Key Takeaways
- Beyond Software Scans: Modern security audits use a forensic approach with human involvement to assess technical stacks, internal policy compliance, and ‘non-human’ identities.
- Escalating Financial Threat: Estimates suggest the cost of cybercrime worldwide will reach $23 trillion by 2027, therefore validated protection is required as a minimum to enable business continuity
- Threat of Hidden Artificial Intelligence: An audit which is to take place in 2026 will include finding ‘Shadow IT’ and AI agents that operate outside of an organisation’s traditional boundaries of security.
- Strategic Compliance: Certifications such as SOC2 and ISO 27001:2022 must be independently confirmed via audit that your controls can be executed in a live operational setting.
- Proactive Resilience: Prioritising your risk provides your organisation a safer pathway to scaling than was available when completing reactive patching and protects the organisation’s brand.
Introduction
A security audit will evaluate your entire digital environment and provide actual proof that your security measures work correctly. In addition to evaluating your internal policies and technical stack for data protection, a professional security audit service will also review your physical security in the workplace. Using this type of service, a company can identify potential weaknesses, comply with international regulations, and prevent data breaches before they happen.
The global economic impact of cybercrime is projected to be nearly $23 trillion by 2027, with more than three thousand attacks experienced by every organization in India each week, and as such will require verification that they are protected as best as possible. An audit will provide businesses with a definitive insight into their current risk profile and supply an action plan toward improved protection from threats. Regardless of the purpose for obtaining a security audit, such as getting your SOC2 certification, understanding the fundamentals of security audits is necessary when seeking to achieve true resilience against cybercriminals.
What Is a Security Audit?
Many organizations do not differentiate between audits and scans, even though they both deal with different levels of protection. For example, a vulnerability scan is a fast and automated process of looking for known software bugs and/or vulnerabilities. However, when conducting an information security audit, the auditor investigates all aspects of an organization’s information security architecture using human intelligence and expertise to determine whether the organization’s internal policies, employees’ behaviors, and all technical configurations align with the organization’s business objectives.
As we move into 2026, the scope of a standard information security audit will include “Non-Human” entities as part of the audit process, such as auditing the permissions granted to automated AI agents and verifying that your cloud-based infrastructure is not leaking data through undocumented “shadow” IT services. Another analogy for a scan versus an audit is if the door is locked versus who has access to the lock, how many keys exist for that lock, and whether the lock has sufficient strength against new attack methodologies.
Audit vs. Pentest vs. Vulnerability Assessment
To choose the right level of protection, you must understand how a security audit differs from other common evaluations. While they often overlap, their goals and outcomes are distinct.
| Feature | Vulnerability Assessment | Penetration Test | Security Audit |
| Primary Goal | Identify known software bugs. | Actively exploit a specific path. | Evaluate the entire security posture. |
| Method | Automated Scanning. | Human-led Attack Simulation. | Technical Review + Policy Audit. |
| Key Output | A list of patches to apply. | Evidence of a successful breach. | A compliance report and roadmap. |
| 2026 Focus | Real-time monitoring. | Testing AI-driven defenses. | Shadow AI & Data Governance. |
You might also like to read about Compliance Security Audit: A Comprehensive Guide
Types of Security Audits
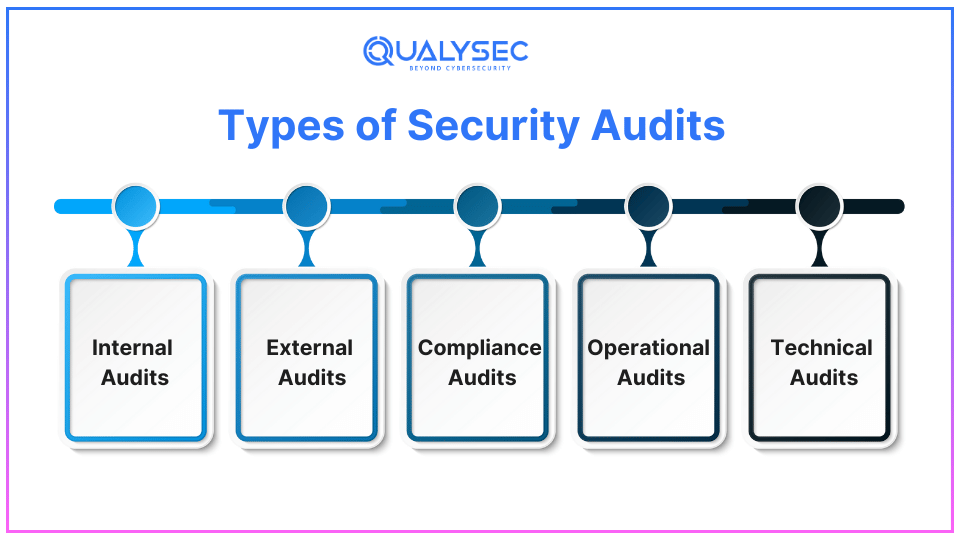
There are several sorts of security audits, each with different goals.
1. Internal Security Audits
These are conducted by your own team for the purpose of ensuring that people are following the internal policies of the organisation. This is very important in order to identify “Insider Threats” and also ensure that employees are processing and managing data in accordance with the company’s standard operating procedures.
2. External Security Audits
As the name implies, these types of audits are performed by a third-party firm (like Qualysec). The auditors are not affiliated with the company being audited and therefore provide an independent opinion that has greater credibility with your customers and stakeholders. This is often a requirement to demonstrate your “Due Diligence” to stakeholders or insurance providers.
3. Compliance Audits
Compliance audits are audited by established frameworks (e.g., SOC2, HIPAA, or ISO 27001). By completing a compliance audit, you show that you comply with the laws governing your particular industry, which is generally required of most enterprise-level service providers by the year 2026.
4. Operational Audits:
Assess the adequacy and efficacy of security measures in operations.
5. Technical Audits:
Includes detailed examination of technical issues relating to the organization’s information systems, including network, application, and database security.
Schedule your free security assessment with our experts.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
What Does a Security Audit Procedure Consist of?
A security audit thoroughly examines an organization’s information system to ensure it adheres to security regulations and preserves data availability, confidentiality, and integrity. Hence, it typically consists of the following basic elements:
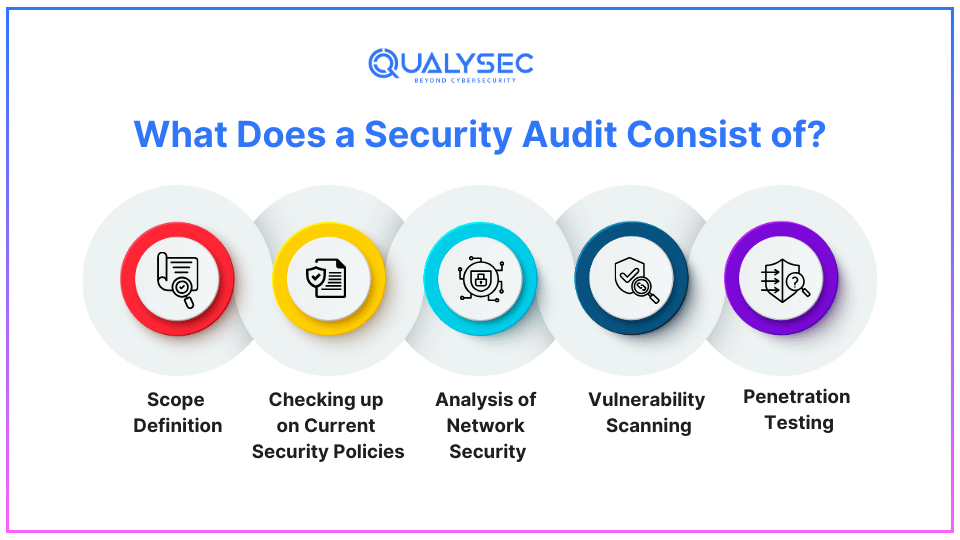
1. Scope Definition
A security audit can be defined as the initial stage of the process that includes determining the systems, applications, or networks to be investigated. Therefore, this means defining essential assets, data kinds, and risks to prioritize what kind of audit is necessary and where there is the most danger.
2. Checking up on Current Security Policies
To check the balance and relevance, auditors also look at the existing policies on security. Evaluate policies and processes for access control, data protection, and overall regulatory compliance to determine whether risk mitigation is effective.
3. Vulnerability Scanning
Software programs perform network and system scans to look for security gaps. This process reveals threats like insecure software, improper configurations, and unpatched systems, which may invite attackers.
4. Penetration Testing
Penetration testing emulates real-life attacks to evaluate the efficiency of applied security measures and reveal the other vulnerabilities that could remain unnoticed. this method uses both automated tools and manual testing methods to discover maximum security vulnerabilities in the system.
5. Analysis of Network Security
This step includes studying the structural design and specifications of networks. Auditors analyze the specifics of the firewall and other security products and check encryption and other methods to prevent intrusion from the outside and internal threats.
Why Do Companies Need a Security Audit?
Companies need security audits for several compelling reasons:
| Protecting Sensitive Information | Protecting the privacy, accuracy, and accessibility of sensitive data. |
| Regulatory Compliance | To ensure that legal penalties are avoided and that industries adhere to the standards and legal requirements set out by the law. |
| Preventing Data Breaches | Preventing loopholes that the attacker can exploit to their advantage. |
| Enhancing Trust | Securing consumer, business, and stakeholder relationships by proving that security is a corporate priority. |
Have you conducted a security audit for your company recently? Do not fear; get in touch with us to receive cybersecurity audit services right away!
Consult with our cybersecurity experts
Discuss your unique security requirements and discover how we can help your business.
Security Audit Procedures (The 7-Step 2026 Framework)
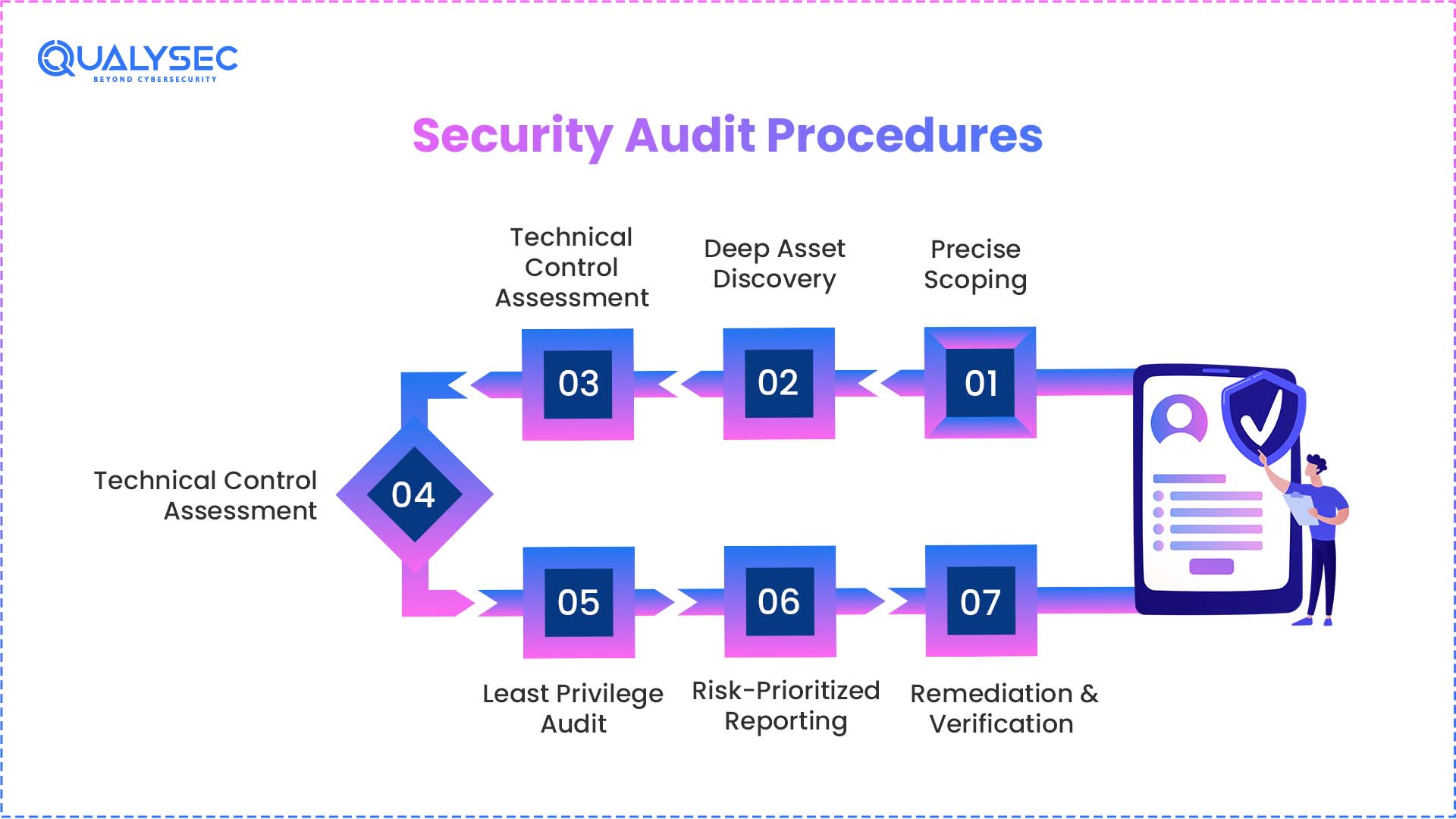
Security auditing today isn’t just one-off assessments, but rather an evolving and dynamic routine, where the audit process must be both dynamic and forensic considering that assets exist within multi-cloud environments along with autonomous AI agents. A methodology of this nature is moving beyond basic compliance to really focus on the true resilience of your operating environment.
Phase 1: Precise Scoping
To begin, we will define the exact parameters of the audit process, determining exactly what networks, applications and cloud instances store and/or process your critical data. Having a clear set of parameters will eliminate any areas of the network that may be “hidden” and will increase the level of due diligence that is applied to the most sensitive areas of your infrastructure.
Phase 2: Deep Asset Discovery
For many organisations, “Shadow IT” is a problem, where different departments have deployed technology without proper authorisation. During this phase, the audit will include a comprehensive mapping of every hidden asset in the environment, including third-party SaaS integrations utilized and/or autonomous AI agents that have been granted a high level of access without oversight.
Phase 3: Administrative Policy Review
Security isn’t just about technology; it is also about the people who use it. We will evaluate your written security policies to see if they are actually being adhered to by your staff throughout their daily operational tasks. This will include a review of your onboarding processes, data handling procedures, and incident response readiness.
Phase 4: Technical Control Assessment
Technical controls for cybersecurity are evaluated through automated test tools and manual review by expert consultants. The next step in this process will include manual testing a wide variety of items, including firewalls, encryption methods, etc., to determine their effectiveness at preventing advanced attempts at hacking.
Phase 5: Least Privilege Audit
Users in your organization have limited privileges to access only the necessary resources needed to do their job. This protects companies from unwanted lateral movement (the opportunity to access multiple systems) if one system is compromised during a breach.
Phase 6: Risk-Prioritized Reporting
The information provided after completion of the assessment will be in order of priority, based on actual impact on your business and how easy the vulnerabilities could be exploited by an attacker. Your organization will receive a clear plan of action for addressing vulnerabilities in order of priority rather than a long list of confusing unknowns.
Phase 7: Remediation & Verification
In order for an audit to be valuable, an improvement in security postures must take place. After the fix has been applied by your team, verification to ensure that all identified weaknesses were resolved and that the remediation process did not cause further weaknesses will take place.
Are you curious about the structure of a security audit report? To download one, click the link below!
Get a Free Sample Pentest Report
The Comprehensive Security Audit Checklist
A full audit analyzes every detail to make sure your organization is protected on all levels. In addition to those listed above, our audit will also review five key areas of concern. These include:
Network & Infrastructure Security
- Configuring Firewalls and Routers: It is important to check all firewall and router configurations for the following: only the required ports are opened-up; boundaries are in-place between different networks.
- Encrypting Network Traffic and Data-at-Rest: Encrypting all network traffic (both at rest and in motion) using newer encryption protocols is essential.
- Securing Wireless Networks: Scan all wi-fi networks (including guest wi-fi networks) for unauthorized access points.
Access Control & Identity Management
- Use of Multi-Factor Authentication (MFA) must be utilised on every system (including legacy systems) where identity verification is required.
- Assessing Password Policies (including length, complexity and frequency of changes in the password) for strength and compliance.
- Auditing the permissions granted to non-human identities (including service accounts, API keys and automated AI agents).
Cloud & SaaS Governance
- Mapping Shadow IT: Planning for unidentified cloud services/apps/systems that can potentially compromise your company’s sensitive data.
- Checking for platform misconfigurations or configuration mistakes by cloud service providers such as AWS, Azure and GCP.
- Verifying that where your data resides and/or is stored meets applicable laws such as the GDPR or the Identification and Prevention of Data Theft Act (ID) for India.
Conclusion
To move away from being reactive about security toward being proactive at creating resilience to various things that threaten a company, an organization first needs to know their current level of security. In 2026, the security audit should no longer be viewed as just a regulatory requirement and/or an IT department task in the form of a “check box.” Instead, the security audit should provide business leaders with a strategic advantage by giving them confidence that they can grow safely within a complex digital landscape. As your organization identifies misconfigured or missing policy items and remediates these items before hackers do; you will be providing protection to your reputation as well as your financial future.
As we move further into a cloud-first and AI-driven era, the quality of your auditing partner will define your ability to navigate emerging threats with confidence. Selecting a firm like Qualysec that understands the intersection of human expertise and automated intelligence is the only way to ensure your organization remains secure.
Schedule a meeting today and get a complete security audit for your business.
FAQs
Q: How long does a professional security audit take?
A: The amount of time to conduct your security audit will be between 2 and 6 weeks, depending on the size and configuration of your environment. The duration will also be affected by many other variables, including the quantity of cloud assets, the number of physical locations, and the complexity of your artificial intelligence integrations.
Q: Is a security audit the same as ISO 27001 certification?
A: No, while they are closely related. A security audit is an assessment of your controls, whereas ISO 27001 is the international standard to which you are being compared. A successful audit is a prerequisite for obtaining and maintaining an ISO 27001 certification.
Q: What is the difference between a security audit and a SOC2 report?
A: A security audit is an evaluation of technical and administrative controls by the auditors. A SOC2 report is a formal document produced at the end of the security audit that provides evidence to your customer that you are complying with all specified trust services criteria for how you handle data.
Q: Can we perform a security audit internally?
A: Yes, internal audits can be beneficial for maintaining security and detecting “Insider Threats.” However, many of our clients, including enterprise clients and insurance companies, require an independent third-party security audit from an external company, such as Qualysec, to ensure that the results of the audit are objective and credible.





















































































































































































































































































































































































































































































































































































































0 Comments