Data security solutions are now a mandatory requirement for businesses in 2025. Hackers now use AI-powered phishing, ransomware-as-a-service, and insider manipulation. That is the reason why each organisation must choose outstanding data security solutions.
The situation is even more acute in India, as the Digital Personal Data Protection (DPDP) Act has been implemented. It also asks businesses to protect the data of their customers and employees, as well as stay compliant.
As the number of people adopting digital in all their niches continues to grow, companies have been producing more data than at any given time. This contributes to the sensitivity of information being not only a compliance issue but also a very important trust issue that customers and stakeholder’s exhibit.
Today, in this blog, we are going to discuss the key data protection solutions that businesses will require in 2025 and how to select the right ones to suit their organisation.
Importance of data security solutions in 2025
The cybersecurity world has transformed significantly in the past years or so. There is a consistent rise in the number of cyber incidents being reported in India, with phishing, malware attacks, and ransomware being the most prevalent of these menaces. To companies, this would mean a lack of profit, loss to operations, and damaged reputation.
These three factors make data security solutions more relevant in 2025:
- Tighter laws: Legal accountability on businesses has been enforced through stricter laws in the DPDP Act in India, as well as international laws such as GDPR and HIPAA. They control the data collection, storage, and use by businesses.
- Advanced threats: With automation and AI, attackers are exploiting vulnerabilities at an unprecedented rate, targeting cloud environments, remote endpoints, and systems that have not yet received a security patch.
- Customer confidence: Within a competitive market, customers will find it easier to do business with a company that can assure them of effective data security. One violation would undermine years of brand equity. Nonprofits are 50% more likely to be targeted by cyberattacks, which is why platforms like Donorbox follow SOC 2 and PCI standards to safeguard donor data.
Companies can reduce the risks, stay compliant, and build resilience in the long term by investing in effective data protection, whether in encryption and data loss prevention tools or managed security services, and choosing the best data security company.
Book your free data security consultation with Qualysec today.
Top 7 Data Security Solutions Every Business Needs in 2025
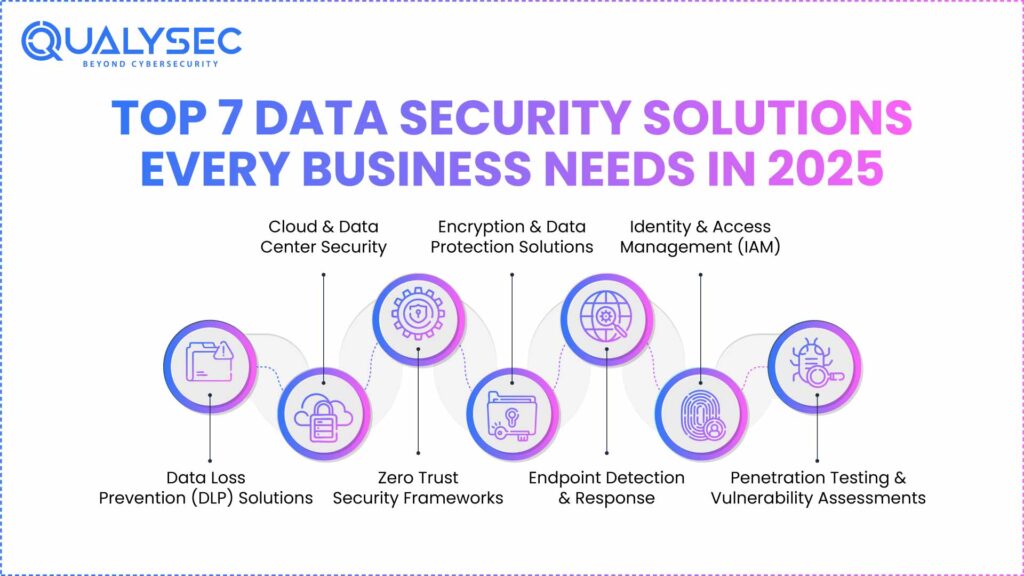
1. Data Loss Prevention (DLP) Solutions
DLP solutions track, identify, and block illegal transfer of sensitive data. They secure against email, cloud storage, or endpoint leakage. Employees work with sensitive data when they are not in secure office networks with hybrid work and the active use of SaaS security tools. Besides, there is the increasing problem of insider threats.
DLP tools help Indian firms to comply with the DPDP Act by ensuring that personal data is not mishandled. They also ensure that intellectual property, financial records, and customer databases do not leave the organisation unmonitored. Hiring the best data security company is an excellent idea.
2. Cloud & Data Center Security
Systems, applications, and policies that protect and defend against intrusions and malicious actions on cloud and on-premise data centers. There is an increased use of cloud-based applications, storage, and processing in most organisations. Nonetheless, one of the most common causes of data breaches has its roots in misconfigured cloud settings.
Implementing strong identity management, encryption, and continuous monitoring ensures data center security. It also implies adhering to RBI rules of safe data storage and avoiding the unsustainable loss of time in Indian companies, primarily in finance and e-commerce.
Read our complete guide on Cloud Data Security
3. Zero Trust Security Frameworks
Zero trust security architectures represent a type of never trust, always verify model in which all users, devices, and applications must be authenticated and authorised before gaining access to resources. Perimeter-based security cannot work any longer. Remote employees, third-party infrastructure, and cloud security solutions give companies no reason to think that anything within the network is secure.
Zero Trust enables Indian organisations to mitigate risks of insider abuse and subsequent movement of threats laterally. It increases adherence in that sensitive data access is strictly regulated at all levels.
4. Encryption & Data Protection Solutions
Encryption is used to protect data by turning it into incomprehensible code, which can only be decrypted using the proper decryption code. It extends to data at rest, data in transit, and data in use. New and stricter laws on data protection require sensitive information like financial transactions, healthcare records, or Aadhaar-linked information to be encrypted to ensure that they are not accidentally exposed.
With encryption, the attackers can still intercept data, but it becomes useless to them. This reduces the impact of breaches and assists businesses in showing that compliance occurred when audited. Using a robust data security platform can also help.
5. Endpoint Detection & Response
These are solutions that track all devices, such as laptops, smartphones, and servers, and identify suspicious activity and react as it happens. Extended Detection and Response (XDR) takes this further to cloud and network environments. Reverse and distance work has increased the attack surface. A hacked employee device may act as the gateway to ransomware or credential theft.
Endpoint detection and response gives companies in India insight into network and device threats, enabling them to address incidents fast before they worsen.
6. Identity & Access Management (IAM)
IAM systems will provide access to authorised users to particular resources, with functions such as multi-factor authentication (MFA), single sign-on, and access privileges. The most popular method through which attackers enter is by stealing credentials. Companies dealing with sensitive customer or financial information simply cannot afford loose access controls.
Secure IAM reduces security breaches, improves compliance, and helps employees and others access without risking security. In India, as an example, these companies (fintech and healthcare) need to show serious identity control when conducting compliance checks. Choosing reliable data protection services can help.
You can explore the top cybersecurity companies in fintech & cybersecurity in healthcare.
7. Penetration Testing & Vulnerability Assessments
Professionals recreate cyberattacks in order to locate and address weaknesses before they are taken advantage of by the bad guys. AI is enabling attackers to scan more quickly than ever before. Vulnerable data can be revealed in one unprotected point.
Considerable penetration testing can also help Indian businesses to enhance the strength of their defences, avert costly breaches, and allow them to keep pace with industry regulations.
Explore the difference between Penetration Testing & Vulnerability Assessments
How to choose the best data security solutions for your business?
There are so many data security services out there that it can seem daunting to find the appropriate match for your organisation in 2025. The following are some of the main considerations that can help you make the decision:
1. Assess Your Business Risks
Start with a risk assessment. Identify the type of information you are dealing with (customer databases, payment data, intellectual property) and where the information exists on-premises databases or a cloud-based environment, or a hybrid environment.
2. Meet Compliance Requirements
The Digital Personal Data Protection (DPDP) Act, 2023, commits companies to securing personal data and reminds them of their responsibility in the event of its misuse. Depending on your industry, you may also be expected to comply with either RBI, SEBI, or international standards of information security, including ISO 27001 and GDPR.
3. Balance Cost with ROI
Budget is a significant issue for most Indian SMEs. Advanced SIEM or Zero Trust systems might seem prohibitively expensive, but they will help stop breaches that could cost crores of downtime, penalties, and reputational loss.
4. Priorities User Experience
Cyber Security solutions will be effective only when employees use them. Select the platforms that have easy-to-use dashboards, can be used on a phone, and least amount of friction.
Latest Penetration Testing Report

How Can Qualysec Help?
Although businesses might know the value of good data security services, it is often difficult to implement and effectively manage them. This is where Qualysec comes in as a well-known pen testing partner.
Businesses must be aware of their vulnerabilities before investing in better data security solutions. To be sure that your data protection strategy begins with the appropriate foundation, Qualysec offers VAPT services to assist in identifying vulnerabilities in applications, networks, and systems.
Qualysec also provides continuous evaluation, audits, and reporting to ensure that its guard remains active against emerging threats. Our professionals work through complicated compliance regulations without any issues, and they come up with audit-ready reports.
Ensure compliance with Qualysec’s expert guidance.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Conclusion
Cyber criminals are also using AI to make their attacks even more brutal. That is why cyber resilience is not an option anymore for a business. Between data loss prevention and Zero Trust frameworks, and managed data protection services, opting for reliable data security solutions is a must.
For businesses in India, this is where expert guidance makes a difference. By engaging in collaboration with a pen testing firm such as Qualysec, you will receive customised solutions, ongoing monitoring, and compliance assistance.
FAQs
1. What are data security solutions?
Data security solutions are defined as technologies, tools, and practices implemented so that unauthorised access, theft, or loss of sensitive information can be prevented. Such measures include encryption, data loss prevention (DLP), endpoint security, identity and access management (IAM), and cloud security.
2. Why are data security solutions important for businesses?
Poor security exposes businesses to cyber attacks, government fines, and loss of publicity. Data security solutions minimise such risks, enhance legal compliance (including the DPDP Act), and resiliency in the case of a security breach.
3. What types of data security solutions are available?
Common types of data protection solutions include:
- DLP to stop unintentional leaks.
- Protecting devices that the employees use with Endpoint Security Platforms.
- Zero-trust Security to check all users and devices.
- SaaS and cloud infrastructure Cloud Security Solutions.
- At rest and during transit, data encryption and Key Management.
- SIEM real-time monitoring and analysis systems.
- IAM Systems to control (secure) user access.
- Business managed security services without in-house resources.
4. What are common challenges in implementing data security solutions?
Budgets are more often than not a disadvantage to any business, especially SMEs, which are not able to pay extra costs to invest in sophisticated tools. It can be challenging to integrate with old systems, and sometimes complicated actions trigger employee opposition. The in-house expertise is itself a problem, and as cybercriminals constantly evolve, organisations have to keep updating their defences to keep pace.





















































































































































































































































































































































































































































































































































































































0 Comments