In the modern online business world, customer or organizational data is the most essential asset for any venture. Some experts and market leaders even claim it to be a new currency. With so many valuable assets for any company, even hackers and exploiters are trying their best to steal them for ransom, exploitation, blackmail, and other malicious activities. That’s why cybersecurity implementation is much more than just a nice-to-have feature, but a necessity for your business survival in 2026. A cybersecurity audit checklist is one great way to find out such vulnerabilities that can lead to data breaches, AI-powered phishing, and ransomware.
As per a report from Demandsage, till now in 2026, around 12,000 confirmed data breaches were recorded on a global scale. This number is the highest till now, exposing critical business and user information.
With huge Artificial intelligence adoption and interconnected cloud systems, the attackers now have multiple entry points to steal critical business or customer information. However, a cybersecurity audit by professional cybersecurity experts is a great tool to fight back against these exploiters. In simple words, this checklist is all about a proactive health check to identify potential vulnerabilities in your code or platforms, leading to data leaks.
In this in-depth guide, we will try to understand more about Cybersecurity Risk Assessment in 2026, and its role in making your business stand up against cyber threats and attacks.
Introduction to Modern Cybersecurity Auditing
In 2026, your approach to merely adding cybersecurity compliance and security measures later will be gone. The yearly checkup schedules are changed to new verification frameworks continuously. With the rise of remote work culture and decentralized teams working for your organization, the possibilities of cyber attacks can occur from anywhere.
If we look into these issues, the danger for the organization is huge. As per the research reports, the global cost of cybercrime is going to cross $12 trillion annually by 2026. Rather than considering this massive problem for technology companies, we are witnessing cases in many small to medium enterprises.
A Cybersecurity audit checklist keeps your organization ready to identify any such vulnerable cases and put up a battle for the hackers. It will provide you with more understanding of your current standing, scenarios, and weak areas. In 2026, this clarity matters a lot if you’re really looking forward to saving your business from massive losses.
Why Your Business Needs an Audit Checklist in 2026
With the modern Information Technology system becoming increasingly complex with each passing day, organizations can’t rely on human memory. Such companies with internet usage require a reliable cybersecurity assessment checklist and a reliable tool. A cybersecurity checklist works great to check a company’s data, user information, servers, accounts, and more against hacking attempts.
In 2026, the majority of cyber threats and attacks from hackers will happen because companies have hidden backdoors. In some cases, there can be old projects with old backdoors that hackers can easily access to steal the sensitive data and information. Along with the customer data, the financial and payment stakes are getting at greater risk now. As per the recent data, the average cost of data breaches or leaks reached a high figure of $4.88 million in 2024, and has been rising since then.
Apart from the financial stakes, cyber risks also damage your organization’s reputation. The modern customers also prefer organizations that are more active towards privacy and payment concerns. They also need to be sure that the company they’re associating with is also concerned about their data safety.
A reliable and successful Cybersecurity Audit Checklist will be like a badge of security experts that you can proudly show to customers, partners, investors, and everyone.
Step-by-step Cybersecurity Audit Checklist
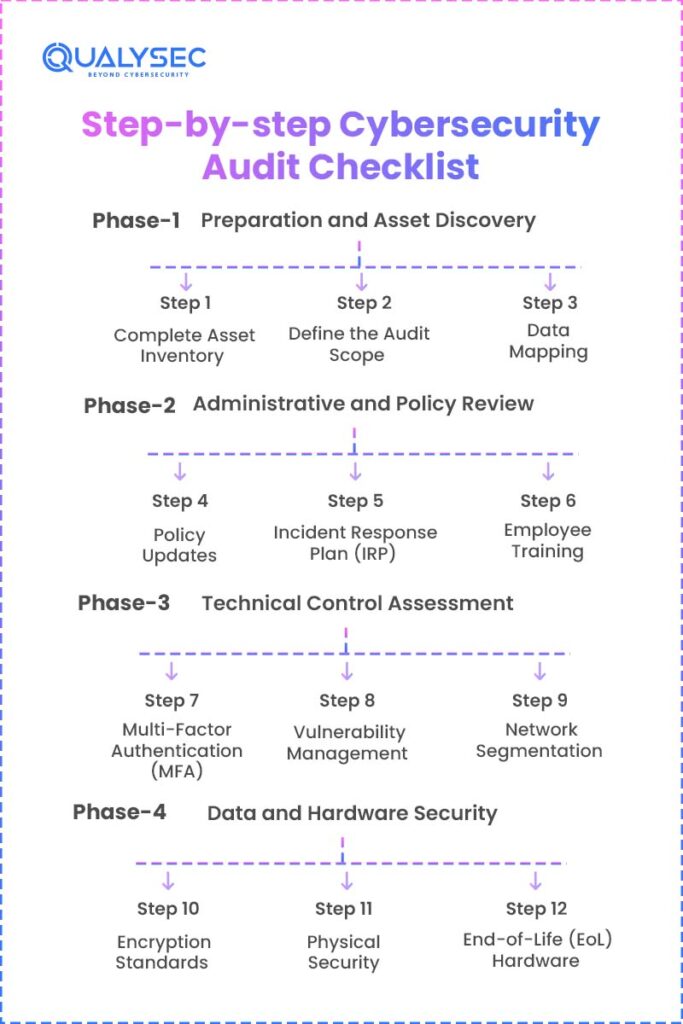
Phase 1: Preparation and Asset Discovery
It’s really challenging to protect your organization from cyber threats and risks until you know them completely. The first phase covers the steps necessary to create a map of the digital world.
Step 1: Complete Asset Inventory
Every device used by your organization must be listed in the Cybersecurity Audit Checklist report. In 2026, shadow IT is coming as a major risk for companies, which happens when employees use apps or devices to access sensitive data without notifying the organization.
Step 2: Define the Audit Scope
Your Cybersecurity Risk Assessment report should be about the whole process system, processes, apps, platforms, etc. The audit scope can also be limited to a specific department, like payment processing, as per the need.
Step 3: Data Mapping
A good report needs to point out exactly what’s at risk, like your bank details or company secrets. It basically shows you what hackers are likely to go after first.
Phase 2: Administrative and Policy Review
Technology assessment is one crucial part of the cybersecurity compliance Audit, with another being the employees, people, or resources.
Step 4: Policy Updates
The cybersecurity experts check if the company policies are from old years. Your current organization policies need to be updated for 2026, like remote work security, and the use of Artificial Intelligence.
Step 5: Incident Response Plan (IRP)
A cybersecurity risk assessment analyzes whether your IRP has the complete roadmap or just plain documentation. In this, the cybersecurity team can also simulate a hacking attempt to understand the employees’ reaction to it.
Step 6: Employee Training
As per this report, around 82% of the data breach cases happen because of human or people’s mistakes. It makes the resource training for the cybersecurity practices a mandatory thing.
Phase 3: Technical Control Assessment
In this phase of the Cybersecurity audit checklist, we need to check the software or network settings on various parameters.
Step 7: Multi-Factor Authentication (MFA)
Gone are the days when simple and common passwords were fine in any organization. Nowadays, in 2026, your organization needs to use MFA (Multi Factor Authentication) for all accounts. In this step, the cybersecurity experts check the MFA implementation across the whole organization with remote access.
Step 8: Vulnerability Management
This step of the security audit in cybersecurity involves checking all system strengths against potential exploitation attempts. According to the Cybersecurity & Infrastructure Security Agency, the majority of the exploiters found loopholes through “known” vulnerabilities that were simply ignored.
Step 9: Network Segmentation
Your servers and systems that have critical data should not be accessible to the public or guest WiFi networks. An audit for network segmentation ensures the security is as strong as it should be.
Phase 4: Data and Hardware Security
In this phase of cybersecurity audit requirements, the experts need to prioritize the digital safety of information.
Step 10: Encryption Standards
This step involves the security audit for all the data stored on disks and moving across the internet. In case no encryption is in place, it needs to be implemented.
Step 11: Physical Security
The cybersecurity experts also evaluate whether physical locks, cameras, equipment, and badges are included in the audit reports.
Step 12: End-of-Life (EoL) Hardware
One of the major risks with the old company devices is their inability to comply with the recent updates. Hence, the cybersecurity reports should report such hardware and recommend its replacement.
| Audit Phase | Focus Area | Key Metric for 2026 |
| Phase 1 | Asset Inventory | % of “Shadow IT” discovered |
| Phase 2 | Human Risk | Phishing simulation click rate |
| Phase 3 | Network Safety | Time to patch critical bugs |
| Phase 4 | Data Privacy | % of sensitive data encrypted |
Common Mistakes to Avoid During Your Audit
The impact of cyberattacks is often anticipated for organizations. Even with a network security audit checklist, there can be certain mistakes, leaving loopholes for exploiters. Some of the crucial and common mistakes to keep a check on are mentioned below.
a) Checking the Box & Not the Risk
Rather than performing a cybersecurity audit checklist to please a lawyer, it should be done with the view to finding all possible risks and vulnerabilities. If you cheat on the cybersecurity audit, there can be massive losses in the future.
b) Forgetting Mobile Devices
Many cybersecurity audits try to emphasize the servers but fail to focus on employee mobile phones. Since these devices are used to check company emails and applications, the hackers get a great way to enter and steal company data.
c) Ignoring Cloud Vendors
No matter how amazing or popular the cloud platform you’re using, the entire responsibility for your organization’s security lies on your shoulders. You need to ensure that your cybersecurity compliance checklist doesn’t miss the cloud configurations.
Explore more about Cloud Security Vendors
| Common Mistake | Consequence | Prevention |
| Scope Creep | Audit never finishes | Define boundaries early |
| Manual Data Entry | High error rates | Use automated discovery tools |
| Ignoring Minor Bugs | “Death by a thousand cuts” | Treat every gap with respect |
How Qualysec Can Help with Your Cybersecurity Audit
Have you ever found the cybersecurity process really challenging? At Qualysec, the best Cybersecurity company in India, we solve all the challenges and complexities involved with the cybersecurity assessment checklist. More than just average security auditors, we are your partner in overseeing all vulnerable areas and preparing your organization against the battle of stealing sensitive data and information.
One of the many benefits Qualysec brings with the Cybersecurity audit checklist is the personalized and business-focused audit processes in 2026. Say goodbye to your company’s security stress with our comprehensive range of services, such as –
a) Expert Penetration Testing
Our team is trained and experienced to think and act like hackers while testing and identifying the weak areas in apps, software, platforms, and network infrastructure.
b) Vulnerability Management
Rather than just leaving you with the list of security issues, we prioritize the crucial ones with recommended solutions to fix them on an urgent basis.
c) Compliance Excellence
Whether your organization needs SOC2, ISO 27001, or other local Indian security compliance certifications, we are there to guide and support the process.
d) Simplified Reporting
At Qualysec, we transform the complex Cybersecurity audit reports into as simple as they could be. With professional reports, your internal developers and team members can easily get on the right track.
With Qualysec, your Cybersecurity audit checklist is your shield to protect your company’s critical data, information, reputation, or future. Contact us today to discuss how we can build a security-first culture for your organization with the best industry standards and practices.
Conclusion
Honestly, if you’re not looking at your security setup in 2026, you’re asking for trouble. It’s the best way to keep your business from being an easy target. Leaving things as they are is basically an open invitation for hackers. Catching those weak spots now is going to save you from a massive disaster later on. With hackers getting smarter with every passing day, the employees and operations need to follow a structured checklist and work with a trusted Cybersecurity company in India, like Qualysec.
This guide has already covered the step-by-step process to perform a security audit of an organization. From asset discovery to backups, your organization can use this checklist to make it a roadmap for security practices. With robust security practices and Cybersecurity Risk Assessment in place, you’re safeguarding the people, business reputation, and everything related to the company.
With the Penetration Testing Checklist by Qualysec, your company’s processes and systems can be more secure against today’s or future risks.
Frequently Asked Questions (FAQ)
Q1. Can you explain the cybersecurity audit checklist in simple words?
In simple terms, a cybersecurity compliance Audit covers all sorts of technical, non-technical, physical, and operational checks to ensure the company is at the right stage against potential exploiters. These cybersecurity reports help evaluate the performance and results of a company’s security systems with legal compliance.
Q2. Why is a cybersecurity audit checklist important?
In the growing era of digitization and adoption of Artificial Intelligence, the IT systems become complex and more vulnerable to hackers. A checklist helps identify every minor to major loopholes with periodic security practices in place.
Q3. What specific things does a cybersecurity audit checklist involve?
The core operations of cybersecurity and Compliance Security Audit include Asset Management, Multi-factor Authentication, Network Security, Data Encryption, Employee Training, Incident Response, and more.
Q4. Who should use a cybersecurity audit checklist?
Every organization, whether online or using artificial intelligence and other platforms, needs a cybersecurity audit checklist. These organizations can be small businesses, Information Technology managers, and specialized security teams to comply with industry standards.






















































































































































































































































































































































































































































































































































































































0 Comments