Most people envision hackers breaching firewalls with a single line of code in the field of cybersecurity. But what if you get to know that the simplest means for a cybercriminal to get your password is by manipulating you and making you give it away yourself, rather than by breaking your system? Social engineering in security has tremendous strength and is among the fastest-growing threat techniques globally.
This blog will examine several types of social engineering in threats, discuss how to stop them, and demonstrate why companies have to act proactively before it is too late. Let’s dive deep into the details.
What is Social Engineering?
Social engineering feeds on psychology, trust, and human error, unlike conventional cyberthreats that focus on technology. Furthermore, these threats can be far more destructive than malware or brute force hacking. The National Cyber Security Centre (NCSC) has frequently advised in the UK that social engineering is among the most frequent attack strategies aiming at both people and companies.
Social engineering in cyber security is the skill of persuading people to engage in actions that endanger security or to reveal secret information. Hackers use interest, terror, urgency, or even helpfulness instead of attempting to break down digital barriers.
Imagine getting a call from someone purportedly representing “IT support” who desperately needs your login information to resolve a network problem. Or, getting an email purportedly sent from your bank requesting account verification. These are intentionally set mental traps, not by chance. The danger is found in the genuine nature of these strikes. Although firewalls penetration testing, and antivirus software can stop viruses, they cannot obstruct human confidence.
Social Engineering Attack Life Cycle
Setting the Stage – The attacker studies their target and quietly prepares the setup to make the trick believable.
Getting the First Foot In – They cleverly trick the victim into sharing a small piece of information or taking a seemingly harmless action.
Gathering Secrets Slowly – Over time, they collect sensitive details without the victim even realizing it.
Leaving Without a Trace – Finally, they exit the interaction carefully to avoid raising any suspicion.
Explore more: What is Cyber Security Testing and its Different Types?
Social Engineering Attack Techniques
Let’s understand different social engineering attack techniques:
1. Baiting
Baiting appeals to curiosity and greed. For example, leaving an infected USB drive in an office parking lot labeled “Confidential Data”. Malware infests the system when an unaware worker connects it to their computer. Digital equivalents of baiting also exist; these could be free downloads, fraudulent giveaways, or pirated programs laced with malicious code.
We find the weak spots and fix them fast. Qualysec, your ongoing penetration testing partner.
2. Scareware
We have all come across those pop-ups, “Your PC is infected! Download this antivirus right away.” Using terror and urgency, scareware drives consumers into paying for bogus fixes or downloading malicious software. Victims think they are defending themselves; they are inviting predators.
3. Pretexting
Pretexting is fundamentally about storytelling. To get sensitive information, hackers create a persuasive narrative known as a “pretext.” For instance, someone might call pretending to be from HR, demanding employee records, or from a bank seeking account verification. Through the creation of a credible story, they gain the confidence of their victims.
Don’t let phishing, vishing, or other social engineering techniques put your company at risk—contact us now.
4. Phishing
Phishing, the most often used social engineering technique, entails mass emails or text messages camouflaged as real communication. These sometimes have dangerous links or attachments intended to steal credentials.
For example, a phishing email might request you to “confirm your address” through a phony website, appearing to be from a delivery firm. One click can allow hackers complete access to your accounts.
5. Spear Phishing
In spear phishing, hackers examine their targets thoroughly, then create emails to seem very real. Spear phishing emails could be addressed to you by name, reference to your job, or mimic a colleague’s writing style. One hacked executive account can cost millions, making companies particularly exposed.
Turn your team into your strongest security asset — train them to spot and stop phishing with Qualysec.
Latest Penetration Testing Report

10 Ways Businesses Can Prevent Social Engineering Threats
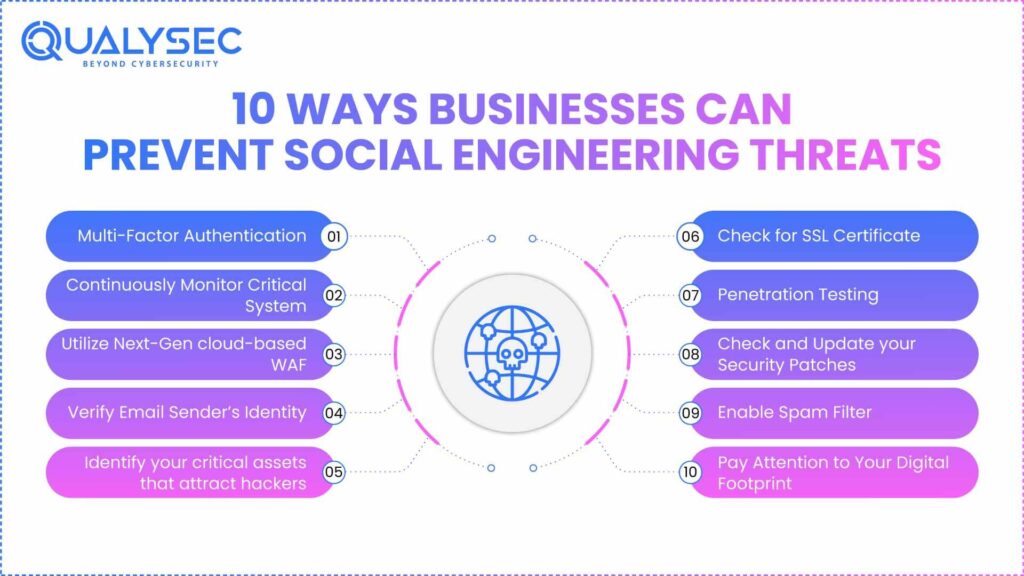
Below are the top 10 ways businesses can prevent social engineering threats:
1. Multi-Factor Authentication
Rely on only one factor; the most fundamental preventative action assures your account security. The password guarantees security naturally, but we have to check that they alone are insufficient. Because another person may simply guess your password and get access to your accounts.
Social engineering allows one to access the passwords. MultiFactor verification—which could be biometric access, security questions, or an OTP code is required.
2. Continuously Monitor Critical System
Ensure that your 24/7 system holding sensitive data is under surveillance. Some exploiting techniques, such as Trojans, rely on the system, therefore making it vulnerable. Web application scanning lets you identify flaws in your system by looking at both external and internal systems.
You should also conduct a social engineering campaign at least once a year to evaluate if your staff would be taken in by the threats of social engineering. Once monitored, fake domains can be immediately deleted to prevent copyright violations online.
3. Utilize Next-Gen cloud-based WAF
Although you already use a firewall inside your company, a next-generation web application cloud-based firewall is meant to provide the maximum protection against social engineering strikes. The web WAF differs greatly from the conventional WAF that most businesses use.
Specifically, AppTrana can monitor a web application penetration testing or website for suspicious activity or misuse regularly. Though human errors fuel social engineering threats, they will prevent threats and notify you of any attempted malware downloads. One of the finest methods to stop any possible infiltration and social engineering assaults is to use a risk-based WAF.
Read also: What is Cloud Web Security? A Brief Guide for Modern Business
4. Verify Email Sender’s Identity
Most hoaxes include pretending as a trusted organization to wrongly get the victim’s information. Particularly in a phishing attack, hackers send email messages that could seem to be from a sender you trust, such as a credit card company, a bank, a social networking site, or an internet store. Often, the emails relate a story to entice you to click on the deceptive link, which appears real.
Contact the alleged sender of the email to verify whether he sent the email or not to prevent this form of social engineering threats. Just remember, genuine banks won’t solicit your permitted credentials or sensitive information via email.
Must Read: Cybersecurity Risk Assessment: Key Steps and How to Perform
5. Identify your critical assets that attract hackers
From the point of view of Jim O’Gorman, a member of SocialEngineer.org, “When a lot of firms concentrate on safeguarding their assets, they are very focused on that”.
That is not necessarily the way a hacker will attack your company. They always strike the assets they deem to be important. Given the assets beyond your product, service, or intellectual property, you should assess from the viewpoint of the hacker to see what to safeguard.
6. Check for SSL Certificate
Data, emails, and correspondence encrypted guarantee that even if hackers intercept your communication, they cannot access the information included inside. Obtaining website Security Audit (SSL certificates) from reputable agencies will help one achieve this.
Always also double-check the site requesting your details. Check the URLs to confirm the legitimacy of the website. URLs beginning with https:// are regarded as safe and encrypted websites. Websites that include http:// are not providing a secure connection.
7. Penetration Testing
Among the methods to stop social engineering threats, performing vulnerability assessment and penetration testing to discover and trying to fix the vulnerabilities in your company is the most effective one.
If your pentester successfully breaches your vital system, you can determine the types of social engineering threats you may be prone to as well as which system or personnel you need to focus on safeguarding.
Discover how Penetration Testing as a service (PTaaS) can keep your business a step ahead of cyber threats, Explore our solutions today.
8. Check and Update your Security Patches
Usually searching for flaws in your application, software, or systems, cybercriminals aim to get illegal access to your data. Always maintain your security patches up to date as a preventative measure; also, keep your web browsers and systems updated with the latest versions.
Hence, companies release security patches as a response whenever they find vulnerabilities. Maintaining your systems with the recent release will help to create a cyber-resilient environment in addition to lowering the chances of cyber threats.
9. Enable Spam Filter
Turn on spam filters and shut the door for security social engineering threat offenders. Your inboxes are shielded from social engineering threats due to the essential assistance spam filters provide.
Most email providers offer spam filters that hold emails thought to be dubious. With spam capabilities, you can quickly classify emails and liberate yourself from the terrible chore of detecting distrustful messages.
10. Pay Attention to Your Digital Footprint
Oversharing of personal information online through social media gives these crooks more materials to work with. For instance, keeping your CV online calls for deleting your birthdate, phone number, and residential address. For hackers organizing a social engineering threat, all of this information helps. We suggest you set your social media to “friends only” and consider twice before posting anything on social media.
Also Read: Understanding 6 Types of Cloud Security Breaches in 2025
Conclusion
Social engineering in security is still one of the most significant security threats to today’s businesses, using a business’s reliance on human trust rather than vulnerabilities in technology. Strong awareness, proactive measures, and continual testing of employee understanding and awareness are essential to reducing risk.
Chat with Qualysec AI Chatbot Now! Get instant answers, security insights, and expert guidance for website security anytime.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
FAQ
1. What is an example of social engineering in security?
An example of cyber security social engineering is impersonating IT support. A hacker calls staff to ask for login credentials while citing urgent system maintenance. Users are misled into divulging sensitive information, therefore jeopardizing system security.
2. What are the five concepts of social engineering?
Authority, urgency, scarcity, familiarity, and social proof are the five concepts of social engineering. These psychological strategies use human behavior to persuade victims to divulge secret information or grant authorization.
3. What are the four types of social engineering?
Phishing (emails), pretexting (created scenarios), baiting (inviting offers), and tailgating (unauthorised physical access) are the four common types of social engineering. Every approach subtly deceives consumers into compromising security.
4. How much social engineering is involved in cybersecurity?
With more than 90% of cyberthreats involving human error, social engineering is a primary contributor. Often, hackers use trust and manipulation instead of only technical vulnerabilities.
Have a concern about phishing or cyber threats? Our team’s here to help – Reach out now .





















































































































































































































































































































































































































































































































































































































0 Comments