Data Environment (CDE) and minimizes the potential risks that go unnoticed, like hidden devices.
3. Good Segmentation and Segmentation Testing
Present PCI segmentation tests in a rigorous manner to demonstrate that the CDE is independent of other systems. Effective segmentation reduces the area and procurement of compliance and restricts the attack surface.
4. Comprehensive Documentation
Maintain precise, good records of all controls, processes, and network maps as well as data flows. Well-documented audits are less complicated and demonstrate actual compliance.
5. Automated Security and Compliance Processes
Automate inventory, detecting changes, access control, collecting logs, and generating reports. Automation eliminates human errors, accelerates audits, and can help you keep track of threats in real time.
6. Partner Managerial Cooperation
Cooperate with technology and service suppliers to implement PCI controls. Assign security responsibilities, Service Level Agreement, and frequent communication in such a manner that the partners remain in compliance and assist you promptly during a damaging incident.
7. Training and Awareness of the Employees
Educate all the employees concerning the PCI regulations, social engineering risks, and incident-related responses. The human factor is a significant source of attack, and training reduces the chances of phishing and stolen credentials.
8. Retesting and Remediation
Address weaknesses fast, depending on the riskiness of these weaknesses. Fixes to retest systems before audit submission to ensure that there are no known issues that are left, as per the PCI DSS certification cost.
9. Recurrent Observations and Incident Response Planning
Monitor log watching on an ongoing basis using real-time alerts and SIEM. Conduct routine incident drills to demonstrate that the organization can react to breaches or compliance failures.
How Qualysec Technologies Can Help You
Qualysec Technologies is an organization that provides consultancy services in the field of data networking and security solutions. Our procedural methodology ensures that all its controls and requirements are proactively verified – we never leave them to chance, and this guarantees outcomes in the course of audits.
Services
- Web Application Penetration Testing
- Mobile Security Assessment
- Cloud Security Audits
- IoT Penetration Testing
- Source Code Security Review
- Vulnerability Analysis & Management
- Compliance Advisory Services (HIPAA, GDPR, PCI DSS, FDA, SOC 2)
- Risk Management Solutions
- Cyber Security Audit
- AI Penetration Testing
What Makes Qualysec Unique
- Proven Testing Methods – Qualysec is unique as it does not rely on generic checklists or easy-to-do automation in PCI Compliance Test, but rather on a process-based and proven method. It begins by doing a deep scoping, asset mapping, and risk assessment with proprietary tools that are designed to be trained on the current Payment Card Industry Data Security Standards.
- Compliance Friendly – Qualysec is a team that implements real-time dashboards, SIEM integrations, and versatile scripts to fit Indian payment settings and ensure all PCI DSS Compliance Requirements are fulfilled and supported by log evidence. All the tests of segmentation are reusable and prepared to be investigator-friendly. RBI audits are painless.
- Human + AI way – Its PCI DSS Segmentation Testing of QA is a test of both digital and human controls. Nothing is skipped, and there are clear points of remediation in every test. In comparison with other consultancies, the automated vulnerability scans are always combined with manual review to ensure that no gap has been overlooked.
- Custom Plans – The custom PCI Risk Assessment map identifies the unique Indian fintech stack, shadow assets, and avoids missed critical vulnerabilities. We will give every client a compliance playbook, dashboard access, and periodic re-audit at a clear and transparent PCI DSS certification cost structure that fits Indian businesses.
Select verified, repeatable, and process-based PCI-DSS compliance testing – select Qualysec Technologies.
Are you ready to protect your cardholder data? Schedule your PCI-DSS compliance testing with Qualysec Technologies – the initial move towards actual PCI-DSS Compliance!
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Conclusion
The compliance testing of PCI-DSS is not a single agenda but a continuous process, which saves your business reputation, revenue, and customer confidence. With the increasing payment environment in India, the threat surface increases. PCI DSS Segmentation Testing, risk analysis, and verified evidence can provide you with a clear security advantage, not to mention that regular PCI DSS Compliance testing is the way to go. Qualysec Technologies is the future of compliance – process-oriented, optimized for Indian businesses, with clear prices and an in-house knowledge base.
Download a Sample Pen Testing Report

FAQs
1. What is PCI-DSS compliance testing?
The PCI-DSS compliance testing is a very rigid exercise that verifies whether organisations that deal with payment card information abide by the Payment Card Industry Data Security Standards. It is the technical reviews, vulnerability scans, penetration testing, and evidence gathering to ensure that networks, systems, and business practices guard cardholder information against unauthorized access or breaches.
2. Why is PCI-DSS compliance testing required?
Organizations need the testing of the PCI-DSS compliance to prevent breaches of data, fraud, and fines. The regulators, such as the RBI in India, are supposed to test all businesses that handle card payments regularly. Strong testing helps to demonstrate vulnerabilities, confirm the presence of controls, and demonstrate to the customers that the organisation adheres to the world-recognised PCI Security Standards established by the PCI Security Standards Council.
3. What does PCI-DSS compliance testing include?
Compliance testing at the PCI-DSS level involves routine vulnerability scans, manual and automated penetration tests, segmentation testing, access control review, and log monitoring. All 12 core PCI DSS requirements are established by these steps, which cover the encryption of cardholder data, the security of systems, and their use by authorised personnel only.
4. Who needs PCI-DSS compliance testing?
PCI-DSS compliance testing is required in any organisation in India that has stored, processed, or passed payment card data, including banks, e-commerce businesses, fintech companies, and merchants. It is compulsory irrespective of the size of the business or volume of transactions undertaken, and the manner of handling payments and risk profiles determines the frequency of the testing.
5. How often should you perform PCI-DSS compliance testing?
Organizations need to do quarterly PCI-DSS vulnerability scanning and annual full penetration testing. The latest version of PCI 4.0 and the regulatory framework recommend having more frequent checks in high-risk settings and high-volume merchants. Periodical testing is essential to continuous compliance and defense against changing threats to payment systems.






















































































































































































































































































































































































































































































































































































































0 Comments