An endpoint security audit is a holistic approach that determines the effectiveness of security measures established to safeguard all interrelated devices in the internet of an organisation. In the UK, with cyber threats rising by 75 percent in the last year compared to the previous year (National Cyber Security Centre, NCSC), regular endpoint security audits are now necessitated by businesses of all sizes. This system review will analyze laptops, smartphones, tablets, servers, and IoT devices to determine the vulnerabilities and provide solid security against emerging cyber threats. As remote working is becoming the new norm among British businesses, an endpoint security audit enables organisations to comply with security requirements and preserve sensitive data against advanced attackers.
Get full insights on What is a Security Audit? Importance, Types & Methods
What Are The Essential Steps In Conducting An Endpoint Security Audit?
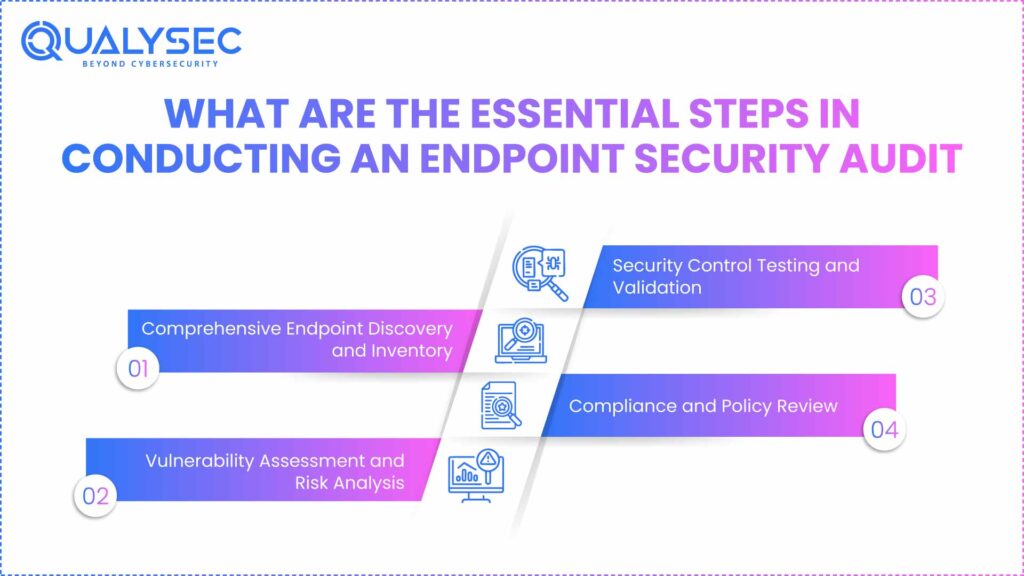
1. Comprehensive Endpoint Discovery and Inventory
To launch any successful endpoint security audit, the first step is to develop an elaborate inventory of all the devices attached to your network. This is done by locating every laptop, desktop, mobile device, and any IoT gadget that connects to your organisation’s systems.
Key activities include:
- Cataloguing all endpoint devices with operating systems and applications
- Documenting security software installations and configurations
- Recording device ownership and usage patterns
- Identifying unauthorised or unmanaged devices on the network
- Creating asset management records for future reference
- Establishing baseline security configurations for each device type
At this stage, companies in the UK have to be particularly mindful of GDPR compliance, as all data processing operations have to be duly recorded and approved.
2. Vulnerability Assessment and Risk Analysis
After the discovery stage, the security experts perform intensive vulnerability tests to detect possible vulnerabilities in the endpoint configurations. It is the key element in the endpoint security audit checklist as it assists organisations in knowing their risk exposure.
| Assessment Area | Focus Points | Risk Level |
| Operating System Patches | Missing security updates, outdated versions | High |
| Application Security | Unpatched software, unauthorised applications | Medium-High |
| Network Configuration | Open ports, insecure protocols | Medium |
| User Access Controls | Weak passwords, excessive permissions | High |
| Device Encryption | Missing or weak encryption standards | Critical |
| Endpoint Protection | Antivirus status, firewall configuration | Medium |
3. Security Control Testing and Validation
This step involves the testing of the current security controls to verify that they are capable of working against real-life threats. The endpoint security audit process also involves the simulation of different attack scenarios to test system responses.
Testing procedures include:
- Penetration testing on selected endpoints
- Malware detection capability verification
- Incident response time measurements
- User access control validation
- Data encryption effectiveness testing
4. Compliance and Policy Review
The endpoint security of UK organisations should be in line with applicable standards such as GDPR, ISO 27001, and industry-specific standards. This element of endpoint management is the review of policies and procedures against existing compliance standards.
Which tools and technologies are most effective for UK endpoint security audits?
Leading Endpoint Detection and Response (EDR) Solutions
The improved detection and response capabilities to identify and prevent threats in real-time are the main pillars of state-of-the-art endpoint protection services. Today, solutions enabled by clouds are replacing the provision of 100 percent monitoring and automatic response facilities to companies in the UK.
Essential EDR features for UK businesses:
- Real-time threat monitoring and analysis
- Automated incident response capabilities
- Machine learning-based threat detection
- Integration with threat intelligence feeds
- Compliance reporting for UK regulations
- Remote endpoint management capabilities
Vulnerability Scanning and Assessment Tools
A successful implementation of endpoint security audit checklists depends on the application of professional vulnerability scanners. These tools detect security violations and give pragmatic corrective instructions.
Popular scanning solutions include:
- Network-based vulnerability scanners
- Agent-based endpoint assessment tools
- Configuration compliance checkers
- Patch management verification systems
- Mobile device management platforms
Compliance and Reporting Platforms
Businesses in the UK need strong reporting systems to show that they comply with the regulations. The audit sites created in modern times produce detailed reports that not only please the internal stakeholders but also the external auditors.
Download our Sample Penetration Testing Report to understand how vulnerabilities are reported and mitigated.
Latest Penetration Testing Report

How can UK businesses implement endpoint security best practices effectively?
Establishing Robust Governance Frameworks
Endpoint management needs proper governance arrangements with clear roles, responsibilities, and accountability aspects to ensure successful resolution. UK organisations need to put in place structures that are aligned with the local business operations but which respond to international security threats in a global context.
Governance elements include:
- Executive sponsorship and oversight committees
- Clear policy documentation and communication
- Regular security awareness training programmes
- Incident response procedures and escalation paths
- Performance metrics and reporting mechanisms
- Continuous improvement processes
You might like to know about How Much Does Endpoint Protection Cost?
Implementing Risk-Based Security Approaches
New endpoint protection services need to prioritise the allocation of resources according to the real level of risk rather than imposing the same level of security across all devices. This will be used to provide maximum protection to vital assets whilst maintaining business efficiency.
The process of classifying the endpoints based on the sensitivity of the data they handle, the exposure to threats, and business urgency is known as risk-based security. Heightened protection is provided to critical systems, and minimum security requirements are provided to standard devices.
Continuous Monitoring and Improvement
The best endpoint security must be based on continuous monitoring and updating of endpoint security to counter new threats. The nature of cyber risks faced by UK businesses is constantly changing, and continued enhancement is the only way to ensure sufficient levels of protection.
Monitoring activities include:
- Real-time threat detection and response
- Regular security posture assessments
- Performance metric tracking and analysis
- User behaviour monitoring and analysis
- Threat intelligence integration and application
Our experts at Qualysec have helped secure fintech, SaaS, and enterprise systems across 25+ countries. Manual + Automated Pentesting. No false positives. Actionable reports.

Why is Qualysec the leading choice for endpoint security audits in the UK?
Comprehensive UK-Focused Security Expertise
Qualysec is the leading endpoint security auditing firm in the UK, and it has unmatched experience in securing British companies against advanced cyber-attacks. Having extensive knowledge and experience of UK regulatory requirements such as GDPR, Data Protection Act 2018, and industry-focused compliance requirements, Qualysec provides a customised solution to meet the specific needs of UK organisations.
Educated on comprehensive endpoint security auditing experience, our certified security professionals have worked in a wide range of industries, including financial services in the City of London and manufacturing centres in the Midlands. This overall view of the business environment in the UK will help Qualysec to deliver contextually sensitive security analysis that contributes to significant change in organisational security posture.
The combination of advanced technology and time-tested strategies, along with the latest technology, provides Qualysec with the endpoint protection service that brings the best outcomes. The most recent threat intelligence, specific to UK businesses, is integrated into our proprietary audit framework, which ensures that the assessment covers the latest and most urgent security issues affecting British organisations.
Why UK businesses choose Qualysec:
- Proven track record with over 500 successful UK endpoint audits
- Deep expertise in UK regulatory compliance requirements
- Advanced threat detection capabilities using AI-driven analysis
- Comprehensive endpoint management solutions tailored for UK businesses
- 24/7 support from UK-based security experts
- Competitive pricing structures designed for UK market conditions
Schedule your free consultation with Qualysec today to discover how our expert team can strengthen your endpoint security posture and ensure regulatory compliance across your organisation.
Key Qualysec differentiators include:
- Bespoke audit methodologies designed for UK business environments
- Integration with leading endpoint security audit checklist standards
- Rapid deployment capabilities minimise business disruption
- Detailed reporting that satisfies UK regulatory requirements
- Ongoing support and guidance for security improvement initiatives
Proven Success Record and Client Satisfaction
The excellence that Qualysec has shown has won it the respect of top businesses in the UK across various industries. Our holistic endpoint security audit service consistently delivers quantifiable improvements in security efficiency without compromising operational efficiency.
Client reviews note how Qualysec identified key vulnerabilities overlooked by other vendors, provided applicable mitigation measures, and offered ongoing service, which promotes greater security resiliency over time. This record of successful implementation qualifies Qualysec as the preferred vendor of organisations that take endpoint security seriously.
Download our comprehensive endpoint security resources to learn more about protecting your organisation against evolving cyber threats.
Conclusion
Endpoint security audits are an essential part of a holistic approach to cybersecurity for UK businesses. As cyber threats keep on advancing and regulatory requirements keep on increasing, organisations need to have a robust audit process that will deal not only with technical vulnerabilities, but also with compliance requirements.
The systematic methodology described in this article offers a convenient model that UK businesses can use to undertake quality endpoint security audits. Since the first discovery and inventory, up to vulnerability assessment, security testing, and compliance review, every step will help create a complete picture of organisational security posture.
The next-generation endpoint protection service providers should incorporate both modern technology and well-established practices to deal with the advanced threats that are threatening businesses in the UK. Combining EDR solutions, vulnerability scanners, and compliance platforms generates a complete security ecosystem with protection and visibility.
To be successful in terms of endpoint management, continuous improvement, regular evaluation, and keeping up with new threats must be committed to continuously. Those organisations in the UK that adopt this proactive strategy will be in a better position to safeguard their valuable assets without necessarily losing competitive advantages in an ever-digitised business environment.
Through collaboration with more established providers such as Qualysec, UK businesses can tap into expert knowledge and established practices to improve their security capabilities whilst adhering to the appropriate regulations and industry standards.
Contact our expert team now to begin your comprehensive endpoint security transformation with the UK’s leading security audit provider.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
FAQ
1. What is meant by endpoint security?
Endpoint security is a blanket term used to describe the protection of all devices that access the network of an organisation, such as laptops, smartphones, tablets, and Internet of Things devices. In this endpoint protection service, security measures are implemented to prevent unauthorised access and block cyber threats like anti-virus software, firewalls, and monitoring tools. These connected devices are correctly configured and adhere to organisational policies through endpoint management.
2. What are the three main types of endpoint security?
The three main categories of endpoint security are Endpoint Protection Platforms (EPP) that offer traditional antivirus and firewall, Endpoint Detection and Response (EDR) solutions that offer enhanced threat hunting and incident response, and Mobile device management (MDM) systems that provide security to smartphones and tablets. All types are essential in a comprehensive endpoint security audit checklist and can help in effective endpoint management in a wide variety of device settings.
3. What does a security audit include?
An endpoint security audit consists of the following: device inventory and discovery, vulnerability, security control, tests, compliance review, and risk analysis. The endpoint security audit checklist includes review of installed security software, access controls, encryption implementations, validations, and testing incident response procedures. This comprehensive assessment determines that the endpoint protection services are efficient in protecting organisational assets against dynamic cyber threats.
4. What’s the difference between EPP and EDR?
Endpoint Protection Platforms (EPP) offer preventive security such as antivirus scanning and firewall protection, and Endpoint Detection and Response (EDR) solutions include threat hunting capabilities, real-time monitoring, and incident response capabilities. EPP is aimed at preventing familiar threats, but EDR is an excellent tool in identifying advanced attacks evading established defences. Both elements are critical aspects of current endpoint security audit procedures and overall endpoint management plans.
Have any questions? Feel free to ask now—our cybersecurity experts are here to help.





















































































































































































































































































































































































































































































































































































































0 Comments