Cyberattacks are genuine, changing, and more sophisticated in today’s digital environment; they are not theoretical any longer. This is why many businesses are turning to trusted Cyber Security Companies in Brisbane to protect their data and operations. Ransomware, phishing attempts, insider breaches, and sophisticated persistent threats constantly target businesses in Brisbane, regardless of their size. Even one cybersecurity failure can lead to financial loss, legal penalties, downtime, or long-term reputational damage. Whether you are a local startup or a government agency, selecting the right cybersecurity partner is now a strategic necessity for operational resilience.
True cybersecurity goes beyond a simple firewall or antivirus installation. The system operates through an integrated system that combines technology with governance and human understanding. The top service provider which you select will help you achieve compliance with Australian regulations while they actively search for security weaknesses. This guide ranks top local firms and provides a refined roadmap for securing local firms’ digital assets.
Qualysec offers a comprehensive Cyber Security Audit to assess your organization’s digital defenses!
What Do Modern Cybersecurity Services Cover?
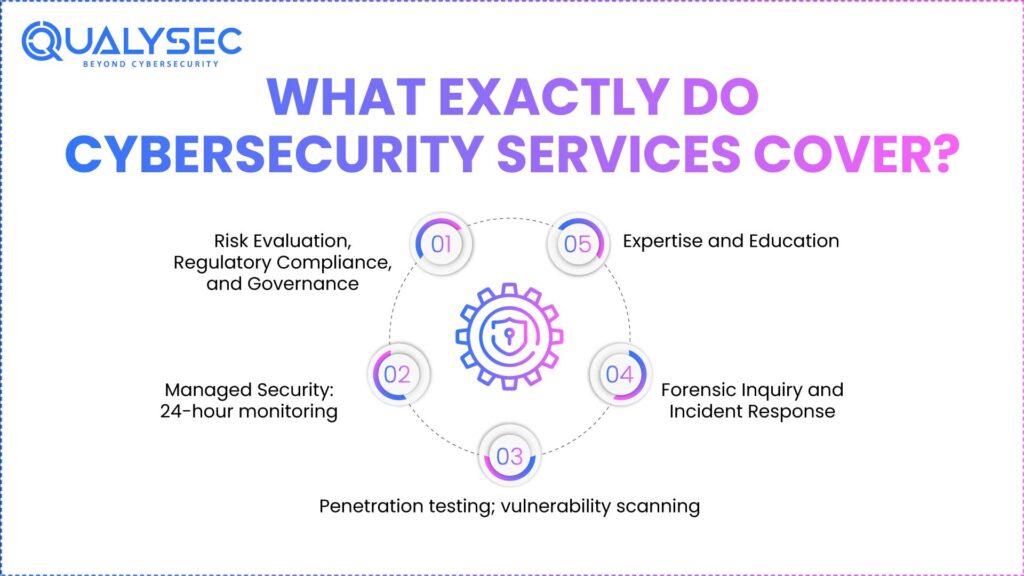
The cybersecurity services provide complete protection, which extends to safeguarding against all potential losses and security breaches. Best cybersecurity companies in Brisbane use their technical skills together with their human-focused methods to create complete security solutions.
These services seek to increase operational resilience, facilitate faster incident response, and cultivate a security-conscious culture throughout your company in addition to preventing breaches. You choose a provider that will satisfy your particular commercial demands when you have complete knowledge of these service areas.
1. Risk Evaluation, Regulatory Compliance, and Governance
- Finding Weaknesses: Investigating personnel behavior, applications, cloud infrastructure, and networks will help one discover faults. Before attackers profit, providers identify technical as well as human errors, so they help businesses set priorities and actively manage risk.
- Implementing Policies: Businesses employ ordered frameworks like ISO 27001 or the Australian Essential Eight to manage information security systematically. In every security procedure, they encourage consistency, accountability, and standards.
- Regulatory Alignment: Brisbane-based companies need to follow laws like the Privacy Act, APRA requirements, or sector-specific rules. Compliance improves customer trust and operational credibility in addition to helping to avoid fines.
2. Managed Security: 24-hour monitoring
- Continuous Surveillance: Through 24-hour network, endpoint, and cloud environment monitoring, businesses may quickly spot odd behavior. Often, viewing accelerates reaction times and stops little problems from getting worse.
- AI-Driven Detection: Comprising incident detection technologies grounded in artificial intelligence, behavioral monitoring, and sophisticated analytics, which find odd patterns or possible dangers. Early identification enables faster incident management and lowers the likelihood of significant breaches.
- Rapid Response: Once a danger is found, a rapid reaction is imperative. By means of managed containment, reduction, and planned recovery, services seek to minimize data loss, company disruptions, and downtime.
3. Penetration testing; vulnerability scanning
- Simulated Attacks: Ethical hackers reveal system, application, and network faults using controlled assaults. Using this aggressive strategy corrects faults before hostile actors can benefit from them.
- Regular Scanning: Regular vulnerability scanning guarantees that recently installed equipment, freshly released software, or system upgrades do not create security vulnerabilities. Continuous visits preserve your defenses against current changing hazards.
- Comprehensive Reporting: Thorough, practical reports highlighting flaws, possible consequences, and recommended remediation strategies help inform and prioritize decision-making by means of thorough reporting.
4. Forensic Inquiry and Incident Response
- Immediate Action: Instant action guarantees fast breach containment, hence reducing operational disturbance and restricting possible damage by means of a well-defined incident response plan.
- Root Cause Analysis: Post-event analyses help prevent future incidents and raise general security posture by determining the attack vector and techniques employed.
- Recovery Plans: Rapidly restore systems, data, and processes using recovery approaches. They include documentation, lessons learned, and testing to improve resilience and preparedness for upcoming events.
5. Security Awareness Training
- Employee Education: Frequently, employee experience acts as the first line of defense. Training sessions highlight correct digital behavior, passwords, phishing, and social engineering.
- Phishing Simulations: Through phishing simulations, personnel members can acquire information on how to identify and respond to actual threats. This realistic approach raises awareness and lowers human mistakes.
- Regular Updates: Continuous protection and business resilience are ensured by means of regular updates, keeping employees informed of the most current threats, legal changes, and security practices.
See the Depth of Our Testing Expertise. Download the Sample Penetration Testing Report Today.
Download a Sample Pen Testing Report

What to keep an eye out for when selecting a cybersecurity business in Brisbane
Selecting the correct provider means assessing capacity, trust, and a match with company requirements. Significant factors to remember include:
- Reputation and Experience: For reputation and expertise, search for years of business, client reviews, and recorded case studies. Experienced practitioners follow appropriate remedial measures and expect hazards.
- Regional Compliance: Deep understanding of the APRA CPS 234 and local Queensland privacy standards.
- Service Scope: See if the provider offers full-service choices (monitoring, testing, compliance) or only specialized services.
- Local presence: Local presence promises faster local hazard knowledge and assistance.
- Certifications & Partnerships: Certifications and alliances show technical knowledge and conformance to industry norms; ISO 27001, CREST, or other certificates help.
- Transparency & Communication: Trust depends on openness and communication channels, clear reporting, and escalation procedures.
- Tailored Method: Adaptive providers modify solutions depending on industry, risk profile, and company size.
- Pricing and Value: Examine the cost in light of the degree of coverage offered and the possible return on investment.
- Culture & Training: Emphasizing staff training and security culture, providers lower human-related hazards.
Download Our Detailed Case Studies to See How We Help Businesses Strengthen Their Cybersecurity.
Top Cyber Security Companies in Brisbane 2026
Company | Primary Specialization | Target Market | Key Technical Strength | Service Model |
Qualysec | Offensive Security (VAPT) | Fintech, SaaS, SMBs | 100% Manual Pentesting | Pure-play Security |
CyberCX | Full-Spectrum Cyber | Enterprise & Gov | Scale & Incident Response | Managed Service (MSSP) |
Itopia | IT & Security Hybrid | Small Business | Local On-site Support | Managed IT (MSP) |
Ever Nimble | Proactive Monitoring | Mid-Market | Human-Centric Support | Managed Security |
Acumenis | Compliance & GRC | Regulated Industry | ISO 27001 Implementation | Specialized Consulting |
1. QualySec
Australia’s Most Trusted Cybersecurity Partner for Brisbane Businesses
Known for its outcome-driven approach, sophisticated technological knowledge, and globally benchmarked security solutions, Qualysec is one of the top cyber security firms in Brisbane. Qualysec, unlike volume-based IT companies, is a pure-play cybersecurity business focusing on offensive security, human-led AI penetration testing, compliance, and digital risk minimization. This makes them the preferred partner for SMBs, corporations, government agencies, fintechs, SaaS companies, and crucial infrastructure providers all around Australia.
Qualysec supports Brisbane companies in improving their security posture via ongoing testing, predictive risk analysis, and customized strategies in line with Australian standards like the Essential Eight, Privacy Act, ISO 27001, and APRA CPS 234, with a significant footprint in the APAC region and a dedicated team of ethical hackers, security leaders, and compliance professionals.
Offers these services:
- Advance penetration testing: network, Internet of Things, cloud, API, mobile, web,
- adversarial simulation and red teaming
- Assessment of vulnerabilities and ongoing scanning
- AWS, Azure, GCP: cloud security assessment
- Inspecting Secured Code
- ISO 27001, SOC 2, APRA, GDPR, HIPAA provide compliance assistance.
- Digital examination and incident reaction
- Evaluating Cyber Maturity and Cybersecurity Counseling.
Why They Stand Out: For their precision and dependability, Qualysec is trusted by more than 300 international corporations for its 100 percent manual, deeply thorough security testing coupled with evidence-based reports, strong NDA policies, and rapid delivery managed by a committed project manager.
Good Vibes: A clear, disciplined, highly competent crew makes cybersecurity simpler for Brisbane companies while providing world-class experience free from enterprise-level complexity or cost.
Tip: Select Qualysec if you need a full cybersecurity partner with industry-leading knowledge and accuracy in testing, compliance, and ongoing monitoring.
Partner with Qualysec to streamline the onboarding process and monitor the performance of your chosen provider!
Latest Penetration Testing Buyer Guide

2. CyberCX- Cyber Security Services Brisbane
CyberCX, which is Australia’s largest cybersecurity company. Offering end-to-end services including governance, risk management, cloud security, and incident response, Australia’s biggest cybersecurity company. Accenture’s acquisition of them emphasizes their level and knowledge.
Why They Stand Out: Ideal for major companies wanting scalable, multi-service solutions.
Good Vibes: Thorough familiarity with Australian compliance guarantees dependable service.
Tip: Smaller firms should look at affordable and scalable options.
3. Itopia- IT Security Brisbane
Concentrating on IT assistance and cybersecurity for SMBs in Brisbane, Itopia offers customized solutions suited to budgets and business needs.
Why They Stand Out: Their customized support for small and medium-sized firms distinguishes them.
Good Vibes: Local knowledge guarantees appropriate, workable answers.
Tip: Inquire about bundled service options for thorough protection.
4. Ever Nimble- Cyber Securities Companies
A provider known for proactive threat detection, Managed IT, and cybersecurity solutions emphasizing compliance and proactive threat detection.
Why They Stand Out: Hands-on, aggressive assistance for companies seeking advice and monitoring helps them to stand out.
Good Vibes: Clear communication and close customer relationships.
Tip: Include reporting and incident reaction systems.
5. Acumenis- Network Security Companies

Specializing in network security and ISO 27001 deployment ISO 27001 deployment, and incident readiness for compliance-focused organizations.
Why They Stand Out: Their expertise in hostile security and regulatory compliance distinguishes them.
Good Vibes: Experienced consultants providing practical suggestions: Good Vibes.
Tip: Include them for audits and to improve your security posture.
Not Sure Which Cybersecurity Company to Choose? Get a free 30-minute consultation with our security experts to help you evaluate the right partner for your business. Click here to book your free consultation.
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
Method for Selecting the Right Cybersecurity Provider
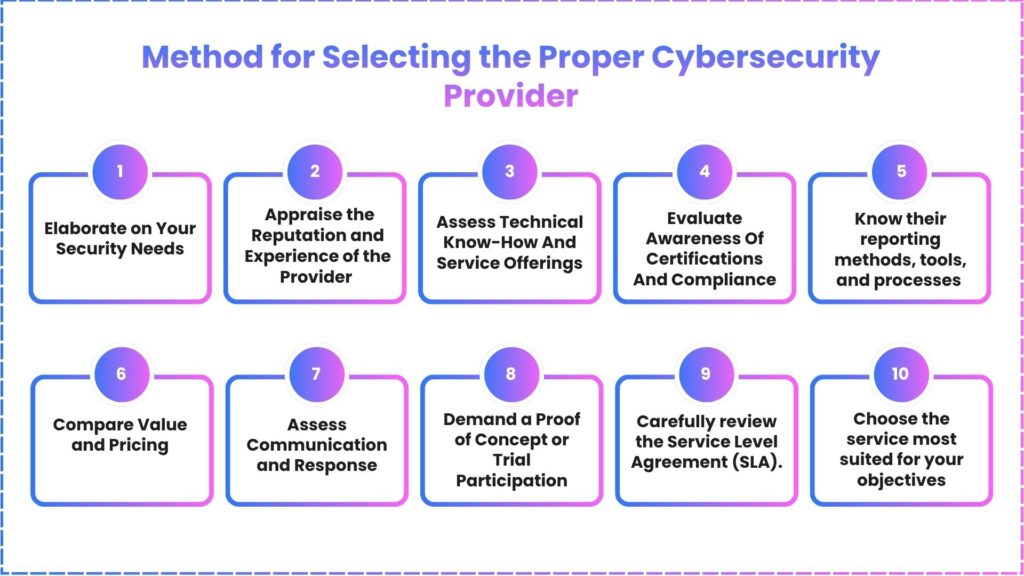
Every Brisbane company must carefully consider its choice of cybersecurity provider. The perfect partner improves general security posture, assists compliance, and provides protection against changing hazards. An easy, realistic, step-by-step strategy to help you assess and select the best cybersecurity provider follows.
1. Define Your Scope
Start by noting your company’s real requirements: penetration testing, compliance assistance, incident response, cloud security, 24/7 monitoring, or a whole security makeover. A precisely defined scope guarantees concentrated analysis and avoids needless expenses.
2. Verify Experience
Check their client comments, certifications, specialisation in the sector, and years of experience. Reliability is suggested by strong recommendations, case studies, and demonstrated success with companies close to yours.
3. Evaluate Cultural Fit
See whether the provider offers just specialist services or complete ones. Search for experts in managed security, risk assessment, cloud security, penetration testing, and conformance with criteria such as ISO 27001 or the Australian Essential Eight.
4. Check Certifications
Be sure their staff possesses pertinent certifications such as CEH, OSCP, and CISSP. Also, ensure they understand Queensland-specific standards as well as Australian law, including the Privacy Act and APRA CPS 234. Learn more about
5. Review Reporting
Inquire about their incident handling procedures, monitoring techniques, and testing methods. Check sample reports to ensure the cybersecurity company gives unambiguous explanations, risk effect information, and practical remediation plans.
6. Compare Value and Pricing
Do not decide just on cost. Rather, weigh what each supplier provides for the price, scope of work, support availability, reporting quality, knowledge, and depth of testing.
7. Assess Communication and Response
A dependable provider will provide rapid response times, a committed point of contact, and open communication. Critical security events call for this.
8. Demand a Proof of Concept (PoC)
A free preliminary security audit, a demonstration, or a little trial project is available from many well-known providers. Before making a long-term commitment, this is a wonderful means of validating their knowledge.
9. Understand the SLA
Include confidentiality, data management, escalation processes, responsibility limitations, deadlines, and deliverables in the SLA.
10. Scalability
Apart from fixing errors, the ideal partner will assist you in developing a long-term, scalable, resilience-centered cyber security plan.
You might also like to read: Top 10 Cybersecurity Companies in Melbourne.
Conclusion
Choosing the appropriate cyber security companies in Brisbane requires alignment of your risk profile, business goals, and operational needs. Usually, the most inexpensive or biggest provider is not the most suited option. With technical knowledge, regulatory compliance, ongoing monitoring, quick reaction, and a security-aware culture catered to your business, a good partner offers these benefits. You can guarantee strong protection for your digital assets by specifying your needs, shortlisting suppliers, posing pertinent questions, and assessing alignment.
Need a security check for your digital assets? Talk with Our AI Security Assistant to Instantly Analyze Your Cybersecurity Needs.
Chat with our intelligent AI Assistant and get tailored insights in seconds.

FAQs
1. What are the best cyber security companies in Brisbane?
A: Best cyber security companies Brisbane, depending on company size, complexity, and resources, CyberCX (large companies), Itopia and Ever Nimble (SMBs), and Acumenis (compliance-oriented).
2. How do I choose the right provider?
A: Define needs, then assess reputation, services, communication, and fit; next, check references and pricing.
3. What services do these companies provide?
A: Twenty-four-hour monitoring, penetration testing, VAPT, incident reaction, staff training, and compliance aid help to evaluate risk.
4. Why invest in professional cyber security?
A: Maintains confidence with customers, partners, and authorities and lowers financial loss, downtime, and breaches.
5. How much do these services cost?
A: Fees change according to risk profile, size, and services needed. Basic SMB monitoring costs less than enterprise full-service solutions, which cost more. Not only price but also value and return on investment always have to be kept in mind.
Have any questions? Feel free to ask now—our cybersecurity experts are here to help.





















































































































































































































































































































































































































































































































































































































0 Comments