FedRAMP penetration testing is a specialized security evaluation process that tests the security posture of cloud service providers seeking to serve the U.S. federal government. Such a comprehensive approach to testing makes cloud systems resistant to advanced cyber threats, capable of protecting detailed and sensitive information of the government. Familiarity with FedRAMP penetration testing requirements is essential for every organization seeking to acquire federal authorization and maintain continuous compliance with a set of rigorous security requirements.
What Is FedRAMP?
FedRAMP includes a government-wide initiative of the U.S. government capable of providing a standard approach to evaluate security, authorization as well as continuous monitoring of cloud products and services. The FedRAMP penetration testing is a significant factor that was proposed in 2011 by the Office of Management and Budget through its Cloud-First Policy which is used to evaluate the cloud service providers (CSPs) before being issued the permission to perform their services to the federal agencies.
The concept behind FedRAMP is to do it once and use it many times, allowing multiple federal agencies to utilize the authorization obtained by cloud service providers. The program adheres to the National Institute of Standards and Technology (NIST) guidelines to implement an aligned approach for mitigating various risks and computer threats.
There are three impact levels within the program, and they are categorized as cloud systems:
- Low Impact: Negative impact is low in case of loss of availability, integrity, or confidentiality
- Moderate Impact: Significant negative consequences on the functioning of organisations, organisation property, or actual people
- High Impact: Serious negative consequences to the organisational functions, property, or the people
What Is FedRAMP Penetration Testing?
FedRAMP penetration testing is a highly technical evaluation of security that explicitly addresses the high requirements of a federal cloud security framework. Unlike customary commercial penetration tests, FedRAMP cloud penetration testing comes with guidelines that must be followed as dictated by the FedRAMP Program Management Office (PMO).
The aspects that make FedRAMP penetration testing unique are:
- Mandatory Attack Vectors: Six particular attack vectors that are required to be tested on all authorised systems
- Testing in Production Environments: The testing should all be done on the production environments (not the staging or development systems)
- Third Party Assessment Organisation (3PAO) Requirement: Reimbursement of the 3PAOs is mandated to be performed by accredited third-party assessment organisations (3PAOs)
- NIST Alignment: The testing approach should be NIST SP 800-53, congruent with security controls
- Continuous Monitoring: Ongoing Requirements During Yearly Tests
The FedRamp pen testing differs from commercial testing in several significant aspects:
| Aspect | Commercial Pentest | FedRAMP Penetration Testing |
| Environment | Often test/staging | Production-only testing required |
| Methodology | Flexible approach | Rigid, PMO-defined framework |
| Reporting | Variable formats | Strict Security Assessment Report (SAR) structure |
| Frequency | Point-in-time | Annual requirement with continuous monitoring |
| Assessor | Any qualified vendor | Must use an accredited 3PAO |
Ensure FedRAMP compliance — schedule your penetration test today and download a real sample report to see expert insights in action.
Latest Penetration Testing Report

FedRAMP Penetration Testing Requirements
The FedRamp penetration test guidance establishes comprehensive requirements that cloud service providers must meet to achieve and maintain federal authorization. These requirements are based on the NIST SP 800-53 security controls framework and include specific testing methodologies for various threat scenarios.
Six Mandatory Attack Vectors
FedRAMP penetration testing requires evaluation of six specific attack vectors for all authorized systems:
1. External to Corporate (Phishing)
- Social engineering attacks targeting system administrators and managing personnel
- Phishing campaigns must bypass all technical controls to test user response
- Landing pages should identify phishing attempts and provide security awareness information
- Sampling approaches are acceptable for organisations with large employee bases
2. External to CSP Target System
- Attacks of an Internet form trying to gain unauthorised access to the FedRAMP boundary
- All external endpoints, management interfaces and administration access are tested.
- During test, security controls like web application firewalls have to be bypassed.
- Manual testing and vulnerability scanning of all internet facing assets
3. Tenant to CSP Management System
- Application penetration testing attempts to access management systems
- Testing for privilege escalation from customer accounts to administrative systems
- Evaluation of multi-tenancy security controls and isolation mechanisms
- Assessment of APIs, web applications, and management interfaces
4. Tenant-to-Tenant
- Testing for data isolation between different customer tenants
- Attempts to access one tenant’s data from another tenant’s account
- Evaluation of authentication, authorization, and session management controls
- Cross-tenant vulnerability assessment and exploitation attempts
5. Mobile Application to Target System
- Security assessment of mobile applications and their backend systems
- Testing for insecure data storage, weak encryption, and authentication bypasses
- Evaluation of mobile-specific attack vectors and vulnerabilities
- Assessment of mobile application programming interfaces (APIs)
6. Client-Side Application and/or Agents to Target System
- Security testing of client-side software, browser extensions, and agents
- Evaluation of thick clients, appliances, and endpoint software
- Assessment of software installation and update mechanisms
- Testing for local privilege escalation and data exposure
Documentation Requirements
FedRAMP-compliant cloud pen test operations have to be systematically reported in several key files:
- System Security Plan (SSP): Describes implemented security controls in place
- Security Assessment Report (SAR): A Testament to what the tests found
- Plan of Action and Milestones (POA&M): Monitors known weaknesses and responds to fix them
- Rules of Engagement (ROE): Specifications of constraints, parameters of testing, and techniques.
The FedRAMP Penetration Testing Process
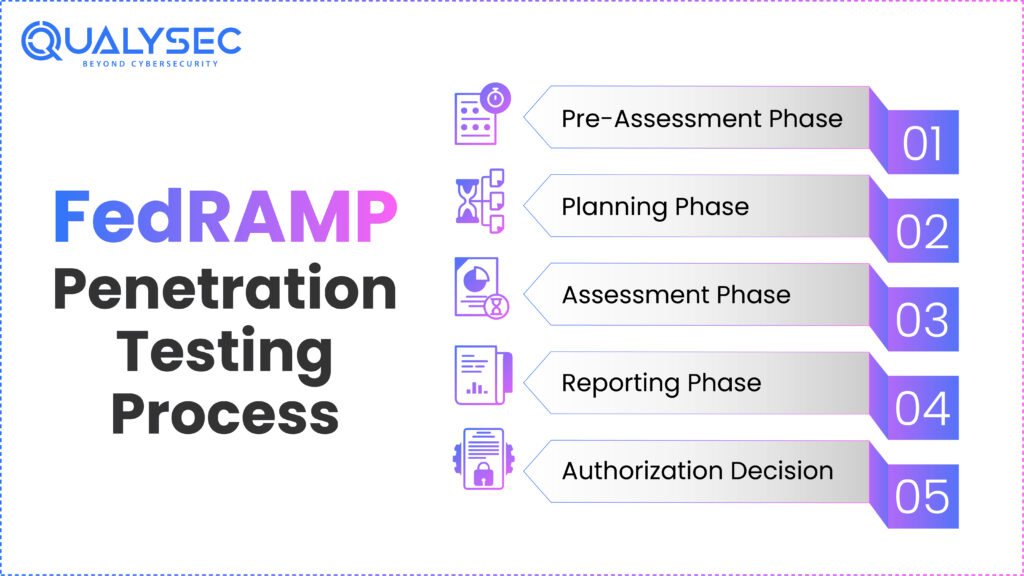
The FedRAMP penetration test process is systematic and intended to be inclusive in security assessments, aiming to cause minimal interruption to production systems. This procedure typically takes several months and must be well-coordinated among the cloud service provider, the 3 PAO, and the sponsoring agency.
Pre-Assessment Phase
The process begins with a comprehensive pre-assessment review where the 3PAO evaluates the CSP’s readiness for formal testing. Key activities include:
- Review of the System Security Plan and supporting documentation
- Evaluation of implemented security controls
- Assessment of authorisation boundary definitions
- Identification of testing scope and constraints
- Development of preliminary testing strategies
Planning Phase
During the planning phase, detailed preparation ensures successful test execution:
- Information Request List (IRL) Response: CSPs provide detailed evidence of security control implementation
- Authority to Test (ATT) Submission: Formal authorization for penetration testing activities
- Security Assessment Plan (SAP) Development: Comprehensive testing methodology and timeline
- Rules of Engagement Finalization: Detailed testing parameters and constraints
Assessment Phase
The assessment stage makes up the essential spot of testing when real FedRamp testing scanning and penetration tests are to be performed:
- Evidence Review: Examination of implementation of security control in details
- Vulnerability Assessment: thorough scanning of all in scope systems
- Penetration Testing: The Active exploitation attempts on all the six attack vectors
- Draft Risk Exposure Table (RET): Early-stage of assessments and risks
- Remediation Period:The time that CSPs are to mitigate recognized weaknesses
Reporting Phase
The final phase focuses on comprehensive documentation and report preparation:
- Draft Security Assessment Report: Initial findings and recommendations
- CSP Review and Response: Opportunity for clarification and additional evidence
- Final SAR Preparation: Comprehensive security assessment documentation
- Sponsor Review: Authorizing official evaluation of testing results
Authorization Decision
The sponsoring agency looks through all the documents and makes the final decision of authorization:
- Authority to Operate (ATO) Decision: Formal authorisation or conditional approval
- FedRAMP Marketplace Listing: Public recognition of authorised status
- Continuous Monitoring Requirements: Ongoing compliance obligations
Request a customized quote today and get expert insights on securing your cloud environment for federal compliance.
Qualysec’s cloud pentest gives you results—no endless emails, no digging through PDFs, no guesswork.

Common Challenges and Best Practices
FedRAMP penetration testing may involve several typical challenges that organizations face when attempting to gain authorization, which can lead to a failure to achieve penetration effectiveness. Learning about these challenges and making best practices is important in achieving compliance.
Common Challenges
Improper Scoping: A lot of organizations do not present proper definition of the boundary of the authorized area, which lead to poor tests. The correct scope definition guarantees that all the critical aspects are taken into consideration and the possible attack paths are revealed.
Poor Timing of Late Testing: Penetration testing should be part of the late phases of FedRAMP as early completion will cause very slow progress. During the testing, the high-severity vulnerabilities can be noted; such facts might affect the Security Assessment Report hence putting off the decisions authorization.
Stakeholder Resistance: Stakeholders, including the legal and IT team, will often have issues with penetration testing, as it will cause disruption and because they are afraid of liability. The issues can be addressed through early engagement and free exchange.
Methodological deficiencies: Some of the 3PAOs use a main practice of automated vulnerability analysis, which in turn might avoid the identifications of security gaps that comprise complexities that can only be identified by human skills.
Best Practices
Advance Planning and Co-ordination
- Make penetration testing planning activities early in the FedRAMP process
- Involve all stakeholders in the very onset
- Create proper communication lines between CSP and 3PAO
- Outline realistic schedules in a sufficient remediation buffer
Comprehensive Scope Definition
- Map all system components and dependencies
- Include all external interfaces and interconnections
- Document authorisation boundary decisions with justifications
- Consider future system changes in scope planning
Production Environment Testing
- Ensure production systems can withstand testing activities
- Implement appropriate monitoring during testing periods
- Plan for potential service disruptions and mitigation strategies
- Coordinate testing schedules with operational requirements
Effective Documentation Management
- Maintain detailed records of all testing activities
- Ensure documentation meets FedRAMP PMO requirements
- Implement version control for all assessment documents
- Plan for document review and approval processes
Take a look at Qualysec’s ratings and reviews on Clutch to see how we help businesses secure their cloud infrastructure. Book a free live consultation to learn more.
How to Prepare for a FedRAMP Penetration Test
Successful FedRamp penetration testing requires extensive preparation across multiple organizational areas. Cloud service providers should begin preparing months in advance of actual testing to ensure optimal outcomes.
Technical Preparation
System Hardening
- Apply all the necessary NIST 800-53 security measures
- Undertake internal vulnerability aud realistic remediation
- Make sure that all systems are properly patched and set up
- Verify security surveillance and logging functionality
Environment Readiness
- Verify production systems can handle testing activities
- Implement backup and recovery procedures
- Establish testing windows that minimize business impact
- Prepare emergency response procedures for critical findings
Access Provisioning
- Create appropriate test accounts for each attack vector
- Establish secure communication channels with the 3PAO team
- Prepare administrative access for testing scenarios
- Document all account privileges and limitations
Administrative Preparation
Documentation Assembly
- Complete System Security Plan with all required attachments
- Prepare evidence packages for all implemented controls
- Organize supporting documentation and policies
- Ensure all documents are current and accurate
Stakeholder Coordination
- Brief executive leadership on testing objectives and timelines
- Coordinate with the legal team on testing authorization and liability
- Align with IT operations on testing schedules and support
- Establish incident response procedures for critical findings
Resource Allocation
- Assign dedicated project team members for testing support
- Budget for potential remediation activities
- Plan for extended testing periods if issues are discovered
- Prepare for post-testing documentation and reporting requirements
Choosing the Right 3PAO for Penetration Testing
The third-party assessment organization should be chosen carefully to conduct the penetration testing for FedRAMP. The selection of 3PAO could have strong implications for the quality, schedule, and eventual success of its authorization.
Key Selection Criteria
FedRAMP Accreditation and Experience
- Verify current FedRAMP 3PAO accreditation status
- Review the track record of successful FedRAMP authorizations.
- Assess experience with similar cloud service offerings
- Evaluate understanding of your specific industry requirements
Technical Expertise and Methodology
- Assess penetration testing capabilities across all six attack vectors
- Review testing methodologies and tool capabilities
- Evaluate manual testing expertise beyond automated scanning
- Confirm understanding of NIST 800-53 security controls
Communication and Project Management
- Evaluate communication style and responsiveness
- Assess project management capabilities and experience
- Review client references and satisfaction ratings
- Confirm availability to meet your timeline requirements
Curious about the cost? View FedRAMP penetration testing pricing and get a clear breakdown tailored to your compliance needs.
Our experts at Qualysec have helped secure fintech, SaaS, and enterprise systems across 25+ countries. Manual + Automated Pentesting. No false positives. Actionable reports.

Why Qualysec Is the Best Organization for FedRAMP Penetration Testing?
QualySec is the best FedRAMP penetration testing service provider with the unrivaled experience and a full range of testing services that guarantee the successful federal authorization of products. Being a top cybersecurity company that focuses on government compliances, QualySec integrates in-depth expertise with extensive FedRAMP experience in order to provide top-quality results to cloud service providers.
1. Comprehensive Testing Expertise
The team of the Certified security professionals of QualySec has experience in all six, mandatory attack vectors of FedRAMP. Our pen testers are not limited to vulnerability scanning with automated tools, but our manual tests will bring to light complex vulnerability issues that were unnoticed by other pen testers. We use the best practices in testing techniques, adhering to the requirements of the NIST SP 800-53 guidelines, and use MITRE ATT&CK to cover the largest possible set of threats.
2. Proven FedRAMP Success Record
With a track record of successful FedRAMP authorizations across multiple impact levels, QualySec understands the nuances of federal compliance requirements. Our team has helped numerous cloud service providers achieve Low, Moderate, and High impact level authorizations, navigating complex technical and administrative challenges throughout the process.
3. Advanced Testing Methodologies
QualySec employs cutting-edge penetration testing techniques that simulate real-world attack scenarios. Our approach encompasses sophisticated adversary emulation, threat hunting capabilities, and the integration of continuous monitoring. We utilize industry-leading tools combined with manual expertise to identify vulnerabilities that automated scans cannot detect.
4. Exceptional Client Support and Communication
Our dedicated project management approach ensures clear communication throughout the testing process. We provide regular updates, detailed explanations of findings, and comprehensive remediation guidance that helps clients address vulnerabilities efficiently. Our technical debriefing sessions ensure a complete understanding of testing results and actionable next steps.
Services Offered:
- Complete FedRAMP penetration testing across all six attack vectors
- Pre-assessment readiness evaluations and gap analyses
- Continuous monitoring and annual testing support
- Vulnerability assessment and remediation guidance
- Security control validation and documentation support
Location: Qualysec maintains offices across all regions, with specialized teams dedicated to federal compliance requirements.
Make a free consultation with QualySec now to discuss your FedRAMP penetration testing needs and learn how our expertise can accelerate your path to federal authorization.
Conclusion
FedRAMP penetration testing represents a critical milestone in achieving federal cloud authorization, requiring specialized expertise, comprehensive planning, and meticulous execution. The evolving threat landscape and updated FedRAMP penetration test guidance require that cloud service providers collaborate with experienced 3PAOs who understand both the technical requirements and administrative complexities of federal compliance.
Success in FedRamp penetration testing depends on early preparation, stakeholder engagement, and selection of qualified assessment partners. Organizations that invest in proper preparation, implement comprehensive security controls, and work with experienced 3PAOs like QualySec are best positioned to achieve successful federal authorization and maintain ongoing compliance.
The investment in FedRAMP-compliant cloud pen test activities extends far beyond compliance requirements, providing valuable insights into security posture and helping organizations build resilient, secure cloud infrastructure capable of protecting sensitive government data against evolving cyber threats.
Talk with our experts today to learn how QualySec can support your FedRAMP penetration testing requirements and accelerate your path to federal authorization.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
FAQs
1. What is FedRAMP in cybersecurity?
FedRAMP (Federal Risk and Authorization Management Program) is a U.S. government-wide program that provides standardized security assessment, authorization, and continuous monitoring for cloud products and services. It ensures cloud service providers meet stringent security requirements before serving federal agencies.
2. Which NIST standard does FedRAMP follow?
FedRAMP follows NIST Special Publication 800-53, which provides a comprehensive catalog of security and privacy controls for federal information systems. The program also incorporates guidelines from NIST SP 800-115 for penetration testing methodologies.
3. What is the difference between FedRAMP and SOC?
FedRAMP is a mandatory government compliance framework for cloud service providers serving federal agencies, whereas SOC (Service Organization Control) is a voluntary auditing standard that focuses on service organization controls. FedRAMP has more stringent requirements and specific penetration testing mandates.
4. What are the key requirements to achieve FedRAMP compliance?
Key requirements include implementing NIST 800-53 security controls, undergoing assessment by an accredited Third-Party Assessment Organization (3PAO), completing comprehensive penetration testing across six attack vectors, maintaining continuous monitoring, and achieving Authority to Operate (ATO) from the sponsoring agency.
5. How much does FedRAMP penetration testing typically cost?
FedRAMP penetration testing costs typically range from $15,000 to $40,000, depending on the system’s complexity, scope, impact level, and the chosen 3PAO. Additional costs may include remediation activities, ongoing monitoring, and annual testing requirements.
Download our comprehensive FedRAMP Penetration Testing Guide for detailed insights into requirements, best practices, and preparation strategies that will help ensure your successful federal authorization journey.






















































































































































































































































































































































































































































































































































































































0 Comments