Cyberattacks cost companies billions of dollars yearly. Most of these attacks take advantage of recognized but neglected flaws, which is yet more terrible. Though these security flaws may seem small, attackers can turn them into serious breaches, data loss, or total system takeovers once found. For businesses of any size, this circumstance makes Vulnerability Remediation and repair a crucial part of cybersecurity.
Learning how to address flaws is especially important if your company depends on digital tools, networks, or customer information, which practically every business does. Understanding the remediation process, acknowledging the difficulties, and applying the best methods enable you to keep resilient and secure systems. Think of this handbook as your step-by-step guide to success with a more secure position as well as survival in a world of cyber attacks.
Want to strengthen your business against threats right away? Start by learning how remediation works before attackers exploit open doors!
What Constitutes Vulnerability Correction?
Experts refer to the systematic process of identifying, evaluating, prioritizing, and correcting flaws in hardware, software, and networks as vulnerability remediation. Knowing where the cracks are is inadequate; you must mend them before they develop, and this is where Vulnerability Testing plays a vital role. Think of it as digital cleanliness: you should not keep your front door open at night; you should not leave an unpatched system exposed either.
This process is not only about correcting programs. It includes reconfiguring incorrect configurations, deleting redundant services, implementing security measures, or totally replacing susceptible components. Unremediated vulnerabilities constantly endanger sensitive data and corporate operations as they wait for exploitation.
Several connected activities link vulnerability remediation:
- Vulnerability scanning and remediation: Vulnerability scanning finds flaws during regular scans; remediation guarantees their correction.
- Vulnerability assessment remediation: Beyond scanning, vulnerability assessment remediation grades concerns by severity and risk before resolving them.
- Automated vulnerability remediation: Using artificial intelligence-driven or scripted solutions, automated vulnerability remediation quickens and simplifies the process.
- Vulnerability remediation services: Outsourced answers to security specialists who offer particular expertise for vulnerability correction services are vulnerability repair services.
- VAPT remediation: Specific remedies for issues discovered during Vulnerability Assessment and Penetration Testing (VAPT).
If your team feels overwhelmed, consider professional remediation services. Outsourcing doesn’t lighten the workload; it ensures critical fixes happen without delay!
Why Addressing Vulnerability Matters
Frequently, the weakest link defines the degree of cybersecurity efficacy. Attacks could start with a single, unpatched vulnerability, so lowering exposure demands treating it. Shielding your systems against ransomware, data theft, illegal access, and other types of assaults helps you close those gaps.
Another strong reason for remediation is compliance. Strict deadlines for companies to address issues set by industry standards include PCI DSS, HIPAA, and ISO 27001. Not following rules could result in accreditation loss, ruin your reputation, and face penalties. It is not discretionary; rather, controlled areas call for correction.
At last, remediation builds confidence and saves money. Far more than preventive solutions cost, violations are also distrusted by consumers who visibly show concern for data security. Proactive remediation not only offers security protection but also gives you a competitive advantage.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Difficulties in Vulnerability Response
Though it sounds easy, most businesses encounter hurdles throughout the process of error correction. Knowing these impediments starts one on the road to overcoming them.
1. Overwhelming amounts of vulnerabilities
Security scans can find thousands of problems. Teams frequently spend time fixing minor defects without a system to rank priorities, leaving essential hazards unprotected.
2. Scarcity of Trained Resources
Worldwide, people have limited access to cybersecurity knowledge. Many firms find it difficult to locate individuals with the expertise needed to properly address sophisticated security flaws.
3. Financial Restrictions and Time Limits
Businesses cannot fix everything right away, given limited funds and time. This frequently results in postponed corrections, exposing vulnerabilities for weeks or months.
4. Complex IT Environment
Businesses meet on-premises servers, third-party platforms, and cloud services. Scheduling regular maintenance throughout this complexity requires a great deal of effort.
5. Delays in patch administration
Vendors don’t always provide patches quickly. Applying patches could disrupt services; thus, companies may postpone updates even if they are available.
6. Gaps in communication
While security teams might find flaws, IT or development teams in charge of fixes sometimes lag because of conflicting priorities.
Should your company face these obstacles, automated vulnerability correction or outsourcing to specialists will lighten the load!
Explore top VAPT companies to analyze your security posture
Process for Vulnerability Remediation
A precise and repeatable method assures regular and efficient vulnerability resolution.
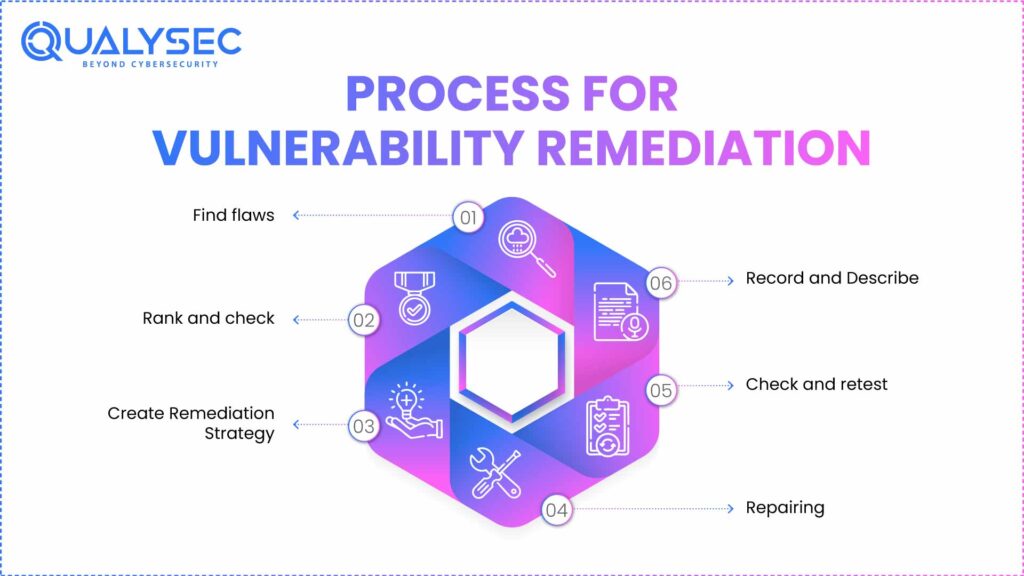
Step 1: Find flaws
First comes frequent vulnerability scanning. Applications, networks, and endpoints are constantly scanned for defects using tools. Early identification lets companies resolve issues before attackers find them.
Step 2: Rank and check
Not all vulnerabilities carry the same risk. To guide what to repair first, teams use severity scores (like CVSS), exploitability, and business circumstances. A flaw in an exposed consumer portal, for instance, takes precedence over a low-risk internal bug.
Step 3: Create Remediation Strategy
Once goals are set, IT and security teams create particular solutions. Options may include:
- Patching software: A software patch is the process of implementing supplier updates to fix defects.
- Configuring systems: Setting up systems: tighten permissions, shut unused ports, or change settings.
- Removing services: Eliminating outdated or unnecessary apps helps with service removal.
- Compensating controls: Adding temporary protections, like firewalls, if a patch is not found.
Step 4: Repairing
The team deploys patches here. Teams change, patch, or replace systems. Automatic vulnerability repair tools speed up repetitive fixes, hence lowering human involvement.
Step 5: Check and retest
It’s important to retest after implementing corrections. This guarantees that the team introduced no new problems and confirms that they fixed the vulnerabilities.
Step 6: Record and Describe
For audits and compliance, keeping thorough records is absolutely essential. Documentation also aids in the enhancement of the next remediation cycle.
Secure your business with expert Vulnerability Management Services.
Best Methods for Vulnerability Remediation
Combining remediation with deliberate methods yields the best results. The following techniques will improve the process:
1. Automate where possible
Automation speeds up patching and lessens manual labor. Automated processes guarantee that vulnerabilities are always handled without delay for repeated issues.
2. Give top priority according to risk level
Focus assets on places with the most potential harm. This approach prevents idle labor on trivial-influence errors.
3. Integrate with DevOps
Integrating remediation into the DevOps pipeline reveals flaws early in development. Early solutions to problems lower later costs and complexity.
4. Regular Vulnerability Assessments
Regular evaluations find fresh weaknesses before attackers do. By acting early, we decrease general risk exposure.
5. Cross-Team Cooperation
It only bears part of the responsibility for security. Good remediation demands open communication among security experts, developers, and system administrators.
6. Outsource when needed
Not all businesses have internal knowledge. Faster fixes and specialized knowledge come from vulnerability remediation services and VAPT remediation experts.
7. Continuous Monitoring
Every day, threats change. Regular monitoring guarantees that companies can detect and immediately fix flaws.
Check out our detailed guide on Vulnerability Assessment Methodology.
Typical Vulnerability Examples in Security
Some security vulnerability remediations seem more common than others and present serious hazards if ignored:
- Unpatched software: Attackers often target outdated applications and operating systems using unpatched software.
- Misconfigurations: Open ports, bad APIs, or incorrect access restrictions make systems easy targets.
- Weak authentication: Weak authentication opens easy access for hackers because there is a lack of strong passwords or multi-factor authentication (MFA).
- SQL injection and XSS: Weaknesses in web applications enable attackers to inject malicious code or control databases by means of SQL injection and XSS.
- Zero-day vulnerabilities: Before businesses release corrections, attackers exploit newly discovered vulnerabilities known as zero-day attacks.
Unsure which weaknesses impact you most? Begin with a professional scan to find high-risk problems in your environment!
How Qualysec Can Help
You might see by now that although you find it difficult to handle by yourself, you need to pursue remediation. Qualysec then becomes your dependable ally.
Qualysec provides end-to-end vulnerability remediation services tailored to global organizations. They don’t find vulnerabilities—they help fix them with actionable guidance and hands-on support. Their services cover:
Finding flaws, ranking corrections, and verifying patches with complete scanning and remediation.
Comprehensive scanning and remediation: Cutting manual delays by means of effective, dependable processes.
Automated vulnerability remediation solutions: Using step-by-step help, expert direction, and VAPT repair solves problems discovered in penetration tests.
Expert guidance and VAPT remediation: guaranteeing that companies meet international rules for PCI DSS, HIPAA, GDPR, and other such requirements.
Compliance support: Constant monitoring keeps vulnerabilities from recurring.
Ongoing monitoring: Ready to protect your systems without overworking your internal teams? Contact Qualysec for customized restoration plans that genuinely help.
Latest Penetration Testing Report

Conclusion
More than a security checklist, vulnerability correction is corporate protection. Left unaddressed, weaknesses could economically and reputationally cripple companies. Adopting a systematic approach, giving fixes priority according to risk, and adhering to best practices, including automation and cooperation, can help companies greatly decrease exposure to attacks through effective Vulnerability Remediation.
Yes, limited resources and complicated IT environments make remedial work challenging. With the right instruments, processes, and collaborations with Qualysec’s help, remediation proves not only workable but also successful. Among the best investments any business can make in a digital age, when hazards change daily, is closing security gaps before attackers use them.
Ready to protect your systems without overburdening your internal teams? Reach out to Qualysec for tailored remediation strategies that actually work!
FAQs
1. What are the four steps of vulnerability remediation?
Identifying flaws, evaluating and ranking them, putting in fixes, and verifying results with retesting are the four major phases.
2. What are the four stages of vulnerability?
The stages are discovering, evaluation, treatment, and monitoring. Each stage builds on the one before it to establish a safe cycle.
3. What are the possible ways to remediate vulnerabilities?
You could update programs, customize systems, disable dangerous services, or put in place compensating security measures, such as firewalls.
4. How does vulnerability remediation differ from vulnerability assessment?
Assessment finds and assesses hazards; treatment solves them. One discovers the issue; the other solves it.
5. What are the common types of vulnerabilities that need remediation?
The most often encountered issues are misconfigurations, weak authentication, web application flaws, zero-days, and third-party dangers, as well as unpatched software.






















































































































































































































































































































































































































































































































































































































0 Comments