Have you ever thought to yourself, “Could my industrial control systems be exploited by hackers using just a few keystrokes?” You aren’t overthinking because many similar infrastructures in 2021 experienced over 1,600 security incidents worldwide. SCADA penetration testing isn’t just a cybersecurity industry buzzword; it can mean the difference between secure operations and massive failures for different industrial facilities.
This blog will take you through everything you need to know in relation to SCADA pentesting, from methodology to implementation.
Understanding SCADA Systems
Definition and Components of SCADA
SCADA is an acronym that stands for Supervisory Control and Data Acquisition. It is the nervous system for industrial operations. It is what allows operators to manage and monitor equipment in radically different geographic locations from a single room.
A typical SCADA system contains the following key components:
- Human-Machine Interface (HMI): The information manual that operators use to see what’s happening to and make modifications to the operation.
- Remote Terminal Units (RTUs): Devices that interface with sensors and translate the sensors’ output to digital form.
- Master Terminal Unit (MTU): The CNS, or brain, of the system, processes all of the information.
- Historians: Databases that store long-term operational data for later analysis.
SCADA systems collect thousands of data points in real-time. When a deviation occurs, SCADA alerts the operator immediately. SCADA can also take action based on the deviation with no human involvement.
Protect Your SCADA systems – Learn How Penetration Testing Helps.
Important Industries Using SCADA
SCADA systems are the backbone of our critical infrastructure. The energy sector relies heavily upon SCADA, from generation to transmission and delivery. SCADA threats to power grids and delivery systems can have a huge impact; one wrong move in a power grid SCADA system can result in millions of people being plunged into darkness. Other essential sectors using SCADA include:
- Oil and gas (wells, pipelines, oil refineries, and oil facilities).
- Transportation (traffic systems and railways).
- Building automation (HVAC systems and security management systems).
- Telecommunications.
Evolution of SCADA Architecture
SCADA has evolved a great deal since the days of simple monitoring. First-generation SCADA systems were entirely isolated, as ‘islands of automation,’ with proprietary hardware and software. Security was built in because they were physically disconnected from everything else.
Second-generation SCADA systems were robust, reliable, and functional; however, they began to network with other systems while still using proprietary protocols. This wider network allowed limited data sharing between systems.
Third-generation SCADA systems were gradually moving towards standard networking and protocols with Ethernet and TCP/IP. This was an improvement in functionality over the previous systems but expanded vulnerability, as many of the systems were opened to external connectivity and significantly lacked modern security designs.
The fourth-generation systems available today include cloud computing, cloud-oriented technologies, IoT, and wireless technologies. They provide unprecedented flexibility and accessibility, and accept security risks that SCADA developers never intended or designed for.
Read Also: Top Cloud Computing Vulnerabilities & How to Address Them?
Qualysec’s cloud pentest gives you results—no endless emails, no digging through PDFs, no guesswork.

Security Challenges in Modern SCADA Environments
Modern SCADA systems are likely facing security threats that their developers never considered possible. One major issue is that many SCADA devices were designed decades ago without even the thought of computer or internet security. They were designed for reliable function only, not to withstand active cybersecurity attacks.
Once these legacy systems are tied into modern networks, just like tearing down the walls of a fortress, devices and systems that were once disconnected from the outside world are now deliberately exposed and unsecured.
Some other major security threats and exposures today are:
- IT/OT Convergence: The integration of traditional information technology with operational technology will lead to security splits in the organization.
- Supply Chain Security: Hardware or software that is compromised before you receive it will have backdoor access to your systems.
- Patch limitations: Many systems cannot be updated easily because they may interfere with critical operations.
- Weak authentication: Weak passwords and shared accounts are common attributes across the landscape.
- Increasing attack surface: Increasing connection points increases the attack surface.
The stakes are high; a successful attack on SCADA systems could cause physical damage and loss of life or environmental disasters.
Also, Check out: Application Penetration Testing: A Complete Guide in 2025
The Need for SCADA Penetration Testing
1. Growing Cyber Threats to Industrial Control Systems
SCADA systems used to be completely isolated from the internet. Those days are long gone. Now these critical systems are connected to corporate networks, remote access points, and yes – the internet. This connectivity creates a massive attack surface for hackers to exploit. The stats are alarming.
2. Potential Consequences of SCADA Breaches
The results of a SCADA intrusion are physical and perhaps catastrophic, not just digital: Think of a hacker interfering with the mixing procedures of a chemical facility or turning off safety mechanisms.
- Environmental disasters: Oil pipeline restrictions broken? Consider great pours
- Economic harm: Lines stopped, supply chains broken, millions lost per hour.
- Critical service outages: Transportation mayhem, tainted water supplies, power outages
SCADA attacks may physically destroy hardware, jeopardize people, and bring crucial services to a standstill—unlike conventional IT breaches, which target data.
3. Regulatory Requirements and Compliance Standards
The regulatory landscape around SCADA security keeps getting stricter:
- NERC CIP: Mandatory for power utilities with penalties up to $1M per violation per day
- IEC 62443: International standards specifically for industrial automation
- NIST SP 800-82: Guidelines for securing industrial control systems
- Industry-specific regulations: Water (AWWA), oil/gas (API 1164), transportation (TSA)
Regular penetration testing isn’t just smart business – it’s increasingly required by law.
Ensure Compliance with Industry Standards – Explore Full Compliance Requirements
4. Risk Management Benefits
Pentest SCADA delivers ROI:
- Vulnerability prioritization: Find what matters most instead of chasing every possible vulnerability.
- Defense-in-depth validation: Test if your layered security works.
- Security investment guidance: Know exactly where to spend your limited security budget.
- Incident response readiness: Practice makes perfect before a real attack happens.
Download our Sample Penetration Testing Report to understand how vulnerabilities are reported and mitigated.
Latest Penetration Testing Report

Real-world SCADA Attack Examples
Nothing drives home the importance of SCADA security like real incidents:
- Stuxnet (2010): The game-changer that damaged Iranian nuclear centrifuges by manipulating their PLCs
- Ukrainian Power Grid (2015/2016): First successful attack on power infrastructure, leaving 230,000 people without electricity
- Oldsmar Water Treatment Facility (2021): Attacker attempted to increase sodium hydroxide to dangerous levels in Florida’s drinking water
- Colonial Pipeline (2021): Ransomware attack shut down the largest fuel pipeline in the US, causing fuel shortages across the East Coast
The question isn’t if your SCADA systems will be targeted, but when. Penetration testing is your best defense against becoming the next cautionary tale.
SCADA Penetration Testing Methodology
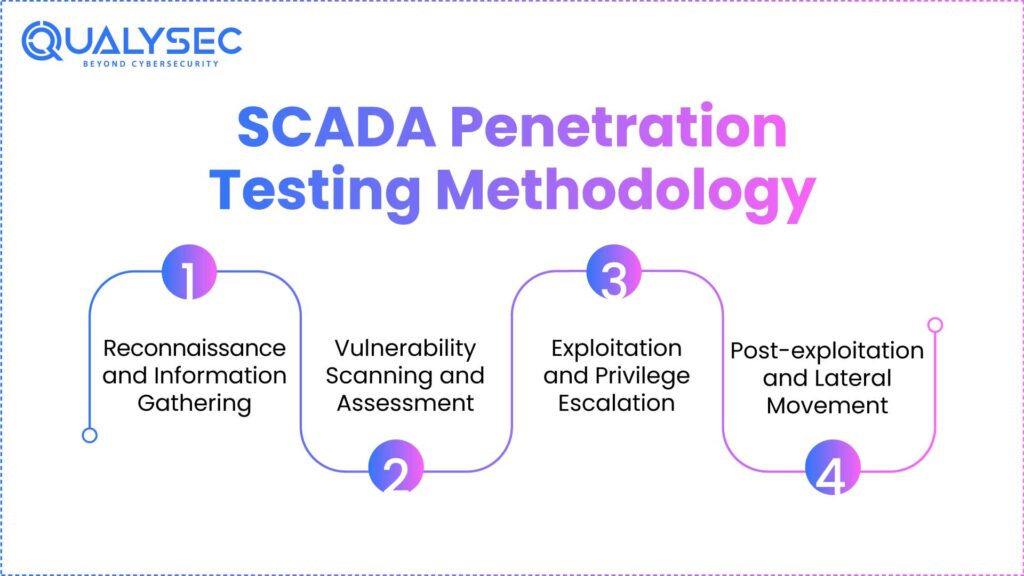
Below is a step-by-step guide on SCADA penetration testing methodology:
1. Reconnaissance and Information Gathering
What is the first step in any SCADA penetration test? Know what you’re dealing with. Think of it as casing a building before you try to find a way in. You need to map out the entire industrial control system landscape – what controllers are running, which networks they’re on, and how everything talks to each other.
Start by identifying all SCADA components – HMIs, PLCs, RTUs, historians, and engineering workstations. Passive recon works wonders here. Look for things like:
- Network traffic patterns
- Device communications
- Protocol usage (Modbus, DNP3, Profinet)
- System documentation (often a goldmine)
You’d be shocked at how much info is publicly available. Critical information on target systems can be found in vendor documents, LinkedIn profiles of engineers, and even maintenance manuals.
2. Vulnerability Scanning and Assessment
Once you’ve mapped everything out, it’s time to look for the vulnerabilities. But here’s the catch with SCADA systems – you can’t just run Nessus and call it a day. These environments are super sensitive, and standard scanning tools might crash critical processes.
Instead, you need specialized tools designed for industrial systems:
| Tool Type | Common Examples | Best Used For |
| Protocol-specific | Redpoint, CyberX | Identifying protocol vulnerabilities |
| Passive scanners | Claroty, Nozomi | Non-disruptive discovery |
| Configuration analyzers | PLCScan, Axiom | Finding misconfigurations |
Focus on these common vulnerability areas:
- Default credentials
- Unpatched firmware
- Insecure protocols
- Missing authentication
- Weak encryption
Recommended: What Is Vulnerability Scanning? and Vulnerability Assessment
3. Exploitation and Privilege Escalation
This is where things get real. With your vulnerability map in hand, it’s time to see if you can break in.
The goal isn’t just getting in – it’s gaining control. In SCADA environments, this could mean:
- Manipulating controller logic
- Altering setpoints
- Injecting false commands
- Disrupting communications
Most SCADA systems weren’t built with security in mind, so once you’re in, privilege escalation is often surprisingly easy. Common paths include:
- Jumping from IT to OT networks
- Exploiting trusted relationships between components
- Using captured credentials across multiple systems
Remember to document everything meticulously. Screenshots, logs, and command history are your evidence.
4. Post-exploitation and Lateral Movement
You’re in. Now what?
This phase is about seeing how far you can go. Can you pivot {status”: false, “data”: null, “message”:” Exception::__construct(): Argument #1 ($message) must be of type string, array given”, “type: “error”, “code”:50,” response “: “error”}
Secure your critical infrastructure today—partner with Qualysec for expert SCADA penetration testing tailored to your industrial systems.
Our experts at Qualysec have helped secure fintech, SaaS, and enterprise systems across 25+ countries. Manual + Automated Pentesting. No false positives. Actionable reports.

Tools and Techniques for SCADA Penetration Testing
Let’s discuss the SCADA pentesting tools:
1. Specialized SCADA Testing Tools
You need specialized tools designed for industrial control environments. Tools like Redpoint, SCADAhacker, and PLCscan are built specifically for SCADA systems. They understand industrial protocols and won’t accidentally trip critical processes.
2. Protocol-specific Testing Approaches
SCADA systems use protocols that would make regular network admins scratch their heads. Modbus, DNP3, and IEC-61850 – these aren’t your everyday TCP/IP. Each protocol needs its testing approach:
| Protocol | Testing Approach | Key Consideration |
| Modbus | Function code manipulation | Watch for undocumented codes |
| DNP3 | Protocol-aware fuzzing | Test authentication bypass |
| IEC-61850 | MMS message manipulation | Avoid triggering protection mechanisms |
The trick with protocol testing is knowing exactly how these systems communicate. A single malformed packet can either reveal a critical SCADA system vulnerabilities or shut down a power grid. Big difference.
Safe Testing Practices for Critical Infrastructure
SCADA systems control real things – water supplies, power grids, and manufacturing lines. Crash a website? No big deal. Crash a power plant? Always:
- Test during maintenance windows when possible
- Have emergency rollback procedures ready.
- Keep operators in the loop during testing.
- Use traffic mirroring instead of direct interaction.
- Document every single test and result meticulously.
One wrong move can turn off the lights for thousands of people. No pressure!
Simulation and Testing Environments
Building a realistic test environment is worth its weight in gold. You can’t just spin up a virtual machine and call it a day.
The most effective SCADA testing environments include:
- Hardware-in-the-loop simulations with actual PLCs and RTUs
- Digital twins of production environments
- Isolated networks that mirror production topologies
- Process simulation software to emulate industrial processes
Tools like the Idaho National Laboratory’s SCADA Test Bed provide comprehensive environments for testing without risk to operational systems.
A completely segregated physical environment with the same hardware, software, and configurations as the production system. Expensive? Yes. Is it worth it when testing critical infrastructure? Absolutely.
Also Read: What is an Api Security Solution?
Overcoming SCADA Testing Challenges
1. Testing Without Disrupting Operations
SCADA systems are the backbone of critical infrastructure. You can’t just unplug them to run tests. Schedule testing during maintenance windows. If those don’t exist, use staged testing approaches where you test components in isolation.
Virtual environments are your best friend here. Create digital twins of the production environment where you can safely simulate attacks without touching operational systems.
And for heaven’s sake, have a rollback plan for everything. If something goes sideways, you need to restore normal operations ASAP.
2. Dealing with Proprietary Systems
SCADA vendors love their secret sauce. Proprietary protocols, closed systems, zero documentation. When you’re facing black-box systems, start by monitoring network traffic. Tools like Wireshark can help identify patterns even in proprietary protocols.
Build a test lab if possible. Having a miniature version of the system lets you poke and prod safely. Vendor cooperation makes life easier, but don’t count on it. Some will help; others will threaten lawsuits if you even look at their systems funny.
3. Air-gapped Network Testing Strategies
Air gaps aren’t as gappy as people think. Test the transfer mechanisms. USB drives, maintenance laptops, and vendor updates are all potential infection vectors. Use authorized media transfer protocols to simulate attacks. Document how malware could potentially cross the air gap through approved channels.
4. Legacy System Security Assessment
Those 30-year-old PLCs weren’t built with security in mind. They were designed when the internet was barely a thing. Focus on compensating controls. If you can’t secure the legacy device itself, secure everything around it. Network segmentation, monitoring, and access controls become critical.
Document known vulnerabilities thoroughly. Just because you can’t patch doesn’t mean you can’t mitigate. And remember – replacing legacy systems isn’t always an option. Some of these systems control billion-dollar infrastructure with decades-long life cycles.
Don’t wait for a breach. Contact Qualysec now to identify and eliminate vulnerabilities in your SCADA environment with proven testing methodologies.
Conclusion
SCADA pеnеtration tеsting providеs a critical layеr of sеcurity for industrial control systеms that powеr our critical infrastructurе. By systеmatically idеntifying vulnеrabilitiеs through propеr mеthodology, tеsting kеy arеas likе communication protocols and fiеld dеvicеs, and еmploying spеcializеd tools, organizations can protеct thеsе vital systеms from incrеasingly sophisticatеd cybеr thrеats.
Partnеr with Qualysеc’s еxpеrt sеcurity tеam to conduct comprеhеnsivе SCADA pеnеtration tеsting and safеguard your ICS еnvironmеnt from еvolving risks.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
FAQ
1. What is SCADA penetration testing?
SCADA VAPT is a means of simulating cyberattacks to expose vulnerabilities in communication protocols, devices, and network design. SCADA security testing is the evaluation of the security of Supervisory Control and Data Acquisition systems.
2. What reasons should businesses have for SCADA testing?
Critical industrial processes are under the control of SCADA systems. Testing guarantees continuous service, safety, and protection against data breaches or physical disturbances by identifying security flaws that attackers could use.
3. What Tools are used in SCADA penetration testing
OT SCADA penetration testing– Traffic analysis, exploitation of flaws, and system resilience testing under simulated attack situations are accomplished using specialized tools like Wireshark, Metasploit, and SCADA-specific simulators.
4. How frequently should SCADA systems be evaluated?
To ensure security measures remain current and effective, we should test SCADA systems at least once a year or following significant policy changes, network modifications, or updates.
Have any questions? Feel free to ask now—our cybersecurity experts are here to help.





















































































































































































































































































































































































































































































































































































































0 Comments