Key Takeaways
- Cybersecurity requires compliance under EU MDR as part of safety and performance requirements, particularly for devices with software, connectivity, or data handling.
- Testing methods such as vulnerability scanning, penetration testing, and fuzz testing are widely used to demonstrate security, based on device risk and architecture.
- Independent testing is often expected as a best practice for higher-risk or complex devices.
- MDR cybersecurity testing must adhere to the latest state-of-the-art standards and security protocols.
- Strong documentation and lifecycle security practices are crucial for cybersecurity assessment
Introduction
The average cost per cyber breach in 2025 was $7.42 million globally. The healthcare industry was one of the industries that suffered the most during data breaches. In the case of medical device manufacturers, this is because your product can be subjected to regulatory and financial risks. To counter this menace, the EU has introduced cybersecurity as a compulsory provision in the CE marking, including the CE Mark Cybersecurity Assessment. The authorities require the medical equipment company to implement MDR cybersecurity testing and vulnerability scanning, penetration testing, fuzz testing, and many others.
To work efficiently in the European market, manufacturers must:
Know the required testing, have a security by design structure that meets the audits of the Notified Body under EU MDR compliance. They must have comprehensive technical documentation throughout the lifecycle of the device.
What is the CE Mark Cybersecurity Assessment?
A CE Mark Cybersecurity Assessment is an obligatory procedure that allows manufacturers to prove their compliance with EU safety, health, and environmental regulations of their digital products. Products cannot be placed on the EU market without meeting applicable CE marking requirements, including cybersecurity-related obligations where relevant. The rules state that to achieve CE marking, it is a prerequisite to maintain cybersecurity.
- Radio Equipment Directive (RED 2014/53/EU): The Radio Equipment Directive (RED) introduces cybersecurity requirements for certain connected devices, with enforced as of August 2025 under Articles 3.3 (d), (e), and (f), depending on device category. The act mandates network integrity, personal data security, and avoidance of fraud or abuse.
- The Cyber Resilience Act (CRA): The upcoming Cyber Resilience Act (CRA) will introduce mandatory cybersecurity requirements for products with digital elements and is expected to impact CE marking in the coming years.
- Sector regulation: Medical devices must comply with cybersecurity regulations such as the EU Medical Device Regulation (MDR) guidelines to prevent unauthorized access and safeguard the sensitive data of patients.
Common Cybersecurity Testing Approaches Used for MDR Compliance
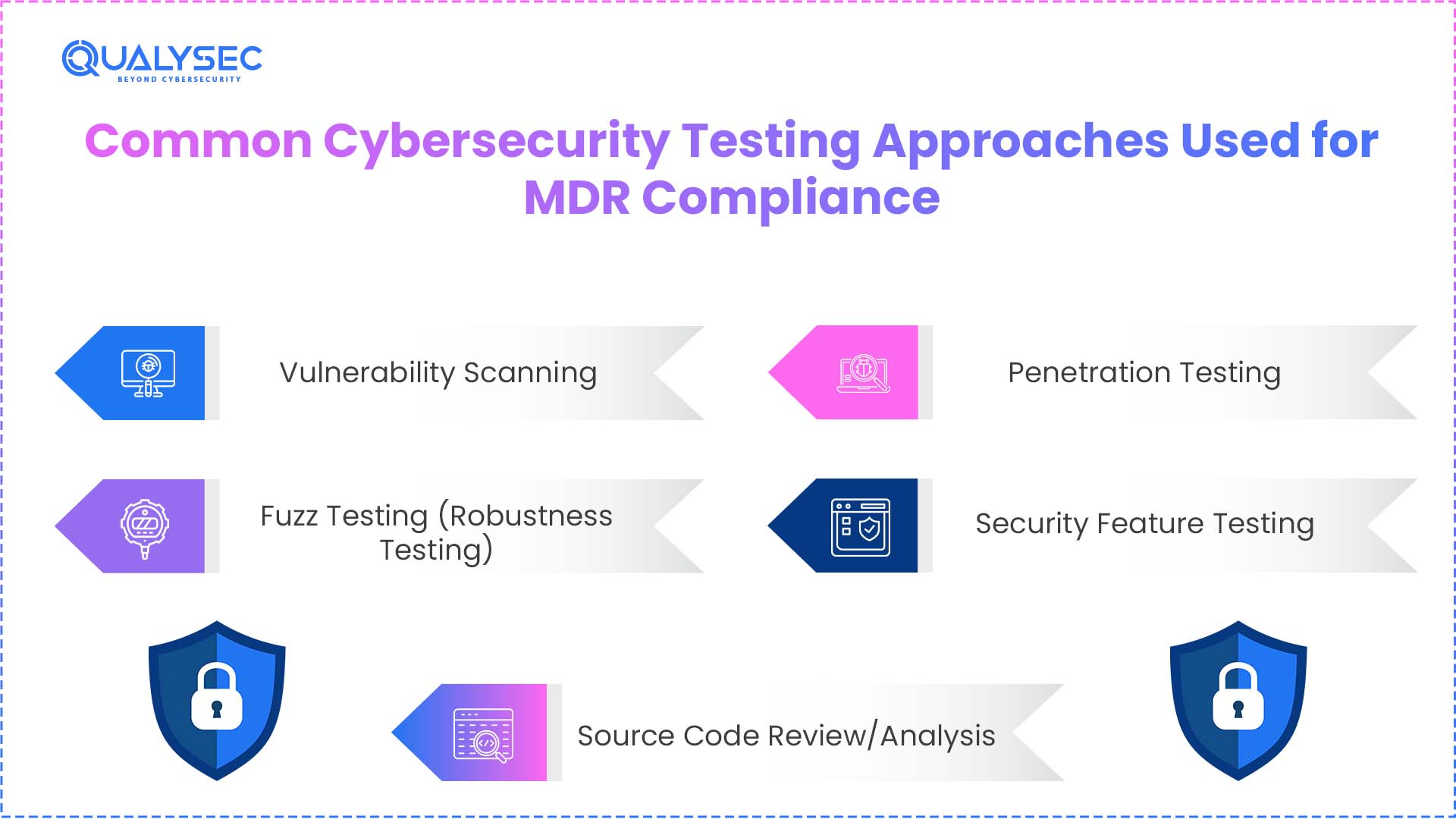
Companies producing medical devices in the European Union must be in compliance with the EU medical device security requirements. To meet the General Safety and Performance Requirement, the manufacturers may go through these 4 types of cybersecurity tests:
1. Vulnerability Scanning
This is technically the minimum of cybersecurity testing in EU MDR compliance. To detect known vulnerabilities, manufacturers must methodically scan software in scanning devices, third-party components, and even the Software of Unknown Provenance (SOUP).
Vulnerability scanning identifies known issues in systems and components, while SAST analyzes source code for security weaknesses during development. Software Composition Analysis also discovers risks in the open-source dependencies and supports SBOM requirements, and Dynamic Application Security Testing (DAST) that tests running applications to identify vulnerabilities such as injection vulnerabilities or cross-site scripting.
2. Fuzz Testing (Robustness Testing)
It involves giving invalid, unpredictable, or random data to the communication interfaces of the device in order to determine whether it can result in a failure or an insecure state. The chief objective of the fuzz testing is to demonstrate that the device is resistant to malformed input types of cyberattacks. The team performs the testing in all the outside interfaces such as Bluetooth Low Energy (BLE), Wi-Fi, USB ports, and proprietary serial ports.
3. Penetration Testing
Medical devices, connected mobile applications, and cloud backends are tested in penetration testing. Security experts perform a simulated real-world attack to identify exploitable weaknesses and test the safety of medical machines as stipulated by the EU MDR.
The key objective of the penetration testing is to demonstrate that the cyberattackers will not be able to circumvent security controls. In the case of more risky devices (Class IIa and higher), independent third parties will be required by the manufacturers to conduct the penetration testing.
4. Security Feature Testing
Such testing confirms that the particular security controls adopted by the manufacturers to minimize risks actually perform practically. It is concerned with proving every countermeasure as to its intent. It encompasses all Security Claims in the Technical File, such as user access controls (RBAC), secure boot sequences, and data at rest and in transit.
As an example, say you have defined encryption in your risk management plan to avoid data theft; in this case, this testing will give evidence that the encryption is working to protect data as expected.
5. Source Code Review/Analysis
It is the White Box assessment of MDR 2017/745. It analyses the software source code of the device to discover security vulnerabilities, bugs, or lack of adherence to secure coding guidelines (e.g., MISRA C, CERT C, or OWASP).
At the time that vulnerability assessment indicates vulnerabilities, Source Code Review/Analysis identifies the so-called hidden flaws of the automated scanners. It dwells upon high-risk modules, such as cryptographic implementations, authentication logic, memory management (to eliminate buffer overflows), and data-handling routines in support of Patient Identifiable Information (PII).
Download a sample penetration testing report to see how cybersecurity testing approaches align with EU MDR compliance. It must help you meet regulatory requirements with confidence.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
How Do Notified Bodies Assess Medical Security?
Notified Bodies (NBs) evaluate device security through an audit. NBs focuses on the “Security by Design” principle:
1. Lifecycle Traceability:
The Notified Bodies ensure that they address cybersecurity throughout the device’s entire lifecycle. It covers risk management according to ISO 14971, development according to IEC 62304 and EN 81001-5-1, and finally post-market activities.
Get a Free Sample Pentest Report
2. Evidence:
The relevant authorities require the manufacturer to produce detailed reports on cybersecurity tests that have been performed. These include vulnerability scanning, source code review, fuzz testing, Penetration Testing, and security feature verification. In addition to this, third-party penetration testing is also required for high-risk devices to ensure unbiased results.
3. State of the Art (SOTA):
The Notified Bodies check to ensure that they have taken security measures according to the state of the art. They use guidelines such as MDCG 2019-16 and security protocols such as TLS 1.3.
Required Documentation for the CE Cybersecurity Assessment
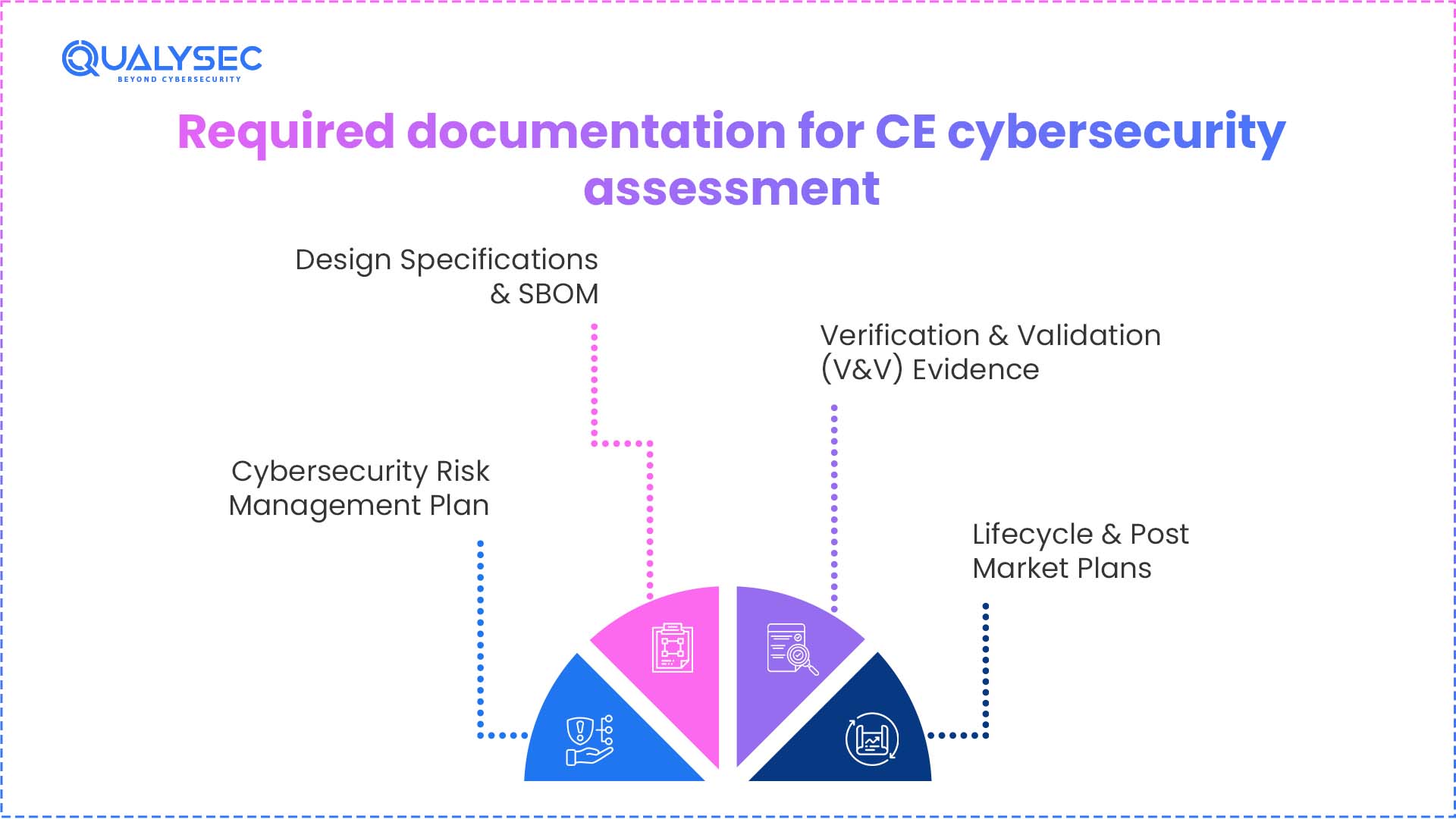
Manufacturers of medical devices need to show the cybersecurity practices throughout the product lifecycle. They are also in line with CE mark cybersecurity requirements and broader EU medical device security compliance expectations.
1. Cybersecurity Risk Management Plan
This is the foundation of your cybersecurity assessment. It must align with ISO 14971 and AAMI TIR57. You need to provide a Formal Threat Model that visually maps your device’s attack surface and entry points.
2. Design Specifications & SBOM
To meet CE mark cybersecurity requirements, you must provide a Secure Architecture Design that includes details of encryption layers and authentication checkpoints. Software Bill of Materials (SBOM), along with Security Requirements Specification (SRS), is critical to support compliance with EU medical device security compliance frameworks.
3. Verification & Validation (V&V) Evidence
Provide evidence from cybersecurity testing in accordance with MDR cybersecurity testing expectations. This includes vulnerability assessment reports (SAST/DAST/SCA), code review summaries, healthcare penetration testing (for connected devices), fuzz testing results, and verification of implemented security features.
4. Lifecycle & Post-Market Plans
A cybersecurity assessment of medical devices requires proof that security continues after the sale. Manufacturers need to document a Post-Market Surveillance (PMS) Plan to monitor new “Zero-Day” threats and a Vulnerability Disclosure Policy (VDP) for external reporting. The manufacturer also needs to secure update mechanisms, including digitally signed updates and validation before deployment
Pro Tip
The Cybersecurity Traceability Matrix is the most important document required for CE cybersecurity assessment.
It ties everything
Threat ID (from Model) → Risk ID (from Analysis) → Security Requirement (Design) → Test Case ID (V&V Report) → Pass/Fail Result
How Qualysec Secures Your Regulatory Approval?
CE mark cybersecurity assessment requires a partner who understands both the technical depth of hacking and the rigid structures of European law. Qualysec acts as a bridge between engineering teams and Notified Body auditors.
Specialized Services Include:
- End-to-End MDR Cybersecurity Testing: Qualysec provides the full suite of mandatory testing required for the Technical File, including Vulnerability Scanning (SAST/DAST/SCA), Fuzz Testing, and Security Feature Validation.
- Penetration Testing: For Class IIa, IIb, and III devices, Qualysec conducts the independent, human-driven cybersecurity assessment for medical devices that Notified Bodies demand to prove resilience against sophisticated, real-world exploits.
- Audit-Ready CE Certification Security Documentation: Beyond finding bugs, Qualysec provides the evidence. Reports are mapped directly to CE mark cybersecurity requirements, providing the “State of the Art” proof, SBOM analysis, and Traceability Matrices needed for a smooth audit.
- Regulatory Alignment (MDR, RED, & CRA): Qualysec helps harmonize security posture across the Medical Device Regulation (MDR), the Radio Equipment Directive (RED), and the Cyber Resilience Act (CRA), preventing redundant testing and fragmented documentation.
- Post-Market Support: Qualysec assists in developing Post-Market Surveillance (PMS) and Vulnerability Disclosure Policies (VDP), ensuring devices remain compliant throughout their entire operational lifecycle.
Discuss with an expert on how to best streamline the regulatory approval process and make your security readiness stronger with the right approach.
Conclusion
A CE mark cybersecurity assessment is the gatekeeper to the European healthcare market. As ransomware incidents increasingly trigger GDPR violations and risk patient lives, the “State of the Art” requirement has moved from a vague guideline to a strict technical mandate. Achieving EU medical device security compliance requires more than just checking boxes; it demands a shift toward “Security by Design.” Manufacturers ensure that every vulnerability scan and penetration test is reflected in their CE certification security documentation.
Frequently Asked Questions (FAQs)
1. Is cybersecurity required for CE marking?
Yes, cybersecurity is mandatory for CE marking if the device includes software, connectivity, or handles data.
2. What cybersecurity tests are needed for MDR compliance?
MDR requires vulnerability scanning, penetration testing, fuzz testing, security feature testing, and source code review.
3. How do notified bodies evaluate device security?
Notified bodies assess cybersecurity by conducting audits that emphasize lifecycle traceability, risk management, testing documentation, and adherence to advanced security standards throughout both development and post-market phases.
4. What documentation do we require for a CE cybersecurity assessment?
Cybersecurity risk management plan, threat model, secure architecture design, SBOM, cybersecurity test reports, vulnerability disclosure, and patch management.
5. How long does a cybersecurity evaluation take?
The duration varies depending on the complexity and risk classification of the device. It can range from a few weeks to several months, influenced by factors such as the scope of testing, the quality of documentation, and the review timelines set by the notified body.





















































































































































































































































































































































































































































































































































































































0 Comments