Global cyberattacks hit around 600 million per day in recent years, with organisational attacks rising 30-50% annually amid escalating cybercrime costs projected at $10.5 trillion yearly by 2025. India faced 265 million cyberattacks in 2025, alongside cyber fraud losses of Rs 22,845 crore ($2.7 billion) in 2024, up 206% from 2023. Chief Information Security Officers (CISOs) face a doubling of ransomware. The first line of defence is to protect the enterprise network. This guide covers the key concepts, including basic components and enterprise network security best practices. CISOs will receive practical tips to protect systems that are interrelated. Strategies that are data-driven can ensure that you eliminate vulnerabilities to network security and develop an effective enterprise network security design.
Time to reinforce your cybersecurity strategies? Contact Qualysec Technologies today to have an enterprise security assessment consultation!
Enterprise Network Security – Definitions
Enterprise network security architecture ensures that the wrong individuals or attacks do not exploit or misuse the networks of a company. Plans, tools, and rules allow CISOs to maintain the privacy, correctness, and availability of data. They guard against the transforming threats to devices like computers, servers, routers, and switches.
Core Definition and Scope – Multilayered Defence Strategies
Multilayered defence involves installing numerous layers of defence to prevent malware, phishing, ransomware, DoS attacks, and other threats. Businesses can operate effectively without breaching regulations like GDPR and the DPDP Act of India because of enterprise network security. CISOs consider the security of the enterprise network as the primary component of the general cybersecurity. They prioritise it so highly to maintain operations in dangerous circumstances.
Role of CISOs
CISOs are taught to apply the use of enterprise cybersecurity solutions in identifying threats before they occur. They employ techniques and procedures that detect intrusions in their early phases. This aids in minimising downtime and data security within the distributed networks.
The 4 Network Security Types
1. Firewalls
Firewalls intercept outgoing and incoming data on the network to determine whether they adhere to established guidelines. They prevent unauthorised access by preventing user entry and implementing rules effectively. The newer firewalls also go deeper into the applications in order to provide better protection.
2. Intrusion Prevention and Detection Systems (IDPS)
IDPS tools monitor traffic and are on the lookout for oddities. They alert the staff or prevent viruses immediately. Patterns and behaviour detection apply to detect problems in better units.
3. The Virtual Private Networks (VPNs)
VPNs encrypt to ensure the safety of remote connections. They use protocols like IPsec to secure the information transmitted over the Internet. Organisations are relying on VPNs to secure remote workers.
4. Access Control Systems
Multifactor authentication (MFA) and role-based access control (RBAC) are used in access control systems. They reduce the usage of sensitive resources to the correct individuals. These rules are even enhanced with the addition of zero-trust ideas.
Relevance of Enterprise Network Security
1. Impact of Breaches
Attacks show personal information and halt operations. In 2024, 92% of the Indian firms had network security issues. Proper enterprise network security prevents loss of money, damages reputation, and causes legal hassles.
2. Building Trust and Recovery
CISO reports indicate that good protection will make people have more confidence in the company. Enterprise network security, as provided by companies that have gone beyond it, can recover half as quickly as other companies. Indian companies that overlook this risk find it riskier with the emergence of state-backed attacks and intelligent ransomware.
3. Strategic Imperative
Indian CISOs encounter local threats like attacks on telecom companies. Enterprise network security enhances security against those threats. In a world where teams are increasingly committing cybercrimes annually, teams are getting harder to catch.
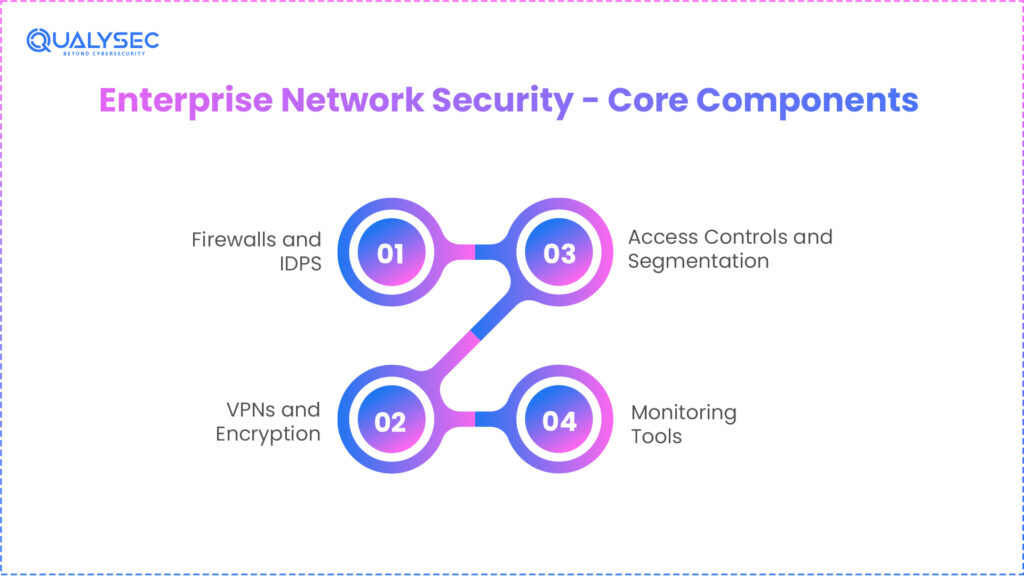
Enterprise Network Security – Core Components
The Foundations of Integrated Architecture
Connected parts create a deep enterprise network security architecture.
Firewalls and IDPS
Firewalls are very thorough in ensuring that they prevent attacks. The recent versions share threat information with the help of AI. Such patterns are IDPS spots and prevent weird patterns, and provide protection earlier.
VPNs and Encryption
VPNs create secure tunnels either by IPsec or by SSL/TLS. Encryption provides protection to data when transferred and when stored. Teams fully-chain and encrypt the entire network.
Access Controls and Segmentation
Role-based access and zero-trust rules scrutinise each request. Breaking the network into individual sections prevents the expansion of a breach. Even finer control is provided by the tiny segmentation of tricky setups.
Monitoring Tools
SIEM tools will gather logs in such a way that managers can view what is going on at any given time. They associate incidents in search of security issues before they become big. The identification of the threats becomes more specific with the help of behaviour analysis in SIEM.
CISOs place these components in a stack one by one to ensure that the defences are not supposed to be broken.
Enterprise Network Security Best Practices
Regular Testing and Updates
Teams put network security to the test frequently to learn the vulnerability in the shortest time possible. Least privilege and MFA are used everywhere in a very strict way.
Patching and Segmentation
CISOs provide fixes and patches in a short time. They divide the network to prevent the threat from spreading over an extended distance.
Training and Backups
Phishing is trained with a special simulation of workers. Data is stored elsewhere and encrypted so that it can be fast recovered.
Network Vulnerabilities in 2026
1. Emerging Threat Landscape
Hackers continue to operate with unpatched equipment and incorrect settings. In 2025, 85% of the companies experienced AI attacks, which sought network security vulnerabilities. The common issues were poor encryption and insider threats.
2. Advanced Persistent Threats
The concept of quantum computers threatens existing codes and demands new ones in a short amount of time. Supply-chain attacks increase 44% annually in India. CISOs look into the future with enterprise tests to be future-prospective.
3. Localised Indian Risks
India Govts attempt to strike critical systems. Teams that are constantly seeking weaknesses address these.
AI in Network Security
Transformative Detection Capabilities
AI alters the way threats are discovered. Machine learning identifies odd things that people overlook. When it comes to 2026, 65% of companies respond using AI.
Predictive Analytics Power
Tools that examine behaviour can predict attacks. AI in network security answers within seconds. CISOs deploy it in large scale for protection because cybercrime in India is soaring.
Scalability Benefits
AI does not get fatigued working on numerous networks. It adapts to emerging threats in time, with special flexibility.
Enterprise Security Assessment Essentials
Use of Systematic Gap Identification
Enterprise checks discover loopholes in a strategy. There is scanning and testing of teams.
Delivery of Actionable Insights
Someone conducts reviews on firewalls, logs and setups. They provide step-wise action plans in order to enhance network security. CISOs work on the most critical things first.
Testing Approaches of Network Security
Simulated Attacks based on Realism
Tests can be well simulated. Hidden problems are detected in pen tests. All day, automated tools search for known weaknesses.
Red Team Validation
Red teams act like attackers. CISOs use them to investigate the strength of defences. The outcomes indicate where improvement is required.
Individual Consulting and Response
Services provide guidance, identification and assistance. Solutions are provided by providers of any size. Indian companies employ them to apply professional prowess.
Enterprise Application Security Integration
All-Encompassing Web Application Defences
Application security is a means of keeping web apps secure in the network. Checks and safe coding are required for the top 10 OWASP hazards. This is joined with network security to have complete protection through teams.
Seamless Layering
CISOs prioritise the protection of apps compared to network regulations. This prevents attacks on a lot of levels.
How Qualysec Technologies Assists You
Qualysec Technologies provides the best enterprise network security services tha suits Indian CISOs. Proven process-based testing is employed by the experts in order to detect and remove threats. Teams also enhance your infrastructure against the attacks that are anticipated in 2026.
Qualysec Technologies is a pioneer in cybersecurity in Indian companies. The company establishes accuracy in the construction of defensive mechanisms to save critical networks without failure.
Core Services
- AI Penetration Testing
- Web Application Penetration Testing
- Mobile Security Assessment
- Network Security Testing
- Cloud Security Audits
- IoT Penetration Testing
- Source Code Security Review
- Vulnerability Analysis & Management
- Compliance Advisory Services (HIPAA, GDPR, PCI DSS, FDA, SOC 2)
- Risk Management Solutions
- Cyber Security Audit
Verified Process-based Testing
Qualysec enhance the secure network of enterprises by applying a unique verified procedure for testing. It is a method of simulating real attacks in repeatable steps.
Step‑by‑Step Verification
- Threat Mapping – Experts discover network security vulnerabilities unique to your security design.
- Staged Tests – Teams also conduct accurate penetration tests, where each threat is tested against real-world situations.
- Automated Checking – AI positive identifiers master the outcomes with utmost accuracy, eliminating false positives.
- Remediation Roadmap – You are provided with a list of priorities of the data-supported fixes.
- Clients identify attacks more quickly. This is better than traditional methods.
Custom Network Security Solutions
Qualysec tailors the enterprise cybersecurity Network Security Solutions to the Indian rules, such as the DPDP.
Artificial Intelligence in Network Security Integration
Qualysec applies AI in network security for predictive threat hunting. It reduces response time to seconds, avoiding attacks by AI.
Comprehensive Coverage
- Enterprise Security Assessment – Discovers silent breaches of firewalls, IDPS and VPN.
- Network Security Testing – Tests the best practices of enterprise network security.
- Network Security Services – Provides 24/7 automatic detection and response.
Scalable Enterprise Application Security
Qualysec extends protection to enterprise software. Teams secure web apps within the network perimeter.
Zero‑Trust Implementation
We prefer businesses to have strict least privilege and MFA. It divides the network to prevent lateral movement.
Proven Outcomes and Support
Qualysec has reduced false positives by 8 per cent in addition to 40% in cost savings. Result-driven certified CEH experts of 15+ years.
Transparent Deliverables
Get detailed reports with images and figures for continuing training of your teams.
Conclusion
To be a world leader in 2026, CISOs are becoming proficient at network security in enterprises. Layered defence, AI in enterprise network security, and best practices should be used. Native enterprise cybersecurity solutions bring benefits to Indian corporations. Regular tests and evaluations of security prevent cyberattacks. Qualysec Technologies provides you with verified means of robust protection!
Start a secure journey with experts at Qualysec Technologies now– get your audit of the enterprise network security now!
FAQs
1. What is enterprise network security?
Enterprise network security is provided to a business network against illegal access, loss of data and attacks. Firewalls, IDPS, VPNs, and access controls are some of the tools that CISOs use to ensure that endpoints, servers, and data are secure. This stratifying strategy maintains data confidentiality, accuracy, and accessibility. To comply with DPDP regulations and reduce trillions of losses, Indian firms rely on it. Network security involves the protection of AI in strong security teams to provide real-time defence.
2. What are the four types of network security?
- Firewalls eliminate the undesired traffic using rule-based filtering.
- IDPS monitors and prevents suspicious traffic.
- Virtual Private Networks (VPNs) are encrypted connections of the public networks.
- Access Control Systems enforce the MFA and role-based entry.
Business enterprise cybersecurity solutions pool them in deep defence. They deal with numerous threats such as malware and DoS. CISOs incorporate them into solutions to reduce risks.
3. Why is enterprise network security important?
Network security of the enterprise prevents severe attacks on cybersecurity spots of the business. In 2026, network security vulnerabilities are present in 92 per cent of the Indian companies, with an expense of INR 15 crore per attack. It develops trust, maintains compliance, and accelerates recovery by half. Companies neglect it as ransomware and state dangers increase. Through this strategy, it guards its revenue and reputation well. It is crucial for enterprise cybersecurity in a cloud-heavy world, according to CISOs.
4. What are the core components of enterprise network security?
Firewalls examine packets on a packet-by-packet basis. They identify real-time anomalies of IDPS spots. VPNs secure the passage of data through encryption. There are access controls that restrict exposure with zero-trust. Breachs exist in network segmentation, so SIEM tools give visibility. These are overlaid by enterprises to protect themselves. They are competent in dealing with security weaknesses. CISOs incorporate them into the network security design of enterprises to protect them comprehensively.






















































































































































































































































































































































































































































































































































































































0 Comments