Network security vulnerabilities pose a significant risk to the security of your digital infrastructure, allowing cybercrime organizations to breach, mine data, or compromise business activities. With the current interdependent digital environment, knowledge of network security vulnerabilities is a major necessity in defending your organization against complex cyber-attacks.
These weaknesses come in different forms in the hardware, software, and human processes. They may include obsolete software, improperly configured firewalls, inadequate passwords, and unconfigured access points. In a digitalized economy where business operations are growing well beyond any physical borders, it is not only advisable but fundamentally essential to Indian businesses to have these security gaps identified and closed.
The effect of security breaches on unattended network security vulnerabilities can be horrifying. The organizations can encounter data breaches, financial losses, regulatory fines, and a serious loss of reputation. This guide will explain the various forms of vulnerabilities, estimate the associated risks, and outline the best prevention measures.
What Are the Main Types of Network Security Vulnerabilities?
Learning the different kinds of network security vulnerabilities is the initial step to establishing a strong security outline. These weaknesses are grouped into three major areas that all organizations must take note of.
1. Hardware-Based Network Security Vulnerabilities
The vulnerabilities of hardware are also a serious threat to network infrastructure security . Anything attached to your network can easily become an entry point for the attacker unless it is effectively monitored and secured.
Common Hardware Vulnerabilities Include:
- Unsecured IoT devices with default passwords
- Misconfigured firewalls and routers
- Unencrypted mobile devices used by employees
- Unauthorized USB drives and external storage devices
- Inadequately protected Wi-Fi access points
- Server hardware without proper physical security controls
With the expansion of the Internet of Things (IoT) in India workplaces, the number of hardware-based risks has risen substantially. A network vulnerability scanner can assist in the detection of these devices and in evaluating their security level. Proper policies of device management should also be in place, and the scanning of internal vulnerabilities should be done using vulnerability scanning tools to ensure monitoring of all devices in continuous connection.
2. Software-Based Network Security Vulnerabilities
One of the most popular attack vectors is a software vulnerability. They occur as a result of bugs, outdated versions, or poor coding practices that create security holes in operating systems and applications.
Critical Software Vulnerabilities:
- Unpatched operating systems and applications
- Vulnerable browser plugins and extensions
- Insecure third-party software integrations
- Outdated content management systems
- Weak application programming interfaces (APIs)
- Misconfigured database systems
Software-related risks can also be identified through regular cybersecurity vulnerability assessment activities. Organisations are advised to install automated patch management operations and enact network vulnerability scanning tools to identify outdated software within their network.
3. Human-Based Network Security Vulnerabilities
Human Link is the most vulnerable aspect of network security. Although the attacks are of a social engineering nature, they are successful due to the use of human psychology as opposed to technical vulnerabilities.
Human-Related Security Risks:
- Weak password practices and credential reuse
- Falling victim to phishing and social engineering attacks
- Insider threats from disgruntled employees
- Inadequate security awareness and training
- Poor adherence to security policies
- Unauthorized software downloads and installations
A comprehensive cybersecurity assessment should include a vulnerability assessment that incorporates human factor analysis in cybersecurity. Constant security training and awareness are some of the key ingredients of a good security policy.
How Do Network Security Vulnerabilities Impact Your Business?
The outcomes of network security vulnerabilities on the business are much more far-reaching than the mere technical implications. Organizations have complex risks that may cripple their existence in the competitive environment.
Financial Consequences
The issue of network security vulnerabilities can result in significant financial losses in various ways. Direct costs consist of incident response costs, system recovery costs, and regulatory fines. Indirect expenses include lost productivity, customer compensation, and disruption to the business.
It has been found that 84 percent of enterprises have severe vulnerabilities in their networks. Indian enterprises have experienced substantial growth in the average cost of data breaches; therefore, it is more economical to spend on prevention rather than on remediation.
| Impact Category | Potential Consequences | Average Cost Range |
| Data Breach | Customer data theft, regulatory fines | ₹50 lakhs – ₹5 crores |
| System Downtime | Lost productivity, revenue loss | ₹10 lakhs – ₹1 crore per day |
| Reputation Damage | Customer loss, market share decline | Long-term revenue impact |
| Recovery Costs | System restoration, security upgrades | ₹25 lakhs – ₹2 crores |
| Legal Expenses | Litigation, compliance costs | ₹15 lakhs – ₹75 lakhs |
Operational Disruptions
Vulnerability in cyber security has the capability to bring about severe operational complications. Ransomware attacks have the potential to encrypt essential business information, while DDoS attacks can cause systems to become unreachable.
Indian businesses in industries such as banking, healthcare, and e-commerce, in particular, are at risk of these shocks. The effect is compounded by service disruption in the supply chain and interruption of customer service.
Regulatory and Compliance Issues
The changing landscape of data protection in India, with the Digital Personal Data Protection Act, is shifting more of the burden towards organizations to secure sensitive data. Network security vulnerabilities can cause compliance breaches and regulatory fines.
Organizations should adopt robust network vulnerability assessment programs to fulfill their regulatory obligations, thereby ensuring they do not face legal repercussions for failing to implement effective assessment programs.
What Are the Best Strategies to Prevent Network Security Vulnerabilities?
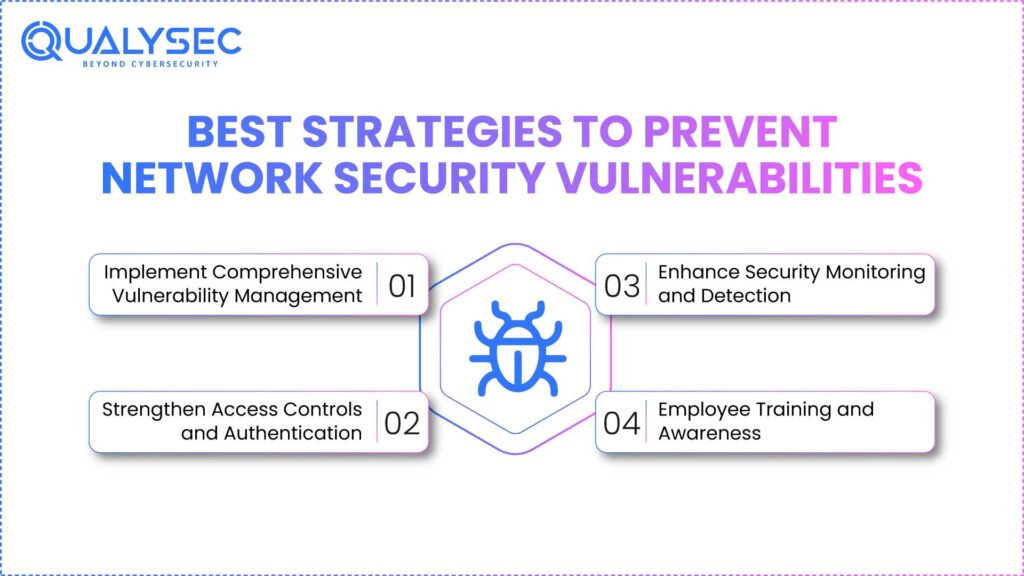
Network security vulnerabilities are averted through the multi-layered approach of the use of technology, processes, and human factors. Organizations should adopt proactive approaches rather than reactive measures to keep up with the changing threats.
1. Implement Comprehensive Vulnerability Management
The core of any network security is a strong vulnerability management program. This includes assessment, prioritization, and remediation of identified vulnerabilities on an ongoing basis.
Key Components of Vulnerability Management:
- Deploy network vulnerability scanning tools for continuous monitoring
- Conduct regular network vulnerability assessment activities
- Use network security scanner solutions for real-time threat detection
- Implement automated patch management systems
- Establish vulnerability prioritization based on risk levels
- Create incident response procedures for critical vulnerabilities
Organizations should schedule regular scans using both internal vulnerability scanner tools and external network assessments to get comprehensive coverage of their security posture.
2. Strengthen Access Controls and Authentication
Access controls prevent network security vulnerabilities from being exploited by unauthorized users. Among the measures of this strategy, multi-factor authentication and the principle of least privilege are fundamental.
Access Control Best Practices:
- Implement multi-factor authentication for all user accounts
- Use strong password policies with regular updates
- Deploy privileged access management solutions
- Monitor user activities and access patterns
- Regular review and update of user permissions
- Implement network segmentation to limit lateral movement
3. Enhance Security Monitoring and Detection
Continuous monitoring enables organizations to identify threats and respond promptly when their network security vulnerabilities and weaknesses are exploited. This requires the ability to utilize sophisticated security tools and have trained staff to track security incidents effectively.
Monitoring and Detection Strategies:
- Deploy Security Information and Event Management (SIEM) systems
- Implement intrusion detection and prevention systems
- Use behavioral analytics to identify unusual activities
- Establish 24/7 security operations center capabilities
- Create automated threat response procedures
- Regular security audit and penetration testing
Explore more in our article on Network Security Testing
4. Employee Training and Awareness
Human aspects are vital in vulnerability to cyber security. Periodic training enables the employees to identify and overcome security threats.
Training Program Elements:
- Phishing simulation exercises
- Social engineering awareness sessions
- Security policy and procedure training
- Incident reporting mechanisms
- Regular security updates and communications
- Role-specific security training programs
Why Choose Qualysec for Network Security Vulnerability Assessment in India?
Selecting the right cybersecurity partner to secure your organization against network security vulnerabilities is crucial. Qualysec is the pioneer of cybersecurity services and comprehensive vulnerability assessment in cyber security in India, ensuring businesses remain safe against a dynamic threat environment.
Qualysec has extensive expertise in network vulnerability scanning and network assessment, with successful clients across multiple industries, including banking and finance, healthcare, e-commerce, and government sectors. They employ their team of certified security professionals, using advanced network vulnerability scanning tools and methodologies to identify, assess, and help remediate security weaknesses in your infrastructure.
Explore more about how to conduct Network Security Assessments and protect your business.
What Makes Qualysec the Best Choice:
Comprehensive Service Portfolio: Qualysec provides the full suite of services in cybersecurity, namely vulnerability assessment, penetration testing, security audit, and compliance consultation. Their network security scanner products provide continuous scanning and timely threat detection.
Explore advance penetration testing services
Industry Recognition: Qualysec has received industry recognition as a partner in providing high-quality security services. Their cyber security vulnerability assessment methodologies adhere to global standards and best practices.
Local Expertise with Global Standards: Qualysec offers global standards of cybersecurity with deep insights into the Indian business environment. Their internal vulnerability scanners are designed to meet the compliance requirements in India.
Advanced Technology Stack: Qualysec utilizes state-of-the-art network vulnerability assessment tools and technologies to ensure successful and in-depth security examination processes. Their capability to scan automatically eliminates the chances of leakage in any vulnerability detection process.
Experienced Team: Qualysec has trained certified security professionals holding credentials like CISSP, CEH, and OSCP to offer a high level of expertise to each engagement. They are aware of new network security vulnerabilities and emerging cyber-threat trends.
Cost-Effective Solutions: Qualitysec offers affordable packages for its services, making enterprise-level security accessible to medium-sized enterprises. Their vulnerability in cyber security solutions provides excellent return on investment through risk reduction.
Network security can only be established with sanctity and professionalism, considering the nature of dynamic cyber threats. Employing a team of highly qualified cybersecurity experts will guide your business to come up with highly effective solutions to network threats and protect essential business resources.
Talk with Our Experts to learn how Qualysec can help strengthen your network security posture and protect your business from evolving cyber threats.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Conclusion
Network security vulnerabilities pose one of the greatest challenges to modern organizations. It is imperative to understand the different forms of vulnerabilities, namely hardware-based, software-based, and human-based, to devise suitable defense measures.
The consequences of such vulnerabilities extend beyond technical aspects, including costs incurred, operations interrupted, and non-compliance with regulations. Businesses in India that work in a more digitalized economy should be more sensitive about vulnerability management to safeguard their resources and retain customer confidence.
A modern multiple-level approach to the implementation of comprehensive prevention strategies should be based on the combination of technology, processes, and human factors. Frequent network vulnerability assessment scans, well-designed access controls, constant monitoring, and training of employees are the key elements of good cybersecurity.
Cyber security vulnerability assessment services are professional services that organizations should invest in. Deploying advanced network vulnerability scanning tools enables organizations to stay ahead of changing threats. The expenses associated with proactive security measures are relatively low compared to the potential consequences of successful cyberattacks.
Download Our Penetration Testing Report to understand how comprehensive security assessments can help identify and address vulnerabilities in your network infrastructure.
Protecting the network against cyber threats requires implementing measures through consistency and professional knowledge. Leveraging the expertise of a highly qualified cybersecurity team will assist your business in creating very effective solutions to network security issues to support and protect critical business resources.
Schedule a Free Consultation with Qualysec’s security experts to evaluate your existing vulnerability management program and establish a personalized security plan to fit your organization.
Latest Penetration Testing Report

FAQ
1. What is a vulnerability in network security?
A vulnerability in network security refers to a weakness or flaw in the security of a network infrastructure, software, or process, which could lead to unauthorized access, causing network damage or destruction. These vulnerabilities may be in hardware devices, software applications, or even human processes; regular network vulnerability assessment should help identify and address these vulnerabilities.
2. What causes vulnerabilities in network security?
The reasons attributed to Network security vulnerabilities include outdated software, improperly configured systems, weak passwords, and inadequate security controls. Amid these security weaknesses, human errors, security awareness failure, and failure to establish proper cyber security vulnerability assessment procedures also play a role.
3. What are the most common types of network security vulnerabilities?
The most common types include software vulnerabilities from unpatched systems, hardware vulnerabilities from misconfigured devices, and human-based vulnerabilities from social engineering attacks. Organizations should utilize network vulnerability scanning tools and conduct regular vulnerability assessments in cybersecurity to identify common security gaps.
4. How do vulnerabilities impact network security?
Network security vulnerabilities can lead to data breaches, financial losses, operational disruptions, and regulatory compliance issues. They provide entry points for cybercriminals to access sensitive information, install malware, or disrupt business operations, making regular network security scanner deployment essential for protection.





















































































































































































































































































































































































































































































































































































































0 Comments